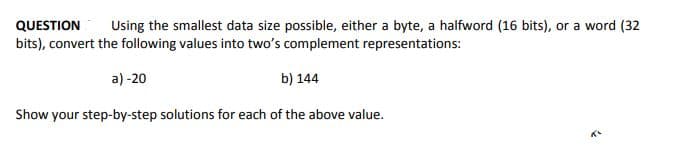
QUESTION bits), convert the following values into two's complement representations: Using the smallest data size possible, either a byte, a halfword (16 bits), or a word (32 a) -20 b) 144 Show your step-by-step solutions for each of the above value.
Q: If data were read from a node other than the main (master) copy, the database may be in an…
A: In a database, replication refers to the act of copying data from a single database to several…
Q: A partial view of interrupt branch table is given below: Address SWI FFFA 10 FFFB BF NMI FFFC 82…
A: When servicing an exception in 6809, at minimum the following register are pushed onto stack PD,…
Q: oneer, develop?
A: Augusta Ada Lovelace, Ada King, Countess of Lovelace, Ada Lovelace, Ada King, Countess of Lovelace,…
Q: What are some of the reasons why a penetration tester could utilize aircracking during an…
A: Answer: Aircrack-ng is a set-up of wireless penetration testing apparatuses used to evaluate the…
Q: Fvbfrftcff
A: I am sorry but what is the question? Please do clarify
Q: echo Enter your Name: read studentnane echo Enter your First Grade: read grade1 echo Enter your…
A: echo is used to print the content on console read is used to read the contents from console Now this…
Q: Taylor Series 1 (x-10)2 f (1x) 50 V507 1. Use MATLAB to plot for above function 2. Obtain the…
A: Matlab Program: % Answer 1 % symbolic functionsyms xf=(1/sqrt(50*pi))*exp((x-10)^2/50); fplot([f])…
Q: Simplify the complement of the following function: F(A,B,C,D)=(0,2,4,5,8,9,10,11)
A:
Q: What are the advantages and disadvantages of using a serial bus versus a parallel bus to transfer…
A: Your answer is given below. Introduction :- A bus is a system that allows data to be transferred…
Q: Which one, waterfall or agile, do you believe is better suited for a project with well-defined needs…
A: FRAMEWORK FOR AGILITY: The agile framework is a software development phase that can respond to…
Q: Q3: Write a program in MATLAB to enter numbers from 1 to 20 and * .printing only the odd numbers
A: I give the code in Matlab along with output and code screenshot
Q: Q2: Give the output of the following program Matlab 1. S-input('Enter the subject:','s'); 2.…
A: The program is to take subject name and marks of a student as user input, then make an array of…
Q: What are some of the reasons why a penetration tester could utilize aircracking during an…
A: The Evaluation: A program's evaluation is a procedure that evaluates it critically. It entails…
Q: In the case of a data security breach, what are the company's rules for disclosing information?
A: Steps to Create an Emergency Evacuation Plan: A precise plan of action or a thorough grouping of…
Q: hetween a private and a
A: Solution - In the given question, we have to tell the difference between private key and public key…
Q: Is it possible to list the Programming Paradigms? What's the point of having so many different…
A: paradigms of programming Programming paradigms are a way of categorizing programming languages based…
Q: Q1: Write a program to enter the time in second and convert it to hours .using function called…
A: Here I have created the function named Seconds_Hour(). In this function, I have returned the…
Q: The Processing unit interacts with memory using the Memory Status Register and the Memory data…
A: Answer the above question are as follows:
Q: Q2: Give the output of the following program 1. for a=0: 5 disp('value of a: %s\n', x); 3. if(a=15)…
A: Here in the given program the value of a ranges from 0 to 5. Therefore for values of a from 0 to 5…
Q: Consider an undirected graph G = (V;E). An independent set is a subset I V such that for any…
A:
Q: Describe the field of technological equipment and provide a list of probable employment in this…
A: Given: Mainframe computers, servers, general computer equipment, printers, displays, hard drives,…
Q: The many degrees of encryption that may be applied to a database are listed.
A: Level of database encryption: Column level encryption is the process of encrypting individual…
Q: What are the phases in data mining data processing?
A: Given: The practice of extracting interesting patterns and information from massive volumes of data…
Q: What is the difference between a private and a public key in cryptography?
A: Cryptography: Cryptography is a security communication technology that allows only the sender and…
Q: In regards to greedy algorithms, which of the following statements are true (select all that apply)?…
A: As the name tells it is an type of algorithm that tend the chose the best solution of the next point…
Q: A computer network is defined as a system that connects computers together. What are the system's…
A: When two or more nodes (for example, computers) are linked together, they can share resources (such…
Q: What are some of the distinguishing properties of a computer?
A: The Answer is in given below steps
Q: If the value passed into the parameter x in the following method is 20. What is the value returned…
A: public static int method3(int x) It receive the value of 20 and store it on x int sum = 0;…
Q: Q1: Write a program to enter the time in second and convert it to hours * .using function called…
A: I give the code in Matlab along with output and code screenshot
Q: In 6809, a portion of the memory has been randomly selected and shown here: ... C7 52 ЕС 89 FF 00 DC…
A: This portion of the memory may contain binary information related to one instruction is: LDD $52
Q: In C#, what is the difference between Const, Read Only, Static, and Non-Static variables?
A: value can be changed again and again through a constructor: Cost is simply "constant," a variable…
Q: Memory sticks (USB Flash drives) are widely used in a wide variety of enterprises. What are the…
A: A USB flash drive (also called a thumb drive)[1][note 1] is a data storage gadget that incorporates…
Q: To depict the structure of a database, you can use either an E-R diagram or DBDL. Which method do…
A: The Answer start from step-2.
Q: 1. Write a java program that will "accept" a user given word if it contains at least 2 Uppercase…
A: Step-1: StartStep-2: Declare a variable word and take input from userStep-3: Declare three variable…
Q: How a user interacts with his or her mobile and desktop operating systems?
A: An operating system (OS) is system software that manages PC hardware, and software assets, and…
Q: An suitable hybrid merge-join technique should be created for the case when both relations are not…
A: The distinction between a merge join and a hybrid merge join is significant. After learning about…
Q: Flynn's taxonomy, we believe, should be enlarged by one level. What distinguishes today's computers…
A: Flynn's taxonomy: Michael Flynn suggested a taxonomy for computer systems called Flynn's taxonomy.…
Q: Write a function that receives three arguments (a string containing a single character, the number…
A: CODE:#include <bits/stdc++.h>using namespace std;void myfunction(string str,int rows,int…
Q: Correct the source codes to completely run the program
A: clrscr and getch functions are available in conio.h library and if we import this there will not be…
Q: After comparing data items, a computer takes action depending on the results. Explain?
A: Introduction: Information about the data element's data type will be included in the definition,…
Q: The OODBMS stands for Object-Oriented Database Management System.
A: Database Management System: A database management system, sometimes known as a DBMS, is a…
Q: Make a list of all of the different sorts of DNS records. Each one should be explained in detail,…
A: You must do the following tasks in order to answer the questions: - Explain the different kinds of…
Q: In the case of a data security breach, what are the company's rules for disclosing information?
A: Data breach: Your Social Security number, bank account or credit card details, personal health…
Q: I want Examples on el gamal cipher i want 2 Examples Examples and interaction with the audience
A: Algorithm of ElGamal Encryption: This block cipher is based on the possibility of establishing…
Q: To depict the structure of a database, you can use either an E-R diagram or DBDL. Which method do…
A: E-R diagram: - Existing databases may be examined using ER diagrams to identify and correct logic or…
Q: Consider the following set of questions: What are the most crucial concerns when it comes to data…
A: The following steps are involved in data backup: We create a data backup when we duplicate data,…
Q: computer How do you feel about Ada Lovelace?
A: Her full name was Augusta Ada Byron, Lady Byron and she was born of December 10, 1815, Piccadilly…
Q: What are the various tables that EIGRP makes use of?
A: The answer for the given question is as follows.
Q: You're working on a new system to help eligible students locate jobs that match their studies. It…
A: Basics: Functional requirements define the underlying framework's behavior. Essentially, these are…
Q: What are the detection mechanisms: a) Sniffing the network (b) Surveillance by wiretap?
A: Sniffing the network: - This technology can be used to test telephone lines and improve call…
Step by step
Solved in 2 steps with 2 images

- Explain the term masking. How is it useful for data representation? Explain the concept using an example For a floating-point format with a k -bit exponent and an n -bit fraction, give a formula for the smallest positive integer that cannot be represented exactly (because it would require an n + 1 –bit fraction to be exact).Show Steps Please 6. Suppose we are given the following subset of codewords, created for a 7-bit memory word with one parity bit: 11100110, 00001000, 10101011, and 11111110. Does this code use even or odd parity? Explain.Consider a hypothetical 8 bit floating point machine representation with a sign bit, a 3 bit exponent, and a 4 bit mantissa (se1e2e3b1b2b3b4), where the exponent bias is 3 (add 3 to exponent of number to form machine representation). Recall that actual mantissa has 5 bits, since the leading 1 is not stored on the machine. (a) What is the number ?≈2.718 in this 8-bit format? (b) What is the number that (10100111)2 represents in this 8-bit format? (c) What is the upper bound of the relative error when representing a real number in this 8-bit format?
- a) A digital sound recorder captures sound from the real-world, processes the audio and stores it in binary form. Using the principles of digital signal processing, practically explain how this phenomenon occurs. b) Use the two’s complement binary representation to represent each of the following integers as 10-bit binary numbers.i) -13710 ii) 14510 iii) -15810 iv) 16710 v) -11510 c) If an 8-bit binary number is used to represent an analog value in the range from 0 to 100kg, what does the binary value 011001002 represent?Consider the 64-bit binary number 11010000 00000100 00001000 00000101 10001001 00110000 10000001 00000001, stored in the doubleword with address 2000. For big-endian architecture, what value is stored in byte 2004?Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.
- 2. The table of ascii characters is of size 128. This requires 7 bits of data. (When stored in an 8 bit byte the high bit is usually left 0) If we had 3 bits of data to represent characters in a data set, how many characters could our set contain? Question 1 options: 7 3 9 8 4Show how the following values would be stored by byteaddressable machines with 32-bit words, using little endian and then big endian format. Assume that each value starts at address 10 . Draw a diagram of memory for each, placing the appropriate values in the correct (and labeled) memory locations.Q.) 0x456789A1Show Steps Please 18. If the floating-point number representation on a certain system has a sign bit, a 3-bit exponent and a 4-bit significand: a) What is the largest positive and the smallest positive number that can be stored on this?system if the storage is normalized? (Assume no bits are implied, there is no biasing, exponents use two's complement notation, and exponents of all zeros and all ones are allowed.) b) What bias should be used in the exponent if we prefer all exponents to be non-negative? c) Why would you choose this bias?
- Show Steps Please 5. Compute the Hamming distance of the following code: 0011010010111100 0000011110001111 0010010110101101 0001011010011110 6. Suppose we are given the following subset of codewords, created for a 7-bit memory word with one parity bit: 11100110, 00001000, 10101011, and 11111110. Does this code use even or odd parity? Explain. 7. Given that the ASCII code for A is 1000001, what is the ASCII code for J? b. Given that the EBCDIC code for A is 1100 0001, what is the EBCDIC code for J? 8. Decode the following ASCII message, assuming 7-bit ASCII characters and no parity: 1001010 1001111 1001000 1001110 0100000 1000100 1001111 1000101Help me answer these please 11. Binary and floating-point arithmetic: Solve each binary operation with detailed, step-by-step explanation. Note that for each of the following operations, first you need to convert the decimal numbers (represented in base 10) into their binary representation. Explain where carry bit is generated and how. a. Binary multiplication of (12 x 9). b. Binary subtraction of (7 – 15). c. Binary division of (12 / 3). d. Convert (1425.75)10 into a 32-bit Single Precision IEEE floating-point binary number. Use the example in the .ppt slidesShort questions: Q. If 8 Bits are equals to 1 byte then how many bytes can be formed in 67464 Bits?

