QUESTION 48 Which of the following umask settings will result in new files receiving the default permissions -rw---? O a. 0177 O b.0600 O c. 0688 O d.0188
QUESTION 48 Which of the following umask settings will result in new files receiving the default permissions -rw---? O a. 0177 O b.0600 O c. 0688 O d.0188
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter14: Troubleshooting Windows After Startup
Section: Chapter Questions
Problem 5TC: When a user, Belinda Lim, signs in to Windows, she cannot see her Documents folder in File Explorer...
Related questions
Question
100%
48 number solution needed
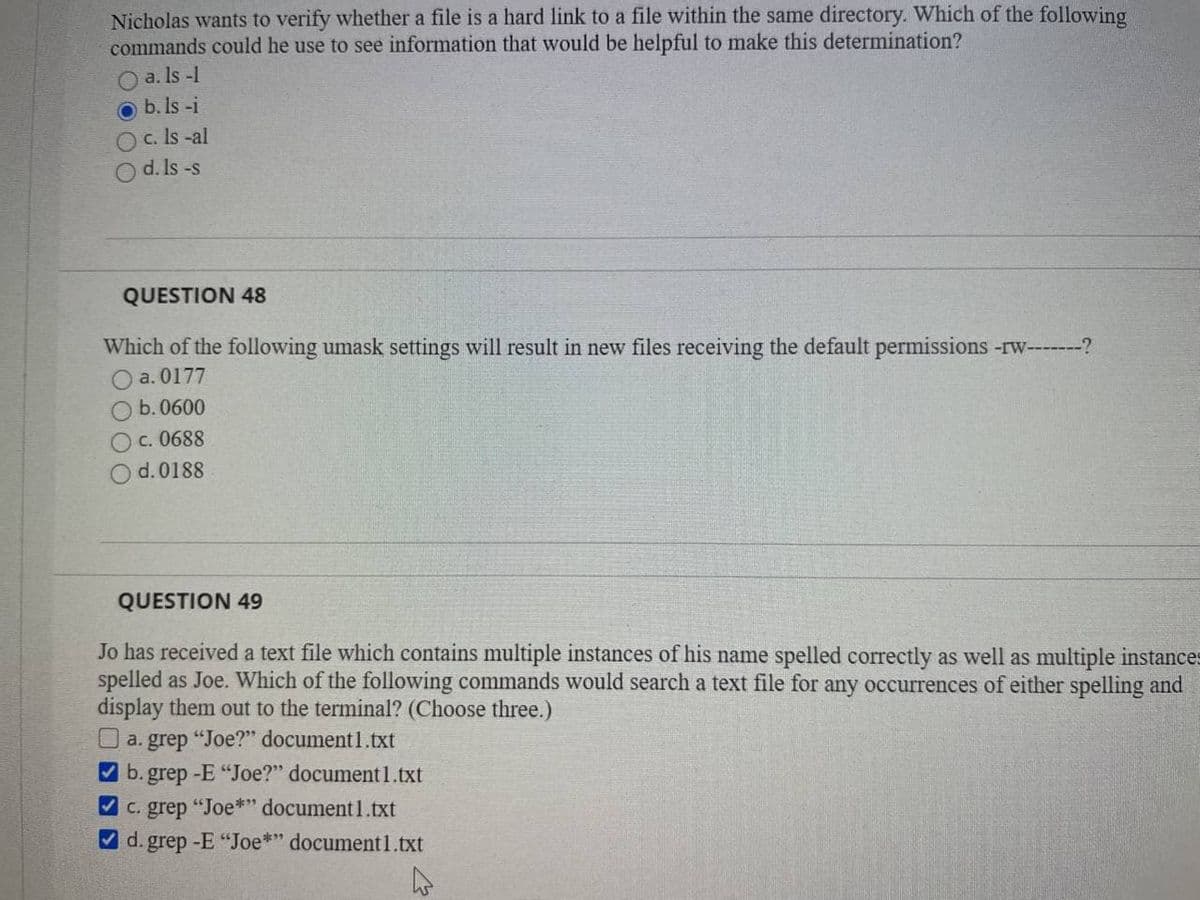
Transcribed Image Text:Nicholas wants to verify whether a file is a hard link to a file within the same directory. Which of the following
commands could he use to see information that would be helpful to make this determination?
O a. Is -1
O b. Is -i
O c. Is -al
O d. Is -s
QUESTION 48
Which of the following umask settings will result in new files receiving the default permissions -rw---?
a. 0177
b. 0600
Oc. 0688
d. 0188
QUESTION 49
Jo has received a text file which contains multiple instances of his name spelled correctly as well as multiple instances
spelled as Joe. Which of the following commands would search a text file for any occurrences of either spelling and
display them out to the terminal? (Choose three.)
O a. grep "Joe?" document1.txt
V b. grep -E "Joe?" document1.txt
V c. grep "Joe*" document1.txt
V d. grep -E "Joe*" document1.txt
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

CompTIA Linux+ Guide to Linux Certification (Mind…
Computer Science
ISBN:
9781305107168
Author:
Jason Eckert
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

CompTIA Linux+ Guide to Linux Certification (Mind…
Computer Science
ISBN:
9781305107168
Author:
Jason Eckert
Publisher:
Cengage Learning