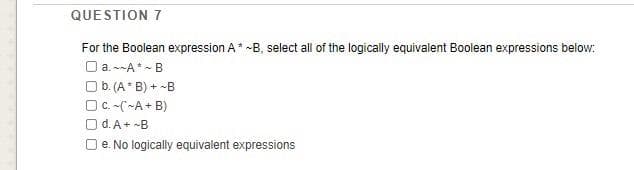
QUESTION 7 For the Boolean expression A* -B, select all of the logically equivalent Boolean expressions beiow: Oa. --A* - B Ob. (A* B) + -B OC. -(-A+ B) O d.A+ -B e. No logically equivalent expressions
Q: eld is it better to work to apply Machine Learning? Geoinformatics or
A: Below the better to work to apply Machine Learning
Q: A strategy that has not been attempted before will be unsuccessful. Recognize the numerous different…
A: Introduction: Testing is required to discover any faults in software that may cause damage. We risk…
Q: Utilize a request for proposal to collect information on hardware and system software, as well as to…
A: Introduction: What is an RFP, and how does it help analysts obtain data on hardware and software? A…
Q: What are some of the benefits of operating systems that are not dependent on a particular platform?
A: What are some of the benefits of operating systems that are not dependent on aparticular platform?
Q: Write (or borrow) a program in one of the following languages (C, C++ or Java). The program (or…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: There are certain variations in IT security implementation between conventional on-premises data…
A: Introduction: Cloud computing has limited customization choices, but on-premises systems are…
Q: The role of a firewall and how it might be implemented in your organization are discussed here.
A: Every system having the one of main motive to provide the security to the user, and every…
Q: For the fallowing 6th order linear system, 3 -1.2 0.03 -1.2 4.5 -0.4 0 -0.9 0.02 0.01 1.2 4.2 -1…
A: MATLAB CODE GAUSS SEIDAL METHOD normVal=Inf ;% Maximumtol=1e-5; % Tolerance…
Q: Explain how a cloud storage program varies from traditional client storage software in terms of…
A: Introduction Cloud Storage: Cloud storage is basically that type of model in which you can save…
Q: Write a MATLAB program that will perform the following mathematical operation: 10 2* = 2' + 22 + 2³…
A: Start Assign sum with 0 for loop runs for i value 1 to 10 sum <- sum + 2^i end print Sum of the…
Q: When it comes to cryptography, what is the difference between symmetric and asymmetric?
A: Introduction: Asymmetric encryption is a relatively recent technology compared to symmetric…
Q: Write the Git-commands necessary to clone the branch and? develop on your local PC. Imagine that you…
A: Git is a code collaboration tool, where developers can work and access the shared code repository as…
Q: Utilize a request for proposal to collect information on hardware and system software, as well as to…
A: Introduction: To be decided: Explain The use of a request for proposal to obtain information about…
Q: Some information technology security specialists believe that ex-computer criminals should be…
A: I believe that having a grey hat on a security team can be really beneficial. That's where my…
Q: In this lesson, we will discuss the link between the four information system functions, as well as…
A: Introduction: Gathering incoming data, storing it, processing it, and finally providing output data…
Q: Urite a Jara Program to take 3 integers from the user, one of them is small, one is medium and one…
A: We are going to write a Java program which will check three integeres are evenly spaced or not.
Q: Question 2: 1- Express the Boolean function F(A,B,C,D) = A' + BD' in (SOP) 2- Express the Boolean…
A: As per mentioned, I have provided the solutions for Part 4 and 5 of Q.2 Here, we are asked the…
Q: 1) Write VHDL code of the following circuitY=(a xor b) or (not (c and b) ).
A: The answer is as follows.
Q: 81 DATA SEGMENT 82 83 ENDS 84 05 CODE SEGMENT 86 07 START: 88 89 10 11 12 13 14 15 ENDS 16 END STARI…
A: Given that, DATA SEGMENT MESSAGE DB "HELLO WORLD!!!$" ENDSCODE SEGMENT ASSUME DS : DATA…
Q: Given the following fragment C program that convert from degrees Celsius to degrees Fahrenheit,…
A: double c = 20;double f;f = (9/5) * c + 32.0;f = 52.0 b first 9/5 = 1 because 9 is int and 5 is int…
Q: Q2) Use the point2D class as base class to derive a new class called Point3D(x,y,z). In addition to…
A: #include "Point3D.h" #include "Point2D.h" #include "Point3D.h" #include <cmath> #include…
Q: Im not sure what the Cybercrime Conceptual Framework is, or how it works. You should add references…
A: The solution to the given question is: Computer and network crime is called cyber crime. The…
Q: hat exactly is the difference between the Screen and Overlay blending modes in Photoshop?
A: Blending Modes in Photoshop: It comes in early 1994 as the first layer of photoshop and there are…
Q: i) Write a Java program to find the number of loops in the array given below. A loop is defined as a…
A: Required:- ii) Write a Java program to find the number of loops in the array given below. A loop is…
Q: library system that includes 1.serach a book. 2.add new book. 3.remove a book. 4.print book…
A: def Menu(): print("Library Management System") print("-"*30) print("-"*30) print('''…
Q: When it comes to cryptography, what is the difference between symmetric and asymmetric?
A: Introduction: The essential distinction between them is that the symmetric cryptosystem only…
Q: I'm not sure what the Cybercrime Conceptual Framework is, or how it works. You should add references…
A: INTRODUCTION: Cybercrime: It is often known as computer crime, which is the unlawful use of a…
Q: A strategy that has not been attempted before will be unsuccessful. Recognize the numerous different…
A: Introduction: Testing is required to uncover any faults in software that might cause damage. Without…
Q: Write a program to determine the cost of an automobile insurance premium, based on driver's age. and…
A: Use an if else if ladder to validate the age, price and then finally prints insurance
Q: What are the measures that can be taken by individuals and organizations to minimize the invasion of…
A: 1. Check social privacy settings If you have social accounts, those networks have a lot of…
Q: Which search engines are legal and ethical in their operations?
A: Introduction: When we compare Ecosia to Google, we can see that Ecosia has a far better ethical…
Q: Which log in Event Viewer would you use to track down attempted computer logins, if you had to?
A: Events that occur in the system are recorded in the event viewer, which also keeps a log file for…
Q: Please offer an example of a computer-based system, as well as a summary of the features of that…
A: Introduction: Software, hardware, people, a database, documentation, and procedures are the…
Q: y1= sin(x) y2= sin(2x) • y3= sin(3x) % 1st plot is to be red and dashed % 2nd plot is to be blue and…
A: Code: x = -6:0.2:6; y1 = sin(x); y2=sin(2*x); y3=sin(3*x); plot(x,y1,'r--') hold on…
Q: I'm not sure what the point of routing is or how it works. Separate and contrast the differences…
A: Answer :
Q: Are embedded computers and general-purpose computers different in terms of what they do?
A: Embedded Computers is also known as embedded systems.
Q: Describe the many forms of semantics, when and how they are utilised, as well as the advantages and…
A: Semantics: Semantic is a linguistic concept separate from the concept of syntax,which is also…
Q: Discuss any ERP benefits when deciding to adopt an ERP system.
A: The solution to the given problem is below.
Q: What are some of the benefits of operating systems that are not dependent on a particular platform?
A: Introduction: CamSaS is working on a special-purpose operating system called Data Intensive…
Q: (20 points) Consider the following function: 100(1 – 0.01x²)² + 0.02.a² (1 – x²)² + 0.1x² y(x) =…
A: % Script Description:Subplots with different plot schemes% Name :% Date…
Q: Write a Java Program to take 3 integers(a.b.c) from the user., print "Great Number" if one of b or c…
A: Java program: Java is a class based, high level object oriented programming language. Java is…
Q: where: a=2; and b=3; c1='A'; c2='a'; printf("The NUMERIC VALUE of %c is…
A: Ascii value of A=65 Ascii valued of a=97
Q: Question: Input an expression containing opening and closing parenthesis. Write a C program to check…
A: In the given question opening and closing parentheses are used to represent the mathematical…
Q: Utilize a request for proposal to collect information on hardware and system software, as wel as to…
A: Introduction: A computer system is comprised of two distinct components hardware and software.…
Q: 2. Encrypt the word SHIELD using an alphabetic Caesar shift cipher that starts with a shift of 8 (A…
A:
Q: Given input {71, 22, 21, 99, 53, 69, 39} and a hash function h(x) = x mod 10, show the resulting:…
A: h(x) = x mod 10. This says, there are 10 locations in hashtable starting from index 0 to 9. It is…
Q: The database administrator has the ability to choose the number of disks that will be clustered…
A: Introduction: Using disc striping with parity, RAID 5 creates a redundant array of separate discs No…
Q: Create an Android Application using java that serves restaurant clints. The user can do the…
A: We are attaching both the XML and JAVA code in the below steps along with the screenshots and output
Q: Discuss different defenses against Man-in-the-Middle (MITM) attacks, which collect wireless…
A: Introduction: A man in the middle (MITM) attack is a broad phrase that refers to when a perpetrator…
Q: Explain how a cloud storage program varies from traditional client storage software in terms of…
A: Introduction: Traditional storage is a kind of storage in which data is stored on local physical…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- Question 5 Use the laws of Boolean algebra to show that the two Boolean expressions below are equivalent. Label each step with the law used to reach it. (Note you are proving the Absorption Law, so don't use that law in your answer!) x + xy = x Full explain this question and text typing work only thanksCan anyone please help to create a logic diagram based on the equation K0 = A’ ? ( This question is not a part of any graded assignment)2. Look for the dual of the following Boolean expressions:a. xyz + x'y'z'b. xz' + x⋅0 +x'⋅1
- Choose the best answer :If the final column of a truth table of a given statement formula has all F then it is called a) A Contradiction b) A negation statement c) none of the aboveI need help to answer Question no. 30 prove that the below WFF is a valid argument. (∀x)(∀y)[(P(x) Λ S(x,y)) →Q(y)] Λ (∃x)B(x) Λ (∀x)(B(x) → P(x)) Λ (∀x)(∃y)S(x,y) → (∃x)Q(x) Chapter 1.4 - Predicate Logic Text Book: Discrete Mathematics and its application 7th edition. Author: Judith L Gersting.What's the logic circuit of this logical statement?A'.C'+A.B.C+A'.B
- Discrete Mathematics: Write each of the two statements in symbolic form and determine whether they are logically equivalent. Include a truth table. "If two is a factor of n and 3 is a factor of n, then 6 is a factor of n. 2 is not a factor of n or 3 is not a factor of n or 6 is a factor of n."Which logic law could be applied to the following clause? please give an explanation of the reasoning. ¬((a∧b)∨(c∨d))Translate each of these nested quantifications into an English statement that expresses a mathematicalfact. The domain in each case consists of all real numbers.a) ∃x∀y(x + y = y) b) ∀x∀y (((x ≥ 0) ∧ (y < 0)) → (x − y > 0))c) ∃x∃y(((x ≤ 0) ∧ (y ≤ 0)) ∧ (x − y > 0))d) ∀x∀y((x ≠ 0) ∧ (y ≠ 0) ↔ (xy ≠ 0))

