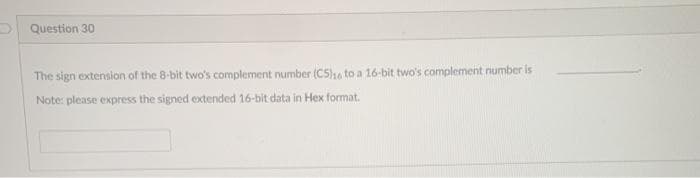
Question 30 The sign extension of the 8-bit two's complement number (C5)16 to a 16-bit two's complement number is Note: please express the signed extended 16-bit data in Hex format.
Q: What steps should be taken to guarantee the long-term viability and reliability of a local network?
A: Local Area Network (LAN): A local area network is a collection of miniature computers or other…
Q: It's important to understand what an infrastructure-based wireless network is and how it works. When…
A: Base stations (BSs) or access points (APs) are two types of infrastructure-based networks that…
Q: Identify the many components that make up an information system and describe the interdependencies…
A: The following components exist: TECHNOLOGY It may be viewed of as the application of our knowledge…
Q: From the outside, what can be done to address the problem of fragmentation?
A: Given: When the overall amount of empty memory space is insufficient to meet all of the allocation…
Q: Select the appropriate response from among the statements that are provided. Applications like as…
A: In contrast to application software, infrastructure software is used to manage the computer…
Q: Cloud-based collaborative working can be used for what? Working together on the cloud has a number…
A: Cloud describes the global network of servers with a unique function and a wide network of remote…
Q: Examine the benefits and drawbacks of doing regular software upgrades.
A: The Answer is given below step.
Q: Consider how the internet has evolved through time and how it depends on the current technical…
A: Answer:
Q: Is there any benefit or drawback to making use of the Java Generics feature?
A: The answer is
Q: Observe the present state of the internet and its technological foundations.
A: Internet and its Technological foundations: The communications and computer sectors have been…
Q: 1- Current Directory Browser used to?
A: Given 1. To know about the current directory browser in Matlab.
Q: A computer's Internet Protocol (IP) address is its unique identification on the Internet. Just how…
A: In order to talk about mnemonic addresses in addition to IP addresses: Find out the maximum number…
Q: explain the three main testing phases for a commercial software system you've experienced in a few…
A: Please find the answer below :
Q: MBX, EXB, GBX, FAR, ABX, AXB, BIN, QXB, YXB, AFF . Build a max- Heap showing all steps in…
A: In max heap, maximum element is at root.
Q: Raspberry Pi has the following features: Select one or more: a. small size b. Hard disk drive c.…
A: Answer- a ,e , f , h.
Q: If you don't have to, why do ML programmers disclose the types of variables?
A: Introduction: ML Programming: In comparison to languages in which programmers must declare all types…
Q: What exactly does it mean to say that anything is an information system? Define and explain the…
A: Information system: An information system is a term that is used to refer to an integrated…
Q: b) Draw the decoder circuit for a systematic linear cyclic code that has a code length n = 7 and a…
A:
Q: Explain (in one to two lines) the function of the instruction XCHG AX, BX, if AX = 5241H and BX =…
A: XCHG : This instruction is used to interchange the data between two registers or memory locations…
Q: The associativity of an exponentiation operator ^ is right side. a) True b) False
A: The question has been answered in step2
Q: 4. Write a Matlab program to compute the value of 30*10 without using the operator. Attach the *…
A: Find the required matlab program given as below and output :
Q: Is it beneficial to have a working knowledge of computers? When it comes to education, business,…
A: Knowledge of computers: A computer is a programmable device for data storage, retrieval, and…
Q: What is an infrastructure-based wireless network? When not in infrastructure mode, what does the…
A: Wireless Network that Relies on Existing Infrastructure The term "infrastructure-based network"…
Q: Oracle database backups using RAID storage? Because handwriting is hard to read, content should be…
A: SOLUTION: Low-Cost Redundant Array (RAID) RAID combines multiple discs into one array. These discs…
Q: What are the duties of a Systems Analyst?
A: Given: An information technology system analyst is responsible for analyzing and creating solutions…
Q: Should the security needs of society, the owners of the information system, and the users of the…
A: Given: It safeguards the company's operations. It ensures the safety of IT applications. It…
Q: complement DFA
A: Hey there,I hope you find my solution helpful.
Q: FSCA needs to support its strategic plan
A: The strategic intent of this document is to outline the FSCA approach in discharging its…
Q: : Complete the following phone conversation. A: Good morning. The British Tourist Authority. B:…
A: Here it is English conversation we can fill in different words but correct match and phrase is very…
Q: What is the concept of an infrastructure-based wireless network? Other than infrastructure, what…
A: The Answer start from step-2.
Q: (Q3)The matrix A= [3 3 3; 5 2 1; 7 5 1] create the submatrix as the following: 1- B matrix is the…
A: All the submatrixes are given below in MATLAB form A = [3 3 3 ; 5 2 1 ; 7 5 1 ] or A = 3 3 3 5…
Q: Q5: Mention the basic drawing instructions, modification instructions, and drawing aids necessary to…
A: STEPS AND COMMANDS USED :- UN enter to set the units to mm lim enter to set the sheet size XL enter…
Q: Your web company will benefit from the use of AMP (Accelerated Mobile Pages).
A: Given: While AMP may aid SEO, it is not required, and its advantages are more relevant to certain…
Q: this cod >>7*DThe .----((6&1) result of executing + (~0.00) +(0&5)); is 7 Ο Ο Ο Ο Ο Ο 49 48 error…
A: Find the required with explanation given as below :
Q: Early Internet research sought to address what problems? What was the solution to these problems?
A: Introduction: Internet history: Started in about the 1960s Started with fewer resources Initially…
Q: Which of the following Turing machine instruction set performs the unary addition in the most…
A: Here all the instruction set perform the unary addition but according to time efficient option 1…
Q: What type of communication is this? Transmitter D6 D1 Select one: D2 D3 a. Parallel communication b.…
A: In data transmission, parallel communication is a method of conveying multiple binary digits (bits)…
Q: List and briefly describe many global information system issues.
A: Global information systems: Global information systems are systems that are used by a number of…
Q: #include using namespace std; //creating an Abstract base class for the Employee class Employee…
A: Encapsulation : Encapsulation is a process of data members and operation made on this data(,i.e,…
Q: Sampler is simply just a transistor switch Select one: O True O False
A: Please find the answer below :
Q: Use Input to print "< =" and stop the program until the user enters a value and presses the Enter…
A: While loop is used to solve this
Q: What are the best ways to ensure the long-term viability and availability of a local area network?
A: Given: In order to get a complete understanding of resilience, it is necessary to first dissect it…
Q: • L₂ = {w = {a,b,c}* | w = b(a UbUcb)*a}
A: The given format represents a language in Automata systems.
Q: In order to maintain the CPU, memory, buses, and peripheral devices, devices balanced, what are two…
A: There are many factors that affect processor performance. The most important factors affecting…
Q: Write pseudocode and draw the flowchart to read the age of a user. You should then display the…
A: Pseudocode is the simple language explanation of the steps of algorithms. Flow chart is the…
Q: What is the data transfer rate of Ethernet local area networks?
A: There is standard 100 Mbps ethernet, which is what most people have at home. 100 Mbps is 100…
Q: QUESTION#3 Interface 8-bit input port (74LS245) to read the status of switches SW1 to SWB to the…
A: It is defined as the central unit of a computer system that performs arithmetic and logic…
Q: MATLAB cod >>A= ones (4); size In A is 22 O 4 O 16 O 44 O 11 O In Matlab, (.1) use for division…
A: Answer 1: Correct Option(c) 4 4 Explanation: ones(n): It is used to create a nxn matrix with all…
Q: Popular social networking site My+Din is struggling to manage its many popular forums. Recent…
A: Here is the approach : First take input for the amount of strings . Take the strings Then…
Q: 1. Among the advantages of the control system, what specific advantage addresses that control system…
A: The question has been answered in step2
30
Step by step
Solved in 2 steps with 2 images

- A(n) __________ is an integer stored in double the normal number of bit positions.How do I convert these decimal values to IEEE-754 single precision and IEEE-754 double precision representation in hexadecimal format? a. 2.625 b.-5.25Represent the following numbers to its 6-bit binary representation and perform binary subtractionusing 2’s compliment representation 50-30?
- Please solve and show all work. Thank you. What is 5ED4 - 07A4 when these values represent unsigned 16-bit hexadecimal numbers? The result should be written in hexadecimal. Show your work. What decimal number does the bit pattern (0C000000)16 represent if it is a floating-point number? Use the IEEE 754 standard. Write down the binary representation of the decimal number 63.25, assuming the IEEE 754 double precision format. What are the corresponding MIPS instructions to this C code: C code: float f2c (float fahr) { return ((5.0/9.0)*(fahr - 32.0));} if fahr in $f10, result in $f2, literals in global memory space.please answer with proper explanation and step by step solution. Question What decimal number does the bit pattern 0xC2280000 represent if it is: A two's complement integer? An unsigned integer? A floating point number assuming the IEE 754 single precision format5. What is the 8-bit binary(two- complement) representation of the following signed decimal integer? -16
- What is the computed difference in binary notation of ((61 base 10) - (58 base 10)) expressed in 8-bit notation?Please find 1.25's corresponding bit pattern as stored in memory in hexadecimal! And show the steps because i dont know how to find hexadecimal with a floating point number.1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?
- 1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?Assuming IEEE 754 single precision format we learnt in the class, what decimal number the hexadecimal bit pattern 0C000000 will represent? You need to first convert the hexadecimal number to its binary representation, and then find out the exponent and the significand using the IEEE format. Show all steps.True/False The number of distinct values represented in a 32-bit sign-magnitude binary representation is identical to the number of numbers represented in a 32 bit 2's complement notation.

