Question II (1. for (i = 0; i
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter2: Problem Solving Using C++using
Section2.4: Arithmetic Operations
Problem 6E
Related questions
Question
Please send me answer of this question immediately and i will give you like sure sir
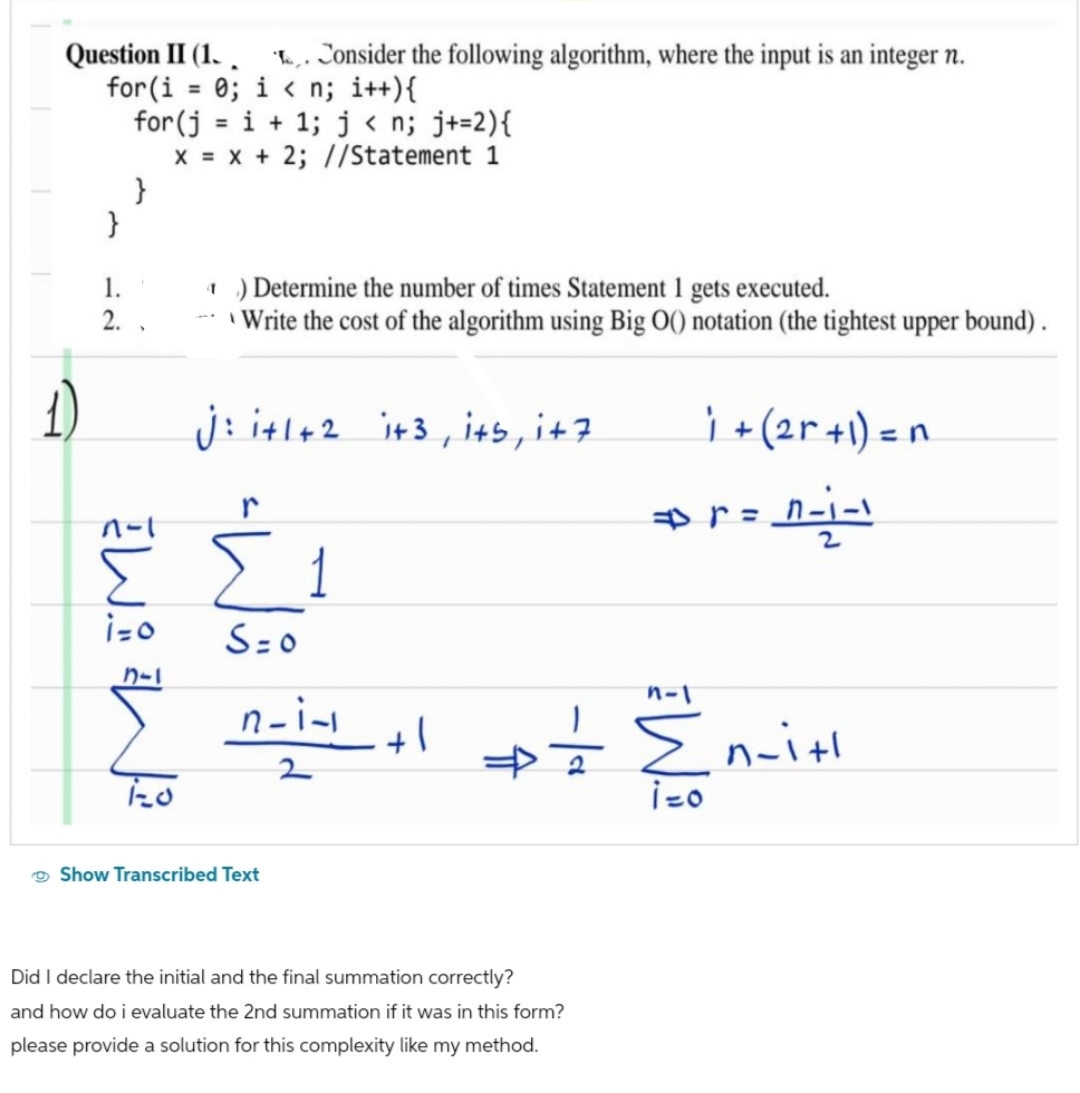
Transcribed Image Text:Question II (1. . Consider the following algorithm, where the input is an integer n.
for(i = 0; i<n; i++){
for(j=i+1; j<n; j+=2){
x = x + 2; //Statement 1
1.
2.
}
1-1
W
i=o
カー
) Determine the number of times Statement 1 gets executed.
- Write the cost of the algorithm using Big O() notation (the tightest upper bound).
j: i+1+2 i+3, its, i+7
r
Σ1
S=0
n-i-1
2
Show Transcribed Text
+1
n-1
Did I declare the initial and the final summation correctly?
and how do i evaluate the 2nd summation if it was in this form?
please provide a solution for this complexity like my method.
i + (2r + 1) = n
r=1-1-1
# = {₁-
i=o
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr