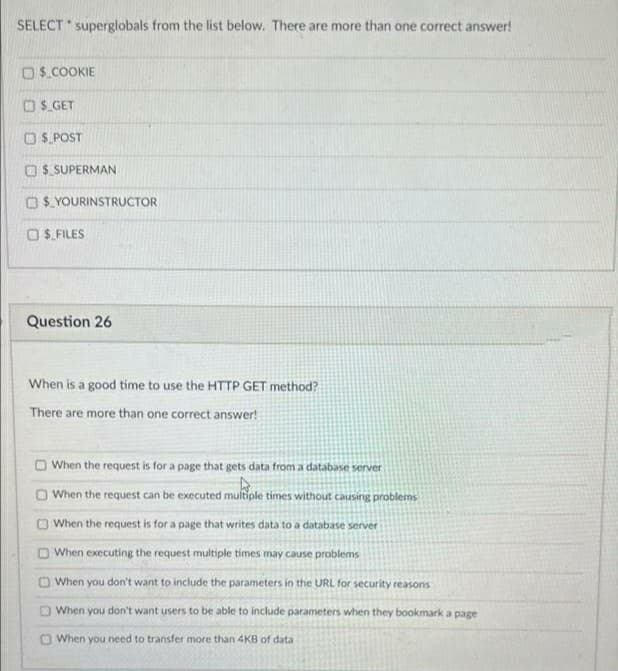
SELECT superglobals from the list below. There are more than one correct answer! OS.COOKIE OS GET O S. POST O $ SUPERMAN OS.YOURINSTRUCTOR OS. FILES
Q: Write the MATLAB Code for the ff: Given the vectors: a = [3 6 7]; b = [1 9 4]; c = a + b
A: The answer is given below.
Q: Programming Assignment Implement the following pseudocode in x86 assembly language. Use short-circu...
A: Solution:: Let's see the above question is assembly language:: Assembly code: cmp val1, ecx jnb ...
Q: Determine the reliability between Devices A and B shown in Figure 1. Step-by-step calculations must ...
A: Five - nines Five-nines availability -- or 99.999% -- is the percentage of time a network component ...
Q: Explore database history and debate the three most significant database developments to date.
A: Introduction: There have been several changes throughout the years. Three significant changes in the...
Q: Which of the following is a challenge for creating dashboards in Excel without the Power BI tools? Y...
A: Dear Student, Excel requires manual compiling of data which will be very difficult for a person to m...
Q: Write a program that prompts the user to input the length of a string as an integer, followed by the...
A: logic:- read length of string from user. i.e read len. create memory size as per value of len using...
Q: 2. Write a JAVASCRIPT program to find the total count of occurrences of the characters j' and 's' in...
A: Iterate over the given string and keep on checking each of the character and increment respective co...
Q: Determine the twos' complement for hexadecimal 4B,, that is stored in a WORD size storage location. ...
A: size of word = 2 byte = 8 bits 1111 1111 1011 0101 procedure- subtract hexadecimal no. from FFFFFF...
Q: What are the conditions under which a VPN between two networks is feasible
A: VPN : VPN stands for Virtual Private Network. VPN is used to create a safe channel for transferring...
Q: Recreate the form below using HTML --- IMPORTANT REMINDER: Make sure that the picture box is able to...
A: Question given - A bio-data form is given on a paper, design this form using HTML so it can be fill...
Q: "Divide and conquer" is one of the most fundamental ideas that guide software engineering practice, ...
A: Introduction: Compound instructions, algorithms, and data structures come to mind when people genera...
Q: Explain the significance of communications protocol selections, as well as the protocols that were u...
A: Introduction: A communication protocol is a set of rules that enables two or more entities in a comm...
Q: Statisticians use the concepts of mean and standard deviation to describe a collection of numbers. T...
A: Program :- import math def gradeCurve(scores, m, s): """ Function that finds grade distrib...
Q: Remember that packet reordering and reassembly take place during the transport step of the TCP/IP pr...
A: Introduction: TCP/IP is an acronym for Transmission Control Protocol/Internet Protocol and refers to...
Q: Computer Science can someone pls make this video 4) Changing the dataset (and thus alteri...
A: First let's calculate BMI (body mass index) BMI of 5' and 100lbs ==19.53 BMI of 5'7'' and 140lbs==21...
Q: Define and implement the overloaded swap function for swapping a pair of strings, vectors of doubles...
A: The answer is given below.
Q: e of a Co
A: Clock Rate: The clock rate, also known as clock speed, is the frequency at which a processor's clock...
Q: What exactly is a data race?
A: Introduction: A data race happens when two or more threads in the same process simultaneously visit ...
Q: You work for AngloGold Ashanti as the Systems Administrator. You've been having problems with your s...
A: INTRODUCTION: Server response time: It takes the web browser a certain amount of time to get a respo...
Q: What are the three most important tactics for installing an operating system? When is each of these ...
A: Introduction: An operating system is a software application that acts as a bridge between the compon...
Q: Examine any possible connections between utility computing and grid computing and cloud computing.
A: Introduction: GRID COMPUTING is the use of computational resources from various administrative juris...
Q: Determine whether the following assertion is true or false; if it is true then prove it, and if it i...
A: We are given an assertion on Euler cycle, we will see if the assertion is true or false. Please refe...
Q: Q.Write a program to create a Distance class containing kilometers and meters as data members. Also ...
A: Program Explanation: Declare the header file Define a class for Distance Declare the instance varia...
Q: Is there a point to Big-existence? O's What is the most dire scenario for Big-O? Why should you be c...
A: Introduction: Big-purpose: O's The big-O notation is used to express how the time required to execut...
Q: Write a Python program to input an integer t and print the sum of all multiples oft and 5 in the out...
A: Python Program: # Enter an integer t by user as inputt = int(input("Enter an integer: ")) # s for su...
Q: What ideas of functions are there in Swift once more? What are some of the aspects of Swift's functi...
A: Functional programming isn't a language or a syntax , however rather a programming paradigm — some w...
Q: What are the approaches of software design and development?
A: Introduction : The following are the components of the programming design: Comprehend the programmer...
Q: fun g(a, b, c, d) = if c[b(a)] < 1.2 then 2 * b(a) else 2 * d * a Using Hindley-Milner type...
A: fun g(a, b, c, d) = if c[b(a)] < 1.2 then 2 * b(a) else ...
Q: A decision tree with better splits means that it can be more accurate in
A: A decision tree is a graphical model used to represent decisions in a decision-making process. It is...
Q: Explain the usefulness and limitations of traffic engineering as a solution for the problem of netwo...
A: The Answer is in step2
Q: Recreate the form below using HTML --- IMPORTANT REMINDER: Make sure that the picture box is able to...
A: Solution - Programming language used: HTML for form design. Internal and inline CSS for style form...
Q: Attributes of a system visible to programmers are under Compu Select one: O True
A: Lets see the solution.
Q: Select for what applies to the following Power off - Sleep Restart Hibernate Power on Designed for n...
A: here we have given the options for the given queries, you can find them in step 2.
Q: Statisticians use the concepts of mean and standard deviation to describe a collection of numbers. T...
A: Code :num_scores = int(input('Number of scores: ')) print('Enter',num_scores,'scores:') scores = [] ...
Q: What exactly is a consistent database state, and how does one go about achieving one?
A: Consistency of data implies no duplication or mismatching of data.
Q: Explain the stages of Donald Norman's model of interaction in a few sentences
A: A model of how people interact with the real world is one of the themes covered by usability researc...
Q: Write a line of Python code to randomly select 4 items from the list menuitems and assign it to the ...
A: Python is the coding language and is the object-oriented requirement as the dynamic, code strong and...
Q: 1- Explain in details what happens for each instruction's execution.
A: The program to be run consists of a set of instructions stored in memory. To finish a job, the centr...
Q: Define collapse which reduces a list of MkType a b to two lists of type a and b respectively. You sh...
A: The collapse which reduces a list of MKType a b to two lists of type a and b respectively respecting...
Q: Explain how to use the DiskPart program.
A: Introduction: It is necessary to open the command window to utilize Disk Part. We'll go through two ...
Q: TCP (Transport Control Protocol) is a transport layer protocol that delivers full duplex, connection...
A: Introduction: TCP is a transport layer protocol that delivers full duplex, connection-oriented, and ...
Q: What kind of data leak has Facebook/Cambridge Analytica experienced?
A: Introduction : A data breach occurs when private information is intentionally or unintentionally lea...
Q: What is a unique feature for Power BI Services (PowerBI.com)? Build interactive visuals Build Pivo...
A: The answer is A) Build interactive visuals
Q: In the process of deleting rows, columns, and tables, what is an important point to bear in mind is
A: Introduction: A database management system is built to efficiently handle the records of numerous as...
Q: (C PROGRAMMING ONLY) Do not edit the main() code. 5. My Sincere Apologies by CodeChum Admin Okay,...
A: Step 1 : Start Step 2 : Declare the function sendApology() which accepts a character and an integer ...
Q: Analyze the advantages of agile development versus traditional formalized development approaches.
A: Agile is iterative and incremental model.
Q: You are a teacher of one programming course and you give to the students one exercise. In this exerc...
A: You are a teacher of one programming course and you give to the students one exercise. In this exerc...
Q: he Word template is used for recording the measur elect one: OTrue
A: Lets see the solution.
Q: What is a conformant array, and how does it work?
A: Given To know about the conformant array.
Q: ite algorithm and draw a flow chart to develop a simple calculator that perform addition, subtractio...
A: Lets see the solution.
Step by step
Solved in 2 steps

- How to remove the item from the cart if the quantity is 0? I have included my code below that I am confused about how to implement this on. <?php session_start(); $page = 'cart'; //DATABASE CONNECTION INFO include_once ('includes/database.php'); include_once ('includes/header.php'); if(!isset($_COOKIE['loggedIn'])) { header("location: login.php"); } if (isset($_POST['update'])) { for ($x = 0; $x < sizeof($_SESSION['quant']); $x++) { $quant_id = 'quant_'.$x; if($_POST[$quant_id] > 0) { $_SESSION['quant'][$x] = $_POST[$quant_id]; } elseif($_POST[$quant_id] == 0) { //HOW DO I REMOVE THE ITEM FROM THE CART IF QUANTITY IS = 0? } else { echo "Quantity must be greater than 0 to purchase."; } } } if(isset($_POST['remove'])) { //HOW DO I REMOVE THE ITEM FROM THE CART IF THE "REMOVE" BUTTON IS CLICKED? } if(isset($_POST['submit_order'])) {…COM. Question 4 ObjectOutputStream can write primitive types and graphs of objects to an OutputStream as a stream of bytes .These strom can subsequently be read uning InputStream. True False Question 5 When a client invokes a remote method , it calls a proxy not the original method . True False Question 6 A cookie is created with this : Cookie cookie new Cookie ( " key " , " value " ) ; After creation , you can change only the value of it with the setter method that's provided in the Cookie class . True False• Exercise 1: Please create a script that print “Hello, your name.” • Exercise 2: Please create a directory call user_bin, and add it to PATH. Then mv script of Exercise 1 to user_bin. Then run it from your root directory.• Exercise 3: Add a new command call ‘l’ which will perform exact same as ‘ls -a’. • Exercise 4: Create a function call sortFile, which will sort all filenames of current directory.• Exercise 5: Please make your own page using shell script, print following as your page. <html><head><title>My System Information</title></head><body><h1>My System Information</h1></body></html> Exercise 6: Could you add one variable in the example, name the variable as greeting, which displays “Hello, my name is xxx xxx” in the body using variable greeting.• Exercise 7: Could you add one variable in the example, name the variable as FILE_LIST, which displays the filenames of current working directory
- The Linux operating system is a very popular server OS. A network administrator has to protect the login/password files stored on the servers. In Linux there are two important files: /etc/passwd And it contains rows that look like this: root:x:0:0:root:/root:/bin/bash bin:x:1:1:bin:/bin:/sbin/nologin daemon:x:2:2:daemon:/sbin:/sbin/nologin adm:x:3:4:adm:/var/adm:/sbin/nologin ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin user1:x:15:51:User One:/home/user1:nologin user2:x:15:51:User One:/home/user1:nologin user3:x:15:51:User One:/home/user1:nologin This file contains login information. It's a list of the server's accounts that has userID, groupID, home directory, shell and more info. And the second file /etc/shadow, contains rows that look like this: root:$1$TDQFedzX$.kv51AjM.FInu0lrH1dY30:15045:0:99999:7::: bin:*:14195:0:99999:7::: daemon:*:14195:0:99999:7::: adm:*:14195:0:99999:7::: ftp:*:14195:0:99999:7::: user1:$1$ssTPXdzX$.kv51AjM.FInu0lrH1dY30:15045:0:99999:7:::…Linux Quiz (Accurate answers please!) Write the command to create a directory Write the command to print "hello World" to the terminal screen Write the command to move to the home directory of user linadm using a relative path. Write the command(s) that will set the color variable and send its value to a sub shell What login ids have access to the sudo command. Extract from the /etc/group file provide a list of all logins that run the bash shell. Include in your list the login name and login id #. Sort the results.dir c:\ /s /b | find "LOG" | more When executed in a cmd.exe shell, what does this command do? Exactly? Every command, every parameter, every meta-character. What is dir? Where does dir reside? (.exe, .com, ??? what is it/who has it) c:\ /s /b | find “log” | more
- Rewrite the same code with a different logic make sure you have the same output. <?php$cookie_name = "user";$userID = $_COOKIE[$cookie_name];if(!isset($_COOKIE[$cookie_name])){ echo "Please login in first!<br>"; exit();} include "dbconfig.php";$conn = new mysqli($hostname, $username, $password, $dbname) or die($conn->connect_error);$name = $_POST['name'];$description = mysqli_real_escape_string($conn, $_POST['description']);$term = mysqli_real_escape_string($conn, $_POST['term']);$enrollment = $_POST['enrollment'];//Query course name$Rid = '';$userGivenFacultyID = $_POST['Fid'];$userGivenRoom = $_POST['Rid'];$queryRid = "SELECT Rid FROM TECH3740.Rooms WHERE CONCAT(Building,Number) like '%$userGivenRoom%' ";$resultRid = mysqli_query($conn, $queryRid);$rid_row_ct = $resultRid->num_rows;if($rid_row_ct = 1){while($ridRow = $resultRid->fetch_assoc()){$Rid = $ridRow['Rid'];}} $queryRoomSize = "SELECT Size FROM TECH3740.Rooms WHERE Rid = $Rid";$resultRoomSize =…ARIES supports ___________ operations, which are physical in that the affected page is physically identified, but can be logical within the page. a. Physiological redo b. Physiological undo c. Logical redo d. Logical undo1) What happens if myfile.txt does not exist? Group of answer choices fopen("myfile.txt", "r") returns FALSE fread("myfile.txt") returns 0 bytes fopen("myfile.txt", "r") creates "myfile.txt" fread("myfile.txt", filesize("myfile.txt")) returns FALSE 2) The mysql command-line tool is used to _____. perform administrative functions in MySQL server access a database without using a username and password connect to any database that exists on the same machine develop websites that need to access a MySQL database 3) Fill in the blank to have this code block display selected information using PDO. $sql = "SELECT itemName, quantity FROM inventory WHERE quantity > 1"; $result = $pdo->query($sql);foreach (_____) { echo "There are $row[quantity] of $row[itemName].<br>\n";} Group of answer choices $result as $row $row = $result->fetch() $row as $result->fetch() $result in $row 4) What MySQL error code is returned when the following SQL statement…
- USING UBUNTU! Show me all code for each step! Be detailed please. * Apache running * All user html directories named pub. Therefore http://googee.nmu.edu/~fred gets mapped to /home/fred/pub. * Make a new user named WWW. The "/" gets mapped to /home/WWW/pub. Therefore http://googee.nmu.edu gets mapped to /home/WWW/pub/ * A basic index.html file in /home/WWW/pub * Setting such that there are no directory listings and no cgis runnable * The URL http://googee.nmu.edu/icons mapped to /home/WWW/Pictures/icons * Logs stored in /var/log/my_wb_logs in combined logfile format * A web analyzer (webalizer = 0.5, analog = 1.0) that shows activity stats accessable via the web. * The user 'someone' is unable to make web pages in his home directory tree, even if he's tricky. No hand written and fast answer with explanationPlease write down the Linux command for each question. 17.1 What command should be used to change the read, write and execute permission of a file? 17.2 The command for a user wants to delete recursively all files and subdirectory from current directory is 17.3 What is the command which edits the scheduler for automatic command executions at background? 17.4 This command let a user check the names of the groups that this a/c belongs to. 17.5 What do we expect to see if running “$ echo `expr 2 \*3`? 17.6 Upon booting up the OS, the latest kernel initialization daemon process that the Ubuntu distribution is using today is ____ 17 Like to find files with “.sh” extensions from current local directory to all its subdirectories, what is the command? 17.8 What is the command to find the IP address of a network card? 17.9 What is usually written on the first line in shell scripts? 17.10 Like to backup all files and subdirectories under /var/www, the output file name is today.tar. The…Assume that there is a function in a web application that allows users to change theircurrent email address to a new one.The following is an example of a HTTP POST request that will be sent to the vulnerableweb application when the user tries to perform email change action:POST usr/emailchange.php HTTP/1.1Host: example.comConnection: Keep-AliveCookie: session=abcwsdagePkBZzeR9hGhTlvxyHfsZf1The following is the parameter for the email in the POST request:Form Dataemail=example@utas.edu.au(a) Design an CSRF attack to exploit the existing vulnerability by creating an HTMLpage with the required method, URL, parameters and action to change the emailwhen the victim hits the URL of this webpage. Assume that there are no preventiontechniques implemented.(b) What will happen if the victim hits your code in (a) when he/she authenticatedalready?(c) What will happen if the victim hits your code in (a) when he/she not authenticatedalready?

