Refer to the below output, which of the following can be determined about port security?
Refer to the below output, which of the following can be determined about port security?
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter9: Supporting Mobile Devices
Section: Chapter Questions
Problem 9TC
Related questions
Question
9
subject Scaling Networks
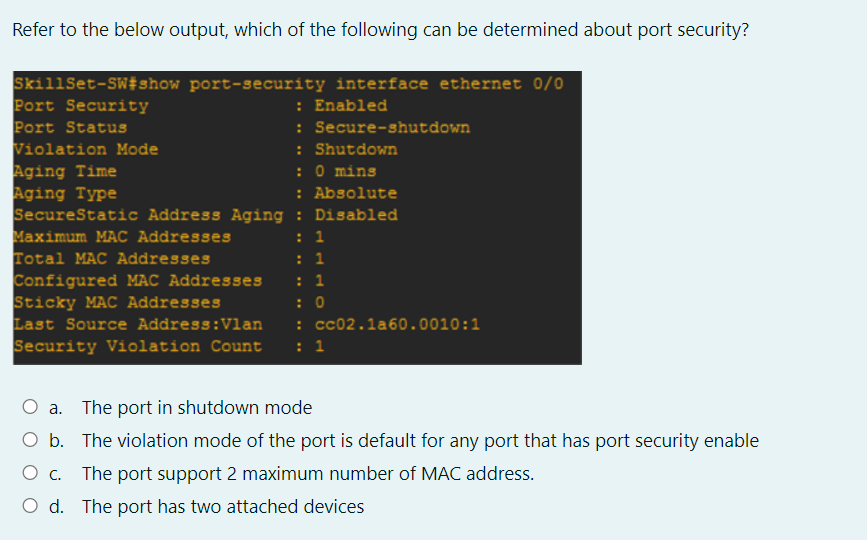
Transcribed Image Text:Refer to the below output, which of the following can be determined about port security?
SkillSet-SW#show port-security interface ethernet 0/0
Port Security
Port Status
Violation Mode
Aging Time
Aging Type
SecureStatic Address Aging : Disabled
Maximum MAC Addresses
Total MAC Addresses
Configured MAC Addresses
Sticky MAC Addresses
Last Source Address:Vlan
Security Violation Count
: Enabled
: Secure-shutdown
: Shutdown
: 0 mins
: Absolute
: 1
: 1
: 1
: 0
: cc02.1a60.0010:1
: 1
a. The port in shutdown mode
O b. The violation mode of the port is default for any port that has port security enable
The port support 2 maximum number of MAC address.
O d. The port has two attached devices
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

LINUX+ AND LPIC-1 GDE.TO LINUX CERTIF.
Computer Science
ISBN:
9781337569798
Author:
ECKERT
Publisher:
CENGAGE L