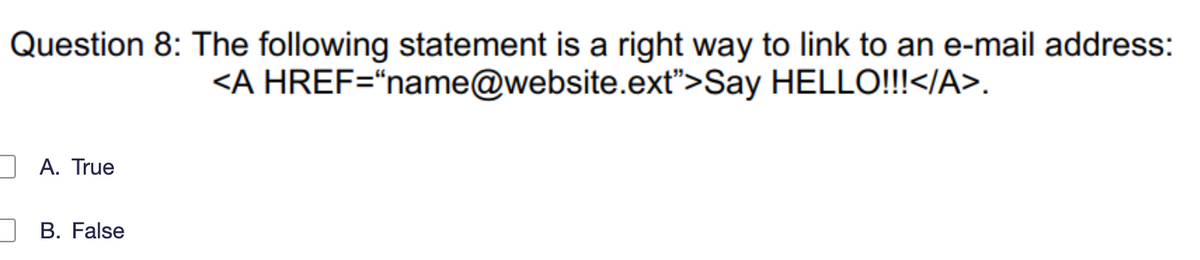
Question 8: The following statement is a right way to link to an e-mail address: Say HELLO!!!. A. True B. False
Q: To be more explicit, in what ways are the BIOS and UEFI passwords on certain PCs able to be…
A: The answer of the question is given below
Q: If the style sheet in Question 4 is named style.css, please at right place add a proper statement in…
A: Style Sheets For Web page developers, style sheets offer a significant advancement in their capacity…
Q: Give specific examples of each method for preventing OS intrusions.
A: Introduction: Gadget or programming application screens organization or frameworks for pernicious…
Q: ow should someone continue if they have forgotten both the administrat assword and the system's…
A: Introduction: Below describe continue if they have forgotten both the administrator password and…
Q: What three factors are taken into account while choosing hardware?
A: The hardware includes your desktop and laptop computers, servers, printers, portable storage…
Q: table comparing HTTP and WebSocket differences.
A: Introduction of HTTP: HTTP protocol is unidirectional used in the client-server computing where the…
Q: How do the BI architecture's elements work together to create a cohesive system?
A: Business Intelligence (BI) Business Intelligence is the most significant and valuable methodology…
Q: If there is one thing that can be stated about software engineering's primary goal, it is this:…
A: Introduction: Software engineering assists you with making a capable response to the issue in a…
Q: How to use rules of logic to simplify ¬q∧(p⇒q) ?
A: Given expression is, ¬q∧(p⇒q) It contains the variables p and q.
Q: Write a program that uses two nested for loops and the modulus operator (%) to detect and print all…
A: Dear Student, As no programming language is mentioned I am assuming it to be c++.
Q: Explain what is meant by the term "caching" when referring to shared memory
A: The cache is a temporary storage area which can retrieve data easily by a computer processor.…
Q: The Common TCP/IP Ports are an example. To correctly design security, businesses must comprehend the…
A: A PC network is a group of computers that share resources on or given by the organization hubs. They…
Q: What effects will the internet of things (IoT) have on how we live our lives? Give an illustration…
A: IoT The Internet of Things (IoT) is an arrangement of interrelated registering gadgets, mechanical…
Q: firewalls for physical security measures.
A: Introduction: Physical security refers to protecting an organization's physical assets, such as its…
Q: What are some of the drawbacks of having pages that are fragmented?
A: Introduction: Fragmentation is an unfortunate issue in the functioning system where the cycles are…
Q: 5. Creating Lookups 6. Automatic Lookups 7. Geospatial Lookups 8. External Lookups 9. KV Store…
A: 5. Creating lookups: Creating a lookup field not only improves the meaning of the data, but helps…
Q: DoS attacks often include the flooding of servers, systems, or networks with traffic, which prevents…
A: In DoS multiple system attack a target and that will result in denial of service for user. It can…
Q: What are the biggest obstacles that companies face when trying to switch to a cloud computing…
A: A cloud platform is the operating system and hardware of a server located in a data center connected…
Q: a. If the last operation performed on a computer with an 8-bit word was an addition in which the two…
A: I have mentioned answer in below steps (a) 000000100000001100000101 Carry = 0; Zero = 0;…
Q: Take into account a job in selling computer gear. Do you believe that the strongest sales…
A: Computer hardware is, in the simplest terms, the physical parts required by a computer system. It…
Q: Problem 3. Let (u, v) be a minimum-weight edge in a connected graph G. Show that (u, v) belongs to…
A: let(u,v) minimum weight show that u,v belongs to some minimum spanning tree of g
Q: a. If the last operation performed on a computer with an 8-bit word was an addition in which the two…
A: please check the solution below
Q: Why is it necessary to study software engineering fundamentals if you are a programmer?
A: Software Engineering Fundamentals is such topics as software metrics, real-time software design,…
Q: Why would you want to use a firewall?
A: A firewall is a networking-based security system which is as to monitor network traffic and it acts…
Q: Think about the standard TCP/IP ports. To correctly build security, businesses need to be aware of…
A: The idea of ports and Demultiplexing or Multiplexing is utilized by the transportation layer…
Q: esource allocation grph
A: We are given a resource allocation graph and we are going to find out if there is any cycle and…
Q: Declare a string of 20 unsigned bytes named bArray and initialize all the elements to zero
A: INTRODUCTION: A source operand, a destination operand, or both are possible requirements for each…
Q: When should data be kept in conventional files?
A: Introduction A record of the bosses' design deals with the procedure for inspecting and making data…
Q: Assume the following C code is stored in a file named main.c. Please split it into two files where…
A:
Q: Write a struct that defines a binary tree node
A: In C, we can use structures to represent a tree node. We can use classes as a component of other…
Q: Why should we use the OSI Security architecture?
A: The OSI security architecture assists managers responsible for an organization's security in…
Q: which among the following is not a privacy harm
A: Privacy harm Unexpected or compelled use of a person's personal information against them falls under…
Q: values
A: Dear Student, Hashing refers to the process of converting object data into a representative integer…
Q: what are the Example of streaming data?
A: Data is sent to a streaming application by detectors in farm machinery, industrial machinery, and…
Q: What advantages might a RAID Level 2 system provide to a university payroll system? What, if any,…
A: The answer of the question is given below
Q: 2. Matrix Quantum Mechanics. Use python matrix and algebraic tools for this problem. Consider…
A: Yes, the operators C and P commute. To find the eigenvalues and normalized eigenvectors of given…
Q: Which of the following algorithms is not follow a greedy approach? Sum-of-subsets algorithm…
A: A greedy algorithm is used for solving optimization problems. It is an approach where we select the…
Q: Describe and contrast the various methods available for scheduling Linux commands to be performed at…
A: We can complete various tasks at specific times and dates with the assistance of commands for…
Q: Describe simply, if at all possible, what Machine Language involves. Also, why can't English be…
A: The computer reads and interprets a set of binary numbers or bits known as machine language, often…
Q: Provide an overview of the built-in antiviral programme for Windows, Windows Defender
A: Here is the solution:
Q: Evidentiary files or files of interest are categorized as _______. evidentiary…
A: Answer:- notable
Q: 3.2 Write a program that contains two instructions: (1) add the number 5 to the EAX register, and…
A: Source Code: The code instructions are as follows: INCLUDE Irvine32.inc.codemain PROC ; consider the…
Q: Fixed-price contracts, where the contractor bids a fixed price to complete a system development, may…
A:
Q: Until a file signature analysis is run, EnCase relies on the ______ to determine its file type.…
A: Here is the explanation about EnCase:
Q: Not all augmenting paths are equal, and starting with different paths leads to different residual…
A: Your answer is given below. Introduction :- Given that, Not all augmenting paths are created equal,…
Q: Transitive-Closure Input: a list of pairs, L. Interpreting L as a binary relation,…
A: Transitive Closure is the accessibility matrix to get from vertex u to vertex v of a graph. Given a…
Q: A new type of keyboard is being developed with the same functionality as a regular QWERTY keyboard.…
A: We will be using priority encoder digital circuit to implement the keyboard
Q: After finding out you are secretly part of the royal family of Genovia, you inherit a 16th-century…
A: I have mentioned hand writened answer in below steps ,please follow steps
Q: Assume that after installing a motherboard, someone forgets to connect the wires from the casing to…
A: Numerous wires protrude from the front panel of the computer casing and link to the motherboard's…
Q: List the justifications for why a company could want firewalls for physical security measures.
A: According to the information given:- We have to list the justifications for company could want…
Step by step
Solved in 2 steps

- Which of these statements is false? A) Cookies identify you personally by name B) Cookies contain preferences and shopping cart information. C) A site usually uses multiple tracking cookies D) Cookies can help get targeted adsWhich of the following statements about cookies is true? a. Cookies were originally intended to facilitate advertising on web. b. Cookies allow websites to off load the storage of information about visitors. c. Cookies always contain encrypted data d. Cookies are text files and never contain encrypted data. e. None of the above is true.Which of the following is user data that is collected automatically? A) user address B) credit card number C) date of birth D) cookie I’d
- Wireless error correction works best. This statement: yes or no? Provide instances.Which one of the following statements is NOT correct about HTTP cookies? a. A cookies is a piece of code that has the potential to compromise the security of an Internet user b. A cookie gains entry to the user’s work area through an HTTP header c. A cookie has an expiry date and time d. Cookies can be used to track the browsing pattern of a user at a particular sitedont post copied content else surely dislike
- DO NOT COPY FROM OTHER WEBSITES Which of the following has incorrect syntax? state reason?You are creating an app that will allow university students to connect with advisors and other students to discuss stressful situations. Only students who attend the university can access the app. Which two steps should you take to protect student’s identity and personal information? (Choose two.) Group of answer choices Hash student data transmissions with a random salt. Hash the password using an algorithm in the Google database Hash the password with a random salt. Encrypt the password. Encrypt student data transmissions.which of the following statements about email and malware are correct? ( choose all that apply)
- Which of the following description regarding the RSA encryption are correct? Group of answer choices RSA Encryption is a symmetric key crypto In RSA Encryption, only the private key can be used to encrypted data. RSA Encryption is an asymmetric key crypto In RSA Encryption, both private key and public key can be used to encrypted data.Please answer all the three choosing the answer option. Thanks a lot in advance. 5) _______________ After an ACL is creatred , a unique number is specified for the ACL. Answer: True or False 6) The component of passivew IDS that deals is a collection of patterns and definitions of known suspicious activities. a) Analysis Engine b) Traffic Collector (Sensor) c) Signature Database d) Protocol Ana;yzer 7) ______________ Many centralized anti-spam methods allow individual users to customize spam filtering for their specific inbox. Answer : True or False.Help with React Try to open the same page in any other browser or incognito tab and you will see that the values didn't persist. Why weren't your answers available in the other browser/incognito tab? ============================================================================== import React from "react"; import { Formik, Form, Field } from "formik"; import { useCookies } from "react-cookie"; const App = () => { const [cookies, setCookie] = useCookies(["name"]); const localStorageKey = "email"; return ( <Formik initialValues={{ name: cookies.name || "", email: localStorage.getItem(localStorageKey) || "", }} onSubmit={(values, { setSubmitting }) => { setTimeout(() => { setCookie("name", values.name, { path: "/" }); localStorage.setItem(localStorageKey, values.email); alert(JSON.stringify(values, null, 2)); setSubmitting(false); }, 400); }} > {({…

