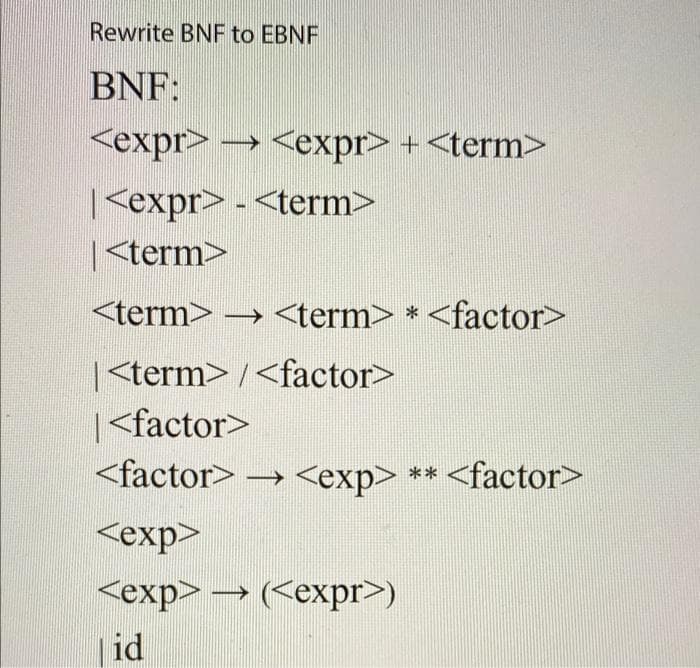
Rewrite BNF to EBNF BNF: Кеxpr> -→ + | - | → * | / | → ** → () |id
Q: In database management, which of the following is not a characteristics and possible drawback of…
A: In a relational view, there are various special characteristics but simultaneously it has certain…
Q: Computer Science C Language program break and continue statement do # 2 nested loops. modify make…
A: The break and continue statements are important because these statements are used to jump out of…
Q: Is a single person capable of orchestrating a distributed denial of service attack?
A: Introduction: What is a distributed denial-of-service assault, and how can a single individual…
Q: Change each number in base (0 1200 four
A: Given question with different numbers with different bases We have to convert it into base 10
Q: Create an algorithm for deleting all nodes with a duplicate key in a linkedlist.
A: The code is given below.
Q: For software development, what is it that makes up the four pillars?
A: Definition: Design, coding, testing, and maintenance are the four concepts that guide the software…
Q: What are the key distinctions between a packet switch network and a circuit switch network?
A: The distinctions between circuit switch network and packet switch network are given below:- Circuit…
Q: Create succinct notes (no more than three lines) on the following subjects:…
A: WHERE DO MANCHESTER CODES COME FROM: Manchester codes are line codes in which the encoding of each…
Q: Describe the security that can be achieved through CDMD spread spectrum.
A: CDMA spread spectrum: CDMA uses spread bandwidth techniques and a unique coding system to achieve…
Q: Write a C program to write the sequence seen below using a while loop: • 1--99---3 • 2--98---4…
A: Program: #include <stdio.h> int main() { int n; scanf("%d",&n); for(int…
Q: Assuming thelist has 10 elements, how many elements are in thelist[:9]?
A: thelist[:9] Here original number of elements in thelist is 10.
Q: Make clear how the software development lifecycle and user-centered design are linked.
A: Software life cycle models (a.k.a. process models) depict the software development life cycle…
Q: Describe an iterative algorithm that takes as input a list of n distinct integers and finds the…
A: 1. Start 2. Declare variables 3. get an input list of n integers. 4. set max_even=0 5. for i=0 to n…
Q: What are the four critical activities that take place throughout the software development process?
A: The following are the four basic activities in software development: Program requirement…
Q: Question 3. Prove using the short north-east diagonals or any other mathematical method of your…
A: According to the information given:- We have to follow the instruction mentioned to prove the north…
Q: Each stage of the software development process should be examined for mistakes.
A: stages of software development process examined mistake.
Q: Q12: Write C++ program to print the following figures: 3 3 3 5555 5 7777777 १ १ १ १ १ १ १ १ १ 777777…
A: In this question we have to program the pattern using for loop in C++ Let's generate these pattern…
Q: A "distributed denial of service attack" is what it is termed, and it may be orchestrated by a…
A: Distributed denial of service: Multiple infected computer systems attack a target and create a…
Q: What can you do to ensure that this issue does not recur in the future?
A: The step-by-step procedure for avoiding stalemate is outlined inWhen two or more processes wait for…
Q: The following code is a Perl script, and it runs on Kali Linux. What is the result. # Perl…
A: The given script will output the following: HackOrDie!
Q: . Write VHDL code of 7 segment decoder as shown in figure below 1 7-segment decoder 4
A: Solution:- Library ieee; Use ieee.std_logic_1164.all; Use ieee.std_logic_unsigned.all; Use…
Q: What Is a Surrogate Key Definition?
A: Let us see the definition below,
Q: Which of the following returns the Boolean value True when thestrPetName variable contains the…
A: The question is to choose the correct option from the given options.
Q: How is a hash value safeguarded for message authentication? Can a MAC algorithm be exploited without…
A: Benning: hash function is generated by the sender combining a message with some symmetric key,…
Q: What sort of variable is required to use an object in code?
A: According to the question the data type identify the value with object variable in the code always…
Q: Assume that a database does not enforce the requirement of maintaining referential integrity. Is it…
A: yes Referential Integrity - It means referring rows of one table to rows of another table. It…
Q: Put the following code into a complete C program: int i = 0; void func(char *str1, char *str2) {…
A: According to the Question below the Solution: Output:
Q: Explain the difference between user-centered design and the software development lifecycle.
A: User centered (UCD) is a bunch of cycles that places clients at the focal point of item plan and…
Q: What exactly is it that the basic principles of software engineering do not take into consideration?…
A: Given: When a database automatically inserts a new record into a table that may be specified as the…
Q: Modify it so that it write the contents of String[] into a file named fileLoop1.txt: package…
A: Given data, Modify it so that it writes the contents of String[] into a file named fileLoop1.txt:…
Q: ava: Arrays a1, a2… are populated as shown; display a[i] for each calls to arr; if a[i] less than…
A: Task : Given the array and the partial code. The task is to complete the code according to the…
Q: Describe an iterative algorithm that takes as input a list of n distinct integers and finds the last…
A: The problem is based on the basics of loops in programming languages.
Q: what are some of the things that ordinary people can and should do to protect themselves from…
A: Some of the things that ordinary people can and should do to protect themselves from network…
Q: What is a Deep URL, and how does it work?
A: Deep URL - It is a type of link which directs the user directly to application instead of web…
Q: Write and implement a program using JAVA and GUI, to find the devising and multiplication for three…
A: Java Program using Swings:- import javax.swing.*;import java.awt.event.*; public class Calci…
Q: /write an essay on the impact of social media.
A: Social media is having the great change in today to day life. It can be change the way that can…
Q: With the help of appropriate examples, discuss the memory representations of 1D and 2D arrays in…
A: A 1D array is a collection of variables of the same data type. It is sometimes referred to as a…
Q: give results of "118 % 11" and "118 // 11" in python
A: The Answer is in Below Steps
Q: Labyrinth solver code with shortest path algorithm with c programming language (I would appreciate…
A: The idea is inspired from Lee Algorithm and uses BFS. We start from the source cell and calls BFS…
Q: Name three virtualization tools. Contrast them
A: VIRTUALIZATION TOOLS(Software) 1) SolarWinds Virtualization Manager SolarWinds Virtualization…
Q: Write method findZero, as started below. findZero should return the index of the first element of…
A: JAVA Program for above : import java.util.Scanner; class Prog{ // required function for…
Q: What are the benefits of mobile technology?
A: Dear learner , hope you are doing well , I will try my best to answer this question. According to…
Q: If you hold the mouse cursor over a jagged line in the code editor, what will happen to the line?
A: Jagged line in the code editor shows the warning in your code.
Q: What does it mean when you talk about a "surrogate main key"?
A: Please find the detailed answer in the following steps.
Q: In your opinion, what are a microcontroller's two most critical features?
A: Critical Features: A critical feature is a portion of a flood protection system that is vital and…
Q: Which is preferable, fully qualified or unqualified references to subprograms, variables, and…
A: Commencement: He must first call another officer in the sales department and request that he provide…
Q: Using the code below, answer the following questions: 1) What are each of the 3 functions…
A: NOTE - As per our guidelines we are supposed to answer only the first three parts, please re-submit…
Q: What do you think the word "computer" mean
A: The answer is
Q: re particularly concerned about the need to learn certain data warehousing skills prior to building…
A: In computing, a data warehouse (DW or DWH), otherwise called an enterprise data warehouse (EDW), is…
Q: What is Artificial Intelligence's (AI) ultimate purpose? Provide a summary of the several areas that…
A: Artificial intelligence: Artificial intelligence (AI) mimics the workings of human intellect.Goals:…
Step by step
Solved in 2 steps with 1 images

- Derive (id *id) + (id/id) from the CFG using rightmost derivation. Also construct parse tree. E ® (E+T) E ® T T ® T * F T ® T / F T ® F F® (E) F® id note: subject: compailer concept deptt: cs/ItDefine the rule echo(LST0, LST1). This rule describes LST1, which holds all the same elements as LST0, except that they are all repeated. You should expect LST0 and LST1 to always be nonempty lists. Please answer in GNU prolog4. Rewrite the BNF of Example 3.4 to add the ++ and -- unary operatorsof Java.
- Write a full coding in C Language using linked list. then, create a segment to seach Dshahreen.Rewrite the following EBNF grammar in BNF. <decl> → <ident_list> : (int | float | char); <ident_list> → <identifier>{,<identifier}.Draw an expression tree for the following, infix expression and find the prefix and postfix expression. (C+D+A*B)*(E+F)

