Question 85 Two key method is a) popular method in e-commerce b) used by encryption algorithm to transform a plain-text message into a cipher c) provides secure transmission d) used in database storage of payment data e) All options are correct O 1) a O 2) b O 3) c O 4) d O 5) e
Question 85 Two key method is a) popular method in e-commerce b) used by encryption algorithm to transform a plain-text message into a cipher c) provides secure transmission d) used in database storage of payment data e) All options are correct O 1) a O 2) b O 3) c O 4) d O 5) e
Chapter7: Working With The Bash Shell
Section: Chapter Questions
Problem 7DE
Related questions
Question
10
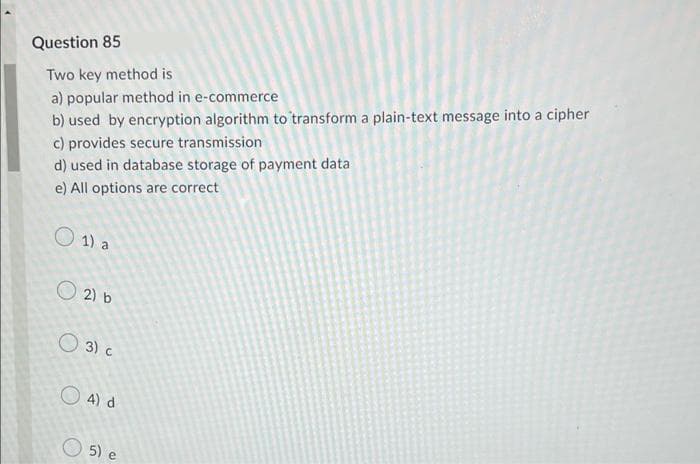
Transcribed Image Text:Question 85
Two key method is
a) popular method in e-commerce
b) used by encryption algorithm to transform a plain-text message into a cipher
c) provides secure transmission
d) used in database storage of payment data
e) All options are correct
O 1) a
O 2) b
O 3) c
O 4) d
O 5) e
Transcribed Image Text:18
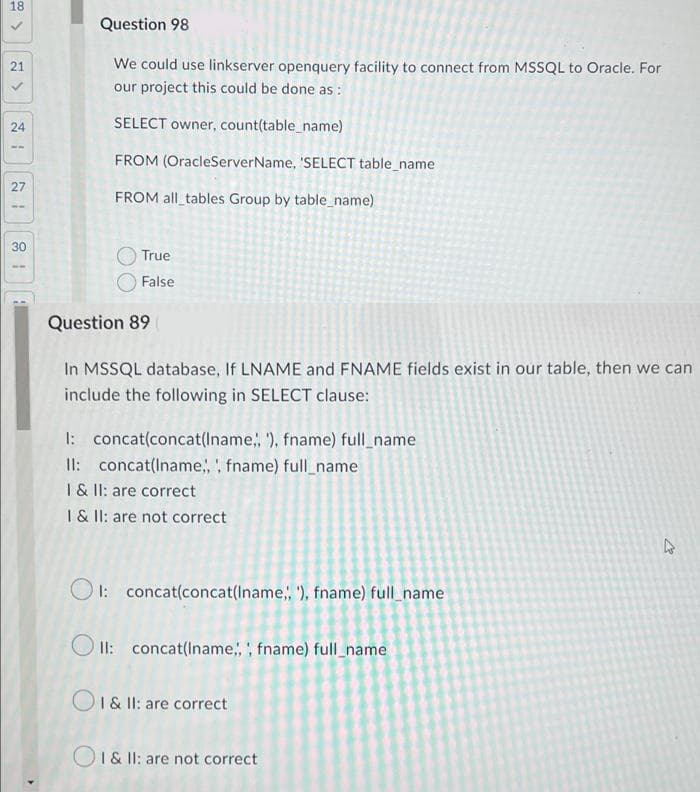
Question 98
21
We could use linkserver openquery facility to connect from MSSQL to Oracle. For
our project this could be done as :
24
SELECT owner, count(table_name)
FROM (OracleServerName, 'SELECT table_name
27
FROM all_tables Group by table_name)
30
True
False
Question 89
In MSSQL database, If LNAME and FNAME fields exist in our table, then we can
include the following in SELECT clause:
1: concat(concat(Iname,, '), fname) full_name
II: concat(Iname,,, fname) full_name
1 & II: are correct
I& II: are not correct
O 1: concat(concat(Iname;, '), fname) full_name
O II: concat(Iname,, fname) full_name
O1& I: are correct
OI& II: are not correct
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L


LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L
