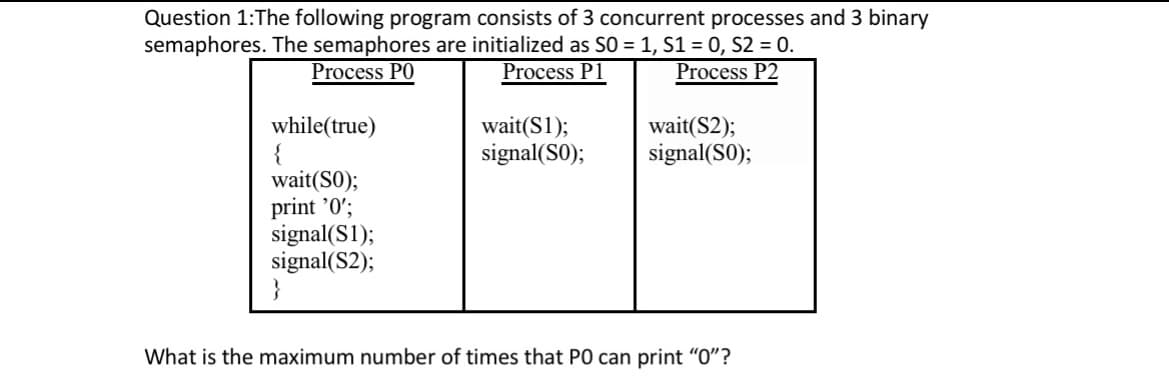
Question 1: The following program consists of 3 concurrent processes and 3 binary semaphores. The semaphores are initialized as S0 = 1, S1 = 0, S2 = 0. Process PO Process P1 Process P2 while(true) { wait (S0); print '0'; signal(S1); signal(S2); wait(S1); signal(SO); wait(S2); signal(S0); What is the maximum number of times that PO can print "0"?
Q: tages does it bring to the testing proce
A: Introduction: As you are aware, the Internet has developed in ways we never could have predicted. A…
Q: What are the two hardware methods for prioritization, and how do they differ from one another?
A: What are the two hardware methods for prioritization, and how do they differ from one another answer…
Q: If you're familiar with C++, how can you tell the difference between basic and advanced data types?
A: Data types specify all the data with a similar property and represent the nature and kind of data…
Q: Give very particular data about the technique for reviewing the program structure, along with some…
A: Program review is the process of evaluating a software program to identify its strengths and…
Q: When may it make sense to use a database system, and why? Give an instance of a data processing…
A: Your answer is given below.
Q: When talking about a system, what exactly do we mean when we say "test it?" Outline the many methods…
A: Introduction: What is system testing exactly? Describe the many testing techniques available.
Q: Where does artificial intelligence (AI) want to go in the long run? Include two illustrations from…
A: HOW IS ARTIFICIAL INTELLIGENCE DEFINED: The primary goal of artificial intelligence (AI) research is…
Q: Q1 Distinguish First-Order Logic f escribe how can we transfer from Syntax - Q2- What are the main…
A: Note: According to the guidelines we can solve only one question at a time. Hence resubmit the…
Q: How are measurements for software upkeep determined?
A: Introduction: There are five different classifications of metrics used in software maintenance.…
Q: Examine when and why the three common forms of testing are conducted.
A: Introduction: There are three different kinds of tests: Testing is done on every system to determine…
Q: Which components of the creation of a compiler need to be prioritized in order to guarantee that the…
A: In this question we need to provide components of the creation of a compiler which are needed to be…
Q: 15. Solve the following recurrence equations using the characteristic equation. (a) tn = 6tn-1-9th-2…
A: a) tn = 6tn-1 - 9tn-2 solution: tn - 6tn-1 + 9tn-2 = 0 ------ (1) tn = crn , (c, r != 0)…
Q: I was wondering what you believe are the most crucial aspects to remember while doing performance…
A: When performing performance testing, it is important to keep the following aspects in mind:…
Q: What does WAN stand for as an acronym?
A: Network It is a grouping of computing devices—including desktop and laptop computers, servers, and…
Q: Utilize illustrative examples if you want your discussion of the software structure review process…
A: Please find the detailed answer in the following steps.
Q: It should be made clear what a buffer overflow is.
A: A buffer is a temporary storage area for data, generally in the computer's memory (RAM). A buffer's…
Q: What happens if an adversary attempts to alter the Tag (the MAC) and the ciphertext of a…
A: The acronym for the ticket is MAC. It is a piece of information used to verify the sender and…
Q: The stack is a helpful data structure for various computer problems, as demonstrated by the…
A: Yes, you're correct. The stack data structure is commonly used in computer science to solve various…
Q: Please provide some examples of IAA balanced scorecard key performance indicators for operations and…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: What makes object-oriented analysis and design superior to other techniques for system analysis and…
A: Introduction: Object-oriented analysis and design (OOAD): OOAD is a technological technique that…
Q: An analysis of the benefits and drawbacks of receiving an education via an online medium supported…
A: Online education supported by AI offers a number of benefits and drawbacks, which can vary depending…
Q: How realistic is the idea that we might incorporate artificial intelligence into our day-to-day…
A: A subfield of computer science called artificial intelligence can do human-level tasks. Artificial…
Q: Some of your friends have gotten into the burgeoning field of time-series data mining, in which one…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: The architectural components of Ven Neumann may potentially be described.
A: Please find the detailed answer in the following steps.
Q: What do you consider to be the most important strategy that database designers use in order to…
A: Databases To create a review of anything, one must first determine how it truly functions and what…
Q: To remove the write permissions for a group, which two parameters should you use with the chmod…
A: Operating system:- An operating system (OS) is a software program that manages the hardware and…
Q: Many of the Smart Cities and Public Transport Hub like Airports and Train Stations nowadays have…
A: Designing a wireless network that can handle more than 100,000 connections at a time, is free for…
Q: Discuss the relationship between the system life cycle and system development approaches.
A: Introduction: This methodology is disciplined and risk-averse, making it suitable for managing…
Q: It is necessary to discuss the Area variable while talking about an OSPF autonomous system (OSPF…
A: In an OSPF AS, the shortest path first autonomy is supported.
Q: There have been several suggestions for a processor that can first decrypt encrypted data and system…
A: A central processing unit (CPU) is an electrical component that processes computer programme…
Q: When comparing IPSec to other possible solutions for network security, including application layer…
A: The Internet Engineering Task Force (IETF) standard suite of protocols known as IP security (IPSec)…
Q: When you ping your computer, what type of communication protocol are you using?
A: The ability to test network connectivity and reachability is a fundamental aspect of network…
Q: Depending on how mature the testing is, write a short essay on three different testing goals
A: Software testing is an essential part of the software development process, and its goals can differ…
Q: When talking about a system, what exactly do we mean when we say "test it?" Outline the many methods…
A: Introduction: Just what does "system testing" entail? Give an account of the many techniques used…
Q: How many distinct types of memory exist in computer architecture?
A: Memory is one of the most critical components of a computer system for storing and processing data.…
Q: Swift: 1. What are three of the primary responsibilities of a UIView Object? 2. How is a view's…
A: Q1 Three of the primary responsibilities of a UIView Object in iOS development are: a. Drawing and…
Q: Why is the internet considered to be one of the most advanced information and communication…
A: Because it can instantly link people and information from across the globe, the internet is…
Q: How did evaluation criteria regarding usability and user experience become weighted?
A: Usability is a more constrained concept than user experience because it concentrates on goal…
Q: ranslate these statements into English, where the domain for each variable consists of all real…
A: There exists x and there exists y such that x + y = y + x
Q: Why, in the eyes of supporters of the open-source software movement, is software that is protected…
A: The open-source paradigm encourages open collaboration and is based on a decentralized methodology…
Q: Pick the Al business application you see the greatest value in right now. Develop the point. Find a…
A: Introduction The use of predictive analytics has enabled companies to save time and money by…
Q: What is the difference between Google Docs and Microsoft Office 365?
A: This article's goal is to examine the similarities and differences between Google Docs and Office…
Q: Given a directed line from point p0(x0, y0) to pl(x1, y1), you can use the following condition to…
A: Turtle is a Python library which enables users to create pictures and shapes by providing them with…
Q: Information on the ALOHA protocol may be found here. Expound upon the merits it has.
A: ALOHA is an early multiple access protocol developed in the 1970s that allows multiple users to…
Q: required that every machine that uses IPsec have its own unique set of private keys; however, it is…
A: Enforcing the requirement of unique private keys for each machine using IPsec can be achieved…
Q: When it comes to a processor's ability to access main memory, a symmetric multiprocessing system and…
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: To be more specific, what are the criteria for the page table?
A: Introduction : The page table is a data structure used in virtual memory management in operating…
Q: Give a credible justification for why the computer needs each kind of interruption.
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: Consider a byte-addressable computer with a 16-bit main memory address and 32 blocks of cache memory…
A: Individual testing: As the name indicates, it is the testing performed by a single tester.…
Q: The software demonstrates why a stack is a valuable data structure for a wide range of computational…
A: Algorithm: Here's the algorithm for the code that converts a decimal number to binary using a stack:…
Step by step
Solved in 2 steps

- The following program consists of 3 concurrent processes and 3 binary semaphores. The semaphores are initialized as S0 = 0,S1 = 1 and S2 = 1. Process P0:while (true) { wait (S0); print '1';release(S1);release(S2);} Process P1:wait (S2);release (S0); Process P2:wait(S2);release(S0); How many times will process P0 print '1'?) Consider the following sequence of virtual memory references (in decimal) generatedby a single program in a pure paging system:100, 110, 1400, 1700, 703, 3090, 1850, 2405, 2460, 4304, 4580, 3640a. Derive the corresponding reference string of pages (i.e. the pages the virtual addressesare located on), assuming a page size of 1024 bytes. (Assume that page numberingstarts at 0)b. For the page sequence derived above, determine the number of page faults for each ofthe following page replacement strategies, assuming that two (2) page frames areavailable to the program.i. LRUii. FIFOiii. OPT (Optimal)In the above, we had the three concurrent processes p1, p2 and p3, each with the number s1 = 2, s2 = 3 and s3 = 2 of states, respectively.
- you are tasked with analyzing an algorithm which schedulea processes in a multiprogramming system. You are working with a computer that has two CPUs, each CPU having two threads (hyperthreading). You are studying a scenario with three processes: P0, P1, & P2., with run times of 5, 10, & 20 msecs, respectively. All 3 programs are 100% CPU bound, don't block, and always run in the CPU it's assigned to. How long will it take for these programs to complete execution. Show three different possible outcomes (and assigned process to processor, 3 different combinations and resulting total time for all three to complete)32. Let m[0]…m[4] be mutexes (binary semaphores) and P[0] …. P[4] be processes. Suppose each process P[i] executes the following: wait (m[i]);wait (m[(i+1) mode 4]); ......... release (m[i]); release (m[(i+1)mod 4]); This could cause a. Thrashing b. Deadlock c. Starvation, but not deadlock d. None of the aboveSuppose your system has a memory of size 100 MB using contiguous memory allocations and there are 4 fixed size partitions. Partition one of size 50, partition 2 of size 200, partition 3 of size 100 and partition 4 of size 150 Consider First 5 letters of your name. The ASCII code of the letters is the size of process and the alphabet is the name of process. The processes appear in alphabetical order. Q= How many processes will be loaded in the memory at a time? For contiguous memory allocation show the algorithms used to allocate memory partitions to each process and state which algorithm will work best and why? Also state the amount of internal and external fragmentation for the processes and partitions after allocation NOTE :MY NAME IS ALIZAHID
- List the 4 conditions that can cause a deadlock for concurrent processes P1 and P2. (short answer is ok)Answer the given question with a proper explanation and step-by-step solution. Consider the following source code, where k,l and m are constants declared with #define. The struct lnode is as defined as: struct lnode { char *str; // points to 32-character string struct lnode *next; // points to next node address struct lnode *prev; // points to prev node address }; You will need to determine the values for k, l and m, which are the dimensions of a 3-D array named A. struct lnode A[k][l][m]; int store_ele(int h, int i, int j, struct lnode dest) { A[h][i][j] = dest; return sizeof(A); } On compiling this program (with gcc -O2 -S -fno-asynchronous-unwind-tables) ,gcc generates the following assembly code for the store_ele function: store_ele: endbr64 movslq %edi, %rdi movslq %edx, %rdx movslq %esi, %rsi movdqu 8(%rsp), %xmm0 movq %rdi, %rax leaq (%rdx,%rdx,2), %rdx salq $6, %rax subq %rdi, %rax salq $4, %rax leaq (%rax,%rdx,8), %rax leaq (%rsi,%rsi,4), %rdx leaq (%rsi,%rdx,4), %rdx leaq…Write a C program Producer – Consumer as a classical problem of synchronizationStep 2. Write a program* that solves the producer - consumer problem. You may use the following pseudo codefor implementation.*program to write: produce -consumer problem to produce and consume the alphabet.//Shared data: semaphore full, empty, mutex;//pool of n buffers, each can hold one item//mutex provides mutual exclusion to the buffer pool//empty and full count the number of empty and full buffers//Initially: full = 0, empty = n, mutex = 1//Producer threaddo {…produce next item…wait(empty);wait(mutex);…add the item to buffer…signal(mutex);signal(full);} while (1);//Consumer threaddo {wait(full)wait(mutex);…remove next item from buffer…signal(mutex);signal(empty);…consume the item } while (1); it consumes and produce the alphabets not numbers sample output is attached you please also attach your sample output
- Develop a program in C to create three processes A, B and C. Job of these individual processes are as follows: Process A: Reads n numbers from the keyboard and counts the number of odd numbers in it. Then this count will be sent to the Process B. Process B: Reads the count from Process A and determines the fibonacci sequence of that count. This fibonacci sequence result will be sent to the process C. Process C: This process reads the fibonacci sequence from process B and sort the numbers in descending order.You could implement an application as either a uni-threaded process or a multi-threaded process or as multiple 1) Discuss the pros and cons of each of the three approaches listed above 2) In case you choose the multi-threaded process approach, how does it matter whether the threads are user-level threads or kernel-level threads? Discuss the pros/cons of both 3) If you were using kernel level threads and your machine is a uniprocessor, is there any benefit in running the application as a multi-threaded process versus; a uni-threaded process?Imagine that you have implemented an algorithm in a program which has 40% parallelizable code. Now consider the following two cases assuming that scheduling overhead is ignored: -The program is executed on a single processor. -The program is executed on a parallel system with 4 processors. Compute the speed-up gained in the case where multiple processors are used.

