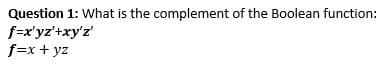
Question 1: What is the complement of the Boolean function: f=x'yz'+xy'z' f=x + yz
Q: How hard is it to keep track of the change from on-premise computers to those housed in a design…
A: The utilization of on-premise PCs is gradually giving methods for cloud computing models like…
Q: How does the data dictionary play a part in each of the DBLC's six phases?
A: The Database Life Cycle (DBLC) is a process followed by database developers and administrators to…
Q: What is the difference between coupling and cohesion? Which should be minimized and which should be…
A: Coupling and cohesion are fundamental concepts in software engineering that play a crucial role in…
Q: What exactly are "condition variables," and how do they make their presence known? What precisely is…
A: Condition variables and monitors are synchronization mechanisms used in concurrent programming to…
Q: The inventor of the Fagan inspection, Michael Fagan claimed on his site. that: “The Fagan…
A: The Fagan Defect-Free Process is a structured peer review process developed by Michael Fagan in the…
Q: You have a responsibility to learn about the most important problems that can happen with…
A: Some of the most important problems that can happen with information systems include cyber-attacks,…
Q: A call perm(1) generates the permutations of the first n integers, stored in array T, where perm is…
A: Answer is explained below in detail
Q: May you please solve quick within 20-40 minutes ? There are two types of personnel working in a…
A: Define three functions - checkEmployee, checkTitleScore, and checkLanguageLevel - that will be used…
Q: In one of the papers we recently read “Storyboarding as a Means of Requirements Elicitation...” the…
A: The design process is defined as the method of finding what needs to do and create something…
Q: In the context of Software Development Project Methodologies, which of the following statements best…
A: The statement that best distinguishes between the traditional Software Development Life Cycle (SDLC)…
Q: List the "lost and found" app's functioning and non-functional student criteria.
A: List the "lost and found" app's functioning and non-functional student criteria.
Q: b. Use resolution to prove the following sentence from the clauses above. ¬AA¬B
A: To prove ¬A ^ ¬B using resolution, we start by converting the given sentences to clauses: {A, ¬BVE}…
Q: Let's say you work for a big company that uses a firewall to keep people from getting into its…
A: In the meadow of network security, it is vital to apply various layer of defense. This idea, known…
Q: Creating a MIS information security strategy, what cyber security threats will you anticipate?
A: Cybersecurity is the protection of internet connected systems such as hardware software and data…
Q: How do the different kinds of routes in a WAN work
A: What is network: A network is a group of computers and devices connected together to share…
Q: How can we distinguish between a local-area network and a wide-area network using the structure and…
A: Local Area Network : LAN refers to a collection of network hardware that enables communication…
Q: What is the key distinction between network architecture and application architecture?
A: Network architecture is the term for the planning and structuring a communication system. It…
Q: nly tell given statement is true or false
A: Java Generics: Java Generics is a feature that was introduced in Java 5 to provide type safety and…
Q: Given the following IEEE 802.15.4 mesh running the RPL protocol. The numbers indicated next to each…
A: RPL (Routing Protocol for Low-Power and Lossy Networks) is a routing protocol designed for use in…
Q: Look at the many categories of access control methods. Talk about the many sorts of controls that…
A: Three fundamental sorts of access control frameworks are: Discretionary Access Control (DAC), Role…
Q: How blocks are put in a database affects how well it works.
A: How blocks are put in a database affects how well it works.
Q: Placing numbers from 1 to 100 in a sequential manner into a 100-element array.
A: An array is a data structure that stores a collection of elements of the same data type in…
Q: What changes in our lives has Google made?
A: Google has entirely replaced how we find and use information. Google's robust search engine enables…
Q: How can you anticipate and prepare for cyber security threats while creating a MIS information…
A: In this question we have to understand How can you anticipate and prepare for cyber security threats…
Q: Please explain what a challenge-response system is and how it works to make sure people are who they…
A: A challenge-response system is a method of verifying a user's identity by asking them to respond to…
Q: Л АЛ TL Write a Matlab program to plot the sequence x(n) = cos(won) for wo = 0 You may use the…
A: According to the information given:- We have to a Matlab script to plot the sequence x(n) = cos(ωon)…
Q: How can a programmer increase their knowledge of web page architecture in multiple ways?
A: To enhance knowledge in web sheet architecture, a programmer must fundamentally understand the…
Q: Python: What are the steps to opening a web page using a software like this?
A: In Python, there are several libraries available to perform various tasks, including opening a web…
Q: The common instruction set operations can be placed into the following categories: ● Data transfer ●…
A: Hello student Greetings The question is related to computer architecture and the common…
Q: The DBLC comprises six stages. How does the data dictionary affect each?
A: The DBLC (Database Life Cycle) is a procedure utilized for the design, development, as well as…
Q: What are some of the most significant capabilities and applications of Azure Monitor?
A: Azure Monitor is a comprehensive monitoring and logging solution provided by Microsoft Azure. It…
Q: System software and embedded system software can be distinguished by a distinct dividing line. Could…
A: System software includes the operating system, device drivers, and system utilities. It supervises…
Q: An engineer who is good at building a wall may not be good at constructing a house or a multistory…
A: Software engineering differs from conventional engineering in that it primarily deals with digital…
Q: I need help with this Java program over a Student class program shown in the image below: The…
A: Introduction:The given task is to create a Student class in Java that extends the Person class and…
Q: a. Write a RECURSIVE algorithm (or a method) that to detect if a given array of integers is sorted…
A: According to our guidelines, we are allowed to solve only the first question, as they are both…
Q: What variations exist between the OSI and TCP/IP protocol models? Use data and evidence to support…
A: What variations exist between the OSI and TCP/IP protocol models? Use data and evidence to support…
Q: Give an outline of the many different ways that data can now be hidden. Each of these methods…
A: Information hiding refers to the practice of concealing data, communication or other forms of…
Q: Staying on Whitney Mesa, use the "Historical Imagery" tool to go forward and backward in time. Look…
A: It is difficult to find evidence of the Whitney Mesa fault in recent images because it is an…
Q: Write a C# program that asks the user to enter their name and age, and then prints a greeting…
A: What is programming: A programming language is a set of instructions used to communicate with a…
Q: Let's examine: You design hospital patient control software. The system is reliable and displays…
A: The Waterfall model is a sequential software development procedure model anywhere The expansion…
Q: Discuss, using real-world examples, the key distinctions that exist between a Web Server software…
A: A web server and a web client are two distinct components that work together to deliver content over…
Q: Mumber of Novels Authored Author Jane Austen Charles Dickens Ernest Hemingway Jack Kerouac Number of…
A: We need to read from the text file so streams are used. For formatting the strings iomanip functions…
Q: hree keepass (tool) to analyze/monitor system or network goals?
A: KeePass is a popular password management tool that allows users to securely store and organize…
Q: Why did Cisco decide to use an IP networked solution instead of a standalone access control system?
A: Cisco is a multinational technology organization that gives networking hardware, software, and…
Q: What are the two types of encryption that are used the majority of the time? What really…
A: 1) Encryption is the process of converting plaintext, or unencrypted data, into ciphertext, or…
Q: What elements are necessary to build a web application?
A: A website application, often known as a web app, is a software application program that uses…
Q: need help with a Java program over a University class program shown in the image below: I need…
A: In this question we have to write a java program for University class program Let's code and hope…
Q: Give an overview of the three methods of file structure that are considered the most significant.
A: Synopsis of File Structure Methods: File structures are necessary in organizing data to enable…
Q: /*Author: Cody Guardipee Date: 5/1/2023 Purpose: Calculate Fuel Economy in Miles Per Gallon and…
A: C is a procedural and general-purpose programming language that can provide level access to system…
Q: Which part of the DBMS is in charge of making sure that concurrency is handled correctly?
A: The part of the DBMS that is responsible for ensuring that concurrency is handled correctly is known…
Step by step
Solved in 3 steps

- 1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as:Simplify the Boolean function F (W, X, Y, Z) wxy + xz + wx'z + w'xExpand to an unsimplified Boolean Function: F= D + AB'C + A'D
- Write a boolean function in sum-of-products form for the following. F(X, Y, Z) is true when exactly one of the following is true: a) X is true b) Y is false and Z is trueDraw a perceptron to simulate the following boolean function: f(x,y,z)= x'.y + x.y.zConsider a boolean function with input a, b, c, and d. The value of the inputs can be defined as V = 8*a + 4*b + 2*c + d. The output of this function is true if V mod 4 is 1 or 2 or 3.
- If A is a Boolean variable then A+0 is equivalent to ____________. a. 1 b. A' c. A d. 0The Boolean function ?(?, ?, ?, ?) = ∑ ? (0,5, 7, 8, 9,11). Simplify the function using appropriatelaws and Rules of Boolean AlgebraGiven a Boolean expression: Y = A.B + (A.B.(A+B)) Find the value of Y in the case when A= 0 and B= 1.
- What are the three methods we can use to express the logical behavior of Boolean functions?In Boolean manipulation, show how the product of sum of this Boolean algebra: (X’+Y’)’ + (X'+Y)(X+Y')Z is = (X+Y+Z)(X+Y'+Z)(X+Y'+Z')(X'+Y+Z)(X'+Y+Z')Find the truth table T = T(E) for the Boolean expression E = E(x,y,z) where: i. E = xy + x'z; ii. E = xyz' + y + xy'.

