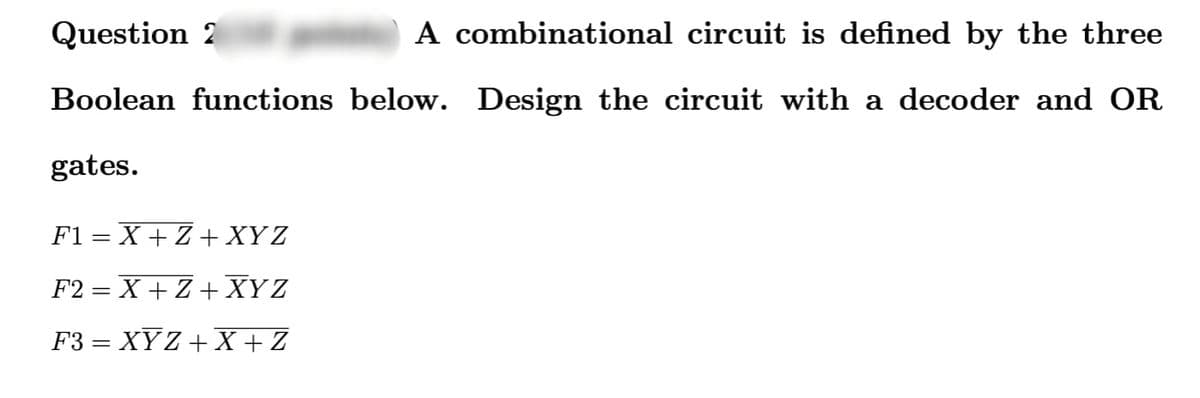
Question 2 A combinational circuit is defined by the three Boolean functions below. Design the circuit with decoder and OR gates. F1=X+Z+ XYZ F2=X+Z+XYZ F3 = XYZ+X+Z
Q: Protocols that are implemented in order to facilitate data transmission. The difficulties that arise…
A: Given: Point-to-point communication is managed, established, and closed via transport layer…
Q: In what ways has the layer 2 protocol for routers been shown to be susceptible to vulnerabilities?…
A: Given: On OSI layer 2, which is the data link layer, the router switches the connection. In general,…
Q: How does object-oriented programming (OOP) function? Object-oriented programming (OOP) may be…
A: An object-oriented Programming, or OOP, is a way of solving problems where all calculations are done…
Q: What are some of the most notable differences that can be observed between the operating systems…
A: Given: A mainframe operating system is network software that runs applications, connects devices,…
Q: To what extent does MVC architecture play a role in designing internet applications? A number of…
A: Introduction: MVC keeps the business logic layer and the show layer separate from each other. It was…
Q: Why does the Internet run on TCP rather than the less dependable UDP when it comes to protocols like…
A: Given: The application data must be received in whole, without any gaps, and in the right sequence…
Q: Please offer a non-technical example of identity, authentication, and authorisation to demonstrate…
A: Intro According to the information given:- We have to define non-technical examples of…
Q: Q3: What is the address field of an indexed addressing mode instruction in order to make it the same…
A: The Answer is in step2
Q: What type of possible error messages you can get whe
A: The answer is
Q: * Q1: For a system that connects 33 CPU registers with an ALU which has 35 operations, the possible…
A: Consider the following diagram 8-2, where 7 sign up as well as a local recorder and ALU. The output…
Q: What precisely does it imply when people talk about a race when they're referring to the typical…
A: The following is an answer to the provided question: A race situation is a synchronisation mishap…
Q: Why is it required to read two sorted lists at the same time when merging them using a binary search…
A: Introduction: Binary search is one of the data structures and using this binary search we can…
Q: How helpful is it to have a standardised user interface while designing the system of systems…
A: In the interface design of SoS, a unified user interface is advantageous: The Benefits of a Communal…
Q: Design the address encoder for the followings: 1) IN AL, 68H
A: URL Encoding (Percent Encoding) URL encoding changes over characters into a configuration that can…
Q: What is cout in c++ programming? give handwritten answer
A: Given that we have to give the definition of term cout in c++ language.
Q: When it comes to interacting through computer, why is it so important to make use of a variety of…
A: Given: Protocols are needed so recipients can understand senders. Protocols in computer…
Q: What type of communication takes place inside the bounds of a wireless local area network?
A: Intro Wireless local area networks make use of technologies like as radio and spread spectrum. These…
Q: What are the key differences between the services that are provided by software components and the…
A: Given: The issue that was just posed is concerned with the distinctions between software components…
Q: How exactly might Model-View-Controller help to organise web applications? What are some of the ways…
A: Given: What role does MVC play in the organisation of web applications? What are the advantages of…
Q: "Discovery" and "integration" are all terms used to describe the process of finding new information.…
A: Given: The Internet Engineering Task Force created UDDI, an XML-based standard for publishing,…
Q: Is it true that traffic control on the internet is assigned to a single central distribution centre?…
A: answer is
Q: Which of the following individuals is considered to be a forerunner in the creation of the mainframe…
A: It was during this time that the first mainframe computer was developed: The term "mainframe…
Q: When it comes to operating systems for the desktop, what precisely are they? Comparing Windows, Mac,…
A: Given: What are desktop operating systems? Answer: The desktop operating system is at the core of…
Q: Question 2: A. Read the 16 bit data stored in an input device that has port number FF00H and store…
A: Answer is given below-
Q: The open systems interconnection (OSI) paradigm is made up of seven layers. Inquiring minds want to…
A: Given: It acts as a window between users for utilizing applications like browser. Presentation…
Q: . Write a java program that receives a positive integer n (n >= 1) from the user and computes the…
A: To write java code to receives an integer from the user and computes 1 + 1/2 + 1/3 + 1/4 + ... + 1/n
Q: Take note of any key linkages that may exist between the cloud and mobile devices. What are the…
A: Intro Cloud computing is a method which is delivering computing services like servers, storage,…
Q: Q-1. Consider the Map Coloring Problem described below: Map Coloring Problem The following map is to…
A: def hillclimbing(objective, bounds, n_iterations, step_size): # generate an initial point…
Q: A TV channel has a bandwidth of 6 MHz. If we send a digital signal using one channel, what is the…
A: Answer: Given Bandwidth(B) =6MHz
Q: Your computer may be shielded from any threats coming from the outside world if you have a firewall…
A: Answer 1) many times yes. because if we have installed firewall , so protected against outside…
Q: How does object-oriented programming (OOP) function? Object-oriented programming (OOP) may be…
A: Given: Visual Basic is an object-oriented language. Visual Basic . NET supports Abstraction,…
Q: What are the functions of a desktop OS?
A: An operating system's primary function is to mediate communication between the software and hardware…
Q: What are the features that differentiate time-sharing systems and distributed operating systems from…
A: Given: Stand-alone operating systems are ones that can run on a desktop computer or another portable…
Q: What exactly is meant when someone makes a reference to DHCP, also known as the dynamic host…
A: The above question is solved in step 2 :-
Q: What are the three Windows security settings that should be checked regularly?
A: Windows Security is your home to manage the tools that protect device and data is virus and threat…
Q: Both the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) are core protocols…
A: Definitions: Once a connection is established, TCP allows two-way data transmission. TCP features…
Q: When migrating from on-premises servers to an laaS-based architecture, what are some of the…
A: Challenges Absence of abilities and information. Numerous DevOps and cloud designing groups "assume…
Q: In Python, Use num.txt file (below). create a program that opens num.txt, a file consisting of a…
A: I give the code in Python along with line by line explanation and also provide the output and code…
Q: Why are watchdog clocks necessary in so many of the embedded devices that we use today? Embedded…
A: Given: Why do embedded systems require watchdog clocks? WDT is a simple embedded system component.It…
Q: Teams that collaborate across functional boundaries carry out the task simultaneously (those that…
A: Given: Covid-19, which launched in 2020, has two impacts on workers. On one side, physicians and…
Q: When should a network update be scheduled, and how long should it last?
A: Intro Modern technologies make business faster and smarter than ever before. Clouds and mobility…
Q: What is the output of the following code: bool w=false; int x=10; while (!w) { X+=10; if (x=60)…
A: The given code in C++ is : bool w=false; int x=10; while(!w){ x+=10; if(x<=30)…
Q: What distinguishes a quantum computer from a regular computer are its defining characteristics? In…
A: The primary distinction compared to a traditional computer: The age of binary computers, which…
Q: In what respects is the configuration and installation of a firewall a must-do precaution?
A: Intro It evaluates whether to allow or reject a certain kind of communication to enter or exit the…
Q: Give a comprehensive breakdown of how the Domain Name System (DNS) works, including explanations of…
A: Domain Name System. The domain name system, or DNS, is a telephone directory for the Internet. This…
Q: What precisely does the phrase "quantum computing" refer to, and how does the corresponding process…
A: AT THE QUANTUM LEVEL COMPUTING: Quantum computing is a kind of computer that uses an item's quantum…
Q: Let's say that in addition to being a component of the primary key, an attribute is also a candidate…
A: Given: What do you respond if someone suggests that an attribute which is a component of a composite…
Q: What type of possible error messages you can get when you try to login with the s
A: The answer is
Q: An individual is using a computer with the IP address 10.0.0.5 to carry out their job on a local…
A: UDP: UDP (User Datagram Protocol) is a common communications protocol used to send data between…
Q: What are the most important distinctions between asynchronous, synchronous, and isochronous…
A: Connection that is Asynchronous: During communication, information is sent along from one end to the…
Q2
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

- 5. Design an appropriate combinational circuit that implements a digital system with the following output functions: ROR, SHL, AND, XOR, ADD, DIV, SUB, MOV using a decoder. 6. Design the circuit diagram and truth table for the Boolean expression : F = (A’B) + (C’B).draw a QPSK demodulator circuit using different circuit components. stop rejecting questionsCreate a own comibinational circuit that has real world application. identify its function and create the truth table.
- Construct the state table for the circuit3) Derive the state table and the state diagram of the sequential circuit shownbelow and explain the function that the circuit performs correctly.A majority circuit is a combinational circuit whose output is equal to 1 if the input variables have more 1’s than 0’s. The output is 0 otherwise.1. (a) Design a three-input majority circuit by finding the circuit’s truth table, Boolean equation, and a logic diagram.2. (b) Write and verify a HDL gate-level model of the circuit.
- "Design a combinational circuit defined by the Boolean function F(X,Y,Z) = (X'+Y)(X'+Z')(X'+Y'+Z), using a decoder and external gate/s. In order to implement this, the size of the decoder should be and we need to include and external gate."QUESTION 3: Drive the Boolean expression for the given circuitTruth Table A B X 0 0 0 0 1 0 1 0 1 1 1 1 Reconstruct the circuit above using only NAND gates. Include Boolean algebra, truth tables, and logic diagrams for the circuit reconstructed with only NAND gates. 3-1) Boolean algebra expression Draw the reconstructed circuit and logic diagram here (only NAND gates)
- Design a combinational circuit with three inputs, x , y , and z , and three outputs, A, B, and C . When the binary input is 0, 1, 2, or 3, the binary output is two greater than the input. When the binary input is 4, 5, 6, or 7, the binary output is two less than the input.Draw the logic diagram of the digital circuit specified by the following Verilog description:Design a circuit using the following criteria. Show that a digital circuit can be simplified to a circuit consisting of three NOT gates, two 2-input AND gate and one 2-input OR gate.

