s this database schema look right? From what these steps
Chapter2: Database Design Fundamentals
Section: Chapter Questions
Problem 11RQ
Related questions
Question
Does this
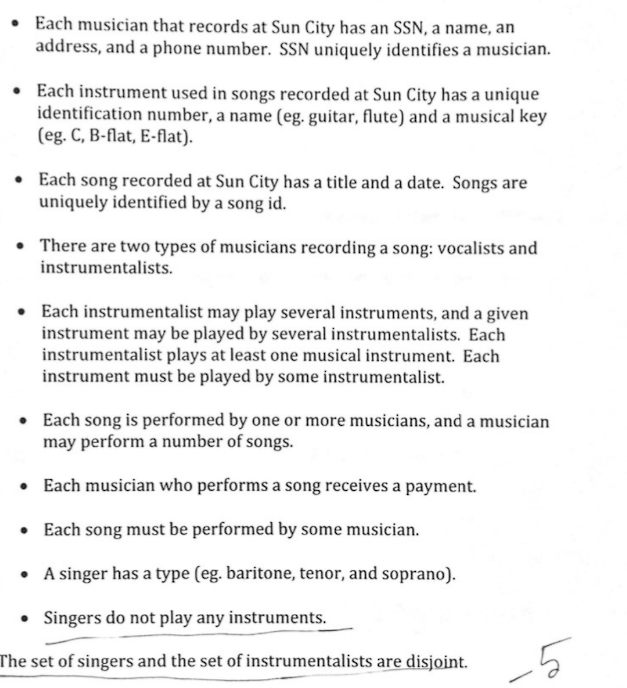
Transcribed Image Text:• Each musician that records at Sun City has an SSN, a name, an
address, and a phone number. SSN uniquely identifies a musician.
• Each instrument used in songs recorded at Sun City has a unique
identification number, a name (eg. guitar, flute) and a musical key
(eg. C, B-flat, E-flat).
• Each song recorded at Sun City has a title and a date. Songs are
uniquely identified by a song id.
. There are two types of musicians recording a song: vocalists and
instrumentalists.
• Each instrumentalist may play several instruments, and a given
instrument may be played by several instrumentalists. Each
instrumentalist plays at least one musical instrument. Each
instrument must be played by some instrumentalist.
• Each song is performed by one or more musicians, and a musician
may perform a number of songs.
• Each musician who performs a song receives a payment.
• Each song must be performed by some musician.
• A singer has a type (eg. baritone, tenor, and soprano).
• Singers do not play any instruments.
The set of singers and the set of instrumentalists are disjoint.
Lo
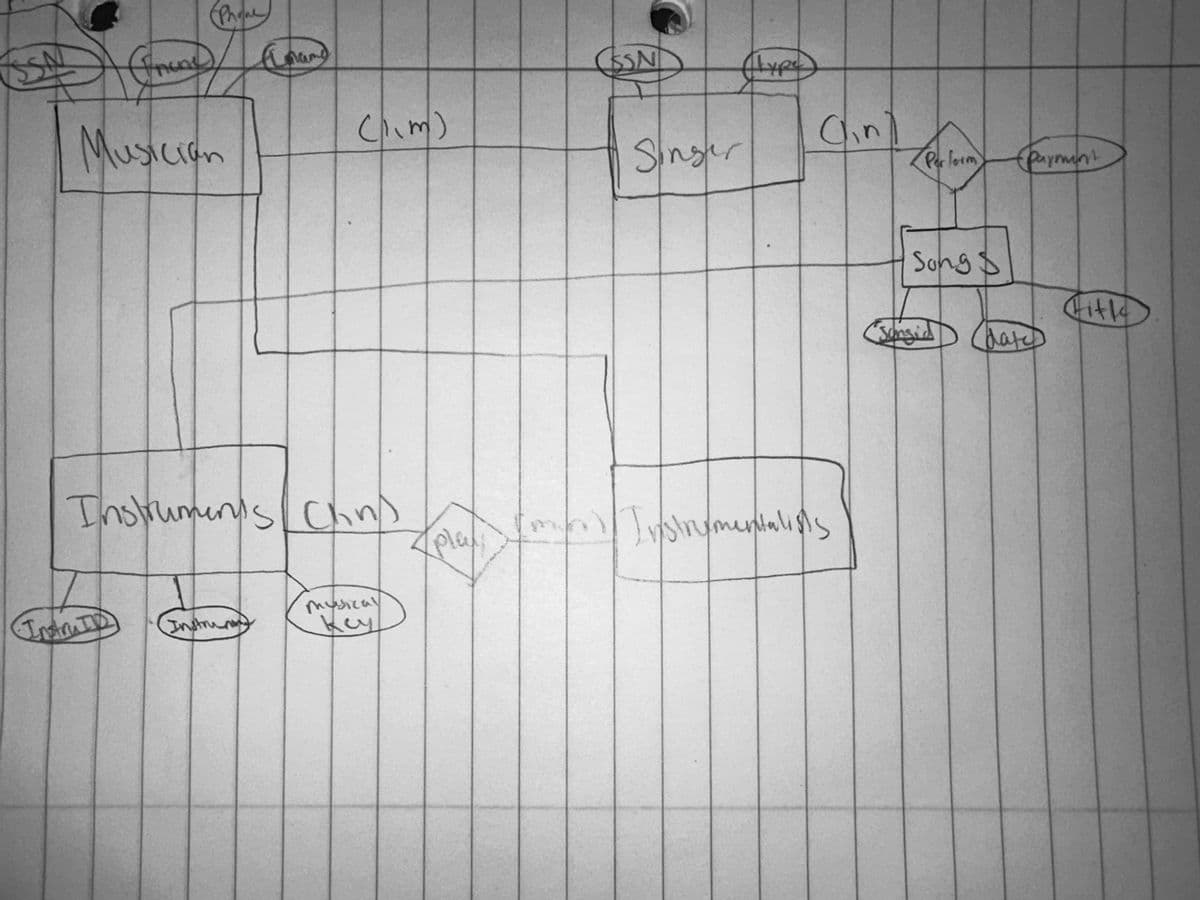
Transcribed Image Text:(Phone
A trace (Loan)
(
Musician
(11m)
Instrumen's Chns
musical
key
ка
4 Play:
CSSN
Singer
Emil
type
Cin)
Instrumentalists
Perform
Song
Sonsid
(parmint
date
Gitk
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage
