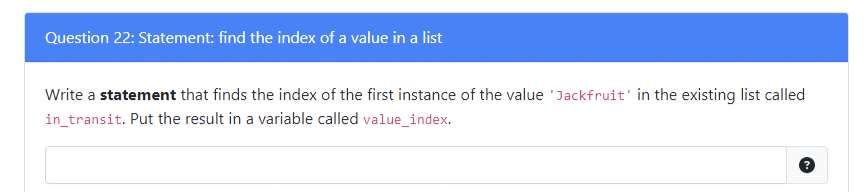
Question 22: Statement: find the index of a value in a list Write a statement that finds the index of the first instance of the value 'Jackfruit' in the existing list called in_transit. Put the result in a variable called value_index.
Q: .Write BST C++ recursively. Find the second smallest element in binary search tree. No iteration
A: first of all, take a node (structure). In which take an int variable data and to node type variable…
Q: Question 12 kan A problem Q is algorithmically solvable if there exists a Turning machine T for…
A: Dear Student, The answer to your question is given below -
Q: think about what this instruction is actually doing and consider its advantages and disadvantages.…
A: Answer This instructions is moving the contents of the register rax into the register r8. The…
Q: Provide a brief description of the core features found in most operating systems
A: INTRODUCTION: An operating system (OS) is a software interface that connects a computer user to…
Q: For the aviation industry, "snapshot isolation" serves as an example of a database design. In the…
A: Snapshot Isolation: A transaction on its private data is never stopped. At any moment, any data…
Q: This problem will compare the difference between an ordinary BST (henceforth referred to as just…
A:
Q: Making sure that encapsulation is not violated (i.e., instance variables must be private); design an…
A: class Vehicle{ private int year; priavte String make; Vehicle(){} Vehicle(int y,…
Q: Which of the following allows us to perform remote command exec
A: SSH allows us to execute command on remote machine without logging into that machine.
Q: Explain the main parts of an OS in a single word.
A: Introduction: The kernel is the primary processing unit of an operating system (OS) for a computer.…
Q: en it comes to memory, what should an OS be responsible for?
A: Here in this question we have asked that when it comes to memory, what should an OS is responsible…
Q: 9. Perform a search for key 1040237. How many (hash table) elements will have to be compared with…
A: Given hash funcion H(K) = K% 11 resolved using Lienar Probing where we find next empty slot in case…
Q: The components of the operating system that are kept in the memory of the computer are referred to…
A: Answer The components of the operating system that kept in the memory of the computer are referred…
Q: brief explanation about the use of number system conversion and why we need this in our lives no…
A: We employ a special language composed of letters or words to communicate with one another. The…
Q: When redistributing a route into EIGRP, what parameter must be used? Factors like the next hop's IP…
A: The administrative distance must be used when redistributing a route into EIGRP.
Q: What is the output of the following code? class Person: def __init__(mysillyobject, name, age):…
A: Given python code for the class Person and testing the class by creating object is : class…
Q: Write code to Convert an Arabic number to a modern Roman number.use c language
A: code to Convert an Arabic number to a modern Roman number in c
Q: create a function in R studio. function name: df_summary (ex. df_summary(data)) first condition:…
A: Here is the r code of the above problem. See below steps.
Q: Suppose you would like to urgently transfer 30 terabytes data from newyork to detroit . You have 1…
A: Data Transfer is required when we need to provide the important information. This information…
Q: Explain how to do Breadth First Search, with an example.
A: INTRODUCTION: Breadth First Search is a traversal approach in which we visit all the graph nodes in…
Q: ment the TNode and Tree classes. The TNode class will include a data item name of type string, which…
A: Dear Student, The source code, implementation and expected output of above question is given below -
Q: 1) Implement a c program function that gets the start and end index of a substrings in a given…
A: Algorithm:- read string, startIndex, endIndex. length=strlen(str) iterate from i=startIndex to…
Q: The following picture has been captured from the Wireshark software. What kind of Packet (In or Out)…
A: Solution:-
Q: 5. True or False: If G is a complete graph (i.e. each pair of vertices is connected by an edge)…
A: 4. Size of B(G) is θ(n*m) This is because the matrix has n rows and m .columns
Q: 6. Analyze the appropriate log file on your Kali Linux VM to identify the events related to the…
A: Kali Linux is a linux distribution designed for digital forensics and penetration testing.…
Q: Write a C program to read in a text file and provide a count of a. The number of strings in the…
A: The Code and output from the above-given question is given below:
Q: Let's talk about the ethical and societal repercussions of our increasing reliance on digital tools.
A: Introduction: The following are some social and ethical concerns about using and utilizing…
Q: I need help in this MCQ question of Data Strucutre and Algorithmn ASAP URGENT. a)Given graph Gr…
A: The graph is considered a collection of vertices and edges and is represented by the G=(V, E). Here,…
Q: Provide the one line of code for each of the following: 1. You are given a string from the user. 2.…
A: The code is provided in c++ program
Q: When compared to a simple translation, why is it preferable to use a segmented translation of memory…
A: Some advantages of memory address translation utilising segmentation methods are as follows: Due to…
Q: allenge: 12 - Password Verifier Use the string data type. Do not use arrays of type char or…
A: Dear Student, The source code, implementation and expected output is given below -
Q: Please rewrite this C program in 2019 Visual Studio where it works the same but looks completly…
A: If length, width and height are the dimensions of the cube then the volume of the cube is calculated…
Q: Creating a class involves creating new instancesof objects defining class attributes changing values…
A: The solution is given below for the above given question:
Q: According to the following requests, please draw the operations procedure of binary search tree as…
A: We need to draw the operations procedure of binary search tree as step by step for the given nodes.…
Q: Calculate the total number of lines of "direct mapping" cache, If a main memory is 1G words divided…
A: We need to find the total number of line in direct mapping cache. See below steps.
Q: What will be output for the following code? import pandas as pd df = pd.read_csv('data.csv')…
A: In first line pandas module is imported. In the next line a CSV file is read using pandas
Q: How are all of a network's physical and virtual networking devices meant to be configured and…
A: Connectivity: Physical networking includes wires and routers. This is different from the virtual…
Q: The table below shows illness, symptoms and treatment. Write a C program to portray the table.…
A: According to the question asked, we just have to create the table by using C as the programming…
Q: Why do you think x86 will not let you run the instruction below : mov [r8], [rax] In order…
A: x86 which refers to the one it is a family of complex instruction set of the computer instruction…
Q: Exactly what is meant by the phrase "memory void," if it exists at all? How is it that this is even…
A: Introduction: A memory blank is like a method for purposefully changing or erasing unfavorable or…
Q: A classification tree with no splits may also be referred to as:
A: Ans: A root node
Q: The components of the operating system that are kept in the memory of the computer are referred to…
A: Dear Student, The answer to your question is given below -
Q: uestion kan True or False: In a program using blocking Input/Output, the program is put to sleep…
A: Dear Student, The answer to your question is given below -
Q: It would be helpful if you elaborated on the software development process metrics you discovered.…
A: Software development matrix: Software metrics are measurements of measurable or countable software…
Q: Non-disclosure of sensitive information in error responses, including system details, session…
A: Solution: Given, a) Non-disclosure of sensitive information in error responses, including system…
Q: For this question please paste in a single line of code that loads training and test data for the…
A: Program Approach: Step 1: Import TensorFlow as tf. Step 2: Load the fashion mnist dataset into…
Q: Look at the idea of utilizing Structured English to describe activities that are beyond the purview…
A: Introduction:- Structured English is used: Structured English is the use of the English language in…
Q: Many companies use telephone numbers like 555-GET-FOOD so the number if easier to remember. On a…
A: Here is the editable source code: def getNumber(alphabet): if alphabet in "ABC":…
Q: Local variables are defined in the method and scope of the variables that exist inside the method…
A: Answer False Local variables are defined in the scope of the method they are declared in, but they…
Q: Apply this algorithm to the tree shown in Figure 5 and provide the result of the traversal in the…
A: it is a binary tree. every root node taking char like (+,*,/) . In python code, the first line…
Q: Algorithm for Match in a pyramid tournament. in: set P of players in the pyramid structure; players…
A: Algorithm for Match in a pyramid tournament:
Question 14 papa
. use python
Full explain this question and text typing work only
We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
Step by step
Solved in 4 steps with 2 images

- Hi! I have to make a function that will return a list with all of the prime numbers removed. It should return as a new list. I've already managed to identify the prime numbers on my list but struggled in coding their removal. How do I proceed with this? Thank you!Replace XXX in the following function header for a doubly-linked list: ListInsertAfter(listName, currentNode, XXX) Group of answer choices headNode tailNode middleNode newNode7-Write a procedure that returns the list that contains everything except for the last element of the given (nonempty) list. For example, (last-element ‘(a (b c ) (d)) ) returns (a (b c)). For example, (last-element ‘(a (b c ) (d) ) ) returns (a (b c)) . Then, Manually trace your procedure with the provided example.
- How to remove duplicate elements from a list?Write a statement that creates a two-dimensional list with 5 rows and 3 columns. Then writenested loops that get an integer value from the user for each element in the list.1-Let the list have a head and a tail. That is, a pointer (have a marker) to both the beginning (first Node) of the list and the last Node. What process does Tail facilitate? 2-insert(int index, int element): adds this element to the index position. For example, if index is 4, it adds this element between index 3 and 4 in the list. The size of the list has increased by one. 3-append(int elem): Adds the element to the end of the list. The size of the list has increased by one. 4-get(int index): Returns the element at the index position of the list, no change in the list. 5-remove(int index): Returns the element at the index position of the list. This element is removed from the list and the list size is reduced by one. 6-findMin(): returns the index of the smallest number in the list. 7-findMax(): returns the index of the largest number in the list. 8-search(int elem): searches elem in the list. It returns -1 when you can't find elem's index when you find it. 9-ToArray(): Return an…
- 1-Let the list have a head and a tail. That is, a pointer (have a marker) to both the beginning (first Node) of the list and the last Node. What process does Tail facilitate? 2-insert(int index, int element): adds this element to the index position. For example, if index is 4, it adds this element between index 3 and 4 in the list. The size of the list has increased by one. 3-append(int elem): Adds the element to the end of the list. The size of the list has increased by one. 4-get(int index): Returns the element at the index position of the list, no change in the list. 5-remove(int index): Returns the element at the index position of the list. This element is removed from the list and the list size is reduced by one. 6-findMin(): returns the index of the smallest number in the list. 7-findMax(): returns the index of the largest number in the list. 8-search(int elem): searches elem in the list. It returns -1 when you can't find elem's index when you find it. 9-ToArray(): Return an…1-Let the list have a head and a tail. That is, a pointer (have a marker) to both the beginning (first Node) of the list and the last Node. What process does Tail facilitate? 2-insert(int index, int element): adds this element to the index position. For example, if index is 4, it adds this element between index 3 and 4 in the list. The size of the list has increased by one. 3-append(int elem): Adds the element to the end of the list. The size of the list has increased by one. 4-get(int index): Returns the element at the index position of the list, no change in the list. 5-remove(int index): Returns the element at the index position of the list. This element is removed from the list and the list size is reduced by one. 6-findMin(): returns the index of the smallest number in the list. 7-findMax(): returns the index of the largest number in the list. 8-search(int elem): searches elem in the list. It returns -1 when you can't find elem's index when you find it. 9-ToArray(): Return an…Write the code that would create a list of data. The list should be called data. The data list should be initialized to the following values: 54, 26, 14, 93, 17, -10, 77, 31, 40, 55, 20
- Given two lists(List1, List2) of INTs create a third list such that should contain only odd numbers from the first list and even numbers from the second list def mergeList(listOne, listTwo): thirdList = [] #complete the functionAssume list1 references a list. After the following statement executes, list1 and list2 will reference two identical but separate lists in memory: list2 = list1, True or FalseWrite a statement that will print the first letter of each element of the following list: list1 = [‘Galileo’,‘Oliver’,’Ostwald’,’Descartes’].

