Recursive Exercises ALL PROGRAMS LISTED BELOW MUST USE RECURSION 1. Write a program that asks the user for a number then adds up ALL of the numbers from 1 to n, after squaring them. Ex/ if the user inputs 5 the answer should be 55
Recursive Exercises ALL PROGRAMS LISTED BELOW MUST USE RECURSION 1. Write a program that asks the user for a number then adds up ALL of the numbers from 1 to n, after squaring them. Ex/ if the user inputs 5 the answer should be 55
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 10PE
Related questions
Question
Answer the given question with a proper explanation and step-by-step solution.
All the
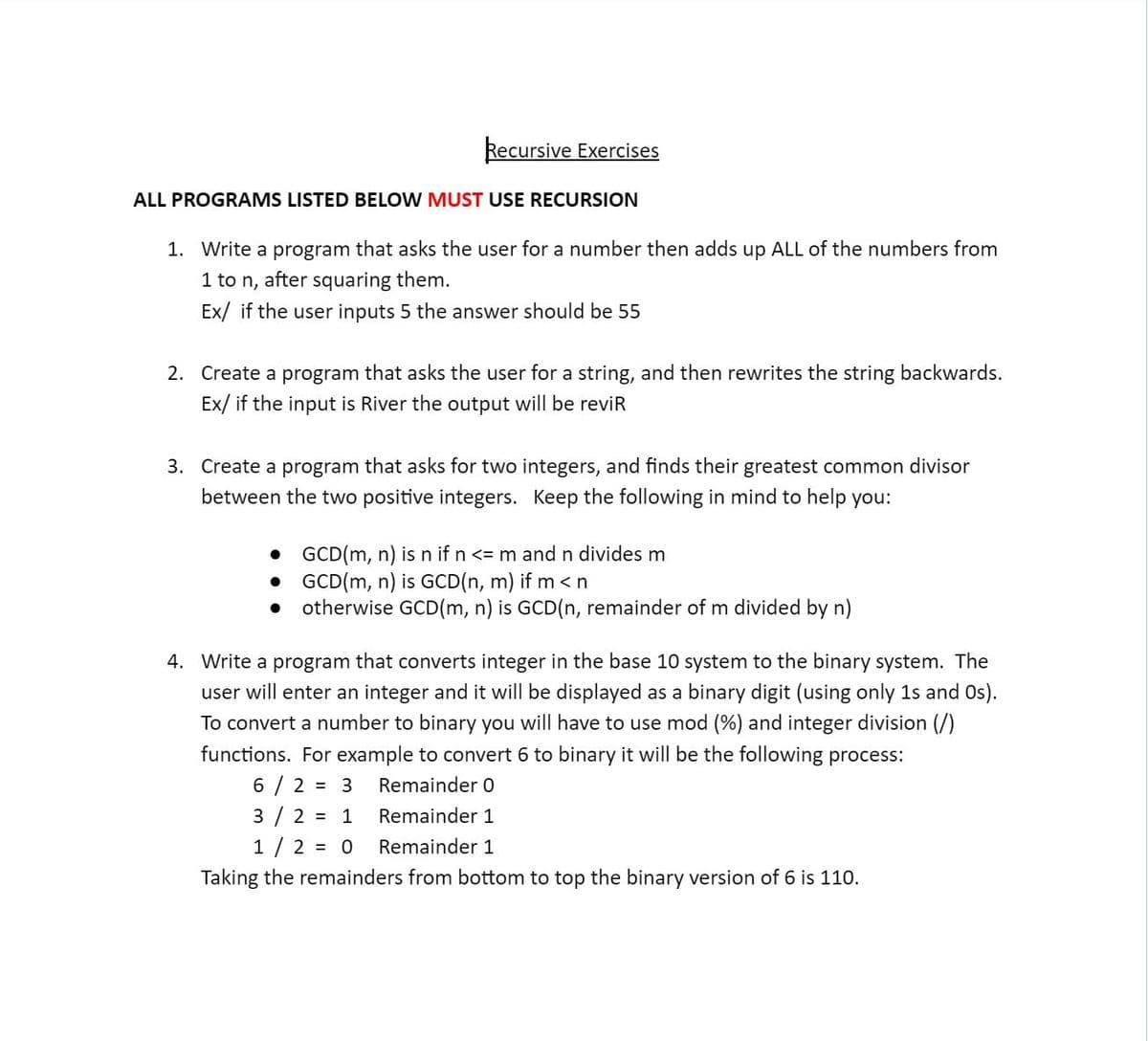
Transcribed Image Text:Recursive Exercises
ALL PROGRAMS LISTED BELOW MUST USE RECURSION
1. Write a program that asks the user for a number then adds up ALL of the numbers from
1 to n, after squaring them.
Ex/ if the user inputs 5 the answer should be 55
2. Create a program that asks the user for a string, and then rewrites the string backwards.
Ex/ if the input is River the output will be reviR
3. Create a program that asks for two integers, and finds their greatest common divisor
between the two positive integers. Keep the following in mind to help you:
GCD(m, n) is n if n <= m and n divides m
GCD(m, n) is GCD(n, m) if m <n
otherwise GCD(m, n) is GCD(n, remainder of m divided by n)
4. Write a program that converts integer in the base 10 system to the binary system. The
user will enter an integer and it will be displayed as a binary digit (using only 1s and Os).
To convert a number to binary you will have to use mod (%) and integer division (/)
functions. For example to convert 6 to binary it will be the following process:
6/2 = 3
Remainder O
3/2 = 1
Remainder 1
1/2 = 0
Remainder 1
Taking the remainders from bottom to top the binary version of 6 is 110.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage