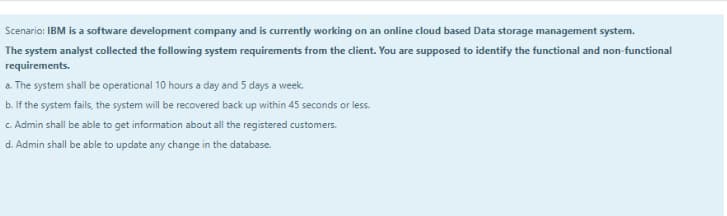
Scenario: IBM is a software development company and is currently working on an online cloud based Data storage management system. The system analyst collected the following system requirements from the client. You are supposed to identify the functional and non-functional requirements. a. The system shall be operational 10 hours a day and 5 days a week. b. If the system fails, the system will be recovered back up within 45 seconds or less. c. Admin shall be able to get information about all the registered customers. d. Admin shall be able to update any change in the database.
Q: The following describes the expenditure cycle for a hypothetical company. The company has a…
A: EC termed as Expenditure cycle which involves the business activities set that is recurring in…
Q: what is the potential consequences and give each of the question a prevention technique. 1)A…
A: Operating System Risks: The risk that compromises the integrity and confidentiality of the system…
Q: Emery Communications Company is considering the production and marketing of a communications system…
A: Net Present Value (NPV): Net present value is defined as the summation of the present value of cash…
Q: for future designs w
A: Given: To explain the best course of action and development process as,
Q: d. Robert discovered a new sensitivity analysis publicdomain program on the Internet. He downloaded…
A: Operating system risk: It is the risk where integrity and confidentiality of the system will be lost…
Q: In March 2021, Price Company began developing a new software system to be used internally for…
A: Introduction To capitalize a cost, company must derive economic benefit from that particular assets.…
Q: Arkitektyukid hired a consulting firm three (3) months ago to redesign the information system used…
A: Accounting:- Accounting is the system which records and processes the financial information of a…
Q: 1. When negotiating new contracts with the vendor, what should the IS auditor recommend to…
A: 1) Business continuity coming up with (BCP) is that the method concerned in making a system of bar…
Q: PKPP Consultants is currently in the process of completing the systems implementation activities for…
A:
Q: Fisher-Gardner Corporation (FGC) began operations 5 years ago as a small firm serving customers in…
A: Given information: Average payments per day $2,100,000 Collection period before lockbox system is 5…
Q: LOCKBOX SYSTEM Fisher-Gardner Corporation (FGC) began operations 5 years ago as a small firm…
A: Free cash flow refers to the amount generated by the company after taking cash outflows in order to…
Q: Listed here are four scenarios. For each scenario, discuss the potential consequences and give a…
A:
Q: The following describes the expenditure cycle for a hypothetical company.The company has a…
A: Transaction process system: Transaction process system can be defined as a system designed to…
Q: Suppose XYZ Software Company faces the threats given in the following table. Using the table,…
A: Cost benefit analysis compares the costs with the benefits received. Cost benefit analysis is one of…
Q: How difficult is it to expand the original RedBrandmodel? Answer this by adding a new plant, two…
A: Warehouses refer to the place of accommodation when a company usually stores its goods or products…
Q: Warehouse operations have shut down at SHXCX Manufacturing suddenly due to a power outage. Warehouse…
A: Business Continuity Planning (BCP) introduces the capability of the businesses to overcome a…
Q: Until a year ago, Dagwood Printing Company had always operated in a centralized computer…
A: Internal Control: Internal control can be defined as the procedures, rules, and mechanisms that…
Q: Robin Alper, a manager of the credit collections department for ACME Building Supplies, is extremely…
A: Definition: System design: System design is defined as the method of explaining elements of a…
Q: A CIA’s client, The Outsider, Inc., is a medium-sized manufacturer of products for the leisure time…
A: The question is based on the concept of Auditing
Q: me time. b. Enables the tracking of all transactions. Enterprise resource planning systems…
A: Solution: a. Allows multiple users to access the system at the same time - Network - Compatible b.…
Q: A new systems development project is being planned for Reindeer Christmas Supplies Company. The…
A: Memo: A Memo is a formal as well as internal business communication means. The purpose of a Memo is…
Q: Please read the following short scenario and answer the two questions given at the end Juniper is…
A: Organizational Buying Process: It refers back to the system via which commercial shoppers make a buy…
Q: Required: Prepare a memo that you will send to Anna Marie, the head of the information systems…
A: Prototyping needed for the workers of an accounting department Memorandum To: Anna Marie, head,…
Q: 1. A new systems development project is being planned for Reindeer Christmas Supplies Company. The…
A: System development is the process of defining, designing and testing the new software and…
Q: Jade Ltd is now considering how to obtain a computer software. The director of Jade Ltd has noticed…
A: Here intangible asset is recognized for internally generating asset
Q: Kruger Designs hired a consulting firm 3 months ago to redesign the information system that the…
A:
Q: Garnett Jackson, the founder, and CEO of Tech Tune-Ups, stared out the window as he finished his…
A: A financial plan is where the firm forecasts for the near future regarding, it's cash flows and…
Q: Downtown! is a rapidly growing web-based retailer with about 100 management and technical support…
A: Answer: Person X views that, they will design the latest to create their own reports. This would…
Q: Which of these is NOT an advantage of using cloud computing? The entity has control over when to…
A: Solution: Following are the advantages of cloud computing: 1. Access to the service/s is based on a…
Q: Which of the following is a situation that might call for an indirect strategy? Check all that…
A: strategy is considered to be important part of an organisations which help the organisation to…
Q: please help, project management, you guys solve only 3 parts and ask me to re submit the remaining…
A: Return on investment (ROI) seems to be a performing metric used to assess an investment's…
Q: a) The CIO and MD have different views on how the system analysis should be performed. Comment on…
A: Requirement a: Evaluate that worker with whom an individual can sympathize in the provided…
Q: Warf Computers, Inc., was founded 15 years ago by Nick Warf, a computer programmer. The small…
A: Financial cash flow is given as follows:- Cash Flow from Assets = Cash Flow to Creditors + Cash Flow…
Q: Input Controls and Data Processing
A: Given information is: You have been hired by a catalog company to computerize its sales order entry…
Q: CyberBest started to develop an anti-malware application on August 1, 20X1. It reached technological…
A: There are international standards for recognition of research and development expenses as expenses…
Q: A new system's development project is being planned for Reindeer Christmas Supplies Company. The…
A: Accounting information system : An accounting information system can be defined as the development…
Q: CME Corporation is a software development company that develops software for their clients. Their…
A: I think a suitable alternative sales model of my software is that company can go for the quarterly…
Q: Imagine there are two companies, East Wafer and West Wafer, which produce silicon wafers, the base…
A: A cartel is a group that independent companies form in order to fix prices or limit the amount of…
Q: Calculate the Risk Exposure rating with the help of information provided in the scenario
A: Information provided: Risk Impact = 12 Weeks Probability = 25% Risk Impact: When the risk truly…
Q: A recent IBM research of 585 mobile application developers and managers revealed that just one-third…
A: Now a days there is an excessive rise in the mobile app development sector. Everyone is coming up…
Q: Kruger Designs hired a consulting firm 3 months ago to redesign the information system used by the…
A: Accounting Information System: The system which helps to gather, store and process the accounting…
Q: Prepare a memo from Ringle to the head of the information systems department, Sandy Klaus. In this…
A: Introduction A Memo is a formal as well as internal business communication means. The purpose of a…
Step by step
Solved in 2 steps

- Until a year ago, Dagwood Printing Company had always operated in a centralized computer environment. Now, 75 percent of the office employees have a PC. Users have been able to choose their own software packages, and no documentation of end-user-developed applications has been required. Next month, each PC will be linked into a local area network and to the company’s mainframe. Required a. Outline a plan of action for Dagwood Printing Company to ensure that the proper controls over hardware, software, data, people, procedures, and documentation are in place. b. Discuss any exposures the company may face if the devised plan is not implemented.You are an audit supervisor assigned to a new client which is listed on a Stock Exchange. You visited the corporate headquarters to become acquainted with key personnel and to conduct a preliminary review of the company’s accounting policies, controls, and systems. During this visit, (j) The enhanced network firewall project appeared to be on a very aggressive implementation schedule. The IT manager mentioned that even if he put all of his personnel on the project for the next five weeks, he still would not complete the project in time. The manager has mentioned this to company management, which seems unwilling to modify the schedule. Identify the problems and explain them in relation to the internal environment.CyberBest started to develop an anti-malware application on August 1, 20X1. It reached technological feasibility on March 1, 20X2, and the application was released on April 30, 20X2. Below are costs to develop the application. August 1 through December 31, 20X1 $5,000,000 January 1 through February 28, 20X2 1,600,000 March 1 through April 30, 20X2 1,800,000 Determine the amount of asset and the amount of R&D expenses relating to the development of this anti-malware application. $1,800,000 asset, and $6,600,000 R&D expenses $5,000,000 asset, and $3,400,000 R&D expenses $6,600,000 asset, and $1,800,000 R&D expenses $3,400,000 asset, and $5,000,000 R&D expenses
- Listed here are four scenarios. For each scenario, discuss the potential consequences and give a prevention technique. a) A company has recently installed a new computer network. The operating philosophy adopted by the new network administrator was to establish an open system that would foster work group date to the network users. To accomplish this objective, the data administrator assigned employee access privileges to data based on department and functional affiliation rather than specific tasks. b) Sara is a system programmer who was told she would be terminated in three weeks due to poor performance and was asked to conclude all of her projects during the three-week period. Two weeks later Sara created a logic bomb designed to get activated three months after her departure. Subsequently, the bomb destroyed hundreds of records in her previous employer’s accounts receivable invoice file. c) Matt discovered a new sensitivity analysis public-domain program on the Internet. He…Kruger Designs hired a consulting firm three months ago to redesign the information system that the architects use. The architects will be able to use state of- the-art computer-aided design (CAD) programs to help in designing the products. Further, they will be able to store these designs on a network server from which they and other architects may be able to call them back for future designs with similar components. The consulting firm has been instructed to develop the system without disrupting the architects. In fact, top management believes that the best route is to develop the system and then to introduce it to the architects during a training session. Management does not want the architects to spend precious billable hours guessing about the new system or putting work off until the new system is working. Thus, the consultants are operating in a back room under a shroud of secrecy. Required a. Do you think that management is taking the best course of action for the announcement…Systems Development and Implementation Kruger Designs hired a consulting firm 3 months ago to redesign the information system used by the architects. The architects will be able to use state-of-the-art CAD programs to help in designing the products. Further, they will be able to store these designs on a network server where they and other architects may be able to call them back up for future designs with similar components. The consulting firm has been instructed todevelop the system without disrupting the architects. In fact, top management believes that the best route is to develop the system and then to “introduce” it to the architects during a training session. Management does not want the architects to spend precious billable hours guessing about the new system or putting work off until the new system is working. Thus, the consultants are operating in a back room under a shroud of secrecy. Required: a. Do you think that management is taking the best course of action for the…
- Emery Communications Company is considering the production and marketing of a communications system that will increase the efficiency of messaging for small businesses or branch offices of large companies. Each unit hooked into the system is assigned a mailbox number, which can be matched to a telephone extension number, providing access to messages 24 hours a day. Up to 20 units can be hooked into the system, allowing the delivery of the same message to as many as 20 people. Personal codes can be used to make messages confidential. Furthermore, messages can be reviewed, recorded, cancelled, replied to, or deleted all during the same message playback. Indicators wired to the telephone blink whenever new messages are present. To produce this product, a $1.75 million investment in new equipment is required. The equipment will last 10 years but will need major maintenance costing $150,000 at the end of its sixth year. The salvage value of the equipment at the end of 10 years is estimated…Better Business Company (BBC) is in the process of planning a more advanced computer-based information system. Slavish, Moore, LLP, BBCs consulting firm, has recently been provided with an overview of their proposed plan: To ensure that the system functions as needed, the BBC Information System (BBCIS) will be created with input from its employees. System construction will begin with prototyping, computer-aided software engineering technology, and Gantt charts. From this point, IT professionals and a systems administrator, who are full-time employees of BBC, will create data models of the business process, define conceptual user views, design database tables, and specify system controls. Users in each department will submit written descriptions of their information needs and business problems to the IT professionals, who will then perform feasibility studies. Each aspect of the system will be documented in accordance with best practices and standards. The systems administrator will determine access privileges and maintain access control lists and database authorization tables. The administrator will have sole access to the transaction log, which will be used to record all changes made to database tables. A role of the administrator is to detect unauthorized access, reconstruct events, and promote personal accountability. The systems administrator will also be responsible for ensuring that virus protection software is current. Another important task of the administrator is to ensure that adequate backup to databases and applications occur and that disks and tapes are stored in a secure off-site location. Each employee requiring computer access will be assigned a user ID and password that will be entered when logging onto the system. If a computer terminal is left idle for more than five minutes, the system will close out the session and the user will need to log on again. Furthermore, users will be required to change their passwords once every year. Hardware will be purchased from Bell Computer Company with the advice of in-house systems developers. With the exception of basic applications, user departments will be allowed to purchase additional software that they need, which will be added to the system. BBCIS will run on a central server in the computer center located in the companys administration building. Two security guards will be assigned to the entrance to the computer room. To access the computer center, employees will swipe their ID cards on the lock to the main entrance door. The system will record the times of each entry and departure from the center. The data center will employ an advanced air-conditioning and air filtration system to eliminate dust and pollens. There will also be a sprinkler system to minimize damages in case of a fire. Required Based on BBCs plans for the implementation of a new computer system, describe the potential risks and needed controls. Classify these according to the relevant areas of the COSO framework.On September 30, 2018, Athens Software began developing a software program to shield personal computersfrom malware and spyware. Technological feasibility was established on February 28, 2019, and the program wasavailable for release on April 30, 2019. Development costs were incurred as follows:September 30 through December 31, 2018 $2,200,000January 1 through February 28, 2019 800,000March 1 through April 30, 2019 400,000Athens expects a useful life of four years for the software and total revenues of $5,000,000 during that time.During 2019, revenue of $1,000,000 was recognized.Required:1. Prepare the journal entries to record the development costs in 2018 and 2019.2. Calculate the required amortization for 2019.
- Avenue Eight Designs hired a consulting firm three months ago to redesign the information system used by the architects. The architects will be able to use state-of-the-art CAD programs to help designing the products. Further, they will able to store these design on a network server where they and other architects may be able to call them back up for future designs with similar components. The consulting firm has been instructed to develop the system without disrupting the architects. In fact, the top management believes that the best route is to develop the system and then to “introduce” it to the architects during training session. Management does not want the architects to spend precious billable hours guessing about the new system of putting work off until the new system is working. Thus, the consultants are operating in a back room under a shroud of secrecy. a) Do you think that management is taking the best course of action for the announcement of the new system? Why? b) Do you…Lamar LLC is in the process of updating its revenues and receivables systems with the implementation of new accounting software. James Loden, Inc. is an independent information technology consultant who is assisting Tamar with the project. James has developed the following checklist containing internal control points that the company should consider in this new implementation: Will all data entry clerks and accounting personnel have their own PCs with log‐in IDs and password protection?Lamar LLC is in the process of updating its revenues and receivables systems with the implementation of new accounting software. James Loden, Inc. is an independent information technology consultant who is assisting Tamar with the project. James has developed the following checklist containing internal control points that the company should consider in this new implementation: Has the company identified an off‐site alternative computer processing location?



