ΡΥTHΟΝ Determine a function T(n) that relates input size n to number of runtime steps and the Big-O Time complexity for this T(n): Example only: T(n) = an^2 +k Соmplexity %3D O(m) def f4(n, list_of_length_n): print (list_of_length_n) T(n) = Complexity =
Q: What are the program's similarities and differences?
A: The term "computer programme" refers to a compilation of instructions. To accomplish a certain job,…
Q: The SPI Firewall in conjunction with the FTP Protocol is a concept.
A: Firewall: It is a piece of software used to prevent unauthorized access and access to unauthorized…
Q: By using Exception(throw, try, catch), validate a grade. ask the user to enter a grade and then if…
A: Introduction By using Exception(throw, try, catch), validate a grade. ask the user to enter a grade…
Q: What additional kinds of firewalls exist besides those that are network-based?
A: Given: Firewalls are used to monitor network traffic and assist prevent unauthorized traffic from…
Q: b. With the aid of an example, describe the dimensional table
A: A dimensional table contains the all details about the fact. For example, a time dimensional table…
Q: 1. Describe an iterative algorithm that takes as input a list of n distinct integers and counts how…
A: As per our policy I have given answer to only first question.
Q: Ist necessary to keep net neutrality? Justify your response.?
A: Net Neutrality : It is a term that refers to the practice of internet service providers treating…
Q: In C#, what is a Collection? Explain the many sorts of collections.
A: Introduction: Collections are, in fact, modifiable. Mutables are just data that will not change once…
Q: How can one person lead a distributed denial of service attack?
A: DDoS is accomplished is through a network of remotely : A distributed denial service (DDoS) assault…
Q: relationship among SDLC and HCI
A: Software Development Life Cycle Software Development Life Cycle(SDLC) is a process of developing a…
Q: Question 4 Chapter 1: Review of packet-switching and circuit-switching networks Question 4: Consider…
A:
Q: What is the most important step the programmer must perform inside an Interrupt Service Routine --…
A: The Answer is given below step.
Q: What is the underlying cause of diskthrashing? What steps can you take to mitigate effects?
A: Please refer below for your reference: Disk thrashing occurs due to the system does not having…
Q: what are the names of all the components in the system?
A: A cutting edge system is both basic and complicated. It is basic as in throughout the long term,…
Q: Based on Big Data in Healthcare - Personal Healthcare: 1. Provide the opportunities in Personal…
A: Healthcare is the maintenance of health via diagnosis, treatment, prevention and physical therapy…
Q: C programming create a text base game to race 4 cars across the screen and determine the first…
A: Description: Create random number generator for the number of movesCreate random number generator…
Q: What distinguishes von Neumann's architecture from its predecessors?
A: The von Neumann model also makes it reasonably easy for hardware designers to build CPUs, memories…
Q: Suppose, you need to service 48 hardware interrupts on your 8086 microprocessor. Explain how many…
A:
Q: i. Write one CSS statement to change the color of all the text in paragraphs to \blue". ii. Tim has…
A: i. Write one CSS statement to change the color of all the text in paragraphsto \blue". ii. Tim has…
Q: What are the benefits of using a firewall and how do you go about installing one?
A: Pros of firewall | Advantages of firewall: A firewall is security device that may assist safeguard…
Q: What role does a honeypot play in a network protected by an intrusion detection system and a…
A: A honeypot is a cybersecurity mechanism that uses a manufactured attack target to lure…
Q: Consider the below integer array which is already sorted { 1, 2, 3, 4, 4, 6, 6, 6 } program in Java…
A: import java.util.*;class GFG { // function to find repeating elements static void…
Q: step by step explaination to write a c program using loops and decision statement?
A: Using while loop and if statement , I have provided a C CODE along with CODE SCREENSHOT…
Q: Examine the connection between computer and network security and the many types of malware. Is there…
A: Connection Between Computer: A computer must have a network interface card (NIC) installed in order…
Q: Fill in blank In xv6, function ----------- can be invoked in order to obtain a pointer to the PCB…
A: A computer program makes system call when it makes request to operating system kernel. System calls…
Q: In C#, how do you make a Windows service?
A: Given: Windows Services are background-running non-graphical package programmes. Windows services…
Q: Regular expression of language part 1: EVEN-EVEN part 2: ODD-EVEN part 3: EVEN-ODD part…
A: The regular expression that accepts the language Even-Even over the Σ={a, b} i.e the number of a's…
Q: 2.12. For each of the following languages, draw an FA accepting it. d. (bbb, baa}* (a) e. (a}U…
A: Given: For the following language draw an Finite automata accepting it . As per the Company…
Q: Briefly explain why software engineering approaches and techniques for software systems are…
A: answer is
Q: create a python program that ask the user to enter 10 number and store in a numlist and display the…
A: Please refer below code and output: I have included both sorting techniques and then given the…
Q: What would be the BER encoding of {weight, 190} {lastname, “Sloanel”}?
A: Given: {weight, 190} {lastname, "Sloanel"} The above given sets are BER encoded as: a) {weight, 190}…
Q: The command x followed by p, given in vim, places the cursor on the first letter of the word.…
A: Command: A command is defined as an order or the power to command. A dog owner instructing their dog…
Q: ways to protect yourself against phishing
A: The Answer is given below step.
Q: One individual may launch a distributed denial of service assault, but how does it work?
A: Service Assault: Services such as flooding or crashing are available. Flood assaults occur when a…
Q: Test data, an integrated test facility, and parallel simulation are compared and contrasted.…
A: Start: It is a version of the test data approach to have an integrated test facility. The most…
Q: Calculate the perceptron network if there are 3 inputs x,-1.7, x,-5.9, x,-3 and b- -1.8.
A: The answer is
Q: 4. We wish to create 16 subnets in a /23 network. Assume that we wish to use the minimum number of…
A: We are given a /23 network where we will have 16 subnets. We are going to find out how many hosts…
Q: cyber security Aims of the project
A: Cyber security awareness is very important. The aims of Cyber security awareness are as follows:…
Q: Create a function that will perform the following: 1. A sample program for basic input and output…
A: C is an imperative procedural language supporting structured programming, lexical variable scope and…
Q: Is there a form of operating system that I can't access because I don't have any money to do so?
A: SYSTEM D'EXECUTION: An Operating System is a piece of software that serves as a link between the…
Q: What exactly is an operating system (OS)? Why do operating systems, software and hardware interact…
A: The Answer is in step2
Q: In terms of firewall administration, what are the best practises? Explain.
A: Firewall Administration: Description of Firewall Administration The correct management,…
Q: 1) largest Write a function int largest(int a[],int n) that will find the largest int in the n ints…
A: Solution: C code: #include<stdio.h> int largest(int a[], int n){ intlargest = a[0];…
Q: What does the term "operating system" refer to? What are the two primary roles of the operating…
A: Operating System: The operating system is the most critical application that runs on a computer. It…
Q: Assume Alice and Bob are exchanging packets through a computer network. Suppose Trudy inserts…
A: Network: A network is made up of two or more computers that are connected together to share…
Q: The program will display the largest number between 2 to 4 numbers using java language getLarge() –…
A: getLarge() – accepts 2 to 4 numbers as parameters and returns the value of X which is the largest…
Q: SFJ Process Suppose we have a four (4) core processor and all processes are designed to be…
A: SJF scheduling algorithm , is type of CPU scheduling algorithm in which process having the smallest…
Q: 4. A function operating on positive integers is described by: { 1,ifn = 1 f(n) = f(n – 1) + 2, ifn >…
A: ALGORITHM:- 1. Take input for the value of n from the user. 2. Define a function that is…
Q: Make a list of the databases that have information about you. What method is used to acquire data in…
A: Database : A list of databases available in your nation may be found online. Each database collects…
Q: What are the different kinds of firewalls and how are they used?
A: Solution for the computers or devices that are connected Firewalls that filter packetsGateways at…
func4
will give thumbs up if correct
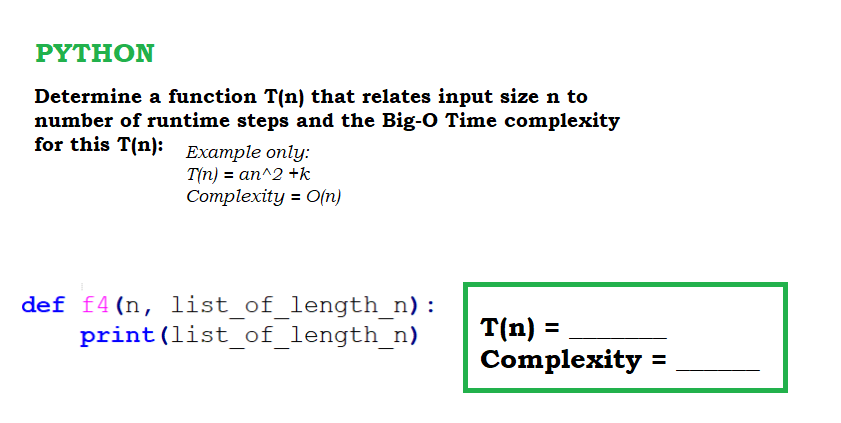
Step by step
Solved in 2 steps

- Suppose that your implementation of a particular algorithm appears in C++ as for (int pass = 1; pass <= n; pass++) { for (int index = 0; index < n; index++) { for (int count = 1; count < 10; count++) { ... } // end for } // end for } // end for The previous code shows only the repetition in the algorithm, not the computations that occur within the loops. These computations, however, are independent of n. What is the Big O of the algorithm?6.Coding-----""Euler's totient function, also known as phi-function ϕ(n),counts the number of integers between 1 and n inclusive,which are coprime to n.(Two numbers are coprime if their greatest common divisor (GCD) equals 1)."""def euler_totient(n): """Euler's totient function or Phi function. Time Complexity: O(sqrt(n)).""" result = n for i in range(2, int(n ** 0.5) + 1): if n % i == 0: while n % i == 0: n //= i.#4. Euler's totient function, also known as phi-function ϕ(n),counts the number of integers between 1 and n inclusive,which are coprime to n.(Two numbers are coprime if their greatest common divisor (GCD) equals 1)."""def euler_totient(n): """Euler's totient function or Phi function. Time Complexity: O(sqrt(n)).""" result = n for i in range(2, int(n ** 0.5) + 1): if n % i == 0: while n % i == 0: n //= i.
- A sequential search of a sorted list can halt when the target is less than a givenelement in the list. Define a modified version of this algorithm and state thecomputational complexity, using big-O notation, of its best-, worst-, and average-case performances. Using this template in python: def sequential_search(input_list, target):target_index = -1#TODO: Your work here# Return target_index. If not found, -1return target_indexif __name__ == "__main__":my_list = [1, 2, 3, 4, 5]print(sequential_search(my_list, 3)) # Correct Output: 2print(sequential_search(my_list, 0)) # Correct Output: -1Given below is the implementation of the bellman ford and dijkstras algorithm. Please complete the code for the time_shortest_path_algs() function according to the instructions in the 1st screenshot provided. Done in python 3.10 or later please def bellman_ford(self,s) : """Bellman Ford Algorithm for single source shortest path. Keyword Arguments: s - The source vertex. """ distances = {v: float('inf') for v in self.adjacency_list} distances[s] = 0 parents = {v: None for v in self.adjacency_list} for _ in range(len(self.adjacency_list) - 1): for from_vertex in self.adjacency_list: for to_vertex in self.adjacency_list[from_vertex]: if distances[from_vertex] + self.weights[(from_vertex, to_vertex)] < distances[to_vertex]: distances[to_vertex] = distances[from_vertex] + self.weights[(from_vertex, to_vertex)] parents[to_vertex] =…Computer Science Write the PSEUDOCODE for an algorithm that takes as input a list of numbers that are sorted in nondecreasing order, and finds the location(s) of the most frequently occurring element(s) in the list. If there are more than one element that is the most frequently occurring, then return the locations of all of them. Analyze the worst-case time complexity of this algorithm and give the O() estimate. (A list is in nondecreasing order if each number in the list is greater than or equal to the number preceding it.)
- Given an unsorted array A of integers of any size, n ≥ 3, and an integer value x, write an algorithm as a pseudo code (not a program!) that would find out if there exist EXACTLY3 occurrences in the array with value x. What is the time complexity of your algorithm, in terms of Big-O? What is the space complexity of your algorithm, in terms of Big-O? What if , the given array A is sorted. Will time complexity change from the case that A was unsorted? • If yes; give a new algorithm that achieves this better complexity (indicate the time complexity as of that algorithm). • If no, explain why such new constraints/conditions cannot lead to a better time complexity.Using Java, give an algorithm for the following problem: given a list of n distinct positive integers, partition the list into two sublists, each of size n/2, such that the difference between the sums of the integers in the sublists is minimized. Determine the time complexityof the algorithm.you may assume that h is a multiple of 2a) Consider a recursive function to return the Number of Binary Digits in the Binary Representation of a Positive Decimal Integer (n) using a recursive algorithm. int Process (int n) { if (n == 1) return 1; else return (Extra() + Process (n/4) + Process (n/4)); } Given that Extra(n) is a function of O(n)1) Find T(n) = number of arithmetic operations. 2) Calculate the complexity of this algorithm using Back Substitution.
- Please written by computer source Let x be a binary string. The minimal description of x, written d(x), is the shortest string ⟨M, w⟩ where TM M on input w halts with x on its tape. If several such strings exist, select the lexicographically first among them. The descriptive complexity, or Kolmogorov complexity, of x, written K(x), is K(x) = |d(x)|. Show that the function K(x) is not a computable function. HINTS: If K is a computable function, there is some TM which computes it. That TM can be used to find strings of large complexity. Try to design a program which outputs “complex” strings but which contradicts their supposed complexity, and even contradicting the supposed complexity of a single string suffices.Assume that each of the expressions below gives the processing time T(n) spent by an algorithm for solving a problem of size n. Select the dominant term(s) having the steepest increase in n and specify the lowest Big-Oh complexity of each algorithm. For example, the dominant term in 0.1n + 10n4 is 10n4 and it is O(n4). Expression Dominant term(s) O(. . .) 5 + 0.001n3 + 0.025n 500n + 100n1.5 + 50n log10 n 0.3n + 5n1.5 + 2.5 · n1.75 n2 log2 n + n(log2 n)2 n log3 n + n log2 n 100n + 0.01n2 0.01n + 100n2 2n + n0.5 + 0.5n1.25 0.01n log2 n + n(log2 n)2 100n log3 n + n3 + 100nBig-O notation. Suppose n is the input size, we have the following commonly seen functions in complexity analysis: f1(n) = 1, f2(n) = log n, f3(n) = n, f4(n) = n log n, f5(n) = n2, f6(n) = 2n, f7(n) = n!, f8(n) = nn. Intuitively, the growth rate of the functions satisfy 1 < log n < n < n log n < n2 < 2n < n! < nn. Prove this is true. Let f, g : N → R+, prove that Ω(f(n) + g(n)) = Ω(max{f(n), g(n)}). [Note: Proving this will help you understand that we can also leave out the insignificant parts in big-Ω notation and the result is still a lower bound, e.g., Ω(n2 + n log n + n) = Ω(n2).]

