question Use substitution method: Show that the solution of T(n) = T(n-1) + n is O(n²) Use master method to find tight asymptotic bounds: T(n) = 2*T(n/4) + n T(n) = 2*T(n/4) + n²
Q: DIRECTION (4-5): One card is drawn from a well-shuffled deck of 52 cards. Find the probability of…
A: '8' of diamond: (C) 1/13 Red ace: (B) 2/26
Q: The assumption that Linux is more secure than other OSes begs the question: why?
A: Linux Is Safest Because it's open source. This is often argued. The many eyes security hypothesis…
Q: Write an assembly program that read char from user then check if the char is digit or not.
A: The answer is given in the below step
Q: Many of software engineering's first ideas have been forgotten. Explain?
A: First, a general overview of software development: Software engineering mixes engineering and…
Q: To build a computer, what do you think are the four most crucial parts of logic?
A: Name four essential computer logic design requirements. The solution is next. logic design, A…
Q: The Instruction Set includes a number of different kinds of instructions of their own. Walk me over…
A: Let's examine the answer : A computer with fewer instructions (RISC) : Reduced Instruction Set…
Q: Python Can you explain what you did with comments class linkedQueue: class _Node: def…
A: Given code: class linkedQueue: class _Node: def __init__(self, value, next = None):…
Q: What are some of the fundamental concepts of design that underpin the CBSE, with the goal of…
A: The CBSE (Component-Based Software Engineering) is a software development paradigm that focuses on…
Q: In the realm of computing, architecture and organization are two very separate things.
A: Introduction Computing is the realm of technology that involves the use of computers and digital…
Q: The inner workings of an OS are beyond our ken.
A: An operating system is complex software system which manages underlying hardware as well as…
Q: What characteristics do add-ons, plug-ins, and extensions have that make them potentially harmful to…
A: Justification: For a specific site, extensions increase a web browser's standard functionality.…
Q: What does the term "prototyping" mean when used to the field of software engineering?
A: Software prototyping involves creating incomplete representations of software applications.…
Q: Is it true that it's always less expensive to prevent a problem than it is to fix it after it's…
A: According to the information given:- We have to define the mentioned statement is true or not.
Q: Please for thi question, kindly explain into details for me. This seems a new topic to me…
A: Introduction Bit strings are sequences of binary digits (bits) used in computing. They can be used…
Q: Before choosing a choice, think about all that might be done to resolve the stalemate.
A: The multiprogramming working framework has several processors that compete for a limited amount of…
Q: Please define "Semantic augmentation" and offer an example to help me get a handle on the…
A: Context Free Grammar:- Context-free grammar (CFG) is a type of formal grammar in which each…
Q: Entities within databases take on many forms. Provide three examples of entities you may encounter…
A: Introduction : Entities in a database are the objects, people, concepts, or events that are…
Q: If you were asked to define the term "network security," what would you say? You can explain the…
A: Network security involves a vast array of strategies, tools, and processes. Software- and…
Q: What does Linux allow you to do, except check your email and surf the web? How feasible is it for…
A: Introduction: Linux's Firefox browser handles email and online browsing. Google Chrome is another…
Q: The three main types of cloud computing systems are as follows.
A: Definition: Without the customer having to actively maintain them, a cloud computing service offers…
Q: Explain the character set in simple terms
A: INTRODUCTION: The essential component that permits the display of text, numbers, and symbols on a…
Q: The number of defects discovered in a software before to release may have an effect on the quality…
A: Such flaws sometimes continue to exist but fail to manifest. For instance, there is very little…
Q: When an exception is thrown outside of a try block, what are the probable outcomes?
A: try block: A try block is a block of code that is used to test whether an error will occur while a…
Q: What types of issues arise during Performance Testing?
A: Performance testing can uncover various types of issues, including: Scalability issues: the…
Q: To what extent does the synoptic technique differ from the incremental one?
A: What distinguishes a synoptic approach from an incremental method? Difference: The add-on method is…
Q: Describe one of the numerous types of compensation mechanisms used in broadband designs.
A: A common compensation scheme is broadbanding. However, Grade and Step frameworks and Market-Based…
Q: Infrastructure and software for networks hosted in the cloud
A: According to the information given:- We have to define Infrastructure and software for networks…
Q: In software development, what do you think are the four most important factors? For optimal overall…
A: In software development, four of the most important factors for optimal overall performance are:…
Q: Why is it that the bulk of multimedia content on the Internet today is sent via TCP rather than UDP?
A: Both UDP and TCP: The full name of "UDP" is "User Datagram Protocol." It allows the raising…
Q: You were assigned to do all field works in a networking company.Describe your internship position…
A: Networking:- Networking is the process of connecting computers and other devices in order to share…
Q: demonstrates the search technique on a skip list S for a key K. The search is carried out using the…
A: Skip list: A skip list is a probabilistic data structure that is used for searching for elements in…
Q: How reliable are IP and UDP? Is it just a coincidence, or some deeper meaning here?
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: The symbol table stores the memory address associated with each variable. What is the memory address…
A: Answer: We need to explain the what are the possible answer for the given question so we will see in…
Q: Is there anything that distinguishes software engineering from the other branches of engineering?
A: Answer: The process of breaking down customer requirements and then planning, developing, and…
Q: Just what does "taking into account" imply in this context? Incorporating ideas from the field of…
A: What's critical concern? Consideration may be anything. Consider past, present, or future factors.…
Q: In a few words, please describe source data automation (SDA) and describe at least two (2)…
A: Introduction: SDA: Source Data Automation : Source Data Automation (SDA) is the method of acquiring…
Q: Ubuntu is superior than other popular Linux distributions. In what ways do you believe your concept…
A: The main differences between Linux and Ubuntu are listed below: Linux kernel-based Ubuntu. Linux…
Q: There are many distinct kinds of instructions included in the Instruction Set. Identify the…
A: Introduction: A Complicated Set of Instructions (CISC)A Complex Instruction Set Computer, often…
Q: In a perfect shuffle a deck of cards is divided exactly in half, which are interleaved alternately…
A: In this question we have to understand what happens when multiple consecutive out-shuffles are…
Q: Is it more expensive to permit deadlocks and then uncover their presence, or to prevent deadlocks…
A: Avoiding deadlock: A situation known as a stalemate occurs when two different activities are…
Q: 6. Find the value of II-oj!.
A: Since no programming language is mentioned, I am using matlab. Algorithm: Start Initialize the…
Q: Why do wireless networks decrease in performance more quickly than wired ones?
A: The answer is given below step.
Q: A marker annotation is a type of annotation that has no members. Its primary function is to denote a…
A: Below is the complete solution with explanation in detail for the given question in Java Programming…
Q: To what extent should several points of view be included when modeling software systems?
A: Software systems modeling refers to the process of creating abstract representations of a software…
Q: Even though sudo is the recommended method, root access is still possible on certain Linux systems.…
A: Introduction: Linux is a free and open-source operating system (OS). An operating system is…
Q: Discuss briefly the means through which device requests may be managed.
A: A computer is a digital electronic machine that can be programmed to automatically perform a series…
Q: Why do we need cache memory if RAM (Random Access Memory) provides fast, volatile storage based on…
A: Introduction RAM, or random-access memory, is a critical component in everything from desktop…
Q: I have this code: def normalize_dictionary(self, d): """""" values =…
A: The given code is implementing a comparison between two dictionaries based on their normalized…
Q: Just what does it mean when people talk about the "Internet of Things" (IoT) or "machine-to-machine"…
A: The term "things" refers to electronic devices that may connect to a communication media and are a…
Q: Write a C# Windows Form program that asks the user to enter a name (in a TextBox) and displays the…
A: Introduction C#: C# (pronounced "C Sharp") is a modern, object-oriented programming language…
please answer with proper explanation and step by step solution.
answer for 2 is theta(n)
answer for 3 is Theta (n²)
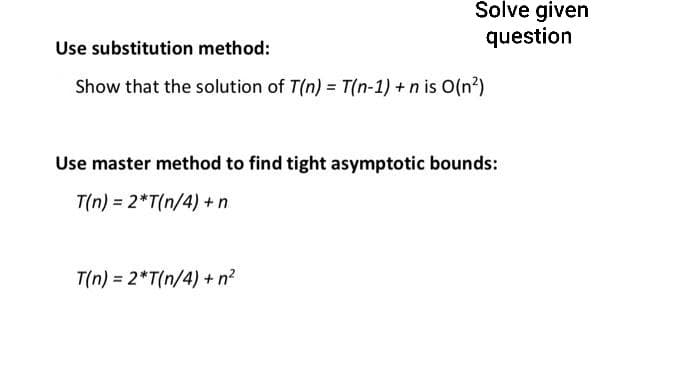
Step by step
Solved in 4 steps

- 3. Solving RecurrencesGive asymptotic upper and lower bounds for T(n) in each of the following recurrences.Assume that T(n) is constant for n ≤ 2. Make your bounds as tight as possible, andjustify your answers. (1) T(n) = 4T(n/4) + 5n(2) T(n) = 5T(n/4) + 4n(3) T(n) = 25T(n/5) + n2recurrence relation obtain L(1) = 0; L(N) = n+4 * L(n/4) T(1) = 1; T(n)= n+2*T(n/2)Use the master method to give tight asymptotic bounds for the following recurrence T(n) = 2T(n/4) + 1 Group of answer choices 1. ϴ(n0.5lgn) 2. ϴ(n0.5) 3. ϴ(n2) 4. ϴ(n)
- Solve the following recurrences using recursion tree method and write the asymptotic time-complexity. 1. T(n) = 3T (n/4) + n^22. T(n) = T (n/5) + T(4n/5) + n3. T(n) = 3T(n − 1) + n^4 4. T(n) = T (n/2) + n^2Lets say an algorithm has 2 base cases. PsuedoCode: if n == 1 return 0 if n == 2 return 1 return A[n..............n-1]solve the recurrence relation for the above simple recursive algorithm?(a) For each of the following recurrences, give an expression for theruntime T (n) if the recurrence can be solved with the Master Theorem.Otherwise, indicate that the Master Theorem does not apply.(i) T (n) = T (n/2) + T(n/2) + T(n/2) + n2(ii) T (n) = 0.5T (n/2)+ 1/n(iii) T (n) = 3T (n/3) + n(iv) T (n) = 4T (n/2) + nlogn
- Solve the recurrence relations shown below. a. T(n)={4T(n−1)+1if n>11if n=1T(n)={4T(n−1)+1if n>11if n=1 -- b. T(n)={3T(n/3)+4nif n>11if n=1Arrange the functions √n (square root of n), 1000log(n), nlog(n), 2n!, 2n, 3n, n2/100000 in increasing order for their Big-O estimate.Solve the recurrence relation by substitution: T(n) = T(n-1) + 2^n

