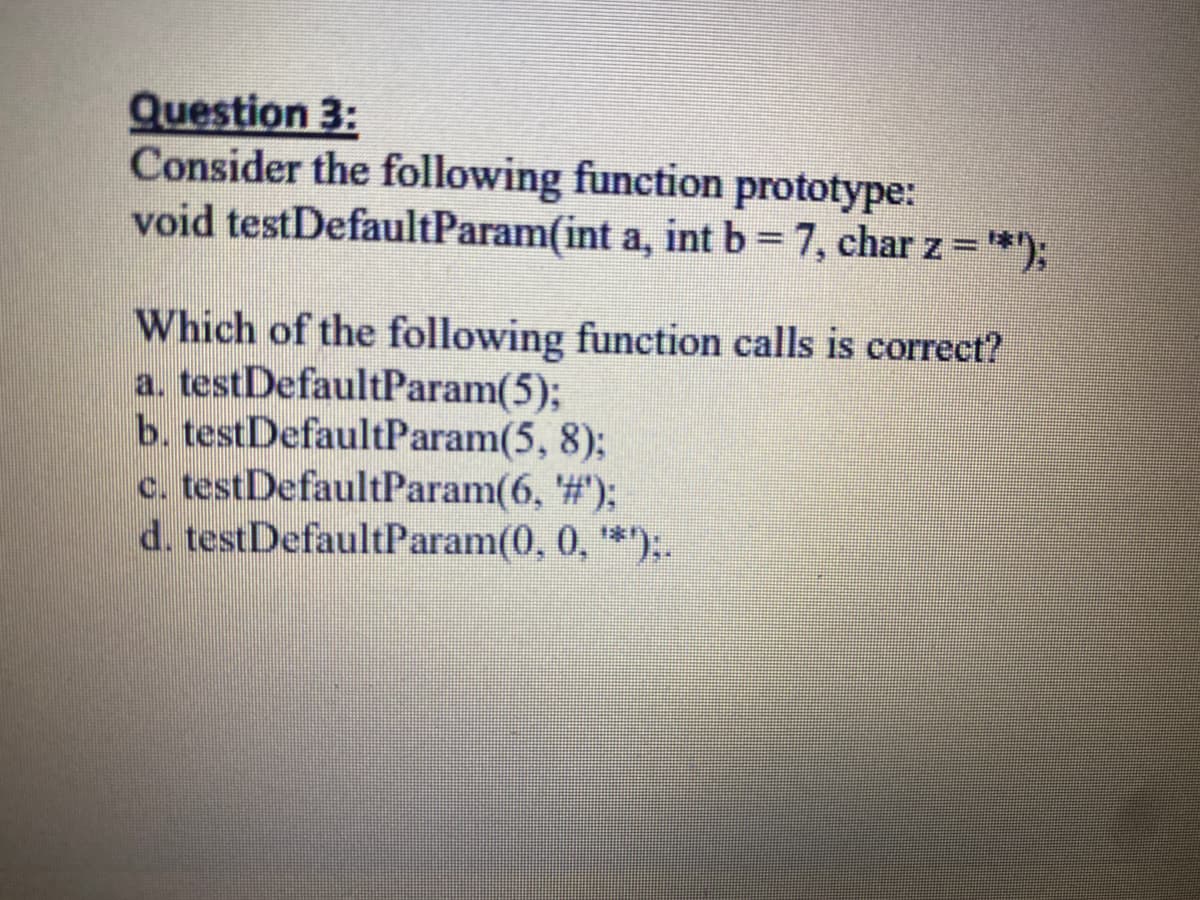
Question 3: Consider the following function void testDefaultParam(int a, int b= 7, char z ="*); prototype: Which of the following function calls is correct? a. testDefaultParam(5); b. testDefaultParam(5, 8); c. testDefaultParam(6, '#); d. testDefaultParam(0, 0, *):.
Q: Advantages and disadvantages of Artifical Intelligence in society
A: Artificial Intelligence is a program which has been designed to do work that can be done by the inte...
Q: Need 2 separate java files: one with class and methods and other with the main method
A: let's know some terms used in the above query: java class/objects:- Java is an object-oriented progr...
Q: Describe the MIDI port. What functions can a MIDI-equipped system unit perform?
A: Introduction : MIDI port: Hence, the MIDI-Port is the principal mechanism by which MIDI-sequencers a...
Q: What computer program translates code written in a high level language to a low level language/machi...
A: Given :- What computer program translates code written in a high level language to a low level langu...
Q: We wish to generate an expression tree from the following postfix expressions. While running through...
A: When the operators are moved after the operands, then it is called a Postfix expression. The express...
Q: Which are operating systems? Solaris, HP-UX, AIX, Tru64, Linux Windows, Vista, XP, Mac OS Both (a) a...
A: Question 1: Solaris ,HP-UX ,AIX is Unix operating system originally developed by Sun Microsystems. ...
Q: Convert the hexadecimal number to binary: (FB17)16 Convert the binary number to hexadecimal: (100110...
A:
Q: What are the drawbacks of Apple devices? What can be done to address these issues?
A: Introduction: Apple devices are very famous and quality devices that are expanding at a great rate. ...
Q: Write a function header for a function named distance. The function should return a double and have ...
A: Given :- Write a function header for a function named distance. The function should return a double ...
Q: Show how given a graph G in adjacency matrix representation, it is possible to use Strassen's matri...
A: Let,Divide matrices A and B in 4 sub-matrices of size N/2 x N/2. Calculate following values recursiv...
Q: Givern the logic expression: F = abcd + ābcd +ābcd + ābcd + abīd + abcd + abēd + abēd Use K-Map to s...
A: We are given a logic expression and we are going to find out its minimal sop and pos expression usin...
Q: defined the struct studentTypeto implement the basic properties of a student. Define the class stude...
A: Write code to define struct studentTypeto implement the basic properties of a student after that def...
Q: Compare two SQL versions that you have access to, such as Microsoft Access and Oracle SQL*Plus. Find...
A: Introduction : A MySQL is a relational database management system that is free and open source. Like...
Q: Explain how to save simple data types in a session using a PHP script.
A: Introduction Data types in sessions the simple data types that are handled by the sessions are an i...
Q: Explain the methods of interprocess communication utilised in the UNIX operating system.
A: There are many methods of interprocess communication in UNIX OS. I have listed them below,
Q: How do forensic investigators obtain data from Windows-based PCs that is both volatile and non-volat...
A: Introduction: According to the question, both are used to safeguard data at organizations that inclu...
Q: For which normal form and of which function is A--Ca part of?
A: Option c is the correct answer.
Q: Identify the major components of a computer, and briefly explain the function or the role of each co...
A: Introduction: The motherboard, often known as the system board, is the most important printed circui...
Q: Make an array called array with three elements in it, a hashmap /dict / associative array called has...
A: int ar1[] = {1, 5, 10, 20, 40, 80}; int ar2[] = {6, 7, 20, 80, 100}; int ar3[] = {3, 4, 15, 20, 30, ...
Q: employee recruitment security protocol that the organization intends to adopt for all recruitment pu...
A: Employers are often confronted with employee relations issues in the workplace and faced with decidi...
Q: assembler language" isn
A: An assembler is a program that converts fundamental computer instructions into a bit pattern that ca...
Q: Convert ABF(16) =x(64)
A: Introduction: Answer with step-by-step explanations the following question. Convert ABF(16) =x(64)
Q: Consider a singly linked list where each node contains two fields – integer data and node type point...
A: The program is written in C Language. Check the program screenshot for the correct indentation. Plea...
Q: Describe the typical actions related with the DBA's technical function's design and implementation s...
A: A database administrator (DBA) is the information technician responsible for directing or performing...
Q: // Definition of copy constructor // Instructions omitted intentionally. // Your code
A: Here,in this section describe the following questions.. // Definition of copy constructor // Instru...
Q: When it comes to ERP implementations, the infrastructure must be handled as well. Describe the infra...
A: What is the meaning of ERP implementation? The Enterprise Resource Planning (ERP) is a term used to ...
Q: Write a loop that reads positive integers from standard input and that terminates when it reads an i...
A: I am submitting the complete working of code please go through it.
Q: What are the advantages of rigorous two-phase locking? What are the drawbacks?
A: Introduction: In contrast to severe 2PL, which allows read-only locks to be released sooner, rigorou...
Q: Define the type of security attack in each of the following cases: A student breaks into a professor...
A: A student breaks into a professor’s office to obtain a copy of the next day’s test. Ans :- Confident...
Q: Justify the significance of computers in scientific research.
A: In science and technology or in scientific research , computers play a critical and vital role.The c...
Q: hance that vour data center would suffer some sort
A: It is given that a $6 million government data center is located in a large city in Pacific Northwest...
Q: What exactly are distributed denial of service (DDOS) attacks?
A: Introduction the question is about What exactly are distributed denial of service (DDOS) attacks a...
Q: QUESTION 20 What is the depth of this tree? 100 46 68 12 34 29 QUESTION 21 The time complexity for r...
A: Find the answer given as below : As per company guidelines we are supposed to answer first three que...
Q: Kevin and Stacy want to play a game they have titled 'Vowels or Not?'. Here are the game rules: Bot...
A: I have answered this question in step 2.
Q: 1. State the memory representation of single linked list with example. 2. Linked lists have several...
A: Hello student, hope you are doing good The answer to both of the question is attached below along w...
Q: Write a c++program that asks the user to insert continously until and then prints the count of even ...
A: Program Explanation:- Using the header file. Using namespace standard input/output function. Define...
Q: 3. A famous bakery in Vellore prepares cakes for their customers. The shop makes cake and stacks it ...
A: Note: Code works perfectly as the above problem is asked. Please use proper indentation for no error...
Q: In the context of cryptography, what are the differences between a cipher that uses symmetric keys a...
A: cryptography: An Cryptography is an important method for protecting information and communications ...
Q: Points] ic static List makeList ( int N) ArrayList 1st = new ArrayList () for ( inti =0; i < N; i++)...
A: According to the question below the solution
Q: The OCR stand for?
A: It's a technique for detecting text within a digital image. It's a program that recognizes text in s...
Q: Could you perhaps explain flooding briefly?
A: Introduction: Flooding is a basic computer network routing strategy in which a source or node distri...
Q: What are the advantages and disadvantages of IPSec over other network security solutions, such as ap...
A: Introduction: IPsec is a collection of linked protocols used to secure communications at the network...
Q: What are the different types of programming paradigms? What are the many types of programming paradi...
A: Programming Paradigms: Following are the several kinds of programming paradigms: Imperative: This...
Q: Why are several versions of Internet Protocols (IP) available?
A: Introduction: There are primarily two types of IP. IPv4 IPv6
Q: Make a list of three technologies that have made the transition from analog to digital. What was the...
A: A digital signal is a signal that represents data as a sequence of discrete values at any given time...
Q: 1. Explain with examples linked lists and arrays with their advantages and disadvantages. When do yo...
A: A linked list is a linear data structure, in which the elements are not stored at contiguous memory ...
Q: When is it OK to use the super keyword? In java
A: Introduction: The super keyword is used to refer to items in the superclass (parent) When is it OK t...
Q: In comparison to machine code, what are some of the benefits of compiling to bytecode?
A: Byte code and machine code are two different types of code: Byte code is a kind of computer code: A ...
Q: Using two's complement form with 8 bits, subtract 30 from 50. If you are converting any number to tw...
A: let's see the soluion with explanation:-
Q: Consider the many data access scenarios that can arise in a distributed database system.
A: Distributed databases are used for horizontal scaling, and they are designed to meet the workload re...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- In C++, Given the following function prototype: void testDefault(int a, int b = 7, char z = '*'); Indicate if each of the following function calls are valid or invalid a) testDefault(5); b) testDefault(); c) testDefault(6, '#'); d) testDefault(0, 0, '?');Assume that the declarations for two functions look as follows: int Function1(double x); 2.void Function2(double x); Give some sample code that would show how each function could be used.Give an example from your own idea, of a program that use a void function (does not return avalue), based on your understanding. (You must include a main function)
- For this question you will design and implement a function that takes 5 arguments and produces 5 return values. This question is internally recognized as variant 0371. The 5 arguments must be of types int, int, bool, bool, and char (in that order), and they must be stored in parameter variables 'ham', 'bar', 'xyz', 'gzk', and 'foo', respectively. As a clarifying example, the second parameter - 'bar' - will be of type int. The function you create must perform the operations list below, in the specified order and exactly as they are described here. You are NOT permitted to simplify the operations. 1. create a new variable named 'ukr' that stores the result of increasing the 'ham' parameter by 42 2. if the conjunction of the 'xyz' parameter and the 'gzk' parameter has a value of True, multiply the value of the 'ham' parameter by a value of 29 and store the result back in 'ham' 3. negate the value of the 'xyz' parameter and store the result back in 'xyz' 4. decrease the value of the 'ham'…Write a declaration for a function called test( ) that takes 2 arguments and returns type char. The first argument is type int and the second is type float with a default value of 5Consider the following function call: draw_circle('red', 3) What is the function name and what is the first argument passed to the function? a. The function name is draw_circle and the first argument is 3. b. You need to see the function definition to determine the function name and arguments. c. The function name is draw_circle, but you need to see the function definition to determine the arguments. d. The function name is draw_circle and the first argument is 'red'. e. The first argument is 'red', but you need to see the function definition to determine the function name.
- Consider the function definition: void Demo (int intVal, float& floatVal ) { intVal = intVal * 2; floatVal = float(intVal) + 3.5; } a. Suppose that the caller has variables int myInt and float myFloat whose values are 20 and 4.8, respectively. What are the values of myInt and myFloat after return from the following function call? Demo(myInt, myFloat); myInt: myFloat: b. Also, describe what happens in MEMORY when the Demo function is called. Think about the by reference and by value parameters.17. A function should determine the average of x and y. What should be the function's parameters and return value(s)? A.Parameters: none Return values: X,y B.Parameters: ×, y, average Return value: none C.Parameters: average Return values; X, y D.Parameters: X, y Return value: average1. Write a program in python that contains a main function and a custom, void function named show_larger that takes two random integers as parameters. This function should display which integer is larger and by how much. The difference must be expressed as a positive number if the random integers differ. If the random integers are the same, show_larger should handle that, too. See example outputs. In the main function, generate two random integers both in the range from 1 to 5 inclusive, and call show_larger with the integers as arguments.EXAMPLE OUTPUT 13 is larger than 1 by 2EXAMPLE OUTPUT 2The integers are equal, both are 3
- 2. If a function have all the default arguments but still some values are passed to the function then _________.This is python Regarding a function, which of the following is not true? The def keyword is used to create a function. A function must contain a return statement. When a function is defined, it must have parentheses. A function can contain another function.Engineers often measure the ratio of two power measurements in decibels, or dB, which can be calculated as follows:dB= log10P2/P1Where P2 is the power level being measured, and P1 is some reference power level. Write a function that calculates the level. The function’s prototype is as follows:double dBCalculator (double P1, double P2);Then, call dBCalculator from the main function to find the power ratio for the measurements from 1 to 20 Watts, in 2 Watt steps. You can assume that the reference power P1 is 1 Watt.



