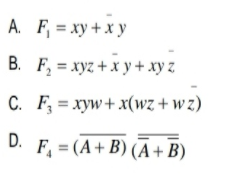
raw logic diagrams. implement the simplified expressions in Exercise 3.
Q: How do you define database security? A complicated administrative procedure governed the physical…
A: Database security considerations include using information security measures to secure database…
Q: Question 4: Funception Write a function (funception) that takes in another function func_a and a…
A: The code for the function is given followed by testing code. The screen shot shows the indentation…
Q: It is unclear where John von Neumann attended college.
A: Calculator John von Neumann For his mathematical contributions to economics, quantum physics, and…
Q: Explain how CDs and DVDs are utilized differently to store information as an example.
A: Introduction Here, we must discuss the various methods that CDs and DVDs are utilised to store…
Q: This article will define whole disk encryption (WDE) solutions and explain why they are required.
A: Definition Solutions for whole disc encryption (WDE) are critical in computer security. It is a…
Q: This topic concerns the number of gigabytes in one terabyte.
A: A gigabyte is a multiple of bytes of digital information. The prefix giga means 10⁹ in the…
Q: Convert the following hexadecimal numbers to decimal (base−10) numbers.…
A: Hello student
Q: public static void simpleLoop(int total) { String tmp = for (int x = 0; x< total; x++) { (x + ",");…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: First, write a Java method merge that takes as parameter a non-empty double array representing…
A: Code: import java.io.*; import java.util.*; public class MergeSalary { private static Scanner…
Q: 2. Write a class named MonthDays. The class's constructor should accept two arguments: • An integer…
A: Here we have given code in java for the given task. You can find the solution in step 2.
Q: What Windows 2016 "flavors" are available?
A: Server Core (no graphical user interface), Server with Desktop Experience (graphical user…
Q: Regarding computers, how many megabytes are required
A: Answer:
Q: Explain the Role of Management in Software Development & write briefly about the…
A: The area of computer science known as software engineering is responsible for the designing,…
Q: Internet research is being conducted, the activities of Mafiaboy How long ago and by what ways did…
A: Mafiaboy: Michael Calce, who at the age of 15 launched a large cyberattack and was known online as…
Q: What is the goal of the new framework for risk management? What makes it superior to the previous…
A: The goal of the new framework for risk management:
Q: Explain how CDs and DVDs are utilized differently to store information as an example.
A: CDs and DVDs are both examples optical disk storage format.
Q: Are firewalls capable of protecting your logical ports?
A: Your answer is given below. Introduction :- By blocking malicious or unneeded network traffic,…
Q: Data Mining is the process of extracting interesting patterns or knowledge from huge amount of Data.…
A: Please find the answer below :
Q: How must a firewall be deployed and configured, if required?
A: Firewall - In computer system, firewall is a network security system. It controls and monitors the…
Q: Explain why it is imperative that software solutions be developed and delivered quickly. What are…
A: Because they're designed and supplied promptly. Most clients cannot wait for sales to be produced…
Q: What does it mean to "back up your data"?
A: Introduction Data is information, for example, realities and numbers used to examine something or…
Q: what are the Common applications of machine learning?
A: Because machine learning goes so neatly hand-in-hand with large datasets, many common machine…
Q: How can a firewall be handled effectively? Explain.
A: Introduction: A firewall is a piece of network security equipment that monitors incoming and ongoing…
Q: What are the differences between top-down and bottom-up data security approaches? Why is the…
A: Difference between top-down and bottom-up data security approaches
Q: h property. b. Your class should have two constructors: one that takes all properties, and one that…
A: the solution is an given below :
Q: When was the first electronic digital computer developed and what was it?
A: The answer is given in the below step Happy to help ?
Q: 5. Write a matlab function (ave_idno) that will take the average of a number vector and stores it in…
A: The Matlab Code is given below:
Q: Conduct research to identify a company that has gone beyond e-commerce to develop an e-business…
A: Introduction: Amazon is one of the businesses that has excelled in e-business or e-commerce. It is…
Q: How can DDOS attacks be mitigated?
A: Introduction: Cut attack surface.Minimize the surface area that may be attacked to reduce attackers'…
Q: #include #include "Sequence.h" #include using namespace std; namespace CS3358_FA2022 { //…
A: Coded using C++.
Q: Included below are two strategies for reducing rework costs: In your opinion, does incremental…
A: Following these steps helps to reduce the number of errors and reworks: 1. Create a Quality…
Q: A multicore computer is a computer with several components.
A: A multi-core processor is an integrated circuit with two or more processors linked to it enabling…
Q: Consider your computer's data. Contains your computer any personal information? What would occur if…
A: Given: "Yes," the vast majority of private users save their private and sensitive information on…
Q: take a look at two classes in JavaScript that implement the same method but with two different…
A: JavaScript (often abbreviated to JS) is a programming language and one of the core technologies of…
Q: Where did John von Neumann attend school as a child
A: John von Neumann: John von Neumann, an American mathematician, was born on December 28th, 1903, in…
Q: Find and fix any logic and syntax errors. Program runs and produces. The sum of 2 and 5 is 7 The…
A: The above code answer in below step.
Q: ow does a "Firewall" fu
A: Introduction: Firewalls are software or hardware devices that prevent unwanted access to and damage…
Q: Explain Systems/Applications with Open Vulnerabilities
A: Systems/Applications with Open Vulnerabilities:-
Q: What are the social effects of an increasing percentage of the world's population using smartphones?
A: Definition: The way that people behave and conform to cultural standards has been drastically…
Q: It is essential to understand what system image recovery is.
A: Systems for computing: Operating systems and other systems collaborate in computer science to…
Q: unsigned int a = 6 E unsigned int b = 1 int c = a long d = unsigned long e = (Assume ints are 3…
A: I have answered below:
Q: Enter a BASH "glob" pattern that will exactly match only (non-hidden) files in the current working…
A: The solution is given below for the above given question:
Q: Several different companies provide the NOS-Network Operating System.
A: The question has been answered in step2
Q: When were the first flash drives introduced?
A: The question has been answered in step2
Q: B AA CD 1 Distances Between European Capitals 2 3 4 5 6 7 8 9 10 11 Athens Berlin 2.4 Exponential…
A: (A) 32768 (B) 9.22 * 1018 (C) 1.84 * 1019
Q: What steps should an organization take to deter workers from violating corporate policies or…
A: The type of employee policy violations and crimes may be categorized as 1)Accidental 2)Intentional…
Q: What issues and concerns does the use of non-integrated information systems raise?
A: The question has been answered in step2
Q: What are some of the challenges involved with IT infrastructure and management system management?
A: Let's discuss what are the major challenges involved in the it infrastructure management.
Q: Write a program which counts the types of characters within a string input. PROGRAM DESIGN The…
A: In this question we need to write a python program which takes a string as input from user and…
Q: What are the many types of malware? What differentiates worms and viruses?
A: Malware Anything that is purposely destructive to a computer, network, or server is known as…
Also draw logic diagrams. implement the simplified expressions in Exercise 3.
Step by step
Solved in 2 steps with 3 images

- If L1={w∈{a,b}* | w starts with a} and L2={w∈{a,b}* | |w|≤ 3} then | L1 ∩ L2 | = a) 15 b) infinity c) 7 d) 12 e) 8 f) 4Let A = {a, b, c}, B = {x, y}, and C = {0, 1}.If S = { x | 0 ≤ x ≤ 10}, A = { x | 1 ≤ x ≤ 5}, B = { x | 1 ≤ x ≤ 6}, and C = { x | 2 ≤ x ≤ 7}(a) S ⋃ C(b) A ⋃ B(d) A’ ⋂ C(c) A’⋃ (B ⋂ C)(e) (A ⋂ B) ⋃ (B ⋂ C) ⋃ (C ⋂ A)
- Rahul is a maths genius so he came up with a game and as raj is Rahul's best friend so Rahul decided to play the game with raj. Rahul gives raj two numbers LL and RR and asks raj to find the count of numbers in the range from LL to RR (LL and RR inclusive) which are a digit palindromic. A number is a digit palindromic if its first digit is the same as its last digit. As raj is not very good at maths so your task is to help Raj find out how many numbers are a digit palindromic in the range LL to RR. For example if LL = 88 and RR = 2525 .The following numbers are a digit palindromic in the range of LL to RR: 8, 9, 11, and 22. If LL = 12511251 and RR = 12661266. The digit palindromic numbers are 1251 and 1261. Input format The first line contains an integer denoting the number of test cases. Each test case is described by a single line that contains two integers LL and RR. Output format For each test case output, an integer denoting how many a digit palindromic numbers are there in the…Given a set of cities, the central point is the city that has the shortest total distance to all other cities. Write a program that prompts the user to enter the number of cities and the locations of the cities (coordinates), and finds the central city and its total distance to all other cities. Assume that the maximum number of cities is 20. Enter the number of cities: 5 Enter the coordinates of the cities: 2.5 5 5.1 3 1 9 5.4 54 5.5 2.1 The central city is at (2.5, 5.0) The total distance to all other cities is 60.81Computer Science Write a Java program that reads a line and a line segment and then determines whether they intersect or not. When they overlap completely, consider that as intersecting. Use variables ((lp1x, lp1y), (lp2x, lp2y)) to represent a line and ((sp1x, sp1y), (sp2x, sp2y)) to represent a line segment
- Give English language translations of the following wffs where L(x, y) is “x loves y”, H(x) is “x ishandsome”, M(x) is “x is a man”, P(x) is “x is pretty”, W(x) is “x is a woman”, k is “Kathy”, andj is “John”.(a) (∀x)(W(x) → (∀y)[L(x, y) → M(y) ∧ H(y)])(b) (∃x)[M(x) ∧ H(x) ∧ L(x, k)](c) (∃x)(W(x) ∧ P(x) ∧ (∀y)[L(x, y) → H(y) ∧ M(y)]) (d) (∀x)[W(x) ∧ P(x) → L(j, x)]Format.cpp)c++ Write a program that gets two real valuesfrom the user, prints their sum and product in scientificnotation, and prints their sum and product in fixed pointnotation. Print answers to three decimal placesWrite a program that inputs a number and checks whether it is a perfect number or not. A perfect number is the number that is numerically equal to the sum of its divisors. For example, 6 is a perfect number because the divisors of 6 are 1, 2, 3 and 1+2+3=6
- Write a program to calculate the surface area and volume of a square pyramid. A square pyramid has a base that is square and all triangle faces are congruent isosceles triangles. (An isosceles triangle is a triangle in which two of the sides are equal. Length of the base: a Height of the pyramid: h Volume = a2h/3 Slant height, s = sqrt(h2 + (a/2)2) This is the Pythagorean Theorem part. Area of one pyramid side = s*a/2 Test Case #1 Height(h): 5.0’ Base(a): 2.5’A geometric sequence is a sequence of numbers where each term after the first isfound by multiplying the previous one by a fixed, non -zero number calledthe common ratio. For example, the sequences2, 6, 18, ....3,15,75, ….are a geometric sequences with common ratios 3 and 5 respectively. A geometricsequence is generally characterized by three numbers, the first term ‘a’, thecommon ratio ‘r’ and the number of terms ‘n’. A geometric series is the sum ofnumbers in a geometric sequence. 2+6+18 and 3+15+75 are examples of geometricseries with three terms each.The nth term of a geometric series with initial value ‘a’ and common ratio ‘r’ isgiven by: ?? = ???-1. While the sum of a geometric series is given by:?(1 - ??)1 - ?Create a class GeometricSeries to model a Geometric series. Using friend function,overload the ‘~’ operator to find the nth term of the series. Likewise, overload the‘!’ operator (using a friend function) to find the sum of a Geometric series.Provide a function display() in…In city street grids, intersections are often defined by two integers, counting the position of horizontal and vertical streets (sometimes called streets and avenues). Imagine traveling from position (h1, v1) to (h2, v2). How many blocks do you traverse?





