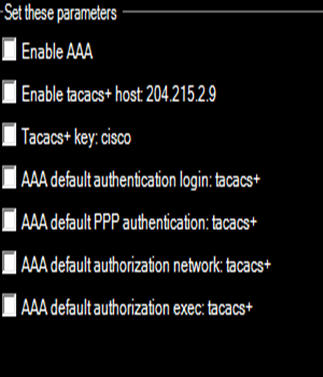
-Set these parameters Enable AAA Enable tacacs+ host: 204.215.2.9 Tacacs+ key: cisco AAA default authentication login: tacacs+ AAA default PPP authentication: tacacs+ AAA default authorization network: tacacs+ AAA default authorization exec: tacacs+
Q: b.Explain, as if to a non-technical friend, what geofencing is and how it can be used as part of an…
A: Geofencing: Geofencing, as the term implies, is a method for setting virtual borders around physical…
Q: What are differences between Cloud and Fog computing?
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: Nextdoor App is popular in rural areas. True or false b. In comparison to legal professionals,…
A: Nextdoor app: It is a social media network to connect neighborhoods. It is an online platform. It…
Q: What are the hallmarks of structural database testing, and how does it differ from other forms of…
A: Introduction: Data that has been organized and stored in a database can be accessed online.
Q: What are the advantages of using COTS (Cost On The Shelf) selection when developing software…
A: Introduction: Below is a list of the benefits of using COTS (Cost On The Shelf) options when…
Q: In addition to the services just mentioned, what additional cloud-based data storage options are…
A: Cloud storage which it is a cloud computing model that enables storing data and files on the…
Q: Q4. Need Asap 0. Write Boolean expression For each Row in Table. 1. Draw a k-map table based on the…
A: As per our company guidelines only 3 sub parts will be answered. So, please repost the remaining…
Q: Please describe the two-tier and three-tier structures for software applications. Which is…
A: In a multi-tiered application, functionality is split into tiers. Define "two-tier" and "three-tier"…
Q: To help, it would be great if you could provide a comprehensive list of all the parts that go into…
A: A PC software called a Kernel serves as the brains and nerve centre of an operating system, which…
Q: Solve an example of searching, deleting and inserting values in a hashtable of certain length using…
A: Solve an example of searching, deleting and inserting values in a hash table of certain length…
Q: 5. Suppose the following expression is given: X =A'B'C'D +A'B'CD' + A'BC'D'. Implement the…
A: Please refer to the following step for the complete solution to the problem above.
Q: I was hoping you could give me a high-level overview of what software engineering aims to achieve.…
A: Software engineering is a systematic approach to software development, usage, upkeep, and retirement…
Q: Question 13 Ensuring compliance with various industry and regulatory standards on information…
A: Company compliance includes both internal policies and procedures as well as federal and state laws.
Q: Abstract data types (ADTs) are a vague concept. To what extent can ADTs help? How might an…
A: Type of Abstract Data A data type is defined by its behaviour from the perspective of the user using…
Q: Describe the design of a chat server in detail. Give specifics on the different classes, methods,…
A: solution is given below
Q: Explain the challenges that come with using real-time speech recognition technologies. It's…
A: In fact, the solution is provided below: a) Analyze the concerns and difficulties associated with…
Q: Your program should: first prompt the user to enter the number of values (input size), second prompt…
A: A. Your program should: first prompt the user to enter the number of values (input size), second…
Q: Is it better to begin a data modelling project with a pre-made data model or a clean slate?
A: A data model aids in conceptual, physical, and logical database architecture. Although the initial…
Q: When was the first tablet computer created, and who created it?
A: A portable or handheld device is increasingly essential for personal computing and storing a…
Q: Why do we need to invest so much time and money into AI research and development? Your summary,…
A: The inquiry is interested in learning what the final goal of Artificial Intelligence is. This…
Q: When you say "abstract data type," what do you mean by that term?
A: "Abstract Data Type" (ADT) In contrast to data structures, which are used to represent concrete data…
Q: Each of the parallel methods discussed here is unique to Linux. This is not the case with any other…
A: In the field of software engineering, the concept of "concurrency" is used to describe methods and…
Q: Which Class member modifier below makes a Java Class data member a constant, and a method member…
A: The solution is given below with explanation
Q: Using Floyd's algorithm, solve the all-pairs shortest path problem for the ligraph with the…
A: Solution to the given question, Using Floyd's algorithm
Q: Which of the conditions below, if any, indicate that the underlying array for an array-based queue…
A: As per the question statement, It is asked to choose the correct options.
Q: What exactly is the definition of a thread in a computer's operating system?
A: These question answer is as follows,
Q: Where do Mobile First and Desktop First diverge in terms of responsive web design? Where do they…
A: Mobile-First Design: The purpose of mobile-first design is essential to make something that appears…
Q: Explain how Internet of Things protocols are standardized. Examine all aspects of the IoT via the…
A: Overview: One of the biggest obstacles to the development of the IoT is standardisation. The…
Q: Show your work to prove that the hexadecimal equivalent to the integer 11110 is 6F16
A: Dear learner, hope you are doing well, I will try my best to answer this question. Thank You!!
Q: Tell me about some of the network commands you've used and how you've gone about fixing problems on…
A: A network is a collection of connected computers, servers, mainframes, network devices, peripherals,…
Q: .My company uses MYSQL but someone said it is outdated so I want to think of a new solution or maybe…
A: MongoDB is a strong open source and allowed to-utilize non-social information base framework well…
Q: Given a decimal number as input, you are asked to write a program in C++ to convert the given…
A: We need to write the main function for the given code.
Q: When compared to the traditional software development lifecycle, the agile approach will be…
A: Introduction: Answer with the points and explanations provided below to compare the traditional and…
Q: When would you need an array with more than two dimensions
A: A matrix has two dimensions, which are represented by rows and columns, respectively. There are two…
Q: f(x)=2x 1 2 +4x 1 x 2 3 −5x 1 x 2 +x 2 2 with…
A: Given: Describe & implement the goal function and the cond7 function for the mentioned task.
Q: The reader has to be aware of the need of conducting regular wireless audits and of the scope of…
A: A security auditor will conduct a wireless audit to evaluate the wireless network security at your…
Q: How does one go about creating cloud storage?
A: Answer is
Q: Generate prefix codes that represent 8 different letters. Then calculate the saving percent compared…
A: We need to generate prefix code for given scenario and calculate the savings in space.
Q: Learn the distinctions between class adapters and object adapters. In addition, how would you sum up…
A: The Adapter class offers the default modification of all interface methods; because we don't have…
Q: 32. How do you find the factorial of an integer
A: I give the code in C along with the output and code screenshots as no language is mentioned
Q: How do the machine learning and deep learning algorithms of today's AI age compare to those of the…
A: New technologies and robotics employ machine learning and AI algorithms. This AI age differs from 50…
Q: 7. A grammar contains A. set of terminals and non-terminals C. set of productions B. start symbol D.…
A: A grammar is a 4 tuple structure (N,T,P,S): N : Non terminals T : Terminals P : Production rules S :…
Q: Consider the following grammar: -> c | b -> a | a -> b | a What nonterminals are disjoint?…
A: Answer The nonterminals A and C are disjoint because all the right-hand sides of the production…
Q: For the.NET Framework, what are the key differences between an executable (EXE) and a dynamic link…
A: Let's first see about the EXE and DLL EXE The programs that need to be compiled on the Windows are…
Q: 3. (a) Check whether the given grammar is ambiguous or not S- aSbs |bSaS € Given input String is…
A: Please refer to the following step for the complete solution to the problem above.
Q: If f(n)=(h(n)) and g(n)=(h(n)) then (select all that applies): a) f(n)+g(n)=(h(n)) b)…
A: Given that: f(n) = theta(h(h)) and g(n) = Θ(h(n)) Note: Θ(h(n)) means both O(h(n)) and Ω(h(n)) means…
Q: Could you please walk me through the process of using cloud storage?
A: Online storage: Cloud storage is the term used in computer science to describe the reading and…
Q: We'll explain why the components of the event delegation paradigm are so useful for creating user…
A: The delegation event model outlines uniform and standardised methods for creating and handling…
Q: Instructions: Write your answer on a piece of paper with your name on top. Take a picture and submit…
A: As per the question statement, It is asked to write code for the requirement. As no language is…
Q: need help coding the nav items so they are spaced vertically on top of the page and for there to be…
A: To build a vertical navigation bar, you can style the <a> elements inside the list, in…
Step by step
Solved in 3 steps

- Consider the following simple authentication dialogue: C → AS: IDc II Pc II IDv AS → C: Ticket C → V: IDc II Ticket; Ticket = E(Kv, [IDc II ADc II IDv]) Where: C = client AS = authentication server V = server IDc = identifier of user on C IDv = identifier of V Pc = password of user on C ADc = network address of C Kv = secret encryption key shared by AS and V ***Explain the process of this protocol.5, For the first mode of Message Authentication code (MAC), which description is NOT correct? The key used in this mode is for message encryption. This mode cannot protect message confidentiality. The receiver is able to detect malicious message modification by checking the MAC. The attacker who does not know the key cannot calculate the MAC.Assume a web server can only receive TCP connections on port 80 (HTTP) and 22 (SSH), but not on any other ports. The web server can only establish connection to a database server hosted on private IP 192.168.100.100 on port 3000, but to no other machines inside or outside the network. Imagine this web server is running Linux, and we’re using iptables to define host-based firewall rules for it. Show the set of iptables commands to install necessary rules for this security policy.
- Write a PHP script that could be used to connect to MYSQL database named gctudb running on a web server with IP address "192.168.10.100". Assume the user name is nuksoft and the password is makadcode. Remember to close your connection explicitly.Look at the following IP scope. Is this a valid scope (YES/NO)?If NO. How would you correct the scope.IP SCOPE: 192.268.4.50 – 272Subnet Mask 255.255.255.0Gateway 192.168.4.1Show how to implement native authentication and authorization services when a web client wants access to protected web server resources. Which two parameters support layered protocols? Give examples to back up your point.
- The following is output from the show ip eigrp topology command. Does this output show a feasible successor? How can you tell? P 192.168.10.4 / 30, 1 successors, FD is 3523840 via 192.168.10.10 (3523840 / 2169856), Serial0 / 1 via 172.16.3.1 (41024000 / 2169856), Serial0 / 0An attacker tries to do banner grabbing on a remote web server and executes the following command:$ nmap -sV hackme.com -p 80 He gets the following output:Starting Nmap 7.90 ( http://nmap.org ) at 2020-09-26 22:47 ESTNmap scan report for hackme.com (108.58.137.114)Host is up (0.048s latency).PORT STATE SERVICE VERSION80/tcp open http Apache httpdService detection performed. Please report any incorrect results at http://nmap.org/submit/.Nmap done: 1 IP address (1 host up) scanned in 7.36 seconds What did the hacker accomplish? nmap can’t retrieve the version number of any running remote service. The hacker successfully completed the banner grabbing. The hacker should have used nmap -O host.domain.com. The hacker failed to do banner grabbing as he didn’t get the version of the Apache web server.1. Which of the following is not usually implemented in the server-side code? a. Routing Code b. All of these are usually implemented in Server-Side Code c. Authentication Logic Code d. User Interface Code 2. True or False. The fetch method can only be used to make GET requests. a. True b. False 3. True or False. Node.js is a asynchronous event-driven framework. This means it can only handle one event at a time a.True b. False 4. When using the router level middleware in express, what must match for the Handler Method to be executed? a. None of these b. Path and URL c. Request and Response d. Method and Path
- Python language 1 - What modification(s) can you do to the code #1 and code #2 to make the server and client use the TCP Protocol?2 - Modify the server code to send an error to the client if the file requested does not exist.3 - Modify the server code to send an error to the client if the line requested does not exist.4 - Modify the client code to request the first line if the client didn't write a line number in their request. Example req = 'book2.txt'Tasks: Part A: Develop a UDP/IP server program in java that waits for clients to server. The server responds to the client with one of the following based on client’s request: Export secret key generated using KeyGenerator Export Text and Message Digest Export Text and Digital Signature Send original text for the encrypted text received from client Part B: Develop a UDP/IP client program that make request secret key, Message Digest, Digital Signature and original text by sending the encrypted text to server program developed (in Part A). This program will display the various objects received from server on its console.Explanation of how to implement native authentication and authorization services for gaining access to protected web server resources. Which of the following provides support for layered protocols? Provide concrete examples to support your assertions.

