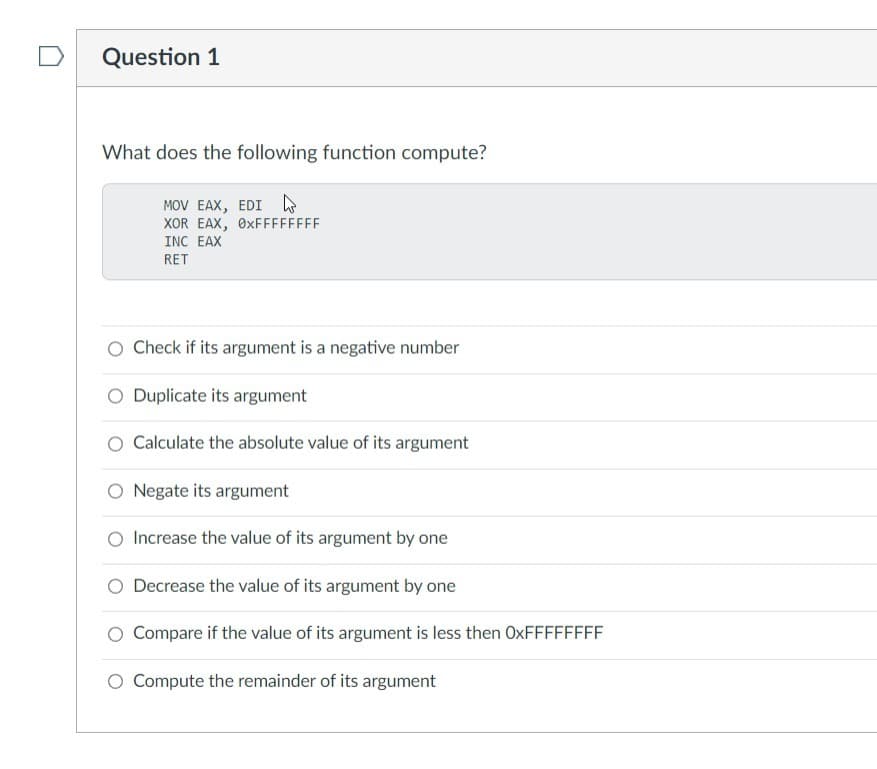
Question 1 What does the following function compute? MOV EAX, EDI XOR EAX, 0xFFFFFFFF INC EAX RET Check if its argument is a negative number Duplicate its argument Calculate the absolute value of its argument O Negate its argument Increase the value of its argument by one Decrease the value of its argument by one Compare if the value of its argument is less then OxFFFFFFFF Compute the remainder of its argument
Q: If you have sensitive information, how confident are you that it will remain private?
A: Introduction: To make sure that your information is secure and well-protected for the rest of your…
Q: What is the difference between normalization and denormalization, two terms that are often used…
A: The processes of normalization and denormalization: Normalization is the process of eliminating…
Q: You should have a look at the five ethical considerations in IT.
A: Ethical considerations in research are a set of principles that guide your research designs and…
Q: In what steps does the Von Neumann Cycle culminate? When doing each stage, what exactly occurs to…
A:
Q: Expound on why Agile is useful and how it may be implemented.
A: Agile methodology is commonly used for software development projects.
Q: Does agile software development have a specific issue that you'd want to talk about?
A: Software Development: Software development is the process of creating a software deliverable via…
Q: A definition is requested for each of the following terms. Things like (a) AI, (b) an agent, (c)…
A: 1) AI is an abbreviation for artificial intelligence, 2) Artificial intelligence refers to the…
Q: The definition of NAT (Network Address Translation). (NAT). When asked why the network layer is…
A: By altering the header of IP packets as they are being transmitted through a router, a network…
Q: You need to access customer’s records in a database as you’re planning and marketing campaign what…
A: HERE IS COMPLETE SOLUTION REGARDING YOUR PROBLEM WITH EXPLANATIONS
Q: Is there anything further we can do to guarantee the accuracy of data collected in the field?
A: In the field of computers, "data" refers to information that has been converted into a form that is…
Q: Consider the following failure model for faulty processors. Processors follow the protocol but might…
A: Assume that each node in the multicast functionality which refer to as basic multicast or…
Q: The systems analyst has a total of forty duties, spread over four categories (40). Can you explain…
A: The upkeep and modernization of a company's and its customers' computer systems is the…
Q: Which online resources do you find most useful as a student in your area of study?
A: Definition: What benefits do the various online platforms provide you as a student in your chosen…
Q: In the years after the American industrial revolution, what happened?
A: Revolutions are born when the social climate in a country changes and the political system does not…
Q: For what use does a layer exist for networks if they are already interconnected?
A: The OSI Model's Seven Layers are Describedlayer of matter. Layer of Data Link. System Layer.…
Q: Why is it problematic to have many, incompatible data sources?
A: Over 60% of organizations said that having too many data sources and inconsistent data was their…
Q: What kind of impact do you see AI having on people's lives in the not-too-distant future?
A: The productivity of our workplaces may be significantly increased by artificial intelligence, which…
Q: In what steps does the Von Neumann Cycle culminate? When doing each stage, what exactly occurs to…
A: Fetch Memory Instructions Instruction and Fetch Operands Decoding carrying out ALU operations Access…
Q: How many distinct data requests are possible in a decentralized database architecture?
A: In a decentralized database system, the number of data queries is theoretically infinite.
Q: What is the difference between normalization and denormalization, two terms that are often used…
A: the difference between is an given below :
Q: The systems analyst has a total of forty duties, spread over four categories (40). Can you explain…
A: System analysts are responsible for maintaining and upgrading the computer systems used by a…
Q: Instead of storing shared structures in shared memory, an alternative architecture would be to store…
A: Here are some problems that could happen with the current architecture:
Q: F router to have an unique ID?
A: Introduction: Routers use the Internet Protocol (IP) to connect networks, and OSPF (Open Shortest…
Q: If you have sensitive information, how confident are you that it will remain private?
A: The question has been answered in step2
Q: What is the result of first performing the cross product of student and advisor, and then performing…
A: Introduction: Cross Product: Cartesian Product in DBMS is an operation used to merge columns from…
Q: When switches belonging to different ATM service providers are linked together, what kind of…
A: The services supplied by ATM networks are those that transport subscriber sessions to the access…
Q: What situations call for the usage of structured English in data processing models? What difference…
A: We need to discuss the situations that call for the usage of structured English in data processing…
Q: Assistance with data entry, database administration, and data integrity checking capabilities?
A: Users are assisted in data input by the characteristics of the data integrity concept in database…
Q: Describe the TCP/IP abstraction stack's four distinct layers.
A: The TCP/IP Stack, frequently known as the web convention suite, is an assortment of communication…
Q: Describe the situation in your own words. 5 categories of ATM services
A: Answer:
Q: Describe the five requisites for wireless LANs and their significance.
A: Answer: Introduction : LAN stands for Local Area Network. It is a very important device that can…
Q: Outhers are often discarded as noise. However, one person's garbage could be another's treasure. For…
A: Introduction: At the point when just a few marked instances of typical items then, at that point,…
Q: Instead of storing shared structures in shared memory, an alternative architecture would be to store…
A: Following are some of the issues that might be encountered with the current architecture:
Q: Just how does agile alter the time-honored system development lifecycle (SDLC)?
A: Just how does agile alter the time-honored system development lifecycle (SDLC) answer in below step.
Q: What two methods of data processing are now used in state-of-the-art systems?
A: The two different data processing approaches that are now used in modern systems are described in…
Q: i am just wondering what does this piece of code do, what language is it and what meaning it has…
A: In this question we have to understand what programming language is present in the code given and…
Q: What two methods of data processing are now used in state-of-the-art systems?
A: The two different data processing approaches that are now used in modern systems are described in…
Q: I'm curious as to what you think the benefits and drawbacks of using information systems are.
A: A tool for organizing the collection, processing, and analysis of information is an information…
Q: the concept of an object in the object-orie
A: Solution - In the given question, we have to tell the difference between the concept of an object in…
Q: efit to using dynamic programming while making decisions in sequence? What give
A: Introduction: It's just a fancy way of saying that you'll save the values of the subproblems as you…
Q: How does the concept of an object in the object-oriented model differ from the concept of an entity…
A: Entity-relationship Diagram:- By characterizing the entity, and their attributes and demonstrating…
Q: Is there software that can help with data entry and database maintenance in a way that do Compromise…
A: Here in this question we have asked that is there any software that can help with data entry and…
Q: Can you please explain how this relates to Agile vs. Waterfall in the context of system development?
A: The agile approach is a notion that facilitates software development by permitting continuous…
Q: How do we ensure that the information we're using is accurate?
A: Data Accuracy The organization can only monitor its performance with the help of efficient data…
Q: If you have sensitive information, how confident are you that it will remain private?
A: INTRODUCTION: Information secrecy is around securing information against inadvertent, illegal, or…
Q: provide a moral dimension to computer systems?'
A: Dimension in Computer: A dimension in data warehousing is a group of references details about a…
Q: Give an example each of two issues that modern information systems are attempting to solve.
A: Modern Information Systems: Daily, new technologies and tools are created, deployed, and introduced…
Q: Explain how Bayes' theorem is applied in real-world software packages.
A: Explain how Bayes' theorem is applied in real-world software packages answer in below step.
Q: Mark Burgess has five tenets of system management, what are they?
A: Security is the discipline of protecting interests and valuables. Student assessment is a security…
Q: List the three components of a database management system and describe their functions.
A: The database management system (DBMS) is a technological tool for managing and optimizing data that…
aNSWER PEROPERLY EXPLAIN IT
Step by step
Solved in 3 steps

- Question 6 # This function checks whether a given number is even or not def isEven(number): """ what it takes? a number what it does? determines if a number is even what it returns? if even, return 1 if odd, return -1 """ # your code goes in here defisEven(number): #check if the number is divisible by 2 by checking the remainder. if number % 2==0: #If remainder is 0, then its divisble by 2 and an even number #hence return-1 return1 else: #if remainder is not 0, it'll be 1, so its NOT divisible by 2 and its an odd number #hence return -1 return-1 Test case for question 6 try: if isEven(5) == -1: score['question 6'] = 'pass' else: score['question 6'] = 'fail' except: score['question 6'] = 'fail' isEven(5)5.11 LAB: User-Defined Functions: Max and min numbers Coral language only please Define a function named LargestNumber that takes three integers as parameters and returns the largest integer. Define a second function named SmallestNumber that takes three integers as parameters and returns the smallest integer. Then, write a main program that reads three integers as inputs, calls functions LargestNumber() and SmallestNumber() with the inputs as arguments, and outputs the largest and the smallest of the three input values. Ex: If the input is: 7 15 3 the output is: largest: 15 smallest: 3 Your program should define and call two functions:Function LargestNumber(integer num1, integer num2, integer num3) returns integer largestNumFunction SmallestNumber(integer num1, integer num2, integer num3) returns integer smallestNumQuestion Asked Jul 9, 2020 3 views Python Programming- Computer-Assisted Instruction Part 1: Computer-Assisted Instruction (CAI) refers to the use of computers in education. Write a script to help an elementary school student learn multiplication. Create a function that randomly generates and returns a tuple of two positive one-digit integers. Use that function's result in your script to prompt the user with a question, such as: How much is 6 times 7? For a correct answer, display the message "Very good!" and ask another multiplication question. For an incorrect answer, display the message "No. Please try again." and let the student try the same question repeatedly until the student finally gets it right. Then, modify the program so that various comments are displayed for each answer. Possible responses to a correct answer should include 'Very good!' , 'Nice work!' and 'Keep up the good work!' Possible responses to an incorrect answer shojld include 'No. Please try again.' ,…
- function myCompose(f,g){// TODO: return (f o g);// that is, a function that returns f(g(x)) when invoked on x.}Hi there please dont put existing one Function ReccurenceCreate a function sumofAllOdd(s,e) that will return the sum of all odd numbers in a range of inputted numbers s (starting number), e(ending number). For example: Test Result sumofAllOdd(22,55) sumofAllOdd(5,10) Answer:(penalty regime: 10, 20, ... %)
- Question 3: Write a function that computes the ratio of vowels vs. consonants (????????????????����������������) in a given sentence. The ratio should be given as a floating-point number rounded off to two decimal places. When writing your function, be sure to appropriately cater for the following punctuation marks: apostrophes (') quotations (") full stops (.) commas (,) exclamations (!) question marks (?) colons (:) semicolons (;) Arguments: sentence (string) →→ sentence required to compute the ratio. Return: ratio (float) →→ a ratio that describes the number of vowels to consonants: vowels/consonants. ?HINT? Remember to cater for the white spaces that appear in your sentence. Expected outputs vowel_consonant_ratio("This is a random sentence!")==0.62 vowel_consonant_ratio("Thomas! Where have you been?")==0.83C++ QUESTION 2. The following function definition is not perfect. What two errors can you find?int search(int a[n], int numberUsed, int target) {int index = 0; bool found = false; while ((!found) && (index < numberUsed)) if (target = a[index]) found = true; elseindex++;if (found) return index;else return -1;}Hi, im making a ladders and chutes game. can someone help me make this into a function which i can call in the game to check if a player landed on any of these squares. Thanks int snakes[100] = {0}; int ladders[100] = {0}; snakes[31] = 11; snakes[23] = 16; snakes[19] = 7; snakes[45] = 20; snakes[61] = 49; snakes[39] = 30; ladders[11] = 26 ; ladders[3] = 22 ; ladders[20] = 29 ; ladders[5] = 8 ; ladders[50] = 60; ladders[80] = 92;
- Given the following function, answer the two questions that follow CREATE OR REPLACE FUNCTION Cale Age (V ID IN Student Sid ID%TYPE)RETURN NUMBER ISV_Age NUMBER, BÉGINSELECT SYDATE - Std_DOB INTO V AgeFROM StudentWHERE Std_ID = V_ID;RETURN V age;END; (a)Wbat does the word IN in the function parameter list mean? (b)Winte a SOL test statement to call the function. You may make up a fake student ID.Using Python I'm trying to create a function to scrape Weather.com for the location and weather of any given zipcode. When I pass in a zipcode as an input argument into a function, it should print the name of the city, the state of the city, the weather in Fahrenheit, and the zipcode. For example, using the url, https://weather.com/weather/today/l/93106:4:US I should be able to create a function that prints out Santa Barbara, CA The current temperature 93106 I am unsure on how to code on passing any input zipcode.Please answer it in Python Write a function input_names that takes as an argument a number player (supposedly valid) corresponding to the number of players who will play the game and which successively asks for the name of each player. The function verifies that the names of the players are all different and returns the list of the names of the players. The messages will ‑have to be clear. For example: input_names(3) #return => Enter player name 1: rara Enter player name 2: rara Enter player name 2: riri Enter player name 3: roro [“rara”,”riri”,”roro”] Input_names(2) #return => Enter player name 1: roro Enter player name 2 : rara

