Sam has been through his scoring card in previous World Cup games. He has played a total of N games and scored A1, A2, A3, ..., AN point in matches. During the selection process, Dhoni wants to know Rohit Sharma's points rating. Thus, Rohit Sharma calculates his rating as follows: You select the match (except for the last match) and change the points of the Ai and Ai + 1 games by one point of Ai-Ai + 1 reduces the number of games on the score card by 1. You continue the process above on the newly created points card until the score card size is 1. Help Rohit grow his middle school.
Sam has been through his scoring card in previous World Cup games. He has played a total of N games and scored A1, A2, A3, ..., AN point in matches. During the selection process, Dhoni wants to know Rohit Sharma's points rating. Thus, Rohit Sharma calculates his rating as follows: You select the match (except for the last match) and change the points of the Ai and Ai + 1 games by one point of Ai-Ai + 1 reduces the number of games on the score card by 1. You continue the process above on the newly created points card until the score card size is 1. Help Rohit grow his middle school.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter7: Arrays
Section: Chapter Questions
Problem 9PP: (Data processing) Your professor has asked you to write a C++ program that determines grades at the...
Related questions
Question
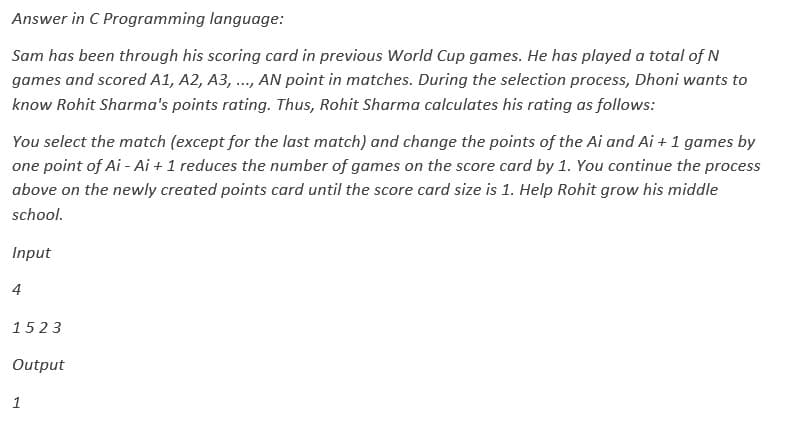
Transcribed Image Text:Answer in C Programming language:
Sam has been through his scoring card in previous World Cup games. He has played a total of N
games and scored A1, A2, A3, ..., AN point in matches. During the selection process, Dhoni wants to
know Rohit Sharma's points rating. Thus, Rohit Sharma calculates his rating as follows:
You select the match (except for the last match) and change the points of the Ai and Ai + 1 games by
one point of Ai-Ai + 1 reduces the number of games on the score card by 1. You continue the process
above on the newly created points card until the score card size is 1. Help Rohit grow his middle
school.
Input
4
1523
Output
1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning