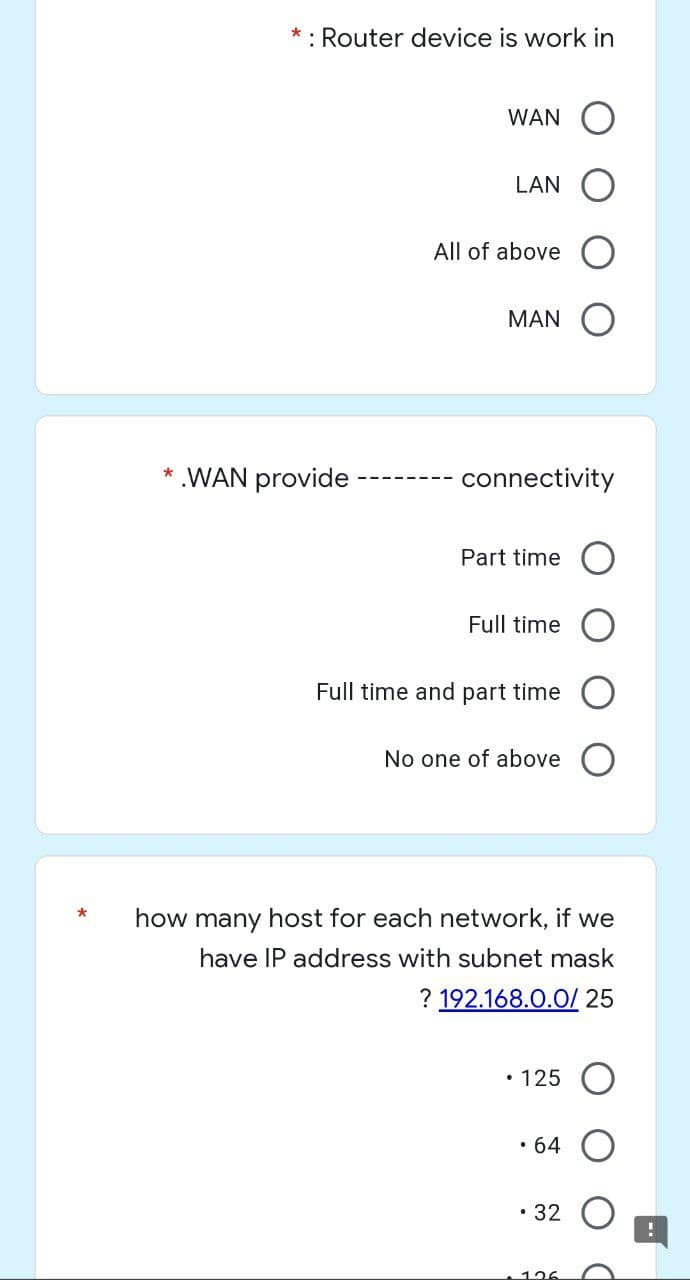
* * : Router device is work in WAN LAN All of above MAN connectivity Part time Full time Full time and part time No one of above how many host for each network, if we have IP address with subnet mask ? 192.168.0.0/ 25 • 125 • 64 32 * .WAN provide
Q: cterised by a number of key qualities, the most prominent of which are its velocity and its variety.…
A: Introduction: Big information is outlined as information with larger diversity, coming back in…
Q: What are the many routes that one may use in order to generate fresh concepts? Explain why you do…
A: 1) The Method of Storyboarding 2) Methods for Creating a Mind Map: 1) The Method of Storyboarding A…
Q: Is it advantageous to have a handicap, whether it be mental or physical, to use the internet? In…
A: Introduction:Internet helps visually challenged people. Internet options include: - Visually…
Q: 4. Write a program that prompts the user to enter a greeting and a name. The program should output…
A: The above program makes use of Scanner class defined in java.util package. This class takes in user…
Q: nct types of computer software are th
A: Introduction: Below the describe distinct types of computer software
Q: Blu-ray discs employ what kind of file system?
A:
Q: What role do you think the internet has in your life as a person who has a handicap, and why do you…
A: On the internet, they have the following options: - To begin, the internet is beneficial to those…
Q: What are the benefits of switching to a replacement strategy that prioritizes pages that have been…
A: Given: The knowledge that the most utilised pages in the previous few commands are likely to be used…
Q: When the first studies were done on the internet, what kinds of issues were researchers hoping to…
A: Launch: The internet is the best specialized equipment ever invented, a quantum leap in utility and…
Q: Provide some concrete examples of the top five most typical applications of system design and…
A: Intro System Design includes a broad range of design, modeling, and simulation services that enable…
Q: llowing are the two primary categories that make up the Ne
A: Introduction: Below the describe the two primary categories that make up the Network diagrams
Q: Which one of the following indexes would you choose to create to improve the runtime of the…
A: So in sql query, we use non-clustered index in b+tree index. so correct answer is:
Q: Data ageing is a process that is concerned with assuring in the context of intrusion detection…
A: Introduction: An intrusion detection system (IDS) is a software program that monitors a network for…
Q: What is fine-grained multithreading?
A: Introduction: The ability of the central processing unit (CPU) to provide several threads for…
Q: Explain the difference between the two primary graph traversal algorithms and also state which data…
A: As i have read guidelines i can provide answer of only 1 part of questions in case of multiple…
Q: OBJECTIVE To find a square and cube of a number.
A: Program
Q: When comparing the advanced features of Pfsense, Opnsense, and other commercial wireless router…
A: Inspection: Any DNS filtering business may help you with DNS filtering. It's more suitable to…
Q: In order to show the five applications for system design and modeling that are used most often,…
A: System Design encompasses a wide variety of design, modeling, and simulation services. These…
Q: Describe the steps that go into the program's analysis phase.
A: Start: Multiple gathered and processed elements are evaluated, correlated, and given the required…
Q: Acquiring an understanding of social media and the concepts that underlie it Let's get things…
A: The above question is solved in step 2 :-
Q: Interrupt Service Routine, whic n than the actual data transfer its
A: Interrupt Service Routines (ISR) are the core of any cutting edge microprocessor-based…
Q: There is a clear separation between the code segment, the data segment, and the stack section. The…
A: The process (extracted software) takes up a certain amount of memory. It is used to capture computer…
Q: What are the problem that are associated with inter process communication? How you solved them?…
A: To process communication with each other with synchronization we use inter-process communication.…
Q: Techniques that are not part of a systems analysis should be explained using well-structured…
A: Well-structured phrases: Well-constructed sentences are vital for efficient business writing because…
Q: The components of the operating system and the tasks they perform may be summed up in a single…
A: Introduction: The kernel is loaded initially when an operating system is loaded and stays in memory…
Q: How would taking this class help you learn even more about and develop a deeper appreciation for…
A: Computer science: The electronic computer was an important twentieth-century innovation. Computer…
Q: The importance of big data technologies in law enforcement and the criminal justice system…
A: Intro Big Data Big data is an important part of every industry, as the world generates 2.5…
Q: The creation of software makes use of a diverse selection of models, each of which, depending on the…
A: Answer: Software development uses several models, each with its own importance. The software…
Q: It is essential to determine the four parts of the project that will assist you in the…
A: Inspection: Four project characteristics that promote the use of software engineering in system…
Q: Do you have any suggestions for the topologies of network systems?
A: Network Topology A network topology is the physical and consistent plan of nodes and associations in…
Q: What are the disadvantages of corporate networking, and how may they be mitigated? A variety of…
A: Introduction: The disadvantages of corporate networking will be discussed, as well as some potential…
Q: Consider the following typed relational schema describing books and borrowers in a library:…
A:
Q: You will get a deeper understanding of issues such as cloud computing, social networking, and other…
A: Introduction: Improve your understanding of not only social networking blogs, but also cloud…
Q: Gain an in-depth and all-encompassing understanding of cloud computing as well as the blogs used for…
A: Answer: Social networking blogs provide facts and information on various social networking websites…
Q: How many distinct types of computer software are there from which to choose?
A: There are basically Two types of computer software present 1) System software 2) Application…
Q: In order to show the five applications for system design and modeling that are used most often,…
A: Encryption: System Design encompasses design, modelling, and simulation services that allow rapid,…
Q: Exist organizational, managerial, and technical elements that make up a system for storing and…
A: Given: Admin, tech, org. Senior managers understand the three measures to analyze the company's best…
Q: Describe the operation of an authentication system that follows the format of a challenge and a…
A: Answer: Explain how an authentication challenge–response system works. It's not immediately evident…
Q: Let G be a directed weighted graph with n vertices and m edges such that the edges in G have…
A: So, the Dijkstra Algorithm may be used to do this. The vertex name, I presume, may be changed to…
Q: What are the planned parameters for the 5G network, such as the required frequency range, the uplink…
A: 5G network: The capabilities of 5G networks would be expanded to encompass not just linking people…
Q: How can health informaticists standardize healthcare data
A: Please find the answer below
Q: explain trojan horse threat in computers
A: Intro Trojan horse A Trojan horse is malicious malware or software that appears to be legal yet has…
Q: The internet is undoubtedly one of the most prominent manifestations of information and…
A: The Internet is a great tool for use in social movements today, thanks to advances in information…
Q: Explain the importance of firewalls in protecting computer networks and the secrecy of online…
A: Intro In answer a to the question, we must explain the relevance a of network scanning and…
Q: Examining the similarities and differences between structured and unstructured data through the lens…
A: Answer:
Q: In the context of the fields of business and information technology, please provide two instances of…
A: information technology is defined as the user computers, physical devices, infrastructure, store,…
Q: Explain the necessity of operating systems in your own words, and whether or not you can communicate…
A: Answer: The Need for Operating System: Operating System is a program that goes about as an Interface…
Q: :How can you do a training requirements assessment for an e-learning system?
A: Intro Companies undertake need-gap analyses to determine the skills needed for competitive success,…
Q: Could you provide a high-level overview of the many components that comprise the operating system?…
A: The above question is solved in step 2 :-
Q: First, you should define and describe the components of the core of the operating system that are…
A: Introduction: Components of the Operating System's Kernel that Make Up the Operating System The…
Step by step
Solved in 2 steps

- Q7. Suppose we have the following IP addresses for two different organizations, we have to create 5 networks having 30 hosts in it. Find first sub network ID, Fist address, Last address and Braodcast for each of the following given addresses.a. 17.23.120.8b. 252.5.15.111Let’s consider you have a Class C IP address 204.15.5.0/24. You have to determine whether it is possible to createfollowing network with the given IP address? If yes, what could be the possible ranges of IP addresses for thesubnetworks? Let’s consider the above network. If you are using VLSM /CIDR, determine what subnet mask numbers allow therequired number of hosts.For the given IP address 193.105.1.60/27, find the network address, First Address, Last address for the host, Broadcast address and next subnet address. please tery to anser in differnt way coz i dont same this answers to avoid plag try to do it in diffrent way with same answers Step 1 Given IP address 193.105.1.60/27 is a Class C address with CIDR /27 /27 means that the subnet mask is 255.255.255.224 Default subnet mask of Class C is /24 or 255.255.255.0 Here the CIDR is /27, so 3 bit subnetting is used, ie, 3- bit is borrowed from host part to network part. Number of hosts/subnetnetwork = 2m - 2, where m is the remaining bits in the host part, here m=5 =25 - 2=30 hosts Given IP 193.105.1.60/27 is in the network range 193.105.1.32 - 193.105.1.63 Step 2 Network address: It is the first address in the network range. So, 193.105.1.32 is the network address First Host address: It is the first valid host IP address which is…
- 49- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. What will be the last host address of 4th subnet? Select one: A. 194.12.1.254 B. 194.12.1.192 C. 194.12.1.253 D. 194.12.1.25548- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. What will be the range of usable (assignable) addresses in 4th subnet? Select one: A. 194.12.1.192 to 194.12.1.255 B. 194.12.1.193 to 194.12.1.254 C. 194.12.1.193 to 194.12.1.253 D. 194.12.1.192 to 194.12.1.25447- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. What will be the first host address in 3rd subnet? Select one: A. 194.12.1.190 B. 194.121.1.192 C. 194.12.11.191 D. 94.12.1.128 E. 194.12.1.129
- 46- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. What will the broadcast address of 3rd subnet? Select one: A. 194.12.11.95 B. 194.12.1.128 C. 94.12.1.191 D. 194.121.1.192 E. 194.12.1.19150- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. What will be the network address of 3rd subnet? Select one: A. 194.12.1.191 B. 194.12.1.96 C. 194.12.1.128 D. 194.12.1.129A Network with id: 192.168.0.0 and subnet mask 255.255.0.0 is given to you to split it in such a way thatfollowing classrooms are given adequate number of IPs based on their needs. Each classroom willoccupy its own subnet. The following information for each subnet must be included: Subnet ID CIDR Subnet Mask First IP usable in the subnet Last IP usable in the subnet Broadcast IP Address for the subnet Classroom1: 8 PCsClassroom2: 400PC and 4 PrinterClassroom 3: 2 PCsClassroom4: 62 PCs and a ServerClassroom5: 24PCs
- q41- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. Based on the designed address scheme, answer the question 41 – 50How many bits were borrowed for subnetting? Select one: A. 2 B. None of the above C. 4 D. 3Imagine you are the network administrator of University X having ? campuses in Towson, Maryland. Youwant to build a connected network of servers (each server is either a regular or a routing one), one at each campus,and want to choose some of them to be the designated routing servers. A routing server will serve regular servers whoconnect directly to it via high speed cables, and every regular server must connect to at least one routing server. Yourgoal is to minimize the total length of high speed cable that you must purchase. Given the geographic locations ofthe ? campuses, design a plan that requires (1) the shortest length of cable and (2) the least number of routing servers.Analyze the time and space complexity of your procedure.44- An organization currently requires 40 hosts for its sales department. Given the IP Address 194.12.1.0 /24, design an optimal address scheme usingTradition Subnetting method, which will enable the connection of the sales department’s 40 hosts in one subnet and uses the remaining subnets for other departments’ hosts in the future. What will be the total number of usable (assignable) addresses per subnet? Select one: A. 62 B. 65 C. 63 D. 64

