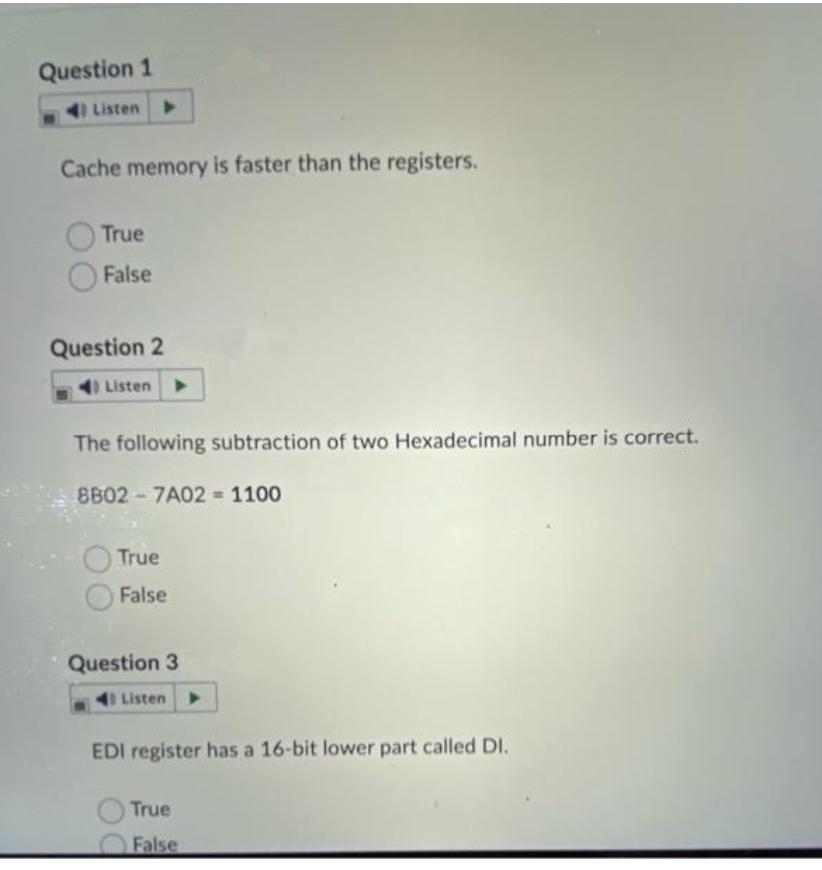
Question 1 Listen Cache memory is faster than the registers. True False Question 2 Listen The following subtraction of two Hexadecimal number is correct. 8B02-7A02 = 1100 True False
Q: We'll analyse the advantages of using Windows Service Control Manager in this post.
A: Introduction: Windows NT functions called SCM are used to start, stop, and communicate with Windows…
Q: To what end are formal techniques aimed? The use of standards in software development should have at…
A: The question is to write the aims of formal techniques in software development.
Q: In what ways does an operating system for a computer network work?
A: Functions of network operating system: A network operating system is built for the sole purpose of…
Q: How are routers set up?
A: Introduction The backbone of your home network is your router. Configuring your router correctly…
Q: Talk about the process of creating a new system.
A: Process of a System: Describe a procedure. Processes are all the interconnected actions (components)…
Q: As a consequence, the CPU suspends all active processes until the interruption is resolved. This is…
A: The answer may be found here: 1) An interruption is a signal that comes from outside the central…
Q: Defect elimination, not prevention, is the principle of Cleanroom Software Engineering, which…
A: Cleanroom Software Engineering: Errors may be identified earlier in the lifecycle thanks to…
Q: The statement passes a value back to a function's caller.
A: ANSWER IS GIVEN IN THE NEXT STEP:
Q: Calculate the waiting time and Turn Around Time (TAT) for each task and the average waiting time and…
A:
Q: Write a SQL statement to get the list of all the team members in the database. Include only the name…
A: Note: as mentioned we assume that Assume that all the statements from Q.6.2 have been executed…
Q: The this pointer is accessible (i) Within all the member functions of the class (ii) Only within…
A: The pointer is the variable whose value is the address of the another variable, i.e. direct address…
Q: Question 13 What is abstract method in Java?
A: Abstract method in java is: answer: An abstract method is a method without body explanation:…
Q: Which usability and user experience benchmarks were utilised in the evaluation and how were they…
A: Introduction: When developing software, the program's quality is one of the essential factors in…
Q: Encapsulation variables such as length, breadth, and height are _____________ .
A: Answer:
Q: Predictive, Diagnostic, and Prescriptive Machine Learning is being discussed for what purpose?
A: Given: Analytical descriptive approaches involve presenting historical data clearly. Descriptive…
Q: When it comes to the procurement of software, it is important to make a distinction between…
A: Software Purchase: A software interface with various features is needed in a traditional or…
Q: RAM, ROM, hard disc, and compact disc are all types of primary memory.
A: Introduction: Goal: Select the option that is called main memory. One that is referred as main…
Q: Please Answer it in Java only. Dinner, a kind of noodle soup with rice. Mr. Ping makes the best…
A: Coded using Java.
Q: This is the situation since computers are so powerful nowadays. How can we prove that computers have…
A: Nowadays, Computers are powerful tools as they will work with high speed, accuracy, and reliability…
Q: The only step of the system development lifecycle that needs to be discussed is the analysis stage.
A: Given: To understand the analysis step of the system development lifecycle. System development…
Q: What are the many kinds of software maintenance there to choose from?
A: Examples of software maintenance include: Remedial Maintenance Software fault rectification…
Q: Is it accurate to say that neural networks handle data sequentially? Explain.
A: SOLUTION: Recurrent Neural Networks (RNN) are a type of Artificial Neural Network that can process a…
Q: It's a common term in the Open Systems Interconnection Model, but what exactly is peer-to-peer?
A: A reference model where application networks are communicated with each other over a network is…
Q: Depending on the demands, a database may have two or three tiers. What attributes are achieved by…
A: There are several advantages to dividing database design into two or three layers by transitioning…
Q: each task and the average waiting time anc Assuming there is not input/output waitin three task…
A: Gantt Chart: T2 T1 T3 0 5…
Q: Problem description. In C++ In Betjemanian University, everyone has to enter his/her name on a…
A: Coded using C++.
Q: As a direct result of this, end users may choose to input data via the command line rather than…
A: Users may become adept at using a graphical user interface (GUI) much more rapidly than with a…
Q: Q. write a c++ program that draw a few shapes in the window.
A: I will explain it in details,
Q: What is the key distinction between object-oriented programming and traditional computer…
A: When you've finished reading this article in its entirety, you will have gained an understanding of…
Q: As a programmer, provide two instances of how you can speed up the cache.
A: ACCESS PERIOD: The speed at which operations are carried out into and out of the cache memory is…
Q: you have two matrixes x [N][N] and Write a program to to implement the following instructions. 1.…
A: since no programming language is mentioned in the question, the question was solved in C language.
Q: To appropriately categorise a variable, its "type" and "additional properties" must be identified.…
A: Introduction: If we are talking about programming languages, then a variable is the name given to a…
Q: he usable life of a system is nearing its end, therefore what are some signs of this?
A: Answer:- The capacity of a system to provide steady data streams is the first sign of its remaining…
Q: Q) BEZIER CURVE PRODUCED BY BERSTEIN BASES FUNCTION HAS LIMITED FLEXIBILITY. JUSTIFY THE STATEMENT.
A:
Q: Draw an Entity Relationship Diagram (ERD) using Unified Modelling Language (UML) notation according…
A: The solution is :
Q: What is a poison packet attack, exactly? Please provide two examples of this type of assault.
A: Definition of a poison packet attack Answer: ARP Poisoning (also known as ARP Spoofing) is a sort…
Q: Here, software development and academic writing are contrasted to see which is more efficient. When…
A: Differences: The objective is achieved by a software developer writing computer code. Research,…
Q: Why do different operating systems insert disc folders at different track places on the disc? What…
A: Introduction: The advantages of constructing more than one division are as follows:
Q: Assume three ready-to-run processes in secondary memory. Process 3 has no priority since 1 is most…
A: The function of the operating system that oversees the completion of a variety of different jobs. It…
Q: What methods are there for improving information privacy?
A: EXPLANATION: The technologies for enhancing information privacy utilize the various kinds of…
Q: "knowledge-based" agent is what? Give a thorough example to help.
A: The question is on the definition go "knowledge-based" agent and giving example.
Q: What does the public visibility modifier mean? -means accessible from any class in the same…
A: Introduction: There are different access modifiers available in the java: Public, private, protected…
Q: What characteristics do you believe a corporation with a "hot site" offshore arrangement should…
A: Introduction: I will just answer the first question. If a response to the second question is also…
Q: When and how did the first video camera appear?
A: Introduction: The History of Video Cameras: Video cameras have evolved significantly. Although…
Q: Recognize and distinguish between the primary tools and methodologies utilized in the creation of…
A: The Answer is given below step.
Q: The creation of software makes use of a variety of models, with each model having a variable level…
A: Definition A computer application that allows the user to construct simulations or other models is…
Q: If you want to compare structured and unstructured data, utilise examples to back up your…
A: Information that is stored in a fixed field inside of a document or record is referred to as…
Q: The importance of the UNIX kernel cannot be overstated. Explain why this is the case and how it…
A: The Kernel is the fundamental core at the heart of any computer operating system (OS). The core…
Q: How do you link LAN endpoints and infrastructure? Which cable do you use? What influences cable…
A: Given: How do you connect endpoints and infrastructure in a LAN? Which cable would you use?…
Q: Where can I get information about the present state of the network management market? Is there a…
A: Introduction: An operating system that has a been specifically designed for a network of computers,…
Step by step
Solved in 2 steps with 1 images

- QUESTION 7 Choose the correct instruction that will read data in from an I/O device. IN AL, 60 IN 60, AL OUT 60, AL OUT AL, 60 MOV AL, 60 MOV 60, AL QUESTION 8 The mask _____ can be used to isolate bit #2 of an 8-bit register. 00 H FF H 02 H 04 H QUESTION 10 Motorola processors use ___________, unlike Intel processors. a Memory-mapped I/O b Interrupts c Peripheral I/O d ParityFor the 8051 family of microcontrollers:i) Draw a representative memory map and explain how part of the data memory isable to share the same address space as the Special Function Registers in thecase of the 8052. ii) When an 8051 device is switched on, which memory bank is active? Explain howyou can switch to memory bank 1? iii) Explain why you should be very careful if you use a memory bank other thanmemory bank 0 if also using push and pop instructions. How can this issue beavoided?To the best of your ability, calculate the minimal number of bits required in the MAR for each of the following memory sizes. What is the real number of memory cells in a 640 KB memory unit that is claimed to have 640 KB? What do you think about 512 MB of RAM? What do you think about 2 GB of RAM? Explain the role that read-only memory (ROM) plays in the architecture of a computer system and why it is used. What kind of information is stored in read-only memory (ROM), and how does that information get into the memory in the first place?
- Explain the following code segments including lui $t0, 0xffff Wait: lw $t1, 0($t0) andi $t1, $t1, 0x0001 beq $t1, $zero, Wait lw $v0, 4($t0) What kind of registers we should use? What is the name of the registers? What do we call these code sequences in MIPS? Explain the memory layout where the registers are located Why do we need to loop? For what should we wait? When the 'ready' bit is changed? The purpose of and instruction The actual meaning of "lw $v0, 4($t0)" Explain the following code segments including lui $t0, 0xffff Wait: lw $t1, 0($t0) andi $t1, $t1, 0x0001 beq $t1, $zero, Wait lw $v0, 4($t0) What kind of registers we should use? What is the name of the registers? What do we call these code sequences in MIPS? Explain the memory layout where the registers are located Why do we need to loop? For what should we wait? When the 'ready' bit is changed? The purpose of and instruction The actual meaning of "lw $v0, 4($t0)"Aim: - Write program to add 3 hexadecimal numbers stored in the memory location (not in registers).Before adding the second number should be incremented once and the third number should be incremented twice. The result of the addition must be stored in another memory location. Platform Required:- sim8085.comCS 218: Assembly Language and Systems Programming Given the following code fragment: mov rax, 4 mov rbx, 3 imul rbx What would be in the below 64-bit registers after execution (in hex)? rax rdx Must answer in hex (must precede number with 0x).
- (a) How many 32 K×8 RAM chips are needed to provide a memory capacity of 256 K bytes?1. How many lines of the address must be used to access 256 K bytes? How many of these lines are connected to the address inputs of all chips?2. How many lines must be decoded for the chip select inputs? Specify the size of the decoder.2. This question is about Digital Logic and Address DecodingA computer is being designed using a microprocessor with a 16-bit address bus (A0—A15, where A0 is the least significant bit). The 64K address space is to be split betweenand allocated to RAM, ROM and I/O hardware as follows:Address Range (hex) Contains Select Signal0x0000 — 0x1FFF Main RAM RAMCS0x8000 — 0x9FFF Video RAM VRAMCS0xB000 — 0xBFFF I/O hardware IOCS0xC000 — 0xCFFF BASIC ROM BROMCS0xF000 — 0xFFFF OS ROM OSROMCSThe rest of the address space is unused.Note: As with many computer systems, it its only necessary to decode addresses to sufficiently identify each of the sections above uniquely. It is acceptable for some parts to be decodeable by more than one address provided these extra addresses do not overlap any of the other specified address ranges. Using a combination of AND, OR and NOT gates and the signals (A12 — A15) that contain the top four bits of the address in binary form: a. Derive the equation for a logic…q) How the operation of software interrupt instructions differs i.e. INT, INTO, INT 3, and BOUND? q) Dynamic RAM (DRAM) retains data for only a short period (usually 2–4 ms) creatingproblems for the memory system designer. What type of mechanism is required to overcome this problem in DRAMs? q) What are the three common methods of expanding the interrupt structure of themicroprocessor? Explain any one of them along with example.
- . set Explain the reason for the number of bits being used for Tag and for the number of bits required for RAM address? for 4way , fully (simple ansewer for each one )Topic: Computer Science, CPU Architecture and Assembly Programming 1. Write ASL programs in EMU8086 to accomplish the following tasks. a) Evaluate (5 + 4) * 36. Your solution should store the answer in the Ax register. b). Evaluate (420 + 312) *300 and explain where is the result of the multiplication. You need to use 2 bytes registers like Ax, Bx, Cx, Dx… to store these type of data that are greater than 255.Which of the following is true? 1) the 80/20 rule states that 80% of the instructions is excutede and 20% of the instruction is generated. 2) in von Neumann architecture, external bus is for data memory only

