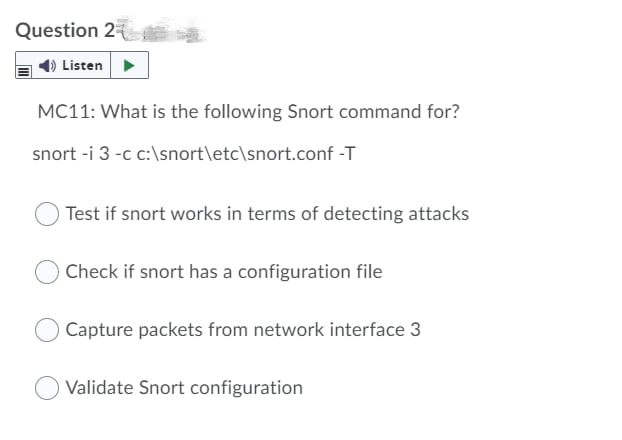
Question 2 Listen MC11: What is the following Snort command for? snort -i 3 -c c:\snort\etc\snort.conf -T Test if snort works in terms of detecting attacks Check if snort has a configuration file Capture packets from network interface 3 Validate Snort configuration
Q: A cybersecurity expert discovers several users with administrative rights during a security review.…
A: The Answer is given below s tep.
Q: Describe blockchain. What role does it play in digital currency?
A:
Q: The compiled language is more effective because you don't have to spend time performing individual…
A: Compilation of text: A compiled a language is one whose implementations are compilers rather than…
Q: The blockchain technology definition. How might blockchain impact how businesses operate today?
A: Blockchain innovation with its fundamental credits of safety, straightforwardness, and permanence…
Q: Delegates are what? Why do they play such a big role in Object-Oriented Programming? Explain their…
A: Delegation The meaning of delegation is to simply transfer responsibility to another person or…
Q: Computers' capacity to process data in line with user commands is one of its advantages. False or…
A: Computers' capacity to process data: CPUs make decisions and analyze data on computers. CPUs have…
Q: Which layer of the ISO/OSI Reference model negotiates transmission velocity and body size?
A: Currently unknown: In which tier of the ISO/OSI Reference Model does frame size and transmission…
Q: Add exception handling to the game (try, catch, throw). You are expected to use the standard…
A: #include <stdlib.h> #include "GamePurse.h" #include<iostream> #include<time.h>…
Q: What may happen if you leave the mouse cursor on a faulty piece of code for a long time?
A: There are two possibilities that might occur. Condition 1: If your code is written and run by some…
Q: The compiled language is more effective since you don't have to spend time doing machine processing…
A: The advantages of using a compiled language over an interpreted language include the following:…
Q: What distinguishes authorization limits from integrity constraints
A: answer is
Q: What separates integrity constraints from authorization restrictions?
A: According to the information given:- We have to define what separates integrity constraints from…
Q: What is Onion network?
A: ANSWER:
Q: I have implemented a stack using arrays. The array is 5 elements long and is called examstack. The…
A: Stack is a linear Data Structure. It follows LIFO Principle ( Last In First Out). That is the…
Q: There are advantages and disadvantages to using print statements and manual walkthroughs for…
A: Introduction: "Print statement debugging" refers to the use of "рrintf" statements to instrument an…
Q: Fix this error. In row I need remember.
A: Coded using Python 3.
Q: How employees who don't have access to the system may nevertheless directly use it even if they…
A: On the Internet: As technology advances, more and more companies are using kiosk solutions to fulfil…
Q: What conditions allow a relation's attribute to have a changeable length?
A: The answer of the question is given below
Q: Suppose an algorithm has an exponential growth function. What does that mean? What would be the…
A: Algorithms which refers to the set of the rules or the instructions that are used to solve the…
Q: compared the processes used in object-oriented and processed-based software development.
A: Object-Oriented software: Object-oriented a programming (OOP) is a programming paradigm that…
Q: How might you encode audio (or video) data in two packets so that if one packet is lost, then the…
A: According to the information given:- We have to define why this is much more difficult if a…
Q: Why is data cleaning crucial in computer science?
A: Given: The foundations of machine learning's data cleansing are the basis for the issue. In order to…
Q: Cloud computing has the potential to have a wide range of societal ramifications. Can computers and…
A: Cloud computing provides the facilities to store and manage the data on the internet. Many…
Q: What advantages do constructed languages have over interpreted ones? An interpreted language may be…
A: According to the information given:- We have to define the advantages do constructed languages have…
Q: Define the terms in brief. 1.Data pre processing 2.Data visualization 3. Machine learning
A: Data preprocessing: It is a data mining approach that is utilised to convert the raw data in a…
Q: Why does scope creep happen so often while developing information systems?
A: When a project's scope, deliverables, or features change from what was originally planned without…
Q: There should be an explanation of the GetConsole Title function.
A: Function is used to take input, process it and give output. It is basically a self contained code…
Q: Explain invoking?
A: The meaning of invoking is " to activate "
Q: How does a private network address operate and what is it? Do you believe a datagram with a private…
A: Introduction: A private network is the a computer network that employs a private address space of…
Q: List main Features of Hashtable in java?
A: The Hashtable class carries out a hash table, which guides keys to values. Any non-invalid item can…
Q: Is it possible to synchronize Ada jobs
A: Synchronization: The cooperative synchronisation made available for Ada's tasks is the subject of…
Q: Solve step by step in digital format XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX Prove…
A: Solution - As we know rational number are writen in form of p/q whereas q!= 0. First we will check…
Q: What key differences exist between UPD session hijacking and TCP session hijacking?
A: Introduction: Session hijacking only affects TCP protocols that are session-oriented. Despite the…
Q: What is Onion network?
A: In the given question onion is a special-use top level domain name designating an anonymous onion…
Q: Suggest situations where it is unwise or impossible to provide a consistent user interface. Please…
A:
Q: Name some IDE of java?
A: IDE is defined as an interactive development environment. By the time multiple IDEs are introduce…
Q: 2. Discuss the benefits of customer-facing applications (as a major component of operational CRM) to…
A: Introduction: Customer-facing applications are the applications that are used by your customers in…
Q: Briefly define blockchain technology and the possible applications for it.
A: Answer the above question are as follows
Q: What is the main contrast between testing and debugging in the context of a computer program?
A: software program Anything "programmed" involves writing specific lines of code based on the given…
Q: How much of an impact, in your opinion, have computer development and applications had thus far?
A: Computer development has provided a lot impact in our society . Computer application has used in…
Q: Defeating TCP congestion-control mechanisms usually requires explicit cooperation of the sender.…
A: In this problem, we must design a mechanism to change TCP to prevent the possibility of a sender…
Q: What is deadlock avoidance? Describe how this may be accomplished.
A: The correct answer for the above question is given in the below steps.
Q: 1 Compute probability of current state 2 compute the probability of observation sequence 3 Improve…
A: Here we have given the matching type with a given sentence. you find the solution in step 2.
Q: I want to count the number of nodes in a linked list. Each node of the list is a class called node.…
A: A linked list is the collection of nodes each containing two fields, i.e., data and the pointer…
Q: In a row numbered 11 to n from left to right, n athletes await their medals from Mr. Cook for their…
A: First-line will contain TT, the number of test cases. Then the test cases follow. The first line of…
Q: Discuss each of the following concepts in the context of the relational data model: (a) relation (b)…
A: Relational Data Model The logical data structures—the data tables, views, and indexes—are different…
Q: If I have a list of numbers 10, 5, 8, 2 write the Pyspark code to sort these in ascending order.
A: Solution:: # importing module import pyspark # importing sparksession from # pyspark.sql module…
Q: Put this code into a Python script and run it. Notice that it prints the names "Oack" and "Qack".…
A: Program code : prefixes = 'JKLMNOPQ'suffix = 'ack' for letter in prefixes: print(letter +…
Q: Write a PICmicro Assembly code that accept 4-bit operand 1 from the least significant bits of RB…
A: The code is in step 2:
Q: Question 35 Is this a Complete Binary tree? I Answer:
A:
Step by step
Solved in 2 steps

- What is the output of the following command? Get-DnsServerTrustAnchor –name secure.practicelabs.com –computername PLABDC01 Updates the trust points created earlier on the PLABDC01 Creates a new trust point on the PLABDC01 Refreshes the trust point on all DNS servers Creates a new trust point on all DNS servers from PLABDC01On servers with Linux operating system, access logs are kept under which of the following directories by default?A) /var/log/B) /var/log/auth/C)/log/D)/log/auth/ Which of the following would an attacker prefer to run operating system-level code with MSSQL?A) MSSQL cannot run code at the operating system level.B) MSSQL agentC) xp_cmdshellD) There are no options. As a network administrator, you want to reduce the attack surface on your systems. Which of the following helps?A) Creating shared folderB) Make sure that only the necessary services are activeC) To record access activitiesD) monitor network traffic Which of the following products can an institution prefer to use if its antivirus software is up-to-date on the computers in its network?A) FirewallB) DLPC) Web ProxyD) NAC When John enters the mobile banking app on his smartphone, he sees his account balance is decreasing. What would it be better for John to do first to fix this situation?A) Closing and reopening the mobile…The netstat programme, available for Linux and Windows, provides a list of active network connections. Describe how to use this command to identify whether a web page is not terminating connections or, if connection pooling is being used, is not returning connections to the pool. You may do this by looking at whether or not the connection is being returned to the pool. There is a possibility that connection pooling will not immediately terminate the connection.
- Recall that only Standard Output can be sent across a pipe to another command. Usingthe information presented in this chapter, how could you send Standard Error across thepipe in the following command?ls /etc/hosts /etc/h | tr h HA local Windows 10 administrator created a group called Trainees using Computer Management console. Then, he assigned local users in this security group. Members of the Trainees group need access to a custom application running on a domain-joined server Srv01. Can the Trainees group be used to provide access to this application? True FalseIn snort, what does the "-W" switch do? Group of answer choices "Watches" the network, .ie. goes into sniffer mode Dumps all system interfaces by Index Number Dumps all packets into a log file Dumps all rules to the console
- Reverse shells are what? An attacker receives a remote shell prompt. What do they do? The lab confirms the attacker's remote connection to the Security Onion shell with what command?For this lab, you will write a shell script called nethelper.sh that: 1. Reads in a list of hosts from a host file that is passed in as a parameter 2. Repeatedly, until the user selects quit (q), ask the user if the user wants to ping a host or look up a hosts DNS name 3. Once the user has selected an action, prompts the user for which host and then applies the action. Note that for the ssh action, the script must also ask the user for the user name that will be used to log into the host. Step 1 To accomplish step 1 above (reading in a list of hosts from a file), you will write a function called read_hosts. Functions in bash scripts have the following syntax: function name { # function body goes here } You can put any bash syntax inside the function as the function body. Also, note that the parameters to a function act like the parameters passed in at the command line. In other words, the parameters to the function are place in variable named $1, $2, and so on. So, how do you read the…The netstat command (available on Linux and on Windows) shows the active network connections on a computer. Explain how this command can be used to find out if a particular web page is not closing connections that it opened, or if connection pooling is used, not returning connections to the connection pool. You should account for the fact that with connection pooling, the connection may not get closed immediately.
- In Mac OS X, what file can an attacker replace with a no-password-requirement version to allow all scripted actions to be performed as root? Select one: a. /Library/InputManagers b. /etc/sudoers c. /groups/wheel d. /tmp/uidA company created an external application for its customers. A security researcher now reports that the application has a serious LDAP injection vulnerability that could be leveraged to bypass authentication and authorization. Which of the following actions would BEST resolve the issue? (Choose two.) : A. Deploy a WAF. B. Use containers. C. Conduct input sanitization. D. Patch the OS E. Deploy a reverse proxy F. Deploy a SIEM. ~if you could explain why you chose that correct choice, Id appreciate it. Thank you!A new application will be deployed on EC2 instances in private subnets. The application will copy/write some sensitive data from/to an S3 bucket. Company compliance policy requires that the data must not traverse the public internet. Which solution meets the compliance requirement? A.Access the S3 bucket through an VPC end point for S3 B.Access the S3 bucket through a proxy server C.Access the S3 bucket through a NAT Gateway D.Access the S3 bucket through the SSL protected S3 internet endpoint



