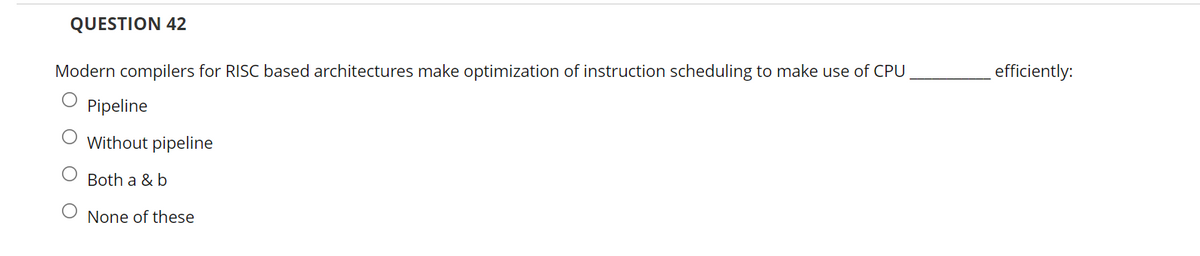
QUESTION 42 Modern compilers for RISC based architectures make optimization of instruction scheduling to make use of CPU efficiently: Pipeline O Without pipeline Both a & b O None of these
Q: What is the most important difference between Internet access and telephone service?
A: Introduction: Internet access is the process of people or businesses connecting to the internet via ...
Q: In a network, an intruder connects two VLANs by permitting user traffic on the second VLAN. Identify...
A: Introduction: VLAN hopping, also known as virtual LAN hopping, is a network assault in which an atta...
Q: Create a pseudocode and flowchart for this c++ program #include using namespace std; int main() ...
A: Find the required code given as below and output :
Q: Network and Communication question. Consider sending a 4,000 byte datagram into a link which has an ...
A: .Consider sending a 4,000 byte datagram into a link which has an MTU of 550 bytes. Suppose the origi...
Q: ascertain if the date format used in the United States is the most often used format
A: Introduction Date Format: Date format varies from region to region and country to country. The basi...
Q: Convert (72BA3DFA)16 from its hexadecimal expansion to its binary expansion. Convert (1011 0100 1111...
A:
Q: What is the job of a Systems Analyst in an organization?
A: Given: What is a Systems Analyst's role in an organization?
Q: Exceptions are ... Solec+
A: Option b exception handling is the process of responding to the occurrence of exceptions – anomalou...
Q: Please answer it in Python write a function word_vers_dictionary(word), which takes a word (string...
A: According to company guidelines we are supposed to answer only one question. Kindly repost other que...
Q: E -> E + T | T T -> T * F | F F -> ( E ) | i 1) Please give the handle for E+(T*i+i) . 2) FIRST(E)...
A: Introduction: Handles: Handles are substrings of sentential forms. 1. A substring that matches the r...
Q: What exactly is Big Data and why is it important?
A: As per company guidelines we are suppose to answer only first 3 subparts of the question. Kindly re-...
Q: Question 3 The order-of-growth performance of most typical algorithms can be described by a small se...
A: Solution: The order of the growth of the running time of the algorithm gives the efficiency of the a...
Q: When designing models of software systems, what views should be taken into account?
A: Given: What perspectives should be considered while creating software system models?
Q: 8. Symbolizing data is preserving their origin b. source c. confidentiality d. significance a.
A: The answer as given below:
Q: Could you please assist me? I only need a concept for my review (research) paper, which will be conc...
A: Intro Information Assurance and Security. Answer: Information Assurance and Security: What is an...
Q: To address 1KB, 2KB, 4KB, 1MB, 1GB, and 4GB of RAM, how many bit addresses are required? How many bi...
A: INtroduction To address 1KB, 2KB, 4KB, 1MB, 1GB, and 4GB of RAM, how many bit addresses are requir...
Q: Create a python program
A: Create a python program
Q: Examine thread scheduling and how processes and threads compare and differ.
A: Threads, processes, and threads are compared and contrasted in their scheduling. Threads are schedul...
Q: 2.circuit breaker accessories, such as shunt release, under voltage release, electrically operated i...
A: Hence the answer
Q: What is the difference between a set of test criteria and a set of test requirements?
A: Answer:
Q: Explain instantaneous description of What is PDA? PDA Show that the following ambiguous. grammar is ...
A: The answer is given in the below step by step
Q: What is a firewall's purpose, and how does one go about installing one?
A: Introduction: A firewall's two functions are network traffic monitoring and control.
Q: Which of the following attacks prevents a company's website and resources from being accessed? Malwa...
A: introduction: The term "denial of service" refers to a sort of cyber attack in which a malicious act...
Q: Create an MVC application that passes the data of the user through a blade and gets the same data in...
A: Introduction Create an MVC application that passes the data of the user through a blade and gets the...
Q: Distinguish between the terms "validation" and "verification." Examples should be given.
A: Introduction: The steps of verification and validation are used to ensure that the data given by the...
Q: What is the definition of hand tracing?
A: Introduction Hand tracing: In the hand tracing the program is debug on pen and paper. There is no ...
Q: Examine a DAG recursively and cc two constants into a single constan
A: Lets see the solution.
Q: Identify and describe the five key areas/fields dealing with internet governance, as well as the int...
A: Associations today are dependent upon numerous guidelines overseeing the assurance of ordered data, ...
Q: What is the significance of architecture? Consider a project and map it both with and without archit...
A: INTRODUCTION: Here we need to tell the significance of architecture and the influence will it have o...
Q: Explain how caches are utilized to leverage "spatial locality" and "temporal locality" for performan...
A: There are two major sorts of reference destinations temporal and spatial locales. Temporal locality ...
Q: How would you use static routes configuration as a network administrator in the following situations...
A: Introduction: Your responsibilities as a network administrator are divided into the following catego...
Q: Network and Communication question. A mid-size organization ABC is granted with 201.10.60.0/26. The ...
A: 201.10.60.0/26 /26 means number of network bits is 26 and number of host bits is 6. For first 3 subn...
Q: You work at Agate Construction Company Ltd as the Information Systems (IS) Manager (ACCL). Your comp...
A: Introduction: It might also aid in the management of the development company's accounting and operat...
Q: What exactly do we mean by "cost to fix defects"?
A: The answer is as follows.
Q: List and explain any ten functionalities of hardware devices that could be deployed to assist the bu...
A: Justification: The topic asks us to list ten hardware functionalities that may be deployed to assist...
Q: An analog signal Xa(t) = sin(480nt) + 3sin (720t) is sampled 600 times per second. (a) Determine the...
A: The Nyquist sampling rate specifies a sampling rate for a signal which is two times the highest or m...
Q: 2. The second integer is the result 2. Furthermore, you are provided with the getExponent() function...
A: Step-1: StartStep-2: Declare three integer variable base, result, exponentStep-3: Take input from us...
Q: Instructions: 1. In the code editor, you are provided with a main function that asks the user for an...
A: Here I have defined the function named getFactorial(). In this function, I have used a conditional s...
Q: What is the difference between these ANN below and what is used for? 1- back propagation artificial...
A: Back propagation artificial neural network (BPANN): Artificial Neural Networks: A neural network i...
Q: Define multimedia
A: let's see the solution
Q: Name the five most important hardware components of a computer system.
A: five major hardware components of a computer system. A motherboard. A Central Processing Unit (CPU)
Q: lve troubleshooting difficulties, all technicians need the right equipment and expertise. Define the...
A: Troubleshooting: Troubleshooting is a method for systematically resolving a problem. The purpose of...
Q: Use mathametical induction to prove this-
A: proof is given below
Q: Explain instantaneous description of What is PDA? PDA Show that the following ambiguous. grammar is ...
A: about pda and ambiguous grammar
Q: What is checklist-based testing and how does it work? It should correspond to your project in the sa...
A: Introduction: These lists are often produced by professional testers with significant technical comp...
Q: What exactly is ACL in networking?
A: Introduction: The term "access-list" refers to a collection of rules that are used to regulate netwo...
Q: What are the ideal QoS settings for real-time network traffic-generating applications?
A: Intro QoS stands for quality of service. QoS refers to technology that work on a network by managing...
Q: An algorithm with running time E(/n(log n)²) spends exactly 1 millisecond to process an input of 1.0...
A: For processing 216 items 20.48 milliseconds required.
Q: What are Apple's stumbling blocks? Is there anything that can be done to address these issues?
A: Introduction: Apple's ambitions to offer discounted, reconditioned versions of its wildly popular iP...
Q: What are the two main distinctions between user-level and kernel-level threads? In what situations i...
A: Introduction: Threads created by users: User threads are implemented by users.User threads are easy ...
Do not copy from other websites
Upvote guarenteed for a correct and detailed answer. Thank you!!!
Step by step
Solved in 2 steps

- _____ is a CPU design technique in which instruction execution is divided into multiple stages and different instructions can execute in different stages simultaneously.Describe the concept of superscalar pipelining. How does it differ from traditional pipelining, and what benefits does it offer in terms of instruction execution?Describe the principles of VLIW (Very Long Instruction Word) and EPIC (Explicitly Parallel Instruction Computing) architectures. How do they differ from traditional pipelining?
- Discuss how pipelining concepts are applied in areas beyond traditional CPU architectures, such as software development and network processing.Describe superscalar and VLIW (Very Long Instruction Word) pipelines. How do these advanced pipelining techniques differ from traditional pipelining, and what advantages do they offer in terms of instruction execution?Explore the concept of dynamic instruction scheduling and its relevance in modern pipelined processors.
- Investigate the impact of superscalar and VLIW (Very Long Instruction Word) architectures on ALU instruction execution in modern processors.Explore the concept of instruction pipelining in the context of compilers and software optimization. How can compilers generate code that takes full advantage of pipelined processors?Explore the principles of superscalar and VLIW (Very Long Instruction Word) architectures. How do these approaches enhance instruction-level parallelism in CPUs?
- What is superscalar pipelining, and how does it differ from traditional instruction pipelining in terms of instruction execution?Dive into the concept of pipelining in CPU architecture. How does instruction pipelining improve the execution of instructions, and what are the potential challenges?This essay aims to elucidate the inherent limitations associated with the continuous addition of cores to a central processing unit (CPU) as a means to enhance its speed and keep pace with the growth dictated by Moore's Law.

