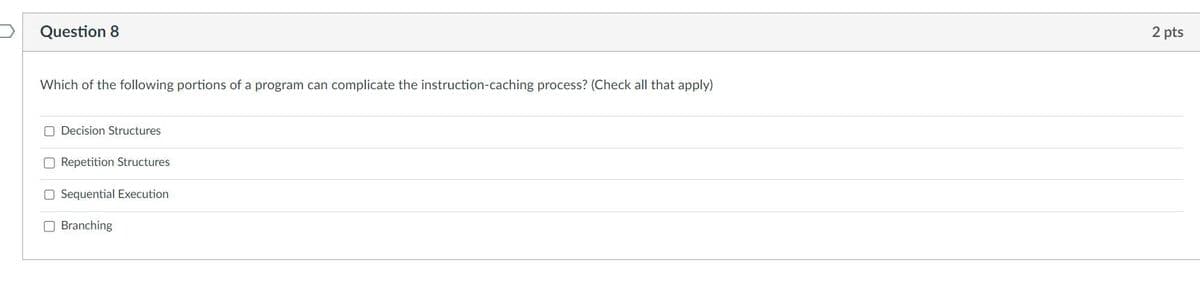
Question 8 Which of the following portions of a program can complicate the instruction-caching process? (Check all that apply) Decision Structures Repetition Structures O Sequential Execution Branching 2 pt:
Q: While building the microkernel of an operating system, what fundamental design principles should be…
A: Intro The idea behind the microkernel operating system is to have a minimal kernel that handles just…
Q: How would you define modern means of communication? To elaborate, please make use of the appropriate…
A: Introduction The act of sharing information, ideas, and messages with other individuals or groups is…
Q: What advantages does the analysis of clicks stream bring to different types of businesses?
A: In recent years, clickstream analysis—which involves monitoring and examining user clicks and…
Q: When referring to the state of a number, what does it mean when a bit is "activated"? What does the…
A: Introduction: Depending on how you purchased your copy of Windows 11, you will either need a digital…
Q: Please provide examples of the three most common types of file organization
A: The three most common file management strategies are hierarchical, network, and relational. Each of…
Q: Is there any way that the advancement of technology has altered the way that we speak to one…
A: Answer: Introduction Advancement of technology such as artificial Intelligence , machine learning…
Q: In-depth description of what a data warehouse is and how it works. Moreover, why was a data…
A: The data warehouse is similar to the information system in many ways. Data warehouses may be thought…
Q: Why do most people believe that the Internet represents the
A: The Internet is undoubtedly one of the most significant technological developments of the 20th…
Q: Why do most people believe that the Internet represents the pinnacle of today's information and…
A: Definition: The abbreviation "ICT" refers to a set of technological tools and resources that are…
Q: Group A has a mean of 0 and a median of 15 What is most likely true? Question 8 options:…
A: Dear student, the answers are provided below.
Q: In what way do communications and the field of data communications relate to one another? Does one…
A: All the above subparts question is solved in step 2 :-
Q: When applied to a concrete thing, what does the term "operating system" signify? Can you name the…
A: When applied to concrete thing, an operating system generally refers to software that manages…
Q: Why do most people consider the Internet to be the pinnacle of modern communication and information…
A: Just a quick note: The internet, the most powerful instrument of the 21st century, has advanced…
Q: a comprehensive description of what a data warehouse is and how it works. For that matter, what was…
A: A data warehouse is a centralized database that stores data from various sources and is optimized…
Q: s may choose to use a seven-step process by using
A: Interface design is a complex and iterative process that involves creating interfaces that are easy…
Q: How may information assurance be thwarted, and what kinds of services or safeguards are available to…
A: Cyber attacks: Cybercriminals can use various techniques to gain unauthorized access to sensitive…
Q: How many steps are there in creating a website? First, briefly explain each stage, and then explain…
A: Introduction A website is a collection of connected web pages and multimedia content that is…
Q: How would you define modern means of communication? To elaborate, please make use of the appropriate…
A: The technology of communication: The term "communication technology" refers to any technology that…
Q: How would you approach developing a real-time operating system if you had to write the code for it?…
A: Operating System in Real Time Real-time operating systems are designed to perform tasks within…
Q: Produce a catalogue of the most common file operations and characteristics, together with brief…
A: A file is a grouping of logically related information and is saved on secondary storage through a…
Q: It is essential that you have a solid understanding of the distinction between an operating system…
A: OS Intro User-computer interfaces are OSs.OSes manage hardware, software, and programme services.…
Q: Find out which passwords are incorrect and how to make the necessary changes.
A: According to the question, Cybercriminals utilize several tactics to break into your accounts. The…
Q: s? For those of you familiar with IRQs, please tell me whether the key is added to the keyboard…
A: When a key is pushed on a keyboard while using software to burn a CD, it depends on the specific…
Q: What kind of a management technique does Linux use for its virtual memory?
A: Virtual memory The term "virtual memory" refers to a method of memory management that enables a…
Q: Interface designers may choose to use a seven-step process by using a hierarchical task analysis as…
A: Yes, interface designers may choose to use a seven-step process that includes a hierarchical task…
Q: To what extent does Windows take the initiative to solve problems, as opposed to relying on users to…
A: Answer Windows has various built-in features that can take the initiative to solve problems…
Q: Can you describe the characteristics of a Unified Communications System? How do businesses who…
A: The answer is given in the below step
Q: ply Prims algorithm to the graph below, starting with vertex a. Construct a table that shows the…
A: Prim's Algorithm: It is a greedy algorithm. It is used to find minimum spanning tree from given…
Q: a differentiation between frequency multiplexing and temporal multiplexing (According to commuter…
A: Here is your solution -
Q: i need Pseudocodes and Algorithm and Flowchart Resolve the following problem by following all the…
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Digital communication has become more popular than traditional methods of communication like talking…
A: Each and every business undertakes a particular project and develops that project in accordance with…
Q: I have the following SQL Script: CREATE OR REPLACE TRIGGER SCSP_VIEW_UPDATE INSTEAD OF UPDATE ON…
A: We have to create How to add logic so that blanks and empty strings cannot be used to update…
Q: Compared with 4Gnetworks,5Gnetworks_______, support fewer devices have higher latency transmit…
A: Introduction : It is very easy to find out the option for the current question we have . We are…
Q: Phishing is a type of social engineering attack often used to steal user data, login credentials and…
A: Phishing is a type of cyberattack in which a dishonest person or business sends emails or messages…
Q: Could we make a complete inventory of the RAM-based components of an OS?
A: A comprehensive inventory of RAM-based operating system components would be difficult to offer…
Q: In the context of the twenty-first century, what role do constraints on access serve? We ask that…
A: Introduction: A kind of cyber security known as "access control" regulates which programmes and…
Q: 6. Determine the breadth-first and depth-first traversals for the following graph: (start with…
A: Depth First Search (DFS) and Breadth First Search (BFS) are algorithms used to traverse or search a…
Q: What should be the overarching idea while creating a microkernel for an OS? As compared to the…
A: According to the information given:- We have to define the overarching idea while creating a…
Q: Unfortunately, we can't provide any insight into the inner workings of an OS.
A: Your answer is given below.
Q: How is a pre-packaged data model different from a clean slate when it comes to kickstarting a data…
A: Let us examine the answer. Like architects study blueprints before creating a structure, you should…
Q: Is Microsoft's Windows OS meant to be proactive or reactive? The performance of each is being asked…
A: Microsoft's Windows OS is designed to be both proactive and reactive.
Q: Provide a few examples of the three broad classifications of file management.
A: File management: It is the process of organizing, storing, managing, and manipulating files on a…
Q: Offer methods for locating and warding off intrusions into the system.
A: A hardware or software programme that monitors a network or system for malicious activity or policy…
Q: Please highlight the most vital features of an operating system. Here is a summary of the key…
A: Operating system: An operating system is a programme that runs application programmes and serves as…
Q: Does the OS's microkernel adhere to any established guidelines? Is there a difference between this…
A: Microkernel operating systems allow other system services to run in user space like any different…
Q: Your task for this lab is to write a program in any language you like(c language) to determine the…
A: We have to create a program which follows the fibonacci rule and by the help of which we have ot…
Q: With what you're about to read, you can understand why data modeling is crucial.
A: Data modeling plays an important role in creating a database that meets the specific requirements of…
Q: When one begins with a product that they have purchased, the process of data modeling is different…
A: Introduction: In the process of making software products, data modelling is an important step. It…
Q: Which key distinctions distinguish the World Wide Web (WWW) from its more familiar counterpart, the…
A: Introduction The World Wide Web (also known as WWW) and the Internet are two terms that are…
Q: Provide answers to the following Questions: a) What can you do to change the content of a String? b)…
A: Answer is
No hand written and fast answer with explanation
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Multiple choice1. The following operations (instruction) function with signed numbers except one. a. SHL b. IDIV c. SAR d. IMUL 2. Suppose AX = 5 (decimal), what will be the value of AX after the instruction SHL AX,3 executes? a. 20 b. 15 c. 9 d. 40Write your own understanding and additional discussion from the following Explain and Discuss in your own words the Instruction Execution **not less than 200 words in each item.Question With the help of an example, describe in detail how PUSH, POP, CALL and Ret instruction works? Explain with the help of a program and also draw diagrams where necessary ---------------------------------------------------------------------------------
- Help me answer this question Picture below show the steps involved in execution of a program inside computer. Identify P, Q, R and S. Explain EACH step involve in instruction-time (i-time) and execution-time (e-time) when computer executing mathematical formula.The instruction below was given to a computer to execute. Kindly identify the possible outcome of the instruction set after execution. Briefly describe if any possible problem(s) or bugs can occur and explain how to correct these bugs. Remove the burned-out bulb Insert a new bulbPlease answer the question below alongside the following; Describe what you expect the instruction to do.
- How may empty calculation cycles be avoided while a computer processor is processing a huge number of instructions? Explain why they should be excused for the consequences of their actions.Question1: Multiple Choice : (please leave it to other tutors who can answer all my sub-question since this is my last question for this month) 1-If for some inputs, a procedure never terminates, the procedure lacks a. computability b. definiteness c. finiteness d. scalability 2-The elements of the ISA for a particular type of CPU include a. addressing modes b. data types c. instructions d. a and b e. a, b and c Question 2: Perform the following logical operations and express your answers in hexadecimal notation. x3487 AND x7254 xABCD or x3234 xF098 XOR x3344How are empty calculation cycles avoided when several instructions are being processed simultaneously by a computer processor, and what are the essential elements of such processing? Give an explanation of what transpired as a result of their actions.
- Question 5 • What are the actions involved during instruction execution? Explain the Fetch cycle or CPU cycle with a proper diagram. Full explain this question and text typing work only thanksAnalyze the flow chart below. QUESTIONS: 6. Determine - calculate the delay generated by [DE] and the value of "F" after the instruction [A]<-[A]v[E] is executed the first and the 10th time. 7. Determine - discuss the contents of the displays. 8. Estimate - Calculate the shortest execution time of the program in terms of instructions, cycles, and seconds. 9. Repeat Part 8 for the longest execution time. 10. Are the two PUSHH instructions required? Discuss.[}][|Question 13 sum.This is for assembly language.1.what are the disadvantages of passing parameters through registers? Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line

