Read This Carefully!! (For your eyes-only) Your task, should you choose to accept it, is to design an application t will accept any phrase as input and allow the user to encrypt or decry it. The program should use one or two keys (two is highly recommend to encrypt the message. These keys could be made up of an integer - a number between -32767 and +32768 or anything else you think might example, the key could be used to shift the letters of the alphabet to th For example, the letter "A" encoded with a key of “3" would produce three letters to its right in the alphabet. If the key is large enough that end of the alphabet, the program should "wrap around" to a letter near
Read This Carefully!! (For your eyes-only) Your task, should you choose to accept it, is to design an application t will accept any phrase as input and allow the user to encrypt or decry it. The program should use one or two keys (two is highly recommend to encrypt the message. These keys could be made up of an integer - a number between -32767 and +32768 or anything else you think might example, the key could be used to shift the letters of the alphabet to th For example, the letter "A" encoded with a key of “3" would produce three letters to its right in the alphabet. If the key is large enough that end of the alphabet, the program should "wrap around" to a letter near
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
Please help using java
Read the instructions carefully
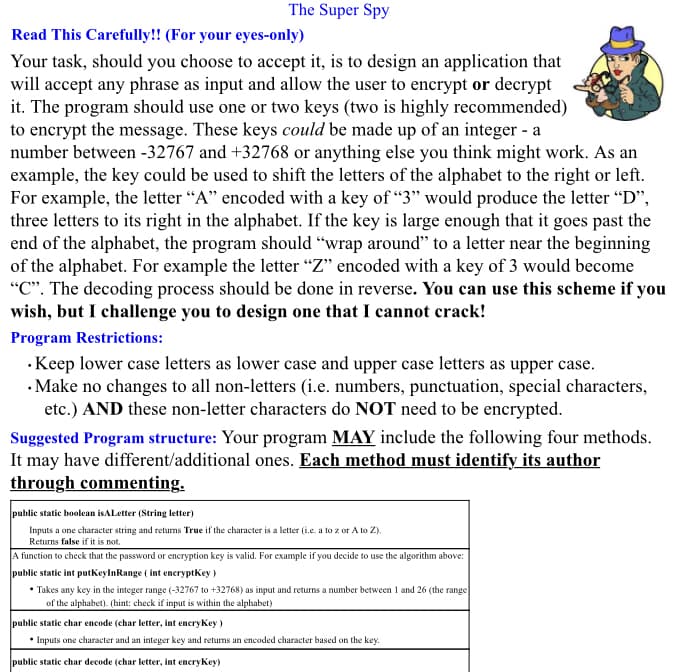
Transcribed Image Text:The Super Spy
Read This Carefully!! (For your eyes-only)
Your task, should you choose to accept it, is to design an application that
will accept any phrase as input and allow the user to encrypt or decrypt
it. The program should use one or two keys (two is highly recommended)
to encrypt the message. These keys could be made up of an integer - a
number between -32767 and +32768 or anything else you think might work. As an
example, the key could be used to shift the letters of the alphabet to the right or left.
For example, the letter “A" encoded with a key of "3" would produce the letter "D",
three letters to its right in the alphabet. If the key is large enough that it goes past the
end of the alphabet, the program should "wrap around" to a letter near the beginning
of the alphabet. For example the letter “Z" encoded with a key of 3 would become
"C". The decoding process should be done in reverse. You can use this scheme if you
wish, but I challenge you to design one that I cannot crack!
Program Restrictions:
· Keep lower case letters as lower case and upper case letters as upper case.
· Make no changes to all non-letters (i.e. numbers, punctuation, special characters,
etc.) AND these non-letter characters do NOT need to be encrypted.
Suggested Program structure: Your program MAY include the following four methods.
It may have different/additional ones. Each method must identify its author
through commenting.
public static boolean isALetter (String letter)
Inputs a one character string and returns True if the character is a letter (i.e. a to z or A to Z).
Returns false if it is not.
A function to check that the password or encryption key is valid. For example if you decide to use the algorithm above:
public static int putkeylnRange ( int encryptkey )
• Takes any key in the integer range (-32767 to +32768) as input and returns a number between 1 and 26 (the range
of the alphabet). (hint: check if input is within the alphabet)
public static char encode (char letter, int eneryKey )
• Inputs one character and an integer key and returns an encoded character based on the key.
public static char decode (char letter, int encrykey)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY