replicate themselves by independently exploiting vulnerabilities in networks. O a. Rootkit O b. Trojan Horse O c. Virus A d. Worm Clear my choice
Q: 1. In what ways are exploits, backdoors and rootkits differ from one another? 2. How can you detect…
A: The answer is given in the below step
Q: (i) Using the following passwords “ABCefg12” and “KojoGiggs12” as examples, discuss the strengths…
A: A strong password is one that is difficult for a computer or a human to guess, making it more…
Q: Thoroughly discuss the functions of the following software-based security threats: I ransomware…
A: As per our company guidelines we are supposed to answer only first 3 sub-parts. Kindly repost other…
Q: A piece of malicious code uses dictionary attacks against computers to gain access to administrative…
A: A logic bomb is a piece of code intentionally inserted into a software system that will set off a…
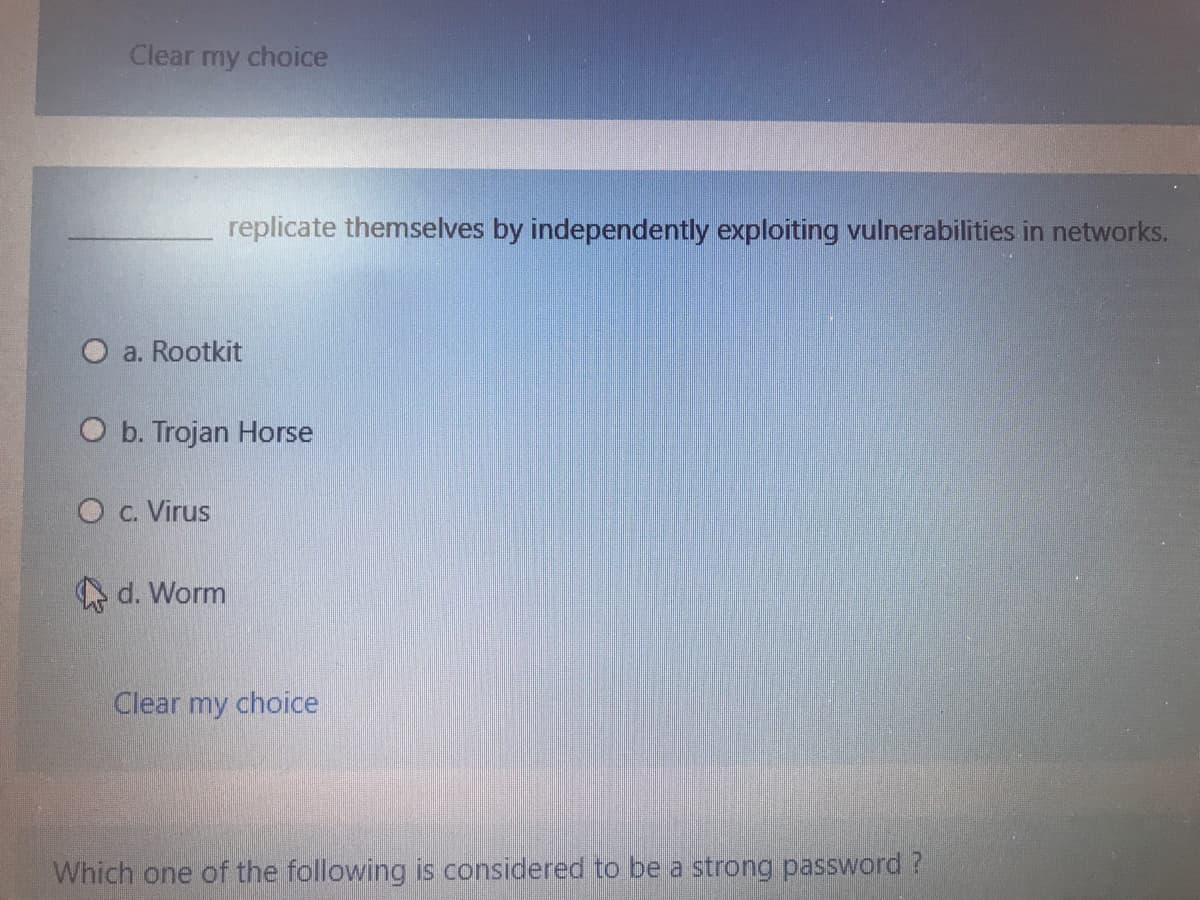
Q: replicate themselves by independently exploiting vulnerabilities in networks. O a. Rootkit O b.…
A: The question is mainly about the different types of malwares over the network. This malwares can…
Q: Choose the example of external security threat. O a. Mishandle colleague's confidential data O b.…
A: Refer step 2 for the answer.
Q: Using Social Engineering Attack tool, Harvest the google Username:c@c.com, Password:c@c.com using…
A: Start SET in a terminal. It should concoct its invite screen. .M"""bgd '7MM"""YMM MMP""MM""YMM…
Q: A company accidentally sends a newsletter with a mistyped website address. The address points to a…
A: A company sends a newsletter with a mistyped website address and noticed that the mistyped website…
Q: What is OWASP Zed Attack Proxy (ZAP) (formerly known as WebScarab)? How can it be used for security…
A: OWASP(Open Web Application Security Project) ZAP (Zed Attack Proxy) is one of the world’s most…
Q: ernet security suites usually include antivirus and antispyware tools. True or false?
A: Required: Internet security suites usually include antivirus and antispyware tools. True or false?
Q: Q1: How does remote user authentication differ from local authentication? Which one raised more…
A: Note: - As per the guidelines we can only answer one question at a time. Please resubmit the second…
Q: Q) Which type of Trojan horse security breach uses the computer of the victim as the source device…
A: Answer in step 2
Q: You open your browser and, rather than pointing to your home page, it opens to a Web page…
A: A is not correct because spyware does not have the set of symptoms described in the question. B is…
Q: 8) What is the goal of secure cookies? Explain. 9) What is the type of following attack? ( Attack…
A: Only an encrypted request over the HTTPS protocol is used to send a cookie with the Secure attribute…
Q: Which of the following attacks can lead to a token hijacking? O a. Network probing/scanning O b.…
A: Answer C
Q: Biometrics Technology: * Firewall: * Wireless Security: Steganography:
A: Biometric Technology for Security It is a pattern recognition system that identifies person…
Q: ent password-related hacks that occur nowadays. Which of these assaults has become more effective as…
A: Few of the most frequent password-related hacks that occur nowadays 1)Phishing It is the most…
Q: 37. Which of the following is the act of hiding a communication from an unknown source as being from…
A: answer to the above question is in step2.
Q: Which of these is required to have a "wormable" virus? 1. A privesc vulnerability 2. A supply…
A: A wormable virus means any future malware that uses this vulnerability could propagate from one…
Q: a) Classify the following attacks and their impact on the security goals 1. Assume that you have…
A: 1. Assume that you have sent a text file to your friend over the LAN, and the file content is viewed…
Q: Which ransomware tormented victims by deleting files incrementally with each hour the ransom was not…
A: A ransom ware can be denoted a malicious software that utilizes encryption on important data of a…
Q: What is a Network-Based Worm Defense System and How Does It Work? Justify why a possible worm is…
A: Worms in the network are a sort of virus or malware implanted in software that spreads from one…
Q: What do you call hackers that are paid to test the vulnerability of a network? * Black Hat Hackers…
A: Hello Student. Warm welcome from my side. Hope you are doing great. Here's your answer.
Q: 4.The cloning of cellular devices to utilize the network resources without paying; and cloning BSs…
A: Network Attack : A network attack can be defined as the situation in which the data sent from one…
Q: which of the following is not true about worm? O a. break in to computer by email e b. Not spread to…
A: Given that which of the following is not true about worm? a. break in to computer by email b. Not…
Q: d) Describe SNMPv1’s poor authentication method. e) Describe SNMPv3’s good authentication…
A: d) Describe SNMPv1’s poor authentication method. SNMPv1 is the first version of SNMP. It's easy…
Q: What is the mechanism of a wi-fi evildirect attack? At all costs, avoid using handwritten notes…
A: Introduction: Core Security security researchers claim to have discovered a Denial of Service (DoS)…
Q: lity to all compute
A: The single greatest hazard to all computer systems and networks is malware and social engineering…
Q: Using your favorite search engine, conduct a search for Internet of Things (loT) vulnerabilities.…
A: - We need to highlight a vulnerability in IOT devices and facts related to it.
Q: 2. Insert Yes or No: DOS Critical Malware Trojan Worm TrojanClicker.Win32/Doplik.B…
A:
Q: Introduction Of Attacks on IP Cameras? Structure and Presentation Of Attacks on IP Cameras?…
A: There are numerous diverse sorts of assaults. A few scenarios include a single step (e.g., DDoSa VPN…
Q: Save attack targets wireless access points that are exposed to nonfitered network traffic, such as…
A: In wifi __________ attack target wireless access point that are exposed to non filtered network…
Q: Man in the middle (MITM) attacks allow an attacker to access sensitive information by altering…
A: An ARP spoofing, also known as ARP poisoning, is a Man in the Middle (MitM) attack that allows…
Q: Principles of Information Security Q : Which of the following is an advantage of Packet Filtering…
A:
Q: ILOVEYOU virus spread on the internet with amazing speed through
A: The answer to the following question:-
Q: How does a Network-Based Worm Defense System Work? Justify why, in "Network Based Worm Defense,"…
A: According to your question From a security standpoint, the Internet very open. The central concept…
Q: A former employee discovers six months after he starts work at a new company that his account…
A: Kind of attack A former employee finds that his or her account credentials still give access to…
Q: Which of the following is NOT a reason why it is difficult to defend against today's attackers? O a.…
A: b. Greater sophistication of defense tools is the correct answer.
Q: The method of infiltration where an attacker calls an individual and lies to them in an attempt to…
A: Generally this is phishing technique, if the call is made my voice it is vishing. If the Phishing is…
Q: As a security specialist you are asked to analyze the following figure Observe pattern of messages…
A: A)Traffic analysis:This type of attack come under passive attack, traffic analysis, is subtler…
Q: security attributes is required to verifying the identity of a user and evict imposters
A: security attributes is required to verifying the identity of a user and evict imposters, sentences…
Q: __________ are often delivered to a PC through an email attachment and are often designed to do…
A: There are so many ways that attackers used to steal our data and all the above terms are briefly…
Step by step
Solved in 2 steps

- Explain the suitability or unsuitability of the following passwords: i. YK 334 ii. mfmitm (for “my favorite movie is tender mercies) iii. Natalie1 iv. Washington v. Aristotle vi. tv9stove vii. 12345678 viii. dribgibMultifactor authentication - how does it work? How does this aid in password theft prevention?Which of the following risks can be minimized by making bit-level copies of data? A. Compromising password hashes. B. Installing inappropriate forensics tools. C. (none of the choices is correct) D. Excluding hidden files.
- Which of the following goals of cryptography would be compromised, if an attacker is able to modify communication between two entities? a.Non-repudiation b.Confidentiality c.Integrity d.Authorization2. What is the ciphertext of the plaintext?: Symmetric encryption uses a single key.Key: 20Answeri._____________is an example of passive network security attack.a) denial of serviceb) replay c) modification of messaged) traffic analysisii. In _________attack, an entity deceives another by falsely denying responsibility for an act a) falsification b) repudiationc) corruption d) intrusioniii. Which one of these cryptographic techniques can be used for both confidentiality and authentication of message or data?a) MACb) Hash Function c) Public Key encryptiond) Symmetric key encryptioniv. Message authentication protects against___________a)passive attack b) active attack c) eavesdropping d) none of the attacksii. Which one is not categorized as an asset of the computer system?• a) Hardware • b) Software • c) Firmware• d) System Operato
- Give two examples of a bad password and for each example, explain why it isconsidered as bad.Which system attacks are distinguished by their ability to replicate? A. Trojan Horse and Stack Overflow. B. Rootkits and trap doors. C. Worms and viruses. D. Trojan horse and botnets.Explain the suitability or unsuitability of the following passwords: • a. YK 334 • b. mfmitm (for “my favorite movie is tender mercies) • c. Natalie1 • d. Washington • e. Aristotle • f. tv9stove • g. 12345678 • h. dribgib
- d) Describe SNMPv1’s poor authentication method. e) Describe SNMPv3’s good authentication method. f) How can good security be an enabler with SNMP?Which of these can be used to defend against some types of client attacks on a password system (note: the system must remain a user-knowledge-based authentication system)? Select one: a. Hash the passwords and store the hashes, rather than the plaintext passwords b. Store the password on a physical object c. Use one-time passcodes d. Limit the number of login attempts allowedSam transmitted an information over the network to David. David noticed that the information was modified during the transmission. What type of security protection was breached? A. Confidentiality B. Authentication C. Integrity D. Availability

