QUESTION 5 Suppose you connect your laptop into a university network (either via wired ethernet or 802.11 wifi). How does your laptop get assigned an IP address with which it can send datagrams across the internet? O IP addresses are unique to each NIC, and therefore, a device does not need to take any action to obtain an IP address. O Every student is assigned a unique and static IP address for every laptop or device they register with IT. The laptop sends out a special ethernet (or 802.11) frame asking all hosts within the subnet to return their IP addresses. The laptop is free to select any IP address that is not in the returned IP address list. O The laptop sends out a DHCP request over UDP to the local DHCP server to obtain an available IP address. QUESTION 6 Which of the following is a disadvantage of using IPV6 addresses when sending datagrams in the network layer? In order to pass through a network with routers not supporting IPV6, we must use tunneling and carry the extra overhead of having both an IPV6 and traditional IP header. With the rate at which smart devices with connectivity are being produced, we will run out of unique IPV6 addresses in the next five to ten years. Very few routers are capable of supporting datagrams with IPV6 addresses. Those that do support it are often prohibitively expensive and only used by top- internet companies (e.g., Google). A router that services both IPV4 and IPV6 will often have namespace resolution issues wherein some addresses cannot be resolved as being traditional IPV4 or IPV6. QUESTION 7 Which of the following is true when a host is on a subnet that is separated from the rest of the internet via a router implementing NAT? O The host can send outbound datagrams to hosts outside of the subnet, but cannot receive responses. A remote host outside of the subnet cannot initiate a TCP connection with the host inside the subnet. The host cannot send (or receive) data to another host outside of the subnet without first encrypting any datagrams. O The host can send an outbound datagram to a remote host outside of the subnet without any risk of IP spoofing.
QUESTION 5 Suppose you connect your laptop into a university network (either via wired ethernet or 802.11 wifi). How does your laptop get assigned an IP address with which it can send datagrams across the internet? O IP addresses are unique to each NIC, and therefore, a device does not need to take any action to obtain an IP address. O Every student is assigned a unique and static IP address for every laptop or device they register with IT. The laptop sends out a special ethernet (or 802.11) frame asking all hosts within the subnet to return their IP addresses. The laptop is free to select any IP address that is not in the returned IP address list. O The laptop sends out a DHCP request over UDP to the local DHCP server to obtain an available IP address. QUESTION 6 Which of the following is a disadvantage of using IPV6 addresses when sending datagrams in the network layer? In order to pass through a network with routers not supporting IPV6, we must use tunneling and carry the extra overhead of having both an IPV6 and traditional IP header. With the rate at which smart devices with connectivity are being produced, we will run out of unique IPV6 addresses in the next five to ten years. Very few routers are capable of supporting datagrams with IPV6 addresses. Those that do support it are often prohibitively expensive and only used by top- internet companies (e.g., Google). A router that services both IPV4 and IPV6 will often have namespace resolution issues wherein some addresses cannot be resolved as being traditional IPV4 or IPV6. QUESTION 7 Which of the following is true when a host is on a subnet that is separated from the rest of the internet via a router implementing NAT? O The host can send outbound datagrams to hosts outside of the subnet, but cannot receive responses. A remote host outside of the subnet cannot initiate a TCP connection with the host inside the subnet. The host cannot send (or receive) data to another host outside of the subnet without first encrypting any datagrams. O The host can send an outbound datagram to a remote host outside of the subnet without any risk of IP spoofing.
A+ Guide to Hardware (Standalone Book) (MindTap Course List)
9th Edition
ISBN:9781305266452
Author:Jean Andrews
Publisher:Jean Andrews
Chapter8: Connecting To And Setting Up A Network
Section: Chapter Questions
Problem 3TC
Related questions
Question
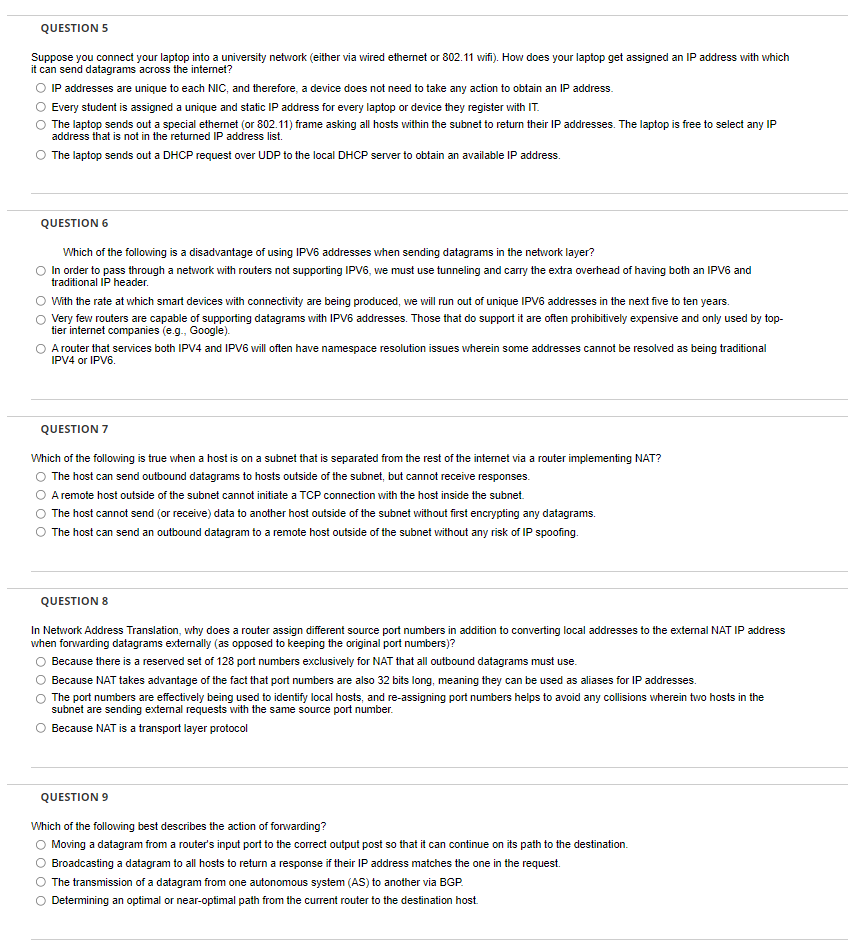
Transcribed Image Text:QUESTION 5
Suppose you connect your laptop into a university network (either via wired ethernet or 802.11 wifi). How does your laptop get assigned an IP address with which
it can send datagrams across the internet?
O IP addresses are unique to each NIC, and therefore, a device does not need to take any action to obtain an IP address.
Every student is assigned a unique and static IP address for every laptop or device they register with IT.
The laptop sends out a special ethernet (or 802.11) frame asking all hosts within the subnet to return their IP addresses. The laptop is free to select any IP
address that is not in the returned IP address list.
The laptop sends out a DHCP request over UDP to the local DHCP server to obtain an available IP address.
QUESTION 6
Which of the following is a disadvantage of using IPV6 addresses when sending datagrams in the network layer?
In order to pass through a network with routers not supporting IPV6, we must use tunneling and carry the extra overhead of having both an IPV6 and
traditional IP header.
With the rate at which smart devices with connectivity are being produced, we will run out of unique IPV6 addresses in the next five to ten years.
Very few routers are capable of supporting datagrams with IPV6 addresses. Those that do support it are often prohibitively expensive and only used by top-
tier internet companies (e.g., Google).
A router that services both IPV4 and IPV6 will often have namespace resolution issues wherein some addresses cannot be resolved as being traditional
IPV4 or IPV6.
QUESTION 7
Which of the following is true when a host is on a subnet that is separated from the rest of the internet via a router implementing NAT?
The host can send outbound datagrams to hosts outside of the subnet, but cannot receive responses.
A remote host outside of the subnet cannot initiate a TCP connection with the host inside the subnet.
The host cannot send (or receive) data to another host outside of the subnet without first encrypting any datagrams.
The host can send an outbound datagram to a remote host outside of the subnet without any risk of IP spoofing.
QUESTION 8
In Network Address Translation, why does a router assign different source port numbers in addition to converting local addresses to the external NAT IP address
when forwarding datagrams externally (as opposed to keeping the original port numbers)?
Because there is a reserved set of 128 port numbers exclusively for NAT that all outbound datagrams must use.
Because NAT takes advantage of the fact that port numbers are also 32 bits long, meaning they can be used as aliases for IP addresses.
The port numbers are effectively being used to identify local hosts, and re-assigning port numbers helps to avoid any collisions wherein two hosts in the
subnet are sending external requests with the same source port number.
Because NAT is a transport layer protocol
QUESTION 9
Which of the following best describes the action of forwarding?
Moving a datagram from a router's input port to the correct output post so that it can continue on its path to the destination.
Broadcasting a datagram to all hosts to return a response if their IP address matches the one in the request.
The transmission of a datagram from one autonomous system (AS) to another via BGP.
Determining an optimal or near-optimal path from the current router to the destination host.
O O
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide to Hardware (Standalone Book) (MindTap C…
Computer Science
ISBN:
9781305266452
Author:
Jean Andrews
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning