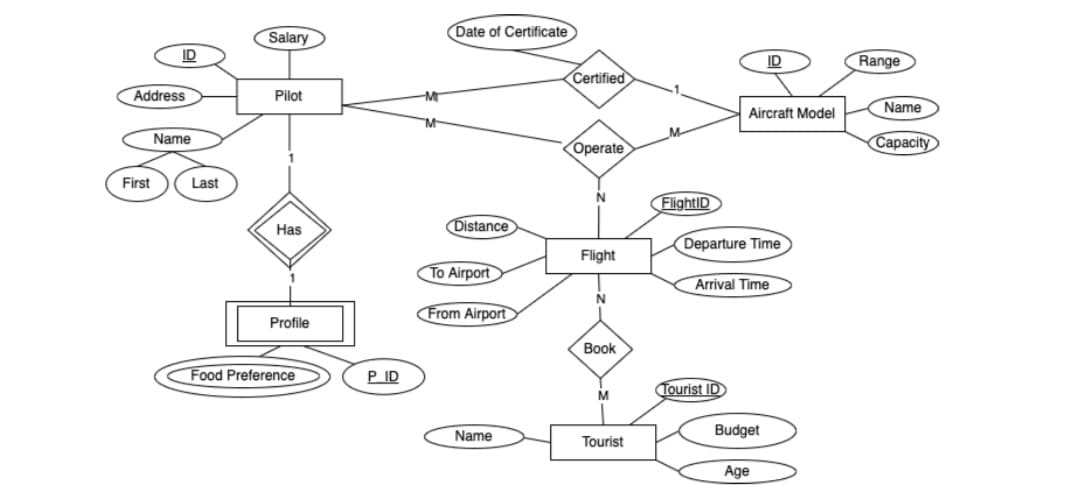
Question- Translate the following ER diagram into the appropriate relational schema(s):
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: Introduction: In this question, we will explore why web application security is important for every ...
Q: true (T) or false (F) ar the following questions by circling eith 1. T F Every database has more tha...
A: In questions with many questions, we must answer 3.
Q: Examine the advantages and disadvantages of various system models.
A: System Models are mainly divided into 5 types: -> Minicomputer model -> Workstation model -...
Q: Write a C++ program to find and print the index of the first three digit positive integer present in...
A: Write a C++ program to find and print the index of the first three-digit positive integer present in...
Q: Using the C#, create programs using the do-while loop that will produce the following outputs: 1 2...
A: The do while loop is the same as while loop except that it executes the code block at least once. ...
Q: Take a look at the data you have on your computer. Do you have any personal data on your computer? W...
A: Computer stores data ,personal data of the user ,and to protect these data we need to have good secu...
Q: Write a Python program to show the use of the isinstance(() function to check whether the value 0.5 ...
A: Approach: The isinstance() function in Python takes the object and the class as the parameters and r...
Q: Explain what the memory addressing capacity of the 20-bit address bus will be.
A: A single bit can have 21 = 2 values, 0 or 1. Two bits can have 22 = 4 values, 00 or 01 or 10 or 11. ...
Q: Complete the code provided to add the appropriate amount to totalDeposit. 5290 2416604.qx3zqy7 1 #in...
A: Introduction:
Q: Determine the major functions of a database and how they differ from one another. Explain why compa...
A: INTRODUCTION: Determine the major functions of a database and how they differ from one another. Expl...
Q: Write a C program and the following functions to compute the average value for the following data ...
A: We need to write a C language program to compute the average value for the data stored in a 2-D arra...
Q: nvm
A: nvm
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: The answer is
Q: Which NOS-Network Operating System providers do you know of?
A: Please check the step 2 for solution
Q: Comment on the current status of IPV4 and idencly d in lv6 Author: Abnan S ONI Henry F. Korth, S. Su...
A: The lack of address space - the number of different devices connected to the Internet grows exponent...
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: Introduction: here in this question we will discuss about why web application security is critical t...
Q: Vhat concerns and issues does the usage of non-integrated information systems rai
A: Here as we know Non-integrated information systems are the ones that are not connected to one anothe...
Q: 11. Write a Python function called word_count that takes a file name as an argument. The function sh...
A:
Q: Explain what the statement below means and provide an example of such a situation in no more than 30...
A: Explain what the statement below means and provide an example of such a situation in no more than 30...
Q: Which authentication method necessitates that the machine be linked to a domain or Azure AD?
A: Introduction: Azure AD is an Office 365 component that aids with identity management and may be cons...
Q: Using the C#, create programs using the do-while loop that will produce the following outputs: 5 4...
A: program on do-while loop syntax for do-while do { code block }while(condition); our program is to di...
Q: What is the next step in the GPO deployment process now that it has been created??
A: the answer is given below:-
Q: Overview One of the oldest methods for computing the square roote of a number is the Babylonian Meth...
A: Given: Python program to find square root using Babylonian Method.
Q: ery the t cis ers si t ey m (er nt te stareal le t s sta. W t che wwth rs es ae ls. a womrante tte r...
A: I have try best for solution Please check step 2 for code & step 3 for output
Q: How can a client know if a server request will be successful or unsuccessful?
A: We have to discuss How can a client know if a server request will be successful or unsuccessful.
Q: Describe the concept of a system model. What issues should be addressed while developing fundamental...
A: We have to discuss the concept of a system model. And also discussed what issues should be addressed...
Q: What does "picking numbers at random" imply?
A: Given :- What does "picking numbers at random" imply?
Q: When it comes to wireless networking, there are benefits and drawbacks to consider. Considering the ...
A: Introduction Wireless networking cannot be the primary transmission source in the workplace; it can...
Q: 1. Which of the following best explains the concept of a 'weak signal? a Information that is too wea...
A: Information that is too weak to be of any use in forecasting trends Information that is wrong and ...
Q: Question:: Examine the advantages and disadvantages of various system models.
A: there are many different types of system models. let's see advantages and disadvantages of them
Q: "Rabenstein code was used to send a message with 4 information bits, you receive 100110001 , if you ...
A: The answer is
Q: n the BinaryTree abstract data structure, there is a remove() function. A. The remove() function run...
A: Solution: In the BinaryTree abstract data structure(DS), there is a function called as remove() f...
Q: Assume, r1= 0XA2FF0010, r2= 0×5D00FFF0 What is the ARM statement which correspond to the each follow...
A: Answer 1: ========================================================================= figure 1:
Q: Write a program (WAP) in c to create an undirected graph using adjacency matrix representation. Numb...
A: The code is given below
Q: Describe a cloud storage application and explain how it differs from a standard client storage progr...
A: Storage server : A storage server is a type of server that is used to store, access, secure and mana...
Q: write c++ program to input a year and to check whether it is a leap year or not
A: I have provided C++ CODE along with CODE SCREENSHOT and also provided TWO OUTPUT SCREENSH...
Q: Find the Worst case time Complexity of the following recursive function T(n) = T(n-1)+n -1, T(1) = 0...
A: Given:T(n) = T(n-1)+n-1, T(1) = 0Solving it using substitution:T(n) = T(n-1)+n-1 <-(1)T(n-1) = T(...
Q: Write a while loop that prompts the user for a password. If the password entered does not equal “Ope...
A: logic:- set i=1 read a string. Use while(true) If(userPass.equals(“OpenSesame”)) ...
Q: Name three features of the 8086 that were improvements over the 8080/8085.
A: The microprocessor(MP) would be a computing chip that incorporates information processing functional...
Q: Write a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: # Check if "0.5" is an object of float typem or not if isinstance(0.5, float): ...
Q: What are the numerous types of computer languages available to us today? Describe each in a few shor...
A: Introduction: Language is the fundamental mode of communication between computer systems, an...
Q: 4. Why should we identify the topologies of networks?
A: Introduction: Why should we identify the topologies of networks?
Q: Complexity of the following recursive functi on
A:
Q: What is one function that FAT performs? Tracks interrupts Tracks distribution of volumes...
A: The main function is Tracks Sequence of Clusters.
Q: In Windows 2016, what are the different types of "flavours?"
A: Solution: The windows 2016 is coming with the two flavours or editions, Standard and Datacenter. 1) ...
Q: Explain what the memory addressing capacity of the 20-bit address bus will be.
A: The Explanation is given below step.
Q: Write an assembly language program using GNUSim8085 i have 30 mins to devliver please slove faster i...
A: The question is to write the assembly language code for the given problem.
Q: Compare the Von Neumann Architecture and the Little Man computer. What are the weakness and strength...
A: answer is
Q: Design DFA(Deterministic Finite Automata) with below given conditions a. You have two options. You c...
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: Suppose the implementation of an instruction set architecture uses three classes of instructions, wh...
A:
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- a)Createa flow chartdiagram tomodel the online course registration described inthe case study belowCASE STUDYONLINE COURSE REGISTRATION SYSTEMThe User enters the surname and password and chooses if the user is a student or administrator. If entered details are valid, the user accounts become avaiable. f it is invaid an appropriate message is displayed to him/her. A student can search al the courses available to him and he chooses the best course he wants. The student can view course duration, facuty and department the course he may choose. When a student has successfully chosen a course, he can register to that course. Upon registration student details are stored in database.After registration to any course, the student may see the details of current course. He may wish to know details about fees and other information. The administrator also has the privilege to display details of the students and the corresponding course for which they have registered. The administrator has to perform…I WANT THIS PROGRAM IN JAVA LANGUAGE OOP KINDLY USE GUI eShop Create/View/Edit ProfileAdmin account for notifications/viewable informationview itemscontact seller (chatbox)add to cartview cartcheckoutmake paymentsview purchase historyview product viewing historyreminder to checkoutGroup Members Click for more optionsBrief expalantion springboot Userservice: public User getUser() { Stringusername=SecurityContextHolder.getContext().getAuthentication().getName(); /* Get User from the DB. */ returnthis.userRepository.findByUsername(username) .orElseThrow(()->newUserNotFoundException(String.format("Username doesn't exist, %s",username))); } ================================================================================= User controller: @GetMapping("/get") publicUsergetUser(){ logger.debug("Getting User Data"); returnthis.userService.getUser(); }
- Dijkstra's algorithm Weight Class Implementationlanguage : C++ Note : Skelton Files Provided Please check the linksproject Details:https://ece.uwaterloo.ca/~dwharder/aads/Projects/5/Dijkstra/ Files:https://ece.uwaterloo.ca/~dwharder/aads/Projects/5/Dijkstra/src/ Please provide clear and complete solution for thumps up.LocalAreaNetwork(LAN)isoneofthebasictypesofcomputernetworks.Briefly describeaboutlocalareanetworkincludingthemajortypesandfeaturesofLAN.Objective: Write a program in Python using wrapper API to get weather information. Step 1.1: Get PyOWM API key Follow these steps to get a weather info API key from Open Weather Map.org: Go to openweathermap.org/appid Under “Sign up and call API for free”, click “Sign up” Register. Click “Create an Account”. Remember your login and password. They may send a confirmation link to the email you used to register. Use it to confirm. Go to “API keys”. Copy key from gray box into a text file and save it for later. You will insert the key into the provided Python code that accesses the API. Step 1.2. Install PyOWM module on your computer Follow these steps to install PyOWM module on your computer: Start your terminal (Windows users start WSL terminal or Windows Console). Type pip3 install pyowm (the module should install). Step 1.3: Download, Add Code, and Test interactive App You should use the starter app weather.py. It includes a predefined function getweather() that…
- dont dont odntpost existing one sure cmpliant answr only 100% sure else skip(Python) Dating App Scenario Interview Question Given a user Id Write/Design/Implement API functions to: 1. like someone's page 2. remove like from someone's page 3. find the most liked profile it should look like def add( int k): def remove (int k): def find(profiles): with implementationBook reference: Windows PowerShell Step by Step 3rd Edition - Ed WilsonChapter 15 3. To which of the above objects can the group policy NOT be applied? a) Organization Unit [OU] b) Computers c) Users d) containers 4. The below script is used to create a new Organizational Unit [OU]; what is the name of the OU created? $strClass = "organizationalUnit" $StrOUName = "OU=MyTestOU" $objADSI = [ADSI]"LDAP://DC=nwtraders,DC=msft" $objOU = $objADSI.Create($strCLass, $StrOUName) $objOU.SetInfo() 5. What is the ADSI Edit tool used for?
- this is the themes xml code activity_main.java package com.example.Appaimport androidx.appcompat.app.AppCompatActivity;import android.os.Bundle;public class MainActivity extends AppCompatActivity {@Overrideprotected void onCreate(Bundle savedInstanceState) {super.onCreate(savedInstanceState);setContentView(R.layout.activity_main);}}--------- <resources xmlns:tools="http://schemas.android.com/tools"><!-- Base application theme. --><style name="Theme.Appa" parent="Theme.AppCompat.DayNight.DarkActionBar"><!-- Primary brand color. --><item name="colorPrimary">#FF0000</item><item name="colorPrimaryVariant">@color/purple_700</item><item name="colorOnPrimary">@color/white</item><!-- Secondary brand color. --><item name="colorSecondary">@color/teal_200</item><item name="colorSecondaryVariant">@color/teal_700</item><item name="colorOnSecondary">@color/black</item><!-- Status bar color.…import android.os.Bundle import android.os.PersistableBundle import android.view.View import android.widget.* import androidx.appcompat.app.AppCompatActivity class TicTacToeActivity : AppCompatActivity(),View.OnClickListener { // TODO (suggested): maintain a reference to a TicTacToe object overridefunonCreate(savedInstanceState:Bundle?) { super.onCreate(savedInstanceState) setContentView(R.layout.activity_tictactoe) // TODO (suggested): get the player's name, symbol, and the first move choice from the activity's intent; use them to instantiate a TicTacToe game; decide whether the computer should play based on the first move choice // TODO (suggested): get a reference to the TextView "player info" area; update the TextView with the player's name and symbol // TODO (suggested): using a loop and button tags, update their texts and "onClick" listeners to TicTacToeActivity; remember to disable the button if…dont dont post copied one sure strong dislike else skip answr only 100% sure

