ΡΥTHOΝ Determine a function T(n) that relates input size n to number of runtime steps and the Big-O Time complexity for this T(n): Example only: T{n) = an^2 +k Соmplexity 3D Om) def f1(n) : print(1) print(2) T(n) = Complexity print(n-4) print(n-3)
Q: Different kinds of malware are discussed; Describe what a botnet is and how it operates; Describe…
A: It is any program or file meant to harm a computer, network, or server known as malware. Malware is…
Q: A control's attributes, like those of other controls, decide whether or not it is shown on a form…
A: Programme Execution: The process of a computer or virtual machine reading and acting on the…
Q: Give an explanation for what the word "firewall" means in terms of network security, and describe…
A: A firewall is a type of equipment used to filter network traffic in the context of cybersecurity.…
Q: What's the use of PCB Diagram
A: Please find the answer below
Q: A persons Twitter feed can be considered what type of data: Personal record Open access Shadow data…
A: Twitter is a social media application or software and it is used to communicate and stay connected…
Q: Explain how a botnet may be built and how it can be used to launch a distributed denial of service…
A: The points below may be utilised to build a botnet: Prepare host systems to discover the…
Q: Make a list of databases that contain your data. How is each database's data stored, and how often…
A: A database concept for the common man Daily life uses of databases: In our daily lives, we are…
Q: What is data abstraction and data encapsulation, and how do they differ? How can we implement in any…
A: Instigation: Abstraction is a technique for concealing undesired information. Encapsulation, on the…
Q: What are the advantages of utilizing virtual memory?
A: Virtual memory: It is a section of the computer's secondary memory that behaves as part of the main…
Q: Show the contents of a queue after performing the following operations: ENQUEUE (10 ENQUEUE (20);…
A: here in the question they given step for following operation ENQUEUE(10) ENQUEUE(20) DEQUEUE…
Q: Programming Exercise 11 in Chapter 8 explains how to add large integers using arrays. However, in…
A: #include <iostream>#include<string>#include<conio.h> using namespace std;class…
Q: Create a C function that will input 10 numbers and will perform the following 1. Display all even…
A: I give the code in C along with output and code screenshot
Q: Create a C++ program that include the Fees to be paid The book was returned on time (Yes/No) If…
A: As per the requirement program is developed. Note: The book was returned on time (Yes/No) If yes,…
Q: What are the advantages of utilizing virtual memory?
A: Introduction of the Virtual Memory: Virtual memory is a portion of the computer's secondary memory…
Q: Where can I learn more about SSL's supported protocols? How do SSL and SSH vary one from the other?…
A: Difference between SSL and SSH are as follows: SSH is a secure tunneling protocol that allows you to…
Q: Managing a firewall is a time-consuming task, so what are the best practises? Explain
A: Time-Consuming Task: Time consuming is defined as something that cannot be completed fast and…
Q: In what ways are firewall rules beneficial?
A: The Answer is given below step.
Q: What should you keep in mind when it comes to the symbols at the start and conclusion of block…
A: Comment-blocking: Comments assist in the comprehension of a code part. These are only internal…
Q: What is the output for the following program below Sub Main () Dim i, sumodd, sumeven As Integer For…
A: The above code add the ith value repeatedly to the sumodd and sumeven variable If i value is odd,…
Q: Is there a better method to deal with DDOS attacks?
A: Reduce attack surface area: One of the first stages in preventing DDoS attacks is to decrease the…
Q: 2. Draw a recursive tree for callMyself(4). What is its return value? public static int…
A: Below I have drawn a recursive tree of the given question:
Q: What does it take to be a successful manager?
A: Given: Effective management requires decisiveness. Employees will turn to their boss for guidance on…
Q: 1. Q v ~P 2. ~Q → ~R :. ~Q> (~P ^ ~R)
A: Hello student, hope you are doing well. The solution of the given question is attached below.
Q: In what ways might a What is the function of a firewall, and how can it be put to use in your…
A: A Firewall is one type of network security device that monitors and filters incoming and outgoing…
Q: create a python program that ask the user to enter 10 number and store in a numlist and display the…
A: Please refer below code and output: I have included both sorting techniques and then given the…
Q: Java program to evaluate the given post-fix expression in O( n) time and with O(n) space complexity.…
A: We will create SolvePostFixExpr Class and in main method we will define our logic. We can use stack…
Q: We have the ability to create computers with human-level intelligence. Are there any applications…
A: Requirements for a computer to be intelligent: Artificial intelligence (AI) is a new breakthrough in…
Q: Indicate how Intel's most recent design generations have improved peripheral and communication line…
A: The more powerful and updated your processor: indicates the CPU generation After i9, i7, i5, or i3…
Q: Generate six random numbers between 1 and 40, and keep them in one array. Sum the six numbers of the…
A: Since the programming language is not mentioned, I have done the code using Python 3.
Q: In terms of firewall administration, are you aware with any best practises? Explain
A: The following are many of the most successful firewall management practices: Traffic is prohibited…
Q: What is the best storage media for users' data backups? Your solution should be justified in terms…
A: Introduction: The most common forms of media used to store data have evolved throughout time.…
Q: Q2- Write a program to read a number (n). Then print all numbers from 0 to n that are not equal to 1…
A: I give code in Matlab as well as in python along with output and code screenshot
Q: Assume you're a systems analyst working on a comprehensive test plan. Describe the testing…
A: analyzer of information systems A system analyst is someone who gathers and organizes…
Q: In C#, what is a Collection? Explain the many sorts of collections.
A: Introduction: Collections are, in fact, modifiable. Mutables are just data that will not change once…
Q: For message authentication, how may a hash value be secured? Can a MAC algorithm be attacked without…
A: a) A hash function is constructed by concatenating a message with a symmetric key and sending it;…
Q: In what ways are firewall rules beneficial?
A: Given: There are several advantages to using a firewall. 1) Network traffic monitors (also known as…
Q: What Are the Characteristics of a Computer System?
A: Computer System: A computer system is a collection of interconnected devices that process, store,…
Q: Dial-up modems, HFC, DSL and FTTH are all utilised for home connectivity. Provide a range of…
A: Introduction Dial-up modems, HFC, DSL and FTTH are all utilised for home connectivity. Provide a…
Q: What is the most significant difference between the operating systems for mainframes and laptops?…
A: Given: For security and versatility, mainframe operating systems such as z/OS are used. Obtain an…
Q: Assume you're a systems analyst working on a comprehensive test plan. Describe the testing…
A: analyzer of information systems: A system analyst is someone who gathers and organizes…
Q: In an asenkron transmission a character size is 5 bits. In this transmission, if total overhead…
A:
Q: Describe one of Alan Turing's contributions to computer science.
A:
Q: Create a nibbles game using python.
A: import random import pygame BOARD_SIZE_WIDTH = 25 BOARD_SIZE_HEIGHT = 25 # This will determine the…
Q: What is the physical address of this instruction Source operand of MOV BL, [SI +
A: The answer is
Q: Explain the features of system architecture that you as a systems analyst must consider while…
A: System development is a systematic process that includes stages such as planning, analysis, design,…
Q: The difference between an interpreter and a compiler should be discussed.
A: Interpreter translates just one statement of the program at a time into machine code.
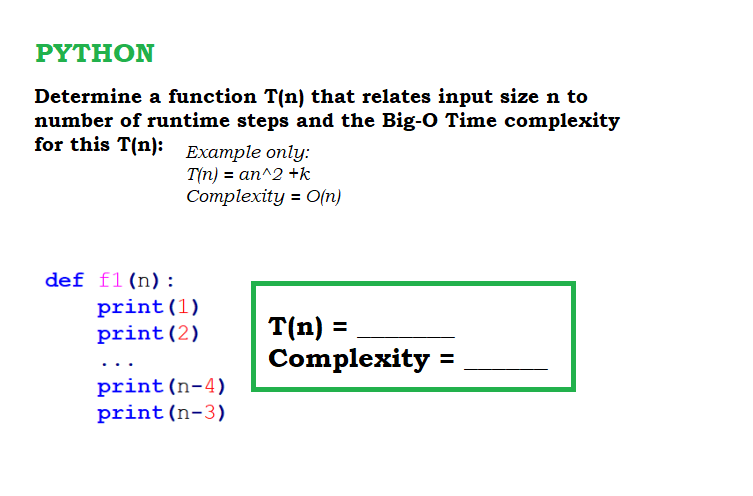
Q: ΡYTHOΝ Determine a function T(n) that relates input size n to number of runtime steps and the Big-O…
A: The time complexity of the program mainly depends on the number of loops and how many times each…
Q: When writing an abstract for a new operating system, what considerations should you keep in mind?
A: Answer the above question are as follows:
Q: In a new application program, how would you determine whether to use a classic SQL-based API like…
A: ORM Framework: ORM is yet another nerd-acronym, it is short for Object Relational Mapping. In a…
Q: The command x followed by p, given in vim, places the cursor on the first letter of the word.…
A: Command: A command is defined as an order or the power to command. A dog owner instructing their dog…
func1
will give thumbs up
Step by step
Solved in 2 steps

- Assume that each of the expressions below gives the processing time T(n) spent by an algorithm for solving a problem of size n. Select the dominant term(s) having the steepest increase in n and specify the lowest Big-Oh complexity of each algorithm. For example, the dominant term in 0.1n + 10n4 is 10n4 and it is O(n4). Expression Dominant term(s) O(. . .) 5 + 0.001n3 + 0.025n 500n + 100n1.5 + 50n log10 n 0.3n + 5n1.5 + 2.5 · n1.75 n2 log2 n + n(log2 n)2 n log3 n + n log2 n 100n + 0.01n2 0.01n + 100n2 2n + n0.5 + 0.5n1.25 0.01n log2 n + n(log2 n)2 100n log3 n + n3 + 100nBig-O notation. Suppose n is the input size, we have the following commonly seen functions in complexity analysis: f1(n) = 1, f2(n) = log n, f3(n) = n, f4(n) = n log n, f5(n) = n2, f6(n) = 2n, f7(n) = n!, f8(n) = nn. Intuitively, the growth rate of the functions satisfy 1 < log n < n < n log n < n2 < 2n < n! < nn. Prove this is true. Let f, g : N → R+, prove that Ω(f(n) + g(n)) = Ω(max{f(n), g(n)}). [Note: Proving this will help you understand that we can also leave out the insignificant parts in big-Ω notation and the result is still a lower bound, e.g., Ω(n2 + n log n + n) = Ω(n2).]Suppose that your implementation of a particular algorithm appears in C++ as for (int pass = 1; pass <= n; pass++) { for (int index = 0; index < n; index++) { for (int count = 1; count < 10; count++) { ... } // end for } // end for } // end for The previous code shows only the repetition in the algorithm, not the computations that occur within the loops. These computations, however, are independent of n. What is the Big O of the algorithm?
- Assume that you were given N cents (N is an integer) and you were asked to break up the N cents into coins consisting of 1 cent, 2 cents and 5 cents. Write a dynamicprogramming based recursive algorithm, which returns the smallest (optimal) number of coins needed to solve this problem. For example, if your algorithm is called A, and N = 13, then A(N) = A(13) returns 4, since 5+5+2+1 = 13 used the smallest (optimal) number of coins. In contrast, 5+5+1+1+1 is not an optimal answer.Let A(n) = 3A(n/2) + n2 + 3n + 4.Using the MasterTheorem, the computational complexity is _______. A.O(n2log n) B.O(n1.58) where 1.58 = log23 C.O(n2) D.O(n0.63) where 0,63 = log32The given time complexity is: m T(m-1) + ca > 1 cb = 0 expanding using substitution: m T(m-1) + ca m[(m-1) T(m-2) + ca]+ ca m(m-1) T(m-2) + mca + ca m(m-1) [(m-2) T(m-3) + ca] + mca + ca m(m-1)(m-2) T(m-3) + m(m-1)ca + mca + ca what is the time complexity? form an expression for adding all the ca
- #4. Euler's totient function, also known as phi-function ϕ(n),counts the number of integers between 1 and n inclusive,which are coprime to n.(Two numbers are coprime if their greatest common divisor (GCD) equals 1)."""def euler_totient(n): """Euler's totient function or Phi function. Time Complexity: O(sqrt(n)).""" result = n for i in range(2, int(n ** 0.5) + 1): if n % i == 0: while n % i == 0: n //= i.a) Consider a recursive function to return the Number of Binary Digits in the Binary Representation of a Positive Decimal Integer (n) using a recursive algorithm. int Process (int n) { if (n == 1) return 1; else return (Extra() + Process (n/4) + Process (n/4)); } Given that Extra(n) is a function of O(n)1) Find T(n) = number of arithmetic operations. 2) Calculate the complexity of this algorithm using Back Substitution.Information is present in the screenshot and below. Based on that need help in solving the code for this problem in python. The time complexity has to be as less as possible (nlogn or n at best, no n^2). Apply divide-and-conquer algorithm in the problem. Make sure all test cases return expected outputs. Hint: Apply bisection method/modules Output FormatOutput contains a line with two space-separated integers W_a and W_b.- W_a is the maximum matchups won by Hamiltonia- W_b is the maximum matchups won by Burrgadia. Sample Input 03 554402410 Sample Output 03 0 Sample Input 15 4833485183 Sample Output 12 2 Sample Input 27 81028121912601319851 Sample Output 27 0 The actual code """Solves a test case Parameters:a : int - number of leaders in Hamiltoniab : int - number of leaders in Burrgadias_i : array-like - rap proficiencies of Hamiltonia's leadersr_j : array-like - rap proficiencies of Burrgadia's leaders Returns:win_a : int - number of…
- Please written by computer source Let x be a binary string. The minimal description of x, written d(x), is the shortest string ⟨M, w⟩ where TM M on input w halts with x on its tape. If several such strings exist, select the lexicographically first among them. The descriptive complexity, or Kolmogorov complexity, of x, written K(x), is K(x) = |d(x)|. Show that the function K(x) is not a computable function. HINTS: If K is a computable function, there is some TM which computes it. That TM can be used to find strings of large complexity. Try to design a program which outputs “complex” strings but which contradicts their supposed complexity, and even contradicting the supposed complexity of a single string suffices.Big-O notation. (a) Suppose n is the input size, we have the following commonly seen functions in complexity analysis: f1(n) = 1, f2(n) = log n, f3(n) = n, f4(n) = n log n, f5(n) = n2, f6(n) = 2n, f7(n) = n!, f8(n) = nn. Intuitively, the growth rate of the functions satisfy 1 < log n < n < n log n < n2 < 2n < n! < nn. Prove this is true. [Hint: You are expected to prove the following asymptotics by using the definition of big-O notation: 1 = O(log n), log n = O(n), n = O(n log n), n log n = O(n2), n2 = O(2n), 2n = O(n!), n! = O(nn). (b) Let f, g : N → R+, prove that O(f(n) + g(n)) = O(max{f(n), g(n)}). [Hint: The key is max{f(n), g(n)} ≤ f(n) + g(n) ≤ 2 · max{f(n), g(n)}. Note: Proving this will help you to understand why we can leave out the insignificant parts in big-O notation and only keep the dominate part, e.g., O(n2+n log n+n) = O(n2).] (c) Let f, g : N → R+, prove that Ω(f(n) + g(n)) = Ω(max{f(n), g(n)}). [Note: Proving this will help you understand…Modeling the spread of a virus like COVID-19 using recursion. Let N = total population (assumed constant, disregarding deaths, births, immigration, and emigration). S n = number who are susceptible to the disease at time n (n is in weeks). I n = number who are infected (and contagious) at time n. R n = number who are recovered (and not contagiuous) at time n. The total population is divided between these three groups: N = S n + I n + R n There are several hidden assumptions here that may or may not apply to COVID-19, such as a recovered person is assumed to not be able to get the disease a second time, at least within the time window being examined. On week 0 (the start), you assume a certain small number of people have the infection (just to get things going). Everyone else is initially susceptible, and no one is recovered. There are two constants of interest: Let period = time period that it takes for an infected person to recover (recover meaning they become not infectious to…

