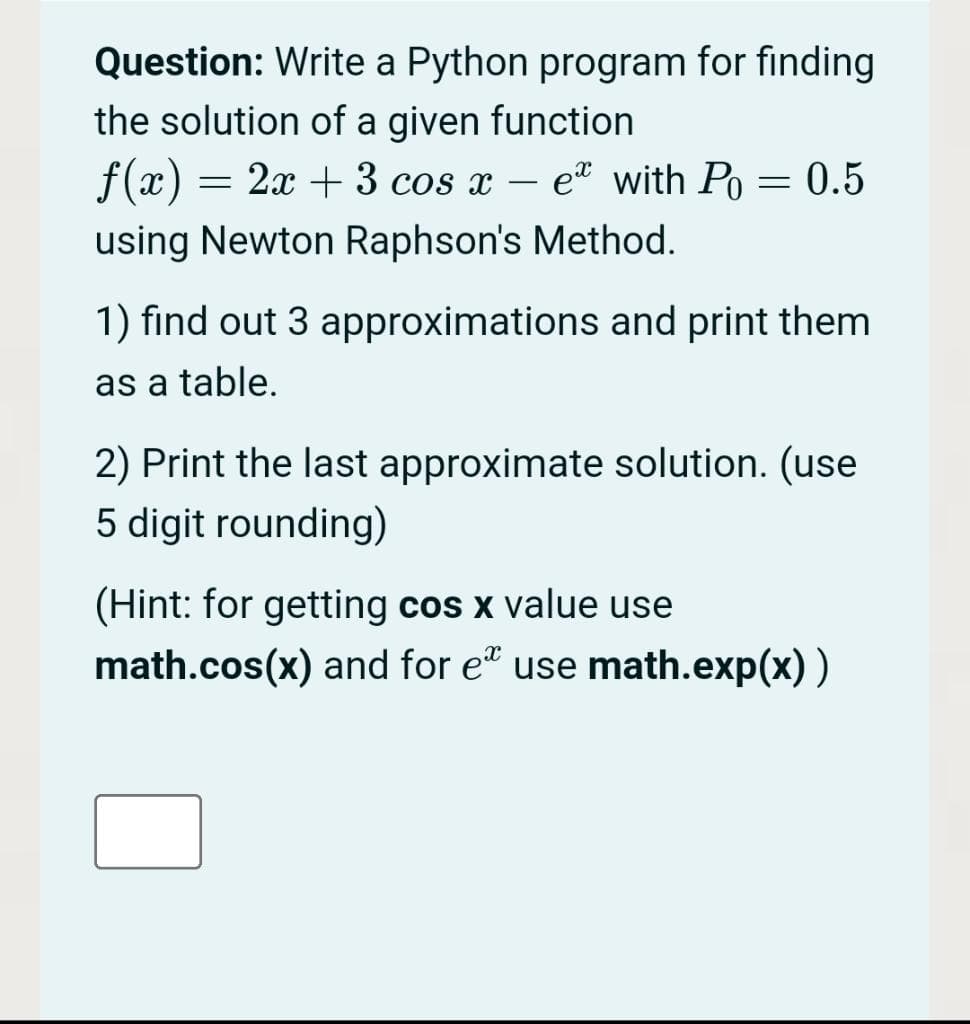
Question: Write a Python program for finding the solution of a given function f(x) = 2x + 3 cos x – e with Po = 0.5 using Newton Raphson's Method. 1) find out 3 approximations and print them
Q: Analysis of bucket sort algorithm
A: Bucket sort is a sorting algorithm that sorts by first dividing the elements into multiple groups/bu...
Q: Encode õEvõpov with Huffman coding. a. List all symbols and their probabilities b. Find the Huffman ...
A: ans is given below -
Q: ementing IDPS
A: given - What are some challenges with implementing IDPS?
Q: Write algorithm for the flowchart: Start False Enter name and password
A: Lets see the solution.
Q: a) Convert (DEFACED), from hexadecimal expansion to a binary expansion. b) List all integers between...
A: Here we have given three parts a,b and c in part (a) we have to convert given hexadecimal expansion ...
Q: Let U=(2,-1,0,-3) ,V=(1,-1,-1,3) and W=(1,3,-2,2) then U.V is:
A: Lets see the solution.
Q: In a database, explain the representations of Identifying Relationships, Non-Identifying Relationshi...
A: Introduction: A non-identifying connection is one between two entities. An instance of the child ent...
Q: ng EF ngs BCA and FGH nes BCA and ABFE
A: given - ) How many permutations of the letters ABCDEFGHIJ contain i) the string FF?in) the strings B...
Q: mine the format of the codeword. c = [message | parity bits] c = [parity bits | message]...
A: Lets see the solution.
Q: CUIL SavingsA gava VISual Studio Code majas O SavingsAccount.java 9+ O SavingsAccountTest.java X C> ...
A: Hopefully I have got your concern and the person suggested is correct that at end there should be br...
Q: The result of the logic gate is* O A BC+AB+AB O AB+AC +ABC O AC+ABC+AB O BC+AB+ABC O skip
A: Answer:
Q: Explain the advantages and disadvantages of sharding, as well as the possible concerns.
A: Introduction: The primary benefit of sharding is that it enables the database to grow beyond the lim...
Q: What are white-hat hackers' objectives? Are black-hat hackers pursuing the same objectives?
A: Hackers: A hacker is an individual who uses a computer, networking, or other skills to overcome a te...
Q: odulo the given polynomial e.g. (x3 + x2 + 1): For example: 011 + 011 or 111 * 111 etc.
A: given - Perform the given polynomial arithmetic in GF (23) modulo the given polynomial e.g. (x3 + x2...
Q: te a program to find the summation of the numbers from 5 to 15.
A: ANSWER:
Q: Draw a flow chart to find Z from the equations: Z= vX+3e Z= 3/X + SIN (X) Z= X²- |x| When X>0 When X...
A: Flow chart: It is used to represent program steps in the pictorial representation. Using the flow ch...
Q: eate a class calculate that uses two separate functions:-a function to multiply two float numbers an...
A: Lets see the solution.
Q: Why is data quality so important in data warehousing, in your opinion? The advantages and indication...
A: Introduction: Data of high quality is data that is useful. To be of good quality, data must be consi...
Q: Investigate the many ways in which information systems are employed in various industries.
A: Introduction: It's worth noting that management support systems (MRS), decision support systems (DSS...
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the acce...
A: Required:- Write a JAVA program in which the user enters the initial velocity u, time of travel t, a...
Q: Given: A %3D {1, 2},В %3D {x, у, z), and C = {3, 4} then A × B × C is : %3D {(1,х,3), (1,х,4) ,(2,х,...
A: Here in this question we have given three set with some element in it.and we have asked to find cros...
Q: Some of the devices in one of the buildings where your organisation has set up a network have comple...
A: Introduction: Protecting the network is critical today since there are many data breaches. The data ...
Q: Write a java program to find the 2nd largest number in the array and explain program with comments.
A: import java.util.*;public class Main { public static void main(String[] args) { int[] arr ...
Q: What is a Smart Office, and how does it work?
A: Introduction: Smart Office: It is a modern workplace where technology enables employees to operate ...
Q: hat will the designer's first assignment be?
A: Introduction: If you are a web designer or UI/UX designer, the following are frequent topics to cons...
Q: What distinguishes a Windows Service from a regular application?
A: Introduction: Standard application: On a Windows system, a standard/regular programme is one that a ...
Q: If a computer is capable only of manipulating and storing integers, what difficulties present themse...
A: The answer as given below steps:
Q: How much of a part will cloud computing play in the future of e-commerce?
A: Introduction: Cloud computing is described as the availability of computer system resources, most no...
Q: What is the minimum number of bits required in PC Morse code for a range of 10,000?
A: PC Morse code is also written as PCM code in short.
Q: hat happens if the cache is too small to hold the program's working set?
A: Introduction: When it comes to our programmes, cache size is crucial because if it is set too small,...
Q: PROGRAM FOR LoNGEST COMMON SUBSEQUECE B/W 2 STRINGS Input: output: abcdda, bdda. LENGTH OF SUBSEQUEN...
A: I give the code in Python along with output and code screenshot
Q: In the conversion of the following NFA into a DFA M using subset construction, what is ö(final state...
A:
Q: The parity check matrix is given as shown: Determine the code rate. Express your answer in fraction.
A: code rate = k/n = 4/7 = 0.571
Q: Assume that there is a shared connection (for example, an Ethernet bus) with a speed of 1 Mbps. How ...
A: Introduction: The all-encompassing Ethernet LAN protocol has now been thoroughly examined. Today's E...
Q: Write the quicksort algorithm and explain how it performs sorting. Analyze its time complexity in th...
A: Based on our understanding of partitioning in quick sort, we will now try to write an algorithm for ...
Q: Data mining: Explain the fundamental concept driving data base analytics.
A: Introduction: Data mining: Explain the fundamental concept driving data base analytics.
Q: Why and how do local minima affect k-means clustering? What are our options for dealing with these...
A: Introduction: Various initializations may generate different clusters due to the iterative nature of...
Q: How to design CNN in Contactless Authentication System Using Hand Gestures Technique
A: Answer the above questions are as follows:
Q: The power set of some set S, denoted P(S), is the set of all subsets of S (including S itself and th...
A: Dear learner , hope you are doing well , I will try my best to answer this question. Thank You!!
Q: module fir ( output [7 :0] Y, input input [7:0] A, B, C, X, clk, input validsample); [7:0] X1, x2, Y...
A: Throughput: The pace at which a digital system computes outputs is known as throughput. Every two cl...
Q: Why is there a modem between a phone line and a communication adapter?
A: Introduction: To determine the modem area between a phone line and a communication adapter
Q: 5a Into what line would bytes with each of the following addresses be stored 0001 0001 0001 1011 1...
A:
Q: Match these PKI terms. CA v [ Choose ] trusted third-party agency responsible for issuing digital ce...
A: Cryptography is the process of securing sensitive data to protect it from malicious third-parties. I...
Q: Describe three system development approaches in system analytics.
A: Introduction: Three methods for system development in system analytics includes:
Q: Consider the following problem, and determine which aspects listed below are ambiguous (i.e., you ca...
A: Consider the following problem, and determine which aspects listed below are ambiguous (i.e., you ca...
Q: What is the router's boot-up procedure?
A: Router : A router is made up of numerous different sorts of parts. Any Cisco router, for example, wi...
Q: Describe the role that computers play in scientific research
A: Introduction Describe the role that computers play in scientific research.
Q: Is it feasible to use a DLL to implement a sorted linked list? What is the advantage of a DLL implem...
A: Doubly Linked List vs Singly Linked List Yes, it is possible to sort a linked list using a Singly l...
Q: ____________ style sheet allows Web designers to modify the appearance of elements in different file...
A: _______________ style sheet allows Web designers to modify the appearance of elements in different f...
Q: What problems have you encountered when adding or removing users in Windows 10 and Linux?
A: Introduction: Problems experienced while adding or deleting users in Windows 10 include the followin...
Step by step
Solved in 4 steps with 2 images

- Please use python The following equations estimate the calories burned when exercising (source): Women: Calories = ( (Age x 0.074) — (Weight x 0.05741) + (Heart Rate x 0.4472) — 20.4022 ) x Time / 4.184 Men: Calories = ( (Age x 0.2017) + (Weight x 0.09036) + (Heart Rate x 0.6309) — 55.0969 ) x Time / 4.184 Write a program using inputs age (years), weight (pounds), heart rate (beats per minute), and time (minutes), respectively. Output calories burned for women and men. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('Men: {:.2f} calories'.format(calories_man)) Ex: If the input is: 49 155 148 60Q. Find out the real and different roots of following equation.ax2 + bx + cwhere, a= 1, b=10, c=-24 & a, b, and c are coefficient and real numbers and also a ≠ 0.Need solution in more pythonic way use python3.In Python: The following equations estimate the calories burned when exercising (source): Women: Calories = ( (Age x 0.074) — (Weight x 0.05741) + (Heart Rate x 0.4472) — 20.4022 ) x Time / 4.184 Men: Calories = ( (Age x 0.2017) + (Weight x 0.09036) + (Heart Rate x 0.6309) — 55.0969 ) x Time / 4.184 Write a program using inputs age (years), weight (pounds), heart rate (beats per minute), and time (minutes), respectively. Output calories burned for women and men. Output each floating-point value with two digits after the decimal point, which can be achieved as follows:print('Men: {:.2f} calories'.format(calories_man)) Ex: If the input is: 49 155 148 60 Then the output is: Women: 580.94 calories Men: 891.47 calories
- If p is false, q is true, and r is true, determine the truth value of the statement. Show your work. (p → ~ r ) Ù (~ p → ~ r)Please give me only the solution to Question-4 solve it by c programming, and please give me the output of the code also!Find the Error(s) in the following program and state how to fix those error(s).
- In Python, Given a line of text as input, output the number of characters excluding spaces, periods, or commas. Ex: If the input is: Listen, Mr. Jones, calm down. the output is: 21 Note: Account for all characters that aren't spaces, periods, or commas (Ex: "r", "2", "!").Write a program to solve any number of equations Wares according to the equation where AX = B user enters when n equations and matrices A, B, and output is a matrix X = A ^ -1 B then applied the following equations as an example type output {Using Matlab only}Answer the given question with a proper explanation and step-by-step solution. Write a Python program in Google Colaboratory (Colab) to swap two variables in the following way. 1) Use a temporary variable 2) Without using a temporary variable
- What does the function return for any positive values of x and n ? The answer should be a general formula in terms of x and n. int what_do_I_do ( int x, int n ) { if ( n = = 1 ) return x; else return x + what_do_I_do ( x, n – 1 ); } C++ be quick pleaseModify question 2 from Lab 2 such that if the value for Celsius is 100 or more, also display “Above or equalBoiling point of Water”Otherwise, display “BelowBoiling point of Water” python codingSolve the following Program Using C++ solve it correctly and quickly please.

