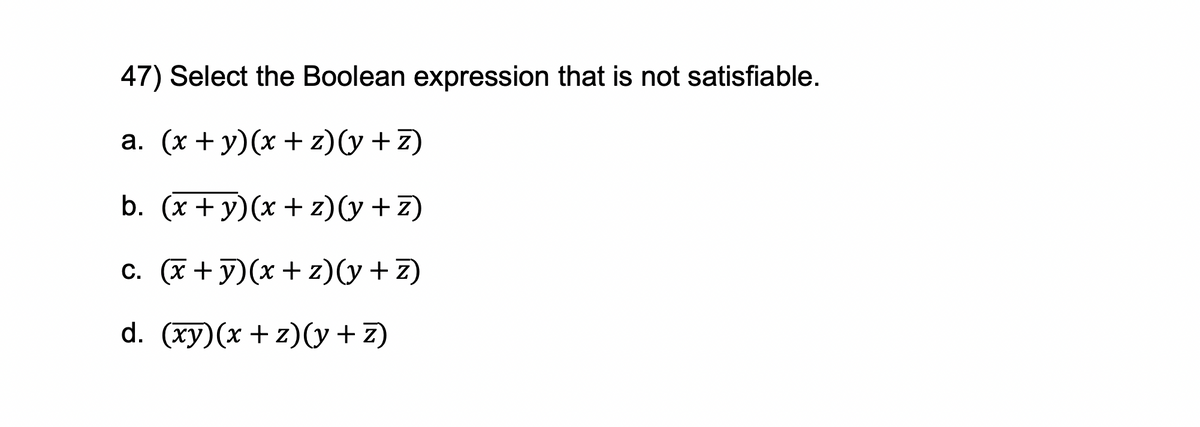
Select the Boolean expression
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: As detailed below, a P2P file-sharing programme has no idea of the client and server sides of a…
Q: How essential do you think computers are to you, and what role do you see them having in your…
A: Use of the computer in our life is incredibly necessary.
Q: Examine how solid-state and magnetic secondary storage systems vary from one another and from one…
A: Magnetic hard drives and solid-state drives have a few different features that make them optimal for…
Q: This is the situation as a direct consequence of computers' recent advances in capabilities. How can…
A: INTRODUCTION: Although the power of computers has been with us since their birth, they are now…
Q: Exercise 3. Consider the following algorithms A and B for the problem of computing 2n (mod 317)…
A: Given: For Algorithm A: mod_exp_A(n) {if (n== 0) return 1;else {t = mod_exp_A (n/2);if (n is even)…
Q: Which of the following statements defines a TRANSACTION? a. A transaction is a physical unit of…
A: TRANSACTION:- A transaction is a commercial occurrence that results in a monetary impact on the…
Q: Describe a situation or problem from your job, everyday life, current events, etc., for which a…
A: Lets see the answer:
Q: Give a justification for why video data uses and consumes more storage space than other forms of…
A: Explain why video data demand and use more storage space than other forms of data. A video is a…
Q: How can app makers generate money if the app requires internet connectivity to function?
A: INTRODUCTION: Some analysts predict that the market for agile software will reach $100 billion by…
Q: Give a description and an explanation of the CRUD procedure. What is it specifically, and how does…
A: The four fundamental actions that each software program should be able to carry out are called CRUD:…
Q: To speed up processing, the majority of retail enterprises employ barcode scanners to collect…
A: This kind of data collection is referred to as bar-code scanning, and the devices that are used to…
Q: Write a Java console application to print a report and determine if a hospital is due for a health…
A: The answer for the above question is given in the below step for your reference.
Q: Can one identify the benefits and drawbacks of different verification methods from the perspective…
A: Introduction: The world is confronting an unfamiliar climb into the new digital scene. We are riding…
Q: What do you think are some possible solutions to the issues that these people confront, and what…
A: The answer is given in the below steps Happy to help you ?
Q: How does ransomware function in terms of computer security?
A: Ransomware infects a compromised computer, encrypting user data and locking it until a ransom is…
Q: When explaining the DNS, be sure to mention authoritative and root servers, iterated and…
A: In this question we need to explain the Domain Name Service (DNS) with mentioning authoritative and…
Q: On the other hand, it has been suggested that a processor be used that can decode encrypted data and…
A: Central Processing Unit (CPU) :This cycle is observed by using the Central Processing Unit (CPU)…
Q: Give a description and an explanation of the CRUD procedure. What is it specifically, and how does…
A: Given: The CRUD approach and its connection to use cases need to be highlighted.We must also…
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Optical scanners include barcode readers and barcode scanners: These scanners can decode printed…
Q: What exactly is a poison package attack and what does its occurrence mean? If you could give me two…
A: Introduction: ARP Poisoning, often referred to as ARP Spoofing, is a type of Internet attack on the…
Q: Write a short essay (roughly 250 words) about some topic related to data communication technology…
A: According to the information given:- We have to define a short essay related to data communication…
Q: How is the word "phishing" defined and what does it truly mean?
A: Phishing: Phishing is cybercrime and social engineering that attempts to obtain critical user…
Q: A program called lsu [104] gives access to role accounts. The user's access rights are checked, and…
A:
Q: What is the authentication procedure? What are a few of the goals? Examine how the advantages and…
A: The answer to the question is given below:
Q: Which of command line tool is used to query d s name servers for information about host addresses…
A: Which of command line tool is used to query d s name servers for information about host addresses…
Q: Look at the assaults coming from inside the academy. If you have any suggestions on how to stop…
A: Consider college's internal assaults. Please provide any tips for avoiding assaults. Students…
Q: What does ransomware really accomplish in terms of computer security?
A: Ransomware is a type of malware that restricts access to data or software on a computer. It is…
Q: irst: make a menu list as you find suitable, three main options for the question ake suboptions for…
A: I have written code for the first one:
Q: Describe the purposes and applications of smartphones, digital cameras, portable and digital media…
A: Modern technology is evolving quickly and introducing new products to the market. digital cameras,…
Q: Convert UML class diagrams to Java code You are required to convert the UML class diagrams shown…
A: Required language is Java:
Q: Which of the following is true of foreign keys? A foreign key should always be linked to a primary…
A: Foreign key is a very important concept in databases.
Q: To speed up processing, the majority of retail enterprises employ barcode scanners to collect…
A: A barcode which refers to the image that consists of a series of parallel black and white bars that…
Q: Why does video data need more storage than other types of data and why does it use up more storage…
A: It's important to discuss why video data needs more storage space than other forms of data. Several…
Q: What advantages come from knowing how to use computers? Technology improvements benefit society,…
A: Given To know the benefits of computer use and how technology is useful in education, business, and…
Q: What type of long-term effects may a data leak have on cloud security? What specific steps may be…
A: The loss of client trust is the most detrimental long-term effect of a data leak: Customers entrust…
Q: Print Floyd’s Triangle in java Program
A: Floyd’s Triangle in java Program:-
Q: How do we Configure both Cisco Router (Standby and Active) and Cisco Switches to defend against HSRP…
A: The Hot Standby Router Protocol (HSRP) is a First Hop Redundancy Protocol (FHRP)(FHRP) designed to…
Q: What websites do you regularly visit?
A: A website can be described as a collection of web pages. A common domain name is used for all those…
Q: Give five recommendations to help stop ransomware attacks.
A: Ransomware is a sort of malicious software (malware) that threatens to publish or limits access to…
Q: Use a software program or a graphing utility to solve the system of linear equations. (If there is…
A: Linear equation : An equation is said to be linear if the maximum power of the variable is…
Q: What actions may be made to improve the security of cloud storage after a data breach? What are some…
A: It has become very common to have data breaches.
Q: A program called Isu gives access to role accounts. The user's access rights are checked, and the…
A:
Q: escribe how a computer program might be t d efficiently on a modern pipelined compute as on these…
A: Design:
Q: LWC Assignment: Create a LWC component to display the output. You can create the dummy data in JS…
A: LWC ( Lightning Web Component ) : A collection of modern, lightweight frameworks built on the recent…
Q: What do you think are some possible solutions to the issues that these people confront, and what…
A: The answer is given in the below steps Happy to help you ?
Q: Describe the most successful ways for discovering images that may be used without authorization.
A: Steps to take: The best approaches to look for photographs that are copyright-free must be…
Q: A synthetic benchmark is a program constructed to have performance very similar to that of the real…
A: Synthetic benchmark In order to simulate the properties of a large number of programmes, artificial…
Q: Which steps while utilizing an application to access a database are mostly the same?
A: The vast majority of the services we use on the Internet are brought to us through web database…
Q: In-depth discussion is given to DNS records, authoritative and root servers, iterated and unified…
A: Introduction: Domain Name Servers (DNSs) are the devices that map the hostname to the IP addresses…
Q: Why does video data need more storage than other types of data and why does it use up more storage…
A: According to the information given:- We have to define why video data need more storage than other…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Create truth tables for the following expressions:a. S = NOT((A OR B) AND (NOT(A) OR NOT(B)))b. S = (A AND B) OR NOT(A OR B)c. S = (A) OR (B AND C) OR (NOT(B OR C) AND (A OR C))d. S = ((A AND B) OR (C AND D)) AND NOT((C AND NOT(A)) OR (B AND D))Assume the variables a = 2, b = 4, and c = 6. state true or false. a >= −1 || a <= b1. Determine if the expression: (!( a>=b) || !( a==c )) is True or False. Given the value of a is 2, b is 10 and c is -5. 2. Determine if the expression: ! (!(a>b) && ( a==c) || ( a>=b ) ) is True or False. Given the value of a is 2, b is 10 and c is -5. 3. Determine if the expression: !( b>c ) || ( c<5 ) is True or False. Given the value of b is 10 and c is -5.
- Assume the variables a = 2, b = 4, and c = 6. state true or false. !(a > 2)Implement the following Boolean expressions as they are stated: (a) X = ABC + AB + AC (b) X = AB(C + DE)true or false 1. Determine if the expression: ! (!(a>b) || ( a==c) || ( a>=b ) ) is True or False. Given the value of a is 2, b is 10 and c is -5. 2. Determine if the expression: ! (!(a>b) || ( a==c) || ( a>=b ) ) is True or False. Given the value of a is 2, b is 10 and c is -5.
- 1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as: 3)convert the following decimal fractions to binary with a maximum of six places to the right of the binary point: 1)25.84375 2)57.55 3)80.9065 4) Convert the following binary fractions to decimal: 1)100001.111 2)111111.10011 3)1001100.1011 5) Fill in the blank. The representation of 60 in binary using 8-bit signed magnitude is ______, in ones complement is ______, in two’s complement is ______, and in excess-127 is ______.Minimize the following expression using Boolean rules: F=XY+X(Y+Z)+Y(Y+Z)Draw truth tables for the following expressions:(a) F = AB (B + C + D′)(b) Y = (A + B + C) AB′(c) F = AB + BA + C (A + B)
- Use C++ to program a Magic Eight Ball.Computer Fundamentals and Programming 2 Problem 2: Given two number for the variables A and B, create a program that would: A. print the sum of A and B B. print the average of A and B, if the sum is greater than 100 C. print the product of A and B, if the sum is less than or equal to 100.Translate this into mathematical symbol: A number is decreased by 12 and is multipled by 8; the result is 7.

