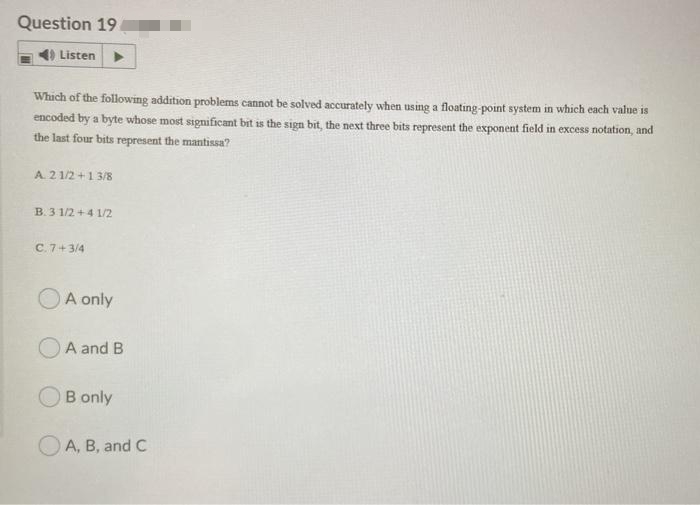
Question 19 Listen Which of the following addition problems cannot be solved accurately when using a floating-point system in which each value is encoded by a byte whose most significant bit is the sign bit, the next three bits represent the exponent field in excess notation, and the last four bits represent the mantissa? A. 21/2+1 3/8 B. 31/2+4 1/2 C. 7+3/4 A only A and B B only A, B, and C
Q: Question 2 Mary Blake is the Country Manager in Trinidad and Tobago for FEDEX International with…
A: One of the most important soft skills in the professional world is good communication. It comes with…
Q: Is it necessary to run a simulation on a computer in order for it to have any value? Explain.
A: The management can use simulation to measure and monitor the system's behaviour. Whether the system…
Q: It is conceivable that poor management of the software project that was responsible for the…
A: Warning (1) The City of Denver hired Breier Neidle Patrone Associates to determine if the projected…
Q: Discuss any four user-initiated activities that a graphical user interface allows (GUI)
A: Introduction: Visually Complex Presentation The visual show is the interface's visual component. It…
Q: What is the value of num3 after the following code is executed: int num1; int num2; int num3; num1 =…
A: value of num1 is 15.
Q: Is it possible to describe how a computer operates using this method? After that, we'll most likely…
A: Introduction: The elements of input, storage, processing, and output are all necessary for a…
Q: Process modelling is useful for more than just IT system development.Is logical process modelling…
A: Introduction: The method of process modelling is used to identify and define processes. It links and…
Q: 1] I need an operand and description of these JC, JNC, JZ, JNZ, JP conditions.
A: The operand and description of above JC, JNC, JZ, JNZ, JP conditions are given below step
Q: in Digital Signal Processing 1. Simple words for the difference between TIME DOMAIN and FREQUENCY…
A: Here we have given the differences between time domain and frequency domain. we have given a brief…
Q: Java compiler decides whether a method can be called by the type, not the type. superclass, subclass…
A: The above question is solved in step 2 :-
Q: Discuss the pros and cons of net neutrality? What is your personal opinion on this matter??
A: Answer: Net neutrality: it state that internet services provider provide internet equally and net…
Q: - For the given IP address 196.62.146.174/25, answer the following questions: Subnet Mask Number of…
A: The answer is..
Q: Assume that, at the '4361 software company, the Unix operating system is in use, and the company…
A: risk: There is major risk of the company 's documents, files if the file is not protected in a…
Q: 1-How can the CPU recognize the device requesting an interrupt? 2-Since different devices are likely…
A: 1-How can the CPU recognize the device requesting an interrupt? 2-Since different devices are likely…
Q: In the statement below, "Xyzzy" is a/an ... public class Foo extends Bar implements Xyzzy { } ...
A: In the statement below, "Xyzzy" is /an ... public class Foo extends Bar implements Xyzzy{ ... } It…
Q: Explain the instruction (fliplr) with example? Your answer
A: The answer is given in the below step
Q: Show all the steps of derivation of the expression aab* a* (b + ab01), by using the production rules…
A: CFG- context free grammar, it is to generate possible string pattern in formal language. where G is…
Q: When the program is run, a file whose full path will be given in the code should be read and the…
A: Program: #include <iostream>#include <fstream>#include <string>using namespace…
Q: Briefly describe and explain what virtual memory in computing means.
A: SOLUTION: Virtual memory is an operating system feature that allows a computer to compensate for…
Q: Determine the ways in which advancements in technology have made it simpler for individuals to evade…
A: Introduction: In many respects, technology lowers societal standards. It makes it simpler for people…
Q: The following table gives the return from 3 activities when 0,1,2,3,4 dollars are invested in each…
A:
Q: Find a piece of writing that describes how to use technologies that don't need you to use your hands…
A: The following states have passed legislation that makes it illegal for drivers to use hand-held…
Q: What factors have an impact on network communication performance?
A: Introduction: Network communication, also known as internetworking, is a collection of protocols…
Q: What exactly is a wireless infrastructure network? Aside from infrastructure, what else does the…
A: Introduction: The term "infrastructure-based network" refers to a wireless network that requires the…
Q: What makes up a computer's visual system?
A: Introduction: Computer vision is a branch of artificial intelligence that studies how computers may…
Q: 3. Let the "Tribonacci sequence" be defined by T₁ = T₂ = T₁=1 and T₁ = T₁+T2+T-3 for n ≥4. Prove…
A: A Tribonacci sequence or series is a sequence of integers such that each term from the fourth onward…
Q: What does cloud security utilizing identity and access management (IAM) and the shared…
A: Cloud technology we are using the virtual space and the internet. Some persons thinks that cloud is…
Q: PROBLEM 4 The Pee Tool Shop has four heavy presses it uses to stamp out prefabricated metal covers…
A: Machine time in minutes Product 1 2 3 4 1 35 41 34 39 2 40 36 32 43 3 38 37 33 40…
Q: The methods of software modelling and software development are separate.Describe how each individual…
A: Introduction: A Software Development Methodology
Q: Do you understand why authentication is so critical? What are the advantages and disadvantages of…
A: Introduction: Servers utilise confirmation when they need to know who is accessing their information…
Q: What do you believe were the effects of the early discoveries that led to the creation of the…
A: We need to talk about the impacts of early inventions on our lives today.
Q: C++ input n, output: 1 12 123 .... 123....n example: n = 3 1 12 123 n= 5 1 12 123…
A: Loop: We can run a set of statements or a statement repeatedly by using a loop statement. For eg:…
Q: What are your opinions on the topic of whether or not social media sites such as Facebook ought to…
A: Facebook: College organizations and policing use Facebook, an online entertainment stage, as a…
Q: What is the relationship between cohesion and coupling in software design and development?
A: Introduction: When an agency creates a software artefact, it outlines how it will achieve goals by…
Q: MCQ3102: The physical layer is concerned with the movement of which of the following over the…
A: This mcq is related to physical layers.
Q: What does a TRC query mean? More precisely, what is the set of answer tuples for a given TRC query?…
A: The question has been answered in step2
Q: Find out how individuals react when they encounter problems with the programmes or applications that…
A: Introduction: When software isn't updated, users grow frustrated. Overcrowded apps will frustrate…
Q: IP Subnetting For the given IP address 196.62.146.174/25, answer the following questions: a. Subnet…
A: For the given IP address 196.62.146.174/25, answer the following questions: Subnet Mask Number of…
Q: 1] I need an operand and description of these JC, JNC, JZ, JNZ, JP conditions.
A: The operand and description of above JC, JNC, JZ, JNZ, JP conditions are given below step
Q: What is the definition of routing? Describe in detail the main components of a router and the…
A: Introduction: Routing: Routing is simply the act of finding a path across several networks, which…
Q: Do the regulations that are already in place provide sufficient safeguards to prevent children less…
A: Introduction: The restrictions are in place for a reason: they safeguard your company, its workers,…
Q: What is the size of my adder and subtractor if I want a maximum output of 6-bits? DRAW A DIAGRAM
A: For a 6 bit output we need 3 adder and 3 subtractor
Q: It is discussed in great length but also its impa cyberbullying the problem.
A: Introduction: Cyberbullying can happen online through social media, forums, or gaming where users…
Q: write a python function that finds the average of that column. The lists will contain None values…
A: Python Code: # function to find mean of lists def f_mean(dlist): m_list = [] l_list =…
Q: Which of the following statements is correct about the MD5 value used with evidence file…
A: The correct answer for the above question is given in the below steps
Q: Determine data access security principles. In terms of network programming
A: Introduction: The three basic concepts of network security are confidentiality, integrity, and…
Q: The ability to demonstrate the four P's is essential for good management of software projects.
A: Project 1: PERSONNEL, PRODUCT, PROCESS, PEOPLE, PEOPLEThe most important factor in managing software…
Q: What is Virtua l-8086? Mode-matching is the process of matching a method call to the proper method.
A: The technique of matching a method call with the appropriate method is called mode-matching.
Q: Do the following without using a cal- culator or a computer, but check your answers with a…
A: Logic : We require a certain amount of bits that can carry at least 1026 in order to represent the…
Q: One of the most significant things to explore when discussing data transmission is how the width or…
A: Introduction: According to the information given:- We have to define the data transmission and the…
19
Step by step
Solved in 2 steps

- Question 23 options: Using the rules of the simple floating point model (1-bit sign, 5-bit biased exponent, 8-bit significand, and normalized such that the leftmost bit of the significand is always 1), the number 8.4375 (decimal) can be expressed as: (Do not use spaces or any English text. Provide only 14 bits.)4, in the fixed-point machine, the following statement is wrong ( ).A. In addition to the complement, the original code and the inverted code cannot indicate that the original code of −1 B. +0 is not equal to −0C. the inverse of +0 is not equal to the negative of −0 D. For the same machine word length, the complement code can represent a negative number more than the original code and the inverted code.Show Steps Please 21. Suppose we want an error-correcting code that will allow all single-bit errors to be corrected for memory words of length 10. a) How many parity bits are necessary? b) Assuming we are using the Hamming algorithm presented in this chapter to design our error-correcting code, find the code word to represent the 10-bit information word: 1001100110. 22. Using the CRC polynomial 1101, compute the CRC code word for the information word, 01001101. Check the division performed at the receiver.
- Let a = 1.0 × 29 , b = −1.0 × 29 and c = 1.0 × 21 . Using thesimple floating-point model described in the text (therepresentation uses a 14-bit format, 5 bits for the exponent with abias of 15, a normalized mantissa of 8 bits, and a single sign bit forthe number), perform the following calculations, paying closeattention to the order of operations. What can you say about thealgebraic properties of floating-point arithmetic in our finitemodel? Do you think this algebraic anomaly holds undermultiplication as well as addition?1. b + (a + c) =2. (b + a) + c =This problem covers floating-point IEEE format.(a) Assuming single precision IEEE 754 format, what is the binary pattern for decimal number -6.16?(b) Assuming single precision IEEE 754 format, what decimal number is represented by this word:0 01111100 01100000000000000000000(Hint: remember to use the biased form of the exponent.)Show Steps Please 21. Suppose we want an error-correcting code that will allow all single-bit errors to be correctedfor memory words of length 10. a) How many parity bits are necessary? b) Assuming we are using the Hamming algorithm presented in this chapter to design ourerror-correcting code, find the code word to represent the 10-bit information word:1001100110.
- Please use C++ to solve the listed problems in one code 1). Decrypt the following: “DY CVOOZ ZOBMRKXMO DY NBOKW” 2). Convert 890 to base 9. 3). Determine if the bits of 1100010 is correct or not by using Hamming Code Detection method. If not, detect which bit is incorrect and print out the decimal format of the message that was sent after the correction 4). Universal Set: [A, B, C, D, E, F, G, H, I, J, K, L, M, N, O, P, Q, R, S, T] Set A: [A, B, C, E, H, M] Set B: [A, C, E, G, I, K, M, O, Q, S] Set C: [A, B, C, E, G, K, M, Q, S] Please print out: ((A Union B) Intersect C) 5). Present a Truth Table for the following statement: !(A XOR B) NAND (A OR C) Please provide the code and a screenshot of outputIt is necessary to formulate the Hamming code for four data bits, D3, D5, D6, and D7, together with three parity bits, P1, P2, and P4.1. Evaluate the 7-bit composite code word for the data word 0010.2. Evaluate three check bits, C4, C2, and C1, assuming no error.3. Assume an error in bit D5 during writing into memory. Show how the error in the bit is detected and corrected.4. Add parity bit P8 to include double-error detection in the code. Assume that errors occurred in bits P2 and D5. Show how the double error is detected.(Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at memory address 159, determine the addresses corresponding to each variable declared in the following statements. Also, fill in the correct number of bytes with the initialization data included in the declaration statements. (Use letters for the characters, not the computer codes that would actually be stored.) floatrate; charch1=M,ch2=E,ch3=L,ch4=T; doubletaxes; intnum,count=0; b. Repeat Exercise 9a, but substitute the actual byte patterns that a computer using the ASCII code would use to store characters in the variables ch1, ch2, ch3, and ch4. (Hint: Use Appendix B.)
- For this question, mark all answers that apply: Assume any float or int is stored in 32 bits and float arithmetic is as specified by the IEEE 754 standard for single-precision. Which of the following statements about floating point arithmetic are true? 1) Catastrophic cancellation can cause loss of accuracy in floating-point multiplication 2) If all values are normal and within range (a+b) must equal (b+a) 3) If all values are normal and within range, (a*b) must equal (b*a) 4) A too-large value can be represented as infinity 5) NaN can be used to indicate that a result is not a valid floating-point number. ( Please do fast i have one hour)7) Do the following conversion problems correctly:(a) Convert decimal 27.315 to binary.(b) Calculate the binary equivalent of 2/3 out to eight places. Then convertfrom binary to decimal. How close is the result to 2/3?(c) Convert the binary result in (b) into hexadecimal. Then convert the resultto decimal. Is the answer the same?You are asked to design a 16-bit floating point number system to store the lengths of various man-made objects. This system should work in a similar way as the IEEE754 standard. Assume a value stored in the system denotes the length of an object in centimeters, assume also that the maximum length to be stored is 45845.0 centimeters (i.e. length of the biggest man-made oil-tanker, the “Seawise Giant”). Note: This representation has normalized, de-normalized and special cases as you have seen in IEEE754 standard. Answer the questions below: a) Is sign bit needed in this system? Why yes or why not. b) What is the minimum number of bits needed for the exponent? What is the value of the corresponding bias? Show your steps clearly. If you write the values directly without showing the steps, you will not get any point. c) What is the maximum length the system can represent? Please show your steps clearly, otherwise no point will be given.

