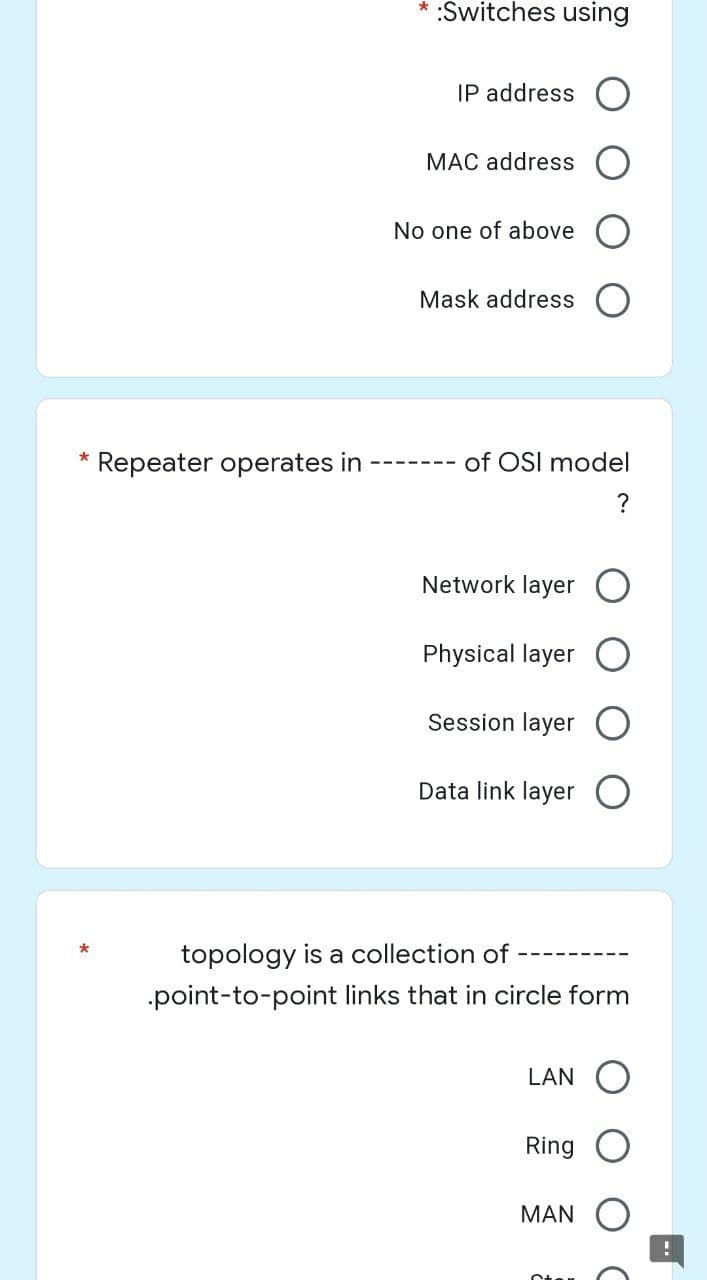
Repeater operates in of OSI model ?
Q: ennie is an ice cream parlour owner. She only sells 9 different type of ice creams. The ice creams…
A: Q: Code the given problem (Language used: java)
Q: Give your own 5 rules to get rid of being infected by computer viruses.
A: Introduction: Consider implementing the following steps in order to acquire sensitive information…
Q: Why should I maintain two copies of the identical file if I can just delete one of them?
A: reason to maintain two copies of the identical file if I can just delete one of them is given in…
Q: What are the benefits and drawbacks of storing data on the cloud? Companies that provide cloud-based…
A: According to the information provided in the question, cloud storage is always used to save the data…
Q: The element being searched for is not in an array of 100 elements. What is the maximum number of…
A: Let take and example of 5 element : 1 7 3 6 4 and search for 8 we have to compare with all five and…
Q: What are the many routes that one may use in order to generate fresh concepts? Explain why you do…
A: 1) The Method of Storyboarding 2) Methods for Creating a Mind Map: 1) The Method of Storyboarding A…
Q: ways to make the protection of personal information more effective?
A: Methods for enhancing data privacy include:- 1) Keep your data source (computer, mobile) virus-free:…
Q: What has been preventing IPv6 adoption? What is driving IPv6 uptake right now?
A: Intro What has been preventing IPv6 adoption? What is driving IPv6 uptake right now?
Q: It is our recommendation that Flynn's taxonomy be expanded by one additional level. What aspects of…
A: Solution: Above the level at which Flynn's Taxonomy is initially implemented, there is room for one…
Q: Why is it preferable to have a single multi-threaded process rather than several instances of a…
A: Single threaded processes Single threaded processes contain the execution of directions in a single…
Q: Find out more about testing for illegal access. In the context of safeguarding sensitive…
A: Intro A penetration test, or pen test, identifies, tests, and highlights security vulnerabilities.…
Q: How many subnets are created by the ?address 192.168.1.0255.255.255.248
A: here in the question ask for multiple choice question,
Q: A) If the matrix A= [2 5 1;7 3 6;2 5 4], find: 1- A' 2- A(2,3) 3-size(A) 4- A(:,2)=[] 5- Inv(A)
A: Find the required answer given as below :
Q: What are the problem that are associated with inter process communication? How you solved them?…
A: To process communication with each other with synchronization we use inter-process communication.…
Q: * What is the subnetwork for a host with IP ?address 200.11.15.56/28 200.11.15.32 200.11.15.16…
A: Answer in step 2
Q: Please help and thank you in advance. The language is Java. I have to write a program that takes…
A: The correct code is given below in the next step with code and output screenshots Now the full date…
Q: What are the different relational operators used in selection structures in the Python programming…
A: Find the required answer given as below : As per company guidelines we are supposed to answer only…
Q: Explain in detail the operating system's kernel, starting with the most basic components and working…
A: The answer is as follows
Q: ways to make the protection of personal information more effective
A: Strategies for enhancing the confidentiality of information? Methods for enhancing the…
Q: You will get a deeper understanding of cloud computing, social networking, and a variety of other…
A: Start: Enhance not just your understanding of social networking blogs but also that of cloud…
Q: What is the primary difference between the operating systems used by desktop computers and those…
A: Introduction: The mainframe OS is a network operating system that allows computers to execute…
Q: Provide some concrete examples of the top five most typical applications of system design and…
A: Manufacturing simulation: Simulation modelling has gained popularity recently. Many manufacturers…
Q: Is it possible to implement other network topologies, and if so, which of them do you like the most?
A: Mesh topology networks have the most connections, making them the most practical option. Because…
Q: Straight cable is connecting Different .devices true False O The NIC mean Networking interface card…
A: 1) True A straight-through cable is used in local area networks to connect different devices like a…
Q: Define the Kernel approach for building a feature space and explain how and why it is used to…
A: Introduction: It is largely comparable to the first thing that springs to mind when thinking about…
Q: In what ways might data profiling specifically help to improve overall data quality?
A: Introduction: Data profiling includes reviewing source data, examining structure, content, and…
Q: alk about the social and ethical problems that might crop up when putting information technology…
A: Introduction The following are examples of social and ethical consequences that might arise from…
Q: The following is a list of the several entry points available for files. I am interested in learning…
A: Given: To access an employee's data, file organisation simply means putting them in alphabetical…
Q: List and explain the challenges that may develop as a consequence of big data's vast volumes of…
A: Data mining for fresh insights is critical to company success, but the test should not be…
Q: benefits and drawbacks that cloud computing has to offer a small business, and how does this compare…
A: Answer to the given question: Cloud computing offers your business many advantages. It permits you…
Q: What is the static and dynamic scope? -Static scope: x=……. y=……. -Dynamic Scope: x=…….…
A: Ans:) Static and Dynamic scope of a variable are related to compile time and run time initialization…
Q: There is a clear separation between the code segment, the data segment, and the stack section. The…
A: A process is an example of a run program, and processes take up a specific amount of memory. It may…
Q: What are some of the numerous ways that one could conceive of new ideas? When coming up with ideas…
A: Numerous feedback techniques include: Story boarding: A storyboard is like a cartoon clip in that…
Q: Provide some concrete examples of the top five most typical applications of system design and…
A: The whole response is provided below: 1. Simulation and Production The popularity of simulation…
Q: What exactly are files that are output?
A: Computer file is used for recording the data in a storage device of computer . It is identified by…
Q: Explain JOBS and Earnings using Information and Communication Technology
A: Answer to the given question: Information and communication technologies (ICTs) are changing the…
Q: What are some of the elements that are often used into diagrams of network connections?
A: Introduction:- Some of the elements that are often used into diagrams of network connections
Q: The following is a list of the several ways files may be accessed. I am curious about the positives…
A: Given: The benefits of allowing guests and internal users to view files are listed below. The…
Q: The last question I have is this: what exactly is the point of artificial intelligence? Are there…
A: Artificial intelligence (AI) is a wide-ranging branch of computer science concerned with building…
Q: If you delete a file by accident and then later decide that you want it back, what steps should you…
A: If you accidentally remove anything, check Windows' Recycle Bin first. Nothing occurs when you…
Q: What are the planned parameters for the 5G network, such as the required frequency range, the uplink…
A: 5G network: The capabilities of 5G networks would be expanded to encompass not just linking people…
Q: 2. Series E by Jemar Jude Maranga Write a program that will print then items in the following…
A: I have written the correct code in C++ as an answer to this question in step 2. I have also provided…
Q: In order to show the five applications for system design and modeling that are used most often,…
A: Encryption: System Design encompasses design, modelling, and simulation services that allow rapid,…
Q: Investigate the commercial potential of Facebook and Twitter. What makes their material different…
A: Research on Online Social Networks: Research on Online Social Networks (OSN): An Overview Online…
Q: Please submit three examples to illustrate how education-oriented robots may be employed. Specify…
A: The question has been answered in step2
Q: If the lengths of the sides of a triangle are denoted by a, b, and c, then area of triangle is given…
A:
Q: Acquiring an understanding of social media and the concepts that underlie it Let's get things…
A: The above question is solved in step 2 :-
Q: Given three variables x, y, z write a function to circularly shift their values to right. In other…
A:
Q: If you are a developer rather than a user, you should utilise deep access rather than shallow…
A: Intro Deep access is a means of gaining access to non-local variables. It is used to keep a stack…
Q: any distinct types of computer software are there from wh
A: Introduction: Below the describe distinct types of computer software
Step by step
Solved in 2 steps

- Network latency issues are often caused by SELinux or AppArmor restrictions. True or False?Write down the OSI layers for each device as shown. Draw a NAT Table Entry at the Router for the Computer (A) (shown with a smiley face J) trying to reach the Web Server (listening at Port 80) as shown. You may use dynamic port numbers. Divide the LAN into 2 subnets and then re-draw it to show the subnets. Assume that you have a supply of switches as needed. A frame is sent from Computer A to Router R1, assume that it is using Ethernet. Draw the frame showing the Source and Destination MAC addresses, IP addresses, and port numbers.Use the following filter rule in Wireshark ip.flags.mf == 1 || (ip.flags.mf == 0 && ip.frag_offset > 0) Answer the following questions What is the size of the largest fragment you are able to find? What address is common to all the fragments of this size? 3. What is the size of the smallest fragment you are able to find?.
- q33- What is one of the characteristics is commonly associated with dynamic routing protocols? Select one: A. Requre special subnets masks B. Require less processing power than static routes require C. Require device configuration D. Consume some bandwidth to exchange routes informationAt university, we have many international students, who when at university communicates with their parents in their home country via university's IP based network. Students nowadays typ- ically use Whattsapp for their communication needs. By just focusing on the main Router at university, map this Router's functionality to OSI layers. Remember that incorrect mapping means deduction of the points.By providing an example of each, compare three types of Medium Access Protocols (MACs): channel partitioning, random access, and taking turns.
- The gRPC protocol does not have this: The gRPC protocol does not have this: a) Support for streams of requests or streams of responses. b) Ability to choose UDP or TCP for communication at the transport layer. c) Ability for the client to specify how long it's willing to wait for a response by providing a timeout. d) Use of HTTP/2 as an underlying protocol.Which two statements about routing protocols are true (choose 2). a) OSPF elects designed routers on multi-access links. b) RIP does not support classless routing. c) EIGRP uses broadcast traffic to establish adjacencies with its neighbors. d) RIP does not advertise a route beyond a hop count of 15. e) IBGP is an internal routing protocol.Suppose Bob is downloading files from an FTP server by sending a request to the server and the server sends the file to Bob. Suppose Bob’s computer is connecting to the server via point-to-point link. It takes Bob 0.83 seconds to download a 400 MB file and 0.43 seconds to download a 200 MB file. 1. What’s the bandwidth of the link? What’s the RTT? (Note: please use RTT rather than the one-way delay as the propagation delay and you can ignore the transmission delay of the short request and ACK in your calculation.) 2. Please explain why the time to download the 400 MB file is not exactly twice as much as the time to download the 200 MB file?
- 96. A _______ can check the MAC addresses contained in the frame. a. passive hub b. repeater c. bridge d. router10. Which layer establishes and terminates connections between cooperating applications?a) Link Layer b) Presentation Layer c) Session Layerd) Transport Layer e) None11. Which layer is related with the mechanical and electrical properties of cables andconnectors?a) Link Layer b) Presentation Layer c) Session Layerd) Transport Layer e) None12. Which term is used to describe the transmission if both sides can transmit but only onedirection at a time?a) Duplex b) Point to point c) Half duplex d) Simplex e) None13. Which one is an example for full-duplex and point to point transmission?a) Telephone conversation between two friendsb) TV or Radio broadcastingc) Downloading a file from a serverd) Listening music from a CD playere) None14. Which one is an example for point to multipoint transmission?a) Telephone conversation between two friends b) TV or Radio broadcastingc) Downloading a file from a server d) Listening music from a CD playere) None15. Which one is the name that can be used to…Lab – Routing Objective Learn and practice routing using Node and Express. Specification Create a web server that Accepts and processes request messages submitted from browser, and Generates and sends response messages back to browser for display. Your web server must be able to handle URL with hostname and port Request message URL: 0.0.1:3000 Response message: “SUCCESS!” URL with hostname, port and path echo Request message URL: 0.0.1:3000/echo Response message: “SUCCESS! echo” URL with hostname, port, path foxtrot and route parameter value kilo Request message URL: 0.0.1:3000/foxtrot/kilo Response message: “SUCCESS! Received kilo via foxtrot” where the value kilo must be retrieved via the route parameter Invalid/unexpected URL Request message URL: 0.0.1:3000/<any other value> Response message: “FAILED! Fix your URL.” Hostname 127.0.0.1 can be replaced by localhost. Port number 3000 can be replaced by any other port number that is from 1024 (2^11)…



