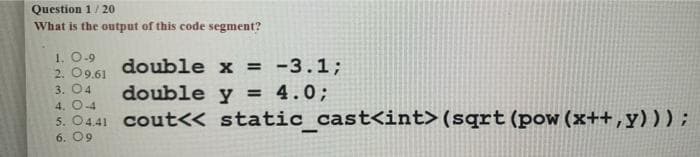
Question 1/20 What is the output of this code segment? 1. 0-9 2. 09.61 3. 04 double double 4. 0-4 5. 04.41 cout<< 6.09 x = -3.1; y = 4.0; static_cast (sqrt (pow (x++, y)));
Q: At each and every step of development, the inputs and outputs of a software system need to be…
A: Introduction: Designing the input: The input is the unprocessed data that is used to create the…
Q: Why do some individuals do this, and how does it work? IP spoofing: Is it a security risk?
A: Given To know about the IP spoofing and it's work.
Q: Write a function definition named first_and_second that takes in sequence and returns the first and…
A: python function to find first and second element in the list
Q: How do you guarantee that each machine employs its own private key pair while utilizing IPsec?
A: Introduction: IPSec protects and authenticates IP traffic between PIX Firewalls, Cisco routers,…
Q: The legal ramifications of employee mobile phone usage should be a worry for companies.
A: Legal Ramification: In its broadest meaning, the concept of a legal ramification is not very…
Q: Identify a crucial person of your team in system development. With the help of proper…
A: introduction: When done correctly, team development has the potential to cultivate an imaginative…
Q: Describe the role that firewalls play in ensuring the safety of your company. What are the benefits…
A: Encryption: The pros and downsides of using hardware and software firewalls, software tools, and the…
Q: 6 Consider converting the following NFA to an equivalent DFA. 0 90 91 1 a The number of states in…
A:
Q: In your perspective, which stage in the process of developing software is the most important, and…
A: Please find the detailed answer in the following steps.
Q: Does the word "privacy" have an agreed-upon meaning in common usage? Here are five things you can…
A: Introduction What does it mean to be private? Is it possible for you to safeguard your private data?…
Q: When you send someone an InDesign file, you should... O be sure to send all linked graphics and…
A: Answer: When you send someone an InDesign file, be sure to send all the linked graphics and required…
Q: Web page content can include O text O images audio & video all of the above
A:
Q: What are the three advantages of using an incremental development approach as opposed to a waterfall…
A: Required: What are the three benefits of incremental development versus waterfall development?…
Q: What, in a nutshell, could one expect to achieve via the practise of software engineering? Who or…
A: Start: Yes, software engineering has a primary goal that can be summarized.
Q: which is transmitted over the channel. Let T(w) denote the re word.
A: The answer is
Q: How employees who are not linked to the internet may nonetheless make direct use of the system
A: Given: With the evolution of technology, an increasing number of businesses are turning to kiosk…
Q: I have 3 images, each one is 8x10 inches but all have different resolutions. Which one is the better…
A: Please find the detailed answer in the following steps.
Q: In order to minimise the risk of injury when using a cell phone, what preventative actions and…
A: Clarification: The world has become very reliant on fantastic cell phone technology. Although we may…
Q: You may learn more about credit card security by browsing the Internet.
A: According to the information given:- We have to define credit card security by browsing the Internet
Q: Bar charts are less confusing than pie charts and should be your first choice when creating a…
A: let us see the answer:- Introduction:- The correct answer is true.
Q: How does IP spoofing operate, and what is it? IP spoofing is technically a security problem,…
A: IP address is spoofing is the act of altering the Source IP header with arbitrary values, generally…
Q: Describe the role that firewalls play in ensuring the safety of your company. What are the benefits…
A: Introduction: The merits and downsides of hardware and software firewalls, software tools, and how…
Q: Where exactly can you get information that you can trust on the internet
A: Introduction Sorts of sources Essential, auxiliary, and tertiary sources are the three different…
Q: What are some of the most popular tools that are utilized in the creation of mobile applications
A: let us see the answer:- Introduction:- Choosing a technology for developing mobile apps is more of a…
Q: Does Windows 10 have anything else on your mind?
A: Windows: Windows 10 is a new operating system from Microsoft. Microsoft's Windows 10 operating…
Q: Write a program using an array that accepts five input values from the keyboard. Then it should also…
A: The program is written in C. Check the program screenshot for the correct indentation. Please check…
Q: It is essential to have an understanding of the function of firewalls in order to ensure the safety…
A: The significance of a firewall: First, let us consider why we need a firewall. I have a pc that…
Q: b. Describe how to use a balanced BST to implement both operations in O(log n) time. Discuss why…
A: Please check the step 2 for solution
Q: At each step of development, the inputs and outputs of a software system must be thoroughly…
A: Introduction: Input is raw data processed to generate output. Input design must consider PC, MICR,…
Q: Keep an eye on the major tools and procedures that will be employed in the system development…
A: System development process: The system development life cycle includes conception, analysis, design,…
Q: b. Describe how to use a balanced BST to implement both operations in O(log n) time. Discuss why…
A: Please check the step 2 for solution
Q: 2.26 LAB: Expression for calories burned during workout The following equation estimates the average…
A: I have provided JAVA CODE along with CODE SCREENSHOT and also provided 2 OUTPUT…
Q: w does knowledge management impact organizational processes?
A: Knowledge administration is the alert process of defining, constitute, maintaining, and giving the…
Q: It may be difficult to detect malware "in the network."
A: Given: Malware is a file or a piece of code that is frequently sent across a network. It is used by…
Q: X(z)= E-ZE+z_22+1_Z+ZE+₂ZZ+Z+1 Z-1
A: For Power we use ** in Python , for example 2**3 = 8 Code :- z = int(input("Enter value of z :"))…
Q: When a project is concluded, it is important to determine what documentation the developer needs to…
A: Launch: Determine which documents the developer should get at the end of the project. When it comes…
Q: The metrics for static testing and route testing are broken out in further depth in the next part,…
A: Static and route tests: Code-free or based static testing is possible. Code, requirement…
Q: Be sure that you are well-versed on the major tools and procedures that will be used during the…
A: Introduction: The system development life cycle includes conception, analysis, design,…
Q: Using MySQL, create a single Structured Query Language (SQL) script that answers all the below…
A: creating Horse table
Q: If you're a software developer, imagine that you've been hired to construct a hospital's…
A: Given: Healthcare management systems aim to speed up hospital procedures. A hospital management…
Q: What are the benefits of prototyping when it comes to the creation of a new system?
A: Launch: System Analysts are the only ones who are given the task of prototyping, and it is their…
Q: Area plots are unstacked by default. Select one: O True O False
A: answer is
Q: What are some of the most popular tools that are utilized in the creation of mobile applications?
A: Consider the following factors while developing an app: Always verify that software resolves a…
Q: Distinguish between DOS and Windows 98, two of the most popular operating systems of the 1990s, by…
A: Operating systems: Operating systems include DOS and Windows. Windows is a multi-tasking,…
Q: Please go into as much detail as you think is required on the differences between the three most…
A: Windows is a gathering of a few exclusive graphical working framework families created and showcased…
Q: Give an explanation on the relevance of firewalls in terms of the privacy and protection offered by…
A: Introduction: In response to the inquiry, we must discuss the significance of network scanning and…
Q: How can you tell the difference between information that is genuine and information that is fake…
A: What Actually is Fake News? Fake news is any article or video containing false data camouflaged as a…
Q: 1. Given two numbers X and Y. Write a program to determine the difference between X and Y. If X - Y…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: What is keybord
A: Introduction The keyboard is perhaps one of the most crucial components of a computer.
Q: The way a Windows Service is configured differs from the way a typical application is.
A: Introduction: A user-initiated programme is referred to as a "standard" or "regular" programme in…
Step by step
Solved in 2 steps with 2 images

- AWS Lambda Function-Python programming Using boto3 library, please give a code that can delete an elastic load balancer with no instance attached to the elastic load balancer Provide code/screenshotYou are a product manager and currently leading a team to develop a new product. Unfortunately, the latest version of your product fails the quality check. Since each version is developed based on the previous version, all the versions after a bad version are also bad. Suppose you have n versions [1, 2, ..., n] and you want to find out the first bad one, which causes all the following ones to be bad. given is an API bool isBadVersion(version) which returns whether version is bad. Implement a function to find the first bad version. You should minimize the number of calls to the API. please write code in pythonConsider the following code chunk:x <- 0while(x < 4) {x <- sample(1:3, 1)print(x)}It is not a good idea to run these lines because...a) x is an invalid argument to print().b) the condition x < 4 is never violated.c) the function sample() does not exist.d) x is initialised with the wrong type.
- extern "C" int f(int *,int,int); int a[2][2] = {{11,12},{21,22}}; void setup(){ Serial.begin(115200); while(!Serial); delay(500); int *arr = (int*)a; Serial.println(f(arr,2,2)); } void loop(){ } .global f f: ldr r3,[r0] // get first element mov r2,#0add r2,r3 mov r1, #3 lp: add r0,#4 // add next elementldr r3,[r0]add r2,r3sub r1,#1 bgt lp mov r0,r2 bx lr Describe what operation is being performed in this codeConsidering the following code fragment, what is the output? int **p = new int*[5];for(int i=0; i< 5; i++){ p[i] = new int[5];}p[0][0] = 96;p[0][1] = 97;p[0][2] = 98;cout << *((*p)+1) << endl; Group of answer choices 96 97 98 Segmentation Fault ================== Which of the following would correctly output the third slot in a dynamic, single dimensional array of integers named numbers? Group of answer choices cout << *(numbers+2); cout << *numbers+2; cout << *(numbers)+2; None of these =============== It is required to create a dynamic array that can store 10 integers. Which of the following will work? Group of answer choices int array=(int*) malloc(10*sizeof(int)); int* array=(int*) malloc(10*sizeof(int)); int array=(int) malloc(10*sizeof(int)); int* array=malloc(10*sizeof(int));Java 1. Need a list of 30 words, phrases and company names commonly found in phishing messages. Assign point value to each based on your estimate of its likelihood to be in a phishing message (e.g., one point if it's something likely, two points if modereratly, or three points if highly likely). Do an application that scans a file of text for these terms and phrases. For each occurance of a keyword or phrase within the text file, add the assigned point value to the total points for the number of occurences and the point total. Show the point total for the entire message. 3. Do a word file answering these questions:Does your program assign a high point total to some actual phishing e-mails you have received? Does it assign a high point total to some legitimate e-mails you have received?
- You have the following code fragment.LOOP: LD R1, 0(R2) ;load R1 from address 0+(R2) DADDI R1, R1, #1 ;R1 <– R1 + 1 SD R1, 0, (R2) ;store (R1) at address 0(R2) DADDI R2, R2, #4 ;R2 <– R2 + 4 DSUB R4, R3, R2 ;R4 <– R3 - R2 BNEZ R4, LOOP ;branch to LOOP if (R4) != 0Assume that the initial value of R3 is (R2)+20.What are the data dependencies in this code fragment?Using Dr-Racket, what is the purpose of the number function?(define (number n)(local [(define (abstract int)(* int 11))] (build-list n abstract))) A) Create a list of the first n multiples of 11 starting at 11. B) Create a list of the first n multiples of 11 starting at 0. C) Create a list of the first n multiples of 11 starting at 1. D) Create a list of the first 11 multiples of n starting at 1. E) Create a list of the first 11 multiples of n starting at 0.F) Create a list of the first 11 multiples of n starting at n.Write the C equivalent “train” function #void train(int*A, int*B, int*C, int k) train: add $t4, $0, $0bus: add $t5, $t4, $a1 lw $t6, 0($t5) add $t5, $t4, $a2 lw $t7, 0($t5) add $t6, $t6, $t7 add $t5, $t4, $a0 sw $t6, 0($t5) addi $t4, $t4, 4 slt $t5, $t4, a3 bne $t5, $0, bus jr ra
- The following code must be written in python for this HW assignment. I will provide a skeleten for the code and you must write some lines of code to satisfy the objective of the prorgram. You will develop a web server that handles one HTTP request at a time. Your web server should acceptand parse the HTTP request, get the requested file from the server’s file system, create an HTTP responsemessage consisting of the requested file preceded by header lines, and then send the response directly tothe client. If the requested file is not present in the server, the server should send an HTTP “404 NotFound” message back to the client. Put an HTML file (e.g., HelloWorld.html) in the same directory that the server is in. Run the serverprogram. Determine the IP address of the host that is running the server (e.g., 128.238.251.26). Fromanother host, open a browser and provide the corresponding URL. For example:http://128.238.251.26:6789/HelloWorld.html‘HelloWorld.html’ is the name of the file you…4) Answer the question in C++ A) What is wrong with the following code segment? enum CarType {GM, FORD, BMW}; int main() { CartType = BMW; return 0; } B) Assume that the addresses of x and y is 0x61feb8 and 0x61feb0, respectively. What will be the values of x, y, p, and q, respectively, when the following code runs successfully? int main() { int x; double y; int* p = &x; double* q = &y; *p = 3; *q = 3.14; increaseByOne(p, q); cout << x << " " << y << endl; cout << p << " " << q << endl; return 0; }void increaseByOne(int*& p1, double* q1){ (*p1)++; (*q1)++; p1++; q1++;} The four value:1. Build a web crawler function that starts with a URL representing a topic (a sport, your favorite film, a celebrity, a political issue, etc.) and outputs a list of at least 15 relevant URLs. The URLs can be pages within the original domain but should have a few outside the original domain.











