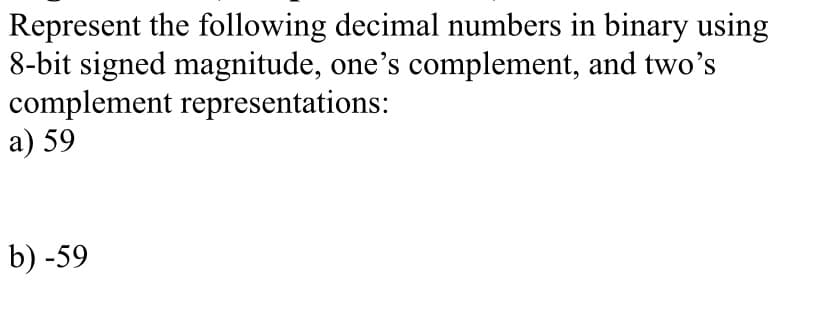
Represent the following decimal numbers in binary using 8-bit signed magnitude, one's complement, and two's complement representations: a) 59 b) -59
Q: What exactly are multimedia systems? Describe the obstacles that multimedia systems face, as well as...
A: Introduction: A multimedia system is in charge of developing a multimedia application. A multimedia ...
Q: Can you implement the Student class using the concepts of encapsulation? A solution is placed in the...
A: public class Student { private String name; private int rollNumber; public String getName() { ret...
Q: Create a program that computes a simple matrix vector multiplication b=Ax, Use OpenMP directives to ...
A: Code Screenshot and output below:
Q: ycertain whole number k ell may be different in various tasks). ituation in the arrangement (perhaps...
A: In this question, we are asked to display the minimum number operation in a programming language. Co...
Q: What is the main purpose of Enterprise Architecture Model from the Systems Theory point of view?
A: Enterprise architecture model: Enterprise architecture model is the concept where there is the theor...
Q: Create a pointer to a char value named nthCharPtr pointing to the 6th character of oddOrEven (rememb...
A: Given: Create a pointer to a char value named nthCharPtr pointing to the 6th character of oddOrEven(...
Q: Sort the given values by using Radix sort and counting sort algorithms. -2 -1 0 5 4 3 5 3 1...
A: The given values are sorted using the Radix sort and counting sort algorithms are as follows.
Q: 7. problems do not have defined solutions, since they infrequent basis. Occur on an
A: NOTE: In this question, we are asked to answer the 7th and 8th question. Clearly 7th question comes ...
Q: Do two iterations of Newton's Method with Horner's Method (synthetic division) to solve 0 = r + 11a*...
A: Horner's method is an algorithm for polynomial evaluation.
Q: What is the name of the data that has been relocated from RAM to virtual?
A: Introduction: RAM (Random Access Memory): RAM is a physical component in the computer that stores th...
Q: Using for loop, write a bash script that must go through all files stored in /etc directory. The loo...
A: Screenshot Of Code:
Q: (using classes SuperOverride & SubOverride) public class TestMethod { public static void main(String...
A: Based on the screens provide, it is observed that the code provided in separate java class files . B...
Q: WHY DO WE NEED TO GET RID OF DATA REDUNDANCY?
A: Suppose in a database we have two tables(relations). SchoolStudent (RollNo, Name, Age, BirthDate, Ge...
Q: How does the call established between two subscriber in mobile communication, explain in details wit...
A: Mobile Phone Communication. How it works: ...
Q: What is the best course of action for dealing with the Denial of Service assault based on the iPremi...
A: iPremier Information In 1996, two college students created iPremier, which was active in the e-comme...
Q: Write a short notes on, (i) Manuals as sources (ii) Help screens and systems (iii) Data dictionary a...
A: The Answer is in Below Steps
Q: Computer Science Using R language Student: 70, 80, 90, 85, 95, Create a histogram and Q-Q plot of ...
A: At a histogram, a rectangular area is used to depict statistical data that is proportional to the fr...
Q: Many new and better functions have been added to Microsoft Excel 2016. Which function in Excel 2016 ...
A: 1. The 'Tell Me' BoxThe "tell me" box is one of the newcomers to the Excel function and, without a d...
Q: What role does the Internet play in the evolution of a global information system? Should the Interne...
A: Introduction: The question about role does the Internet play in the evolution of a global informati...
Q: Try catch where is it usually used in Programming?
A: Exception is an event that causes abnormal behaviour of program.
Q: ix) Define a function named arrayCount that takes an array and a number as the parameters and the fu...
A: Define a function named arrayCount in Python that takes an array and a number as the parameters and ...
Q: Consider a Direct Mapped cache with 32-bit memory address reference word addressable. Assume a 2 wor...
A: Given: Goal: Find which block of cache does the address 253 maps to.
Q: Suppose you have a table t with a column labeled 'XYZ. What is the difference between t.YYZ.cumsum()...
A: Answer: For each row of the table t.YYZ.cumsum() sum of the all values of the column XYZ. For each r...
Q: Write a simple payroll program that will display employees information. Refer to the UML Class Diagr...
A: Given: Write a simple payroll program that will display employees information. Refer to the UML Clas...
Q: What decimal value does the 8-bit binary number 10101110 have if: a) it is interpreted as an unsigne...
A: The question is to write the answers related to binary number representation. As it a multipart type...
Q: The Business Implications Of These Results a. Explain how these detections impact the business, what...
A: The problems in a product impacts a business image both in long-term and the short-term.
Q: What are the contents of W and Temp after executing the following program?
A: ANSWER: Execution: Execution in PC and programming is the interaction by which a PC or virtual machi...
Q: What competitive advantages has Vivobarefoot achieved as a result of its infrastructure upgrade?
A: The question is to write the competitive advantages has Vivobarefoot achieved as a result of its inf...
Q: Investigate the three primary methods of IPv6 migration
A: Introduction The question is about three primary methods of IPv6 migration and here is the solution ...
Q: The degree of a relation is the number of its columns. True False
A: Defined the given statement as true or false
Q: PLEASE HELP ME GET A CODE. THANK YOUUU ANYONE!
A: Program Explanation- Apply the main function. Declare the numberPlus10. ShowNumberPlus10(n). ShowNu...
Q: Create state Table and Perform state table-based testing for the below state transition Diagram.
A: State Table: State/Input giveinfo or startPayTimer Paymoney PayTimerExpires Cancel print/ticket c...
Q: By using Truth Table, show that (p→q)→r and (p→r)→q are not logically equivalent
A: As given, we need to show that (p→q)→r and (p→r)→q are not logically equivalent.
Q: Activity 5. Identify an application/system interaction scenario or a specific task. Execute Donald N...
A: The answer is given below.
Q: Print the area of a polygon: --------------------------------- Input the number of sides of the poly...
A: Formula to find area of a n sided polygon with length l is l2n/4*tan(180/n) (in degrees) l2n/4*tan...
Q: Question 1 In this question, you need to create an interface and an abstract class. For the interfac...
A: SUMMARY: -Hence, we discussed all the points.
Q: How do you create a file (document) using a vi text editor on the UNIX system? When using the Putty ...
A: How do you create a file (document) using a vi text editor on the UNIX system? When using the Putty ...
Q: Dihan has completed his bachelor's degree from the University. The University of offers bachelor pro...
A: NOTE: As per guidelines, we are allowed to answer only one independent question per post. Please pos...
Q: Using for loop, write a bash script that must go through all files stored in /etc directory. The loo...
A: The answer is given below:-
Q: What is the d-ary tree's minimum feasible depth?
A: minimum feasible depth of a d-ary tree is Ω (log n / log d). Here, "n" is the number of nodes prese...
Q: Task 1: 1-bit Full Adder For this task, you will be building a 1-bit Full Adder circuit. To begi...
A:
Q: explain with proper working that how we can come up with these answers.
A: Consider the given :
Q: What does the term Cell mean in terms of computer architecture? (Include details)
A: Introduction: CELL is a microprocessor chip with parallel processing and multi-core design in comput...
Q: What will be the output of the program ? #include int main() { int k=1; printf("%...
A: Ternary operator takes three operands. It is simplest form of if else. Syntax:- Variable_name= (co...
Q: 2- Show how each of the following MIPS instructions is converted into machine code. Assume the memor...
A: Answer:- Solution: Conversion of machine code to MISP can done by following below steps ...
Q: T(1) = 1 T(n)= T(n - 1) + n² , n > 1
A: we need to find recessive equation for T(n)=T(n-1) +n2 using telescoping method
Q: The password is stored in a file. If you want to keep anything safe, hash it rather than encrypt it....
A: - We need to talk about a password file.
Q: Kindly give working code and output with explanation i have output in terminal like this: [[22, 3...
A: If you want to print output in the terminal and save it as a pdf file: from fpdf import FPDF # ...
Q: WHY DO WE NEED TO GET RID OF DATA REDUNDANCY?
A: ANSWER: Data Redundancy: Data redundancy takes place while the identical piece of information is sav...
Q: What methods are used to process data? (Include details)
A: Introduction: What methods are used to process data? (Include details) Manual, mechanical, and elect...
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- A(n) __________ is an integer stored in double the normal number of bit positions.Represent the following decimal numbers in binary using 8-bitsigned magnitude, one’s complement, two’s complement, andexcess-127 representations:1. a) 892. b) −893. c) 664. d) −66Represent the following decimal numbers in binary using 8-bitsigned magnitude, one’s complement, two’s complement, andexcess-127 representations.1. ◆a) 772. ◆b) −423. c) 1194. d) −107
- 6. Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below. Show the sign, exponent, and mantissa (significand).b. 11.22656251)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625Represent the following decimal numbers in binary using 8-bit signed magnitude, one'scomplement, two's complement, and excess-127 representation: a) 77 b) -42
- Show the numbers given below according to the decimal system in both binary and hexadecimal order by using the two's complement representation in 32 bits. a) 482 b) -28035) Assuming seven-bit two’s complement binary representation, write the bit patterns for the following decimal numbers in hexadecimal: a) -73b) -1c) 94Represent each of the following integers as 10-bit two’s complement binary numbers.i) -18510 ii) 15610 iii) -20510 iv) 16910
- 3. Represent the following decimal numbers in binary using 8-bit signed magnitude, one'scomplement and two's complement:a. 77b. −42c. 119d. −107Represent the following numbers to its 6-bit binary representation and perform binary subtractionusing 2’s compliment representation 50-30?1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?

