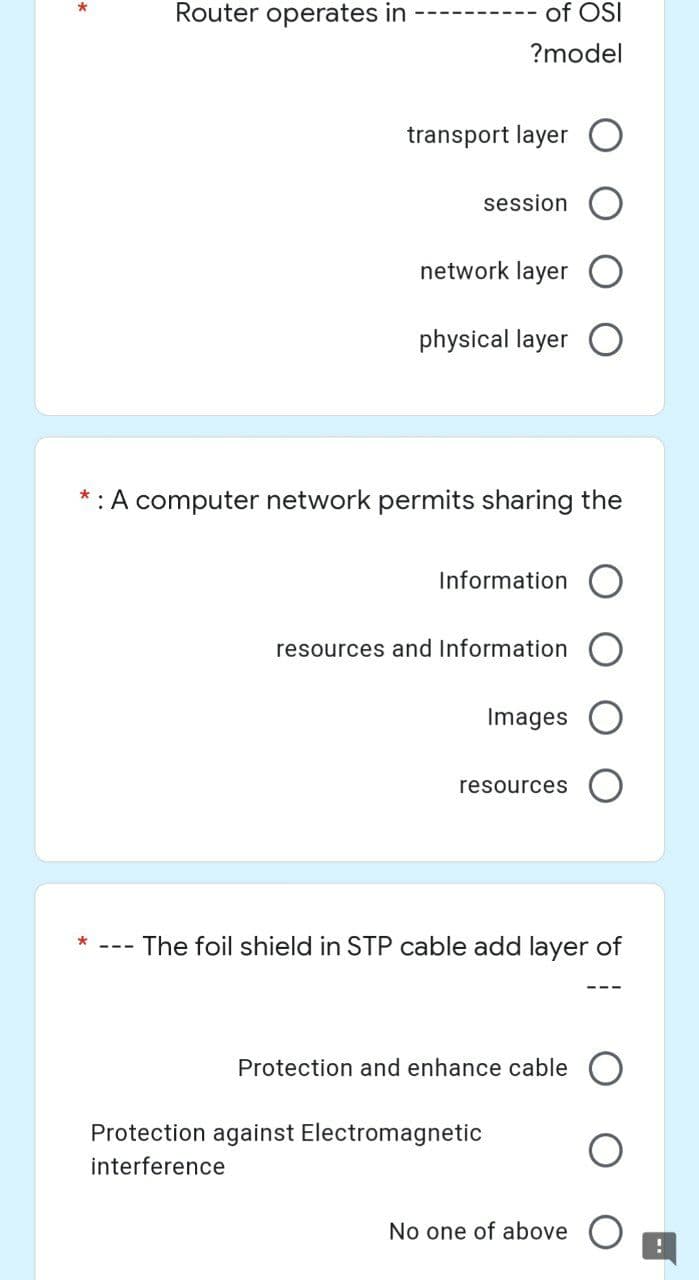
Router operates in transport layer session network layer physical layer : A computer network permits sharing the Information resources and Information Images resources The foil shield in STP cable add layer of Protection and enhance cable No one of above Protection against Electromagnetic interference of OSI ?model !
Q: In order to show the five applications for system design and modeling that are used most often,…
A: Encryption: System Design encompasses design, modelling, and simulation services that allow rapid,…
Q: You will get a deeper understanding of issues such as cloud computing, social networking, and other…
A: Introduction: Improve your understanding of not only social networking blogs, but also cloud…
Q: Consider Ubuntu in comparison to other well-known Linux distributions such as Red Hat and SUSE.…
A: As per our policy, "Since you have asked multiple questions, we will solve the first question for…
Q: Why should I maintain two copies of the identical file if I can just delete one of them
A: Introduction : Among your own data, you might be using a program that stores its data in a special…
Q: There should be a list of the five most popular network topologies given. Which one do you consider…
A: In this question we have to explain the network topologies and which one is the most reliable and…
Q: Make the distinction between RIP and EIGRP.
A: Introduction: The following is a comparison of RIP and EIGRP:
Q: Privacy is affected by two to three (2-3) technological tools. Next, explain how the tools you've…
A: Technological tools: A device, whether electrical, digital, or physical, that enhances the human…
Q: Q3/ Write a Program to compute the area of circle with design.
A: According to the information given:- We have to write a program to compute the area of a circle with…
Q: What are the two types of issues that may be modeled with the use of simulation models?
A: define impersonation as “the repetition of a real-world process or event in a place that is isolated…
Q: A positive integer is entered through the keyboard, write a function by using C language to find the…
A: Answer:
Q: An illustration-based explanation of the security safeguards you should take while outsourcing data…
A: Safeguards: Unlocked lockers. Lock unattended offices, even briefly (past incidents have shown that…
Q: Please describe Linux and some of its characteristics in your own words. Please offer specifics on…
A: Introduction: The Linux operating system, like any other operating system, has the ability to…
Q: Explain the commandment number 8 in netiquette
A: The above question is solved in step 2 :-
Q: Give a True or False answer, as well as an explanation. In the Big Data universe, Spark has…
A: Introduction: Spark is a data processing engine that is built on the Java Virtual Machine (JVM) that…
Q: After completing this course, you will have a more in-depth understanding of cloud computing, social…
A: Introduction: Improve your knowledge of not just social networking blogs, but also cloud computing…
Q: A known excellent external modem installed on a leased line exhibits no carrier detect light. Where…
A: Introduction: A telephone line or telephone circuit is referred to as a single-user circuit when it…
Q: What exactly is a simulation, and how does it contrast with its real-life counterpart? The factors…
A: Inspection: System behavior may be predicted with the use of simulation. Simulation software may be…
Q: Discuss the many ways in which information privacy might be improved, as well as the importance of…
A: Given: Privacy refers to the state of not being exposed to public scrutiny or having your secrets or…
Q: that supports 16 hosts. What subnet mask ?should you use • 255.255.255.252 . O • 255.255.255.224 . O
A: Answer to the given question: Answer(1): choice(b) is the right answer. Answer(2): choice(d) is the…
Q: How many distinct types of computer software are there from which to choose?
A: There are basically Two types of computer software present 1) System software 2) Application…
Q: Explain the importance of firewalls in protecting computer networks and the secrecy of online…
A: Intro In answer a to the question, we must explain the relevance a of network scanning and…
Q: What is a mobile database, and how does its functionality manifest?
A: In three points, explain what a mobile database is: The central data server and the mobile data…
Q: Do you have any suggestions for the topologies of network systems?
A: Network Topology A network topology is the physical and consistent plan of nodes and associations in…
Q: Q4/ Write functions to plot y = 0.1cos(x) in the interval 0≤x≤ 2л with yellow color, * symbol and…
A: syms x fplot(sin(x),[-2*pi 2*pi]) grid on title('sin(x) from -2\pi to 2\pi') xlabel('x') ylabel('y')…
Q: This is because modern computers have such an astounding capacity for processing data. What changes…
A: PCs have been persuasive since their introduction, but they are now everywhere; we can see PCs…
Q: The importance of big data technologies in law enforcement and judicial administration.
A: Introduction: IBM estimates that 2.5 quintillion bytes of data are produced every day throughout the…
Q: :How can you do a training requirements assessment for an e-learning system?
A: Intro Companies undertake need-gap analyses to determine the skills needed for competitive success,…
Q: If the lengths of the sides of a triangle are denoted by a, b, and c, then area of triangle is given…
A:
Q: A positive integer is entered through the keyboard, write a function by using C language to find the…
A:
Q: By examining their similarities and differences, unstructured data and structured data may be…
A: Given that: Compare and contrast unstructured and structured data to determine which kind of data is…
Q: Which of the following are some of the advantages of data profiling
A: Introduction: Data profiling enhances data quality, shortens the time it takes to perform large…
Q: To what extent is it necessary to maintain the privacy of one's personal information? List five…
A: Given: What does the term "information privacy" mean? Make a list of five things you can do to…
Q: xactly is meant by the phrase "Big Data"? What are the most significant benefits that Big Data has…
A: Answer to the given question: "Big data" is like little data yet bigger. "Big" in big data not…
Q: Provide an explanation using your own words as to what went wrong with the data security breach that…
A: A cyber attack is referred to as a data violation when the attacker gains unauthorized access to…
Q: How many subnets are created by the ?address 192.168.1.0255.255.255.248
A: here in the question ask for multiple choice question,
Q: How many distinct types of computer software are there from which to choose?
A: Software is a term that is used to describe a collection of instructions, data, or programs that are…
Q: The following is a condensed version of several suggestions for the creation of operating system…
A: Encryption: In contrast to the traditional kernel-based approach, the microkernel operating system…
Q: What are the four most important lessons that can be learned from the development of MINIX, and how…
A: The following are some of the things we have realized as a result of the creation of MINIX: 1. Just…
Q: alk about the social and ethical problems that might crop up when putting information technology…
A: Introduction The following are examples of social and ethical consequences that might arise from…
Q: Give instances of systems where conventional file processing could be preferable to a database…
A: Examples of systems that employ conventional file processing rather than a database strategy: Much…
Q: I need help please. This is a C++ program Design and implement a program that rolls two dice. Ask…
A: A dice is a cubical structure that has values from 1 to 6. It is thrown by a player and the number…
Q: How is computer forensics different than data recovery?
A: The above question is solved in step 2 :-
Q: When videography isn't an option, animation is employed. Can you explain why?
A: Introduction: In situations where there is no opportunity for videography, animation is typically…
Q: The benefits and drawbacks of keeping data on the cloud are well-documented. Do you aware of any…
A: Given: The phrase "web 2.0" was formerly considered to be the most fashionable buzzword in the…
Q: What exactly are sequence access files and where can I get them?
A: A sequence access file is a file that contains the next sequence of bytes from a file. By…
Q: It looks as if this section need to provide a concise explanation of the two components wwwww of the…
A: operating system: An operating system is a software programmed that manages and operates a broad…
Q: Following completion of this course, you will have a more in-depth understanding of cloud computing,…
A: Given: Improve your knowledge of not just social networking blogs, but also cloud computing and…
Q: The following returns ______ when passed the argument 3. int example(int n) { if (n == 0)…
A: The question is to write the output of the code if the argument passed is 3.
Q: OBJECTIVE To find a square and cube of a number.
A: Program
Q: Describe the operation of an authentication system that follows the format of a challenge and a…
A: Answer: Explain how an authentication challenge–response system works. It's not immediately evident…
Step by step
Solved in 2 steps

- Why is SSL stripping a particular danger with open Wi-Fi networks? WPA2 is not secure enough to prevent this Open hotspots do not assert their identity in a secure way Open hotspots can be accessed by any user 802.11ac is insecure and traffic can be redirectedQuestion 5 Compare and Contrast the following protocols 1.Telnet 2.FTP 3.ICMP (Windows and Unix (hint: they are different - find out how) 4. A protocol of your choice. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineCompare how access rights are set when using Samba, NFS and FTP. Whatproblems needs to be addressed in each of the mentioned protocols? Your answermust address both user authentication and file access rights. And must take into consideration a heterogeneous network.
- Write down the OSI layers for each device as shown. Draw a NAT Table Entry at the Router for the Computer (A) (shown with a smiley face J) trying to reach the Web Server (listening at Port 80) as shown. You may use dynamic port numbers. Divide the LAN into 2 subnets and then re-draw it to show the subnets. Assume that you have a supply of switches as needed. A frame is sent from Computer A to Router R1, assume that it is using Ethernet. Draw the frame showing the Source and Destination MAC addresses, IP addresses, and port numbers.Suppose in a wireless communication network transmitter Alice wants to send some confidential information to receiver BOB. The EVE is there to hear (confidential information) what is being communicate between Alice and BOB. In this case what types of security you will propose (From OSI layers) as a network engineer. Explain your proposed method/s and justify your answer.Maximum 400 words. Do not copy. Write it in your own way. The assignment will be checked by similarity finding registered software.Hints: Go through the Application Layer, Data Link Layer, and Physical Layer security. Then you will be able to propose possible solution/s.How does the individual come to be able to make moral decisions? e. All of the above a. By understanding his motives b. By understanding the consequences of his actions c. By being deterred and frightened of the penalties incurred on him for his action d. By understanding the means adopted to execute action Known as “packet switches,” perform much of the work in getting data transmitted over the Net to its ultimate destination. a. Routers b. Packets c. Protocols d. Addresses The fastest growing industries in cyberspace are called: a. information industries b. data industries c. information intermediaries d. data intermediaries One of the challenges facing all social media sites is: a. getting users b. monetizing their extensive web traffic c. Keeping users interested d. Providing information
- Add a DHCP server to the network with network ID of 223.12.12.0/24. Configure the DHCP server so that it provide IP addresses to all the PCs inside all the subnetworks. Describe step by step process of the DHCP configuration and add screenshot of successful DHCP calls from PC3,PC4,PC5.Q1/ Suppose you has IP address 220.254.255.x / 28, conclude the class and analyze the subnetting for finding mask address, number of subnets, addersses range of subnets , and number of hosts at each subnet. Q2/ How can perform encapsulation process of OSI model for sender, and what happen of encapsulation data at receiver side, explain and draw graph of that. Q3/ Discuss the advantages and disadvantages of shielding the copper cables .i. Describe the steps invloved in a distributed coordination function using a simple carrier sense multiple access algorithm with interframe space delay to transmit frames in a wireless LANii. Describe the four abstraction layers of TCP/IP iii. Descrive a typical scenarion invloving 2 Computer Devices transferring a video file using an unsecured ftp connection where TCP three-way handshake is susceptible to vulnerabilityiv. Describe four units that makes IEEE 802.11 Architiecture
- q23- Why is VLSM important to modern IP networks? Select one: A. Because it allows us to uniquely identify each subnet by its mask number. B. C. Because it allows each subnet in a network to be correctly sized for the requirement. C. Because every subnet must use a different mask to avoid conflicts. D. Because networks that use the same mask cannot route.2. Layer 2 security best practices include: Disable unused network device ports Disable CDP Implement port security Implement 802.1X All responses 3. Actions to minimize network attack surfaces and attack vectors could include Defense in depth practices De-militarized zones for public facing system services Control inbound and outbound network access via firewalls All available answersexplain the role and how the following arecoordinated in networking to achieve efficientand secure intranet and internet(i) NAT(il) VPN(ili) Gateway router(iv) Firewall

