Ш Imag 10 5 сл о -5 -10 -20 -15 -10 Real Ф -5 0 5
Q: How does agile's iterative and incremental approach connect to the system development lifecycle?
A: The answer to the question is given below:
Q: Calling demonstrates Network APIs' capabilities. (sockets)
A: Introduction Data structures and calls to subroutines that extend the functionality of pre-existing…
Q: Study how computer and mobile app users respond to issues. Provide customers advice on avoiding such…
A: THE FIX IS HERE Due to the portrait orientation of desktop computers, a tremendous quantity of…
Q: Talk about the different services that operating systems offer, as well as the three different…
A: operating system: The operating system is only an interface that offers functionality to the user…
Q: What is the concept of cloud computing in computer science, and how is it used to deliver on-demand…
A: Introduction: Computer technology refers to the tools, hardware, software, and infrastructure that…
Q: In as few words as possible, please explain what the noun "linker" refers to and its meaning.
A: Given: Provide a brief yet comprehensive explanation of the meaning of the word "linker."
Q: What is peer-to-peer communication in the OSIM?
A: Introduction Communication: "communication" refers to the exchange of data, information, or…
Q: Some why people may often switch off their computers or mobile devices. Differentiate sleeping from…
A: Introduction Sleep mode and hibernation are two power-saving options that are available on many…
Q: In this course, security management concepts are discussed.
A: It remains to be seen: Specify the fundamental ideas and principles of security management…
Q: Software development is frequently plan-driven and agile. This article discusses six factors that…
A: Given: Explain six factors that might help a software engineer choose between plan-driven and agile…
Q: Which of the following statements about debugging is NOT correct?: A -In some ways debugging is…
A: Debugging Finding and fixing errors or defects in the source code of any piece of software is the…
Q: Cloud advantages Cloud computing's risks? Cloud computing's pros against cons? Belief? Imagine:
A: According to the information given:- We have to define cloud advantages Cloud computing's risks?…
Q: Describe the three main testing steps for a commercial software system you've used in a few words.
A: Introduction :- It's a kind of software that's either for sale or used for commercial reasons, and…
Q: Understand social media. How is autonomous computing used in cloud computing? All instances show…
A: Social networking is the use of online social media to communicate with friends, family, and peers.…
Q: Why is data quality so crucial to data warehousing? List excellent data's advantages and…
A: Data quality: The term "data quality" refers to the process of evaluating the accuracy,…
Q: What safety issues must be addressed in a Parking management System (software) from coding to…
A: Please find the answer in next step
Q: What governance problems should be considered while switching from on-premise servers to IaaS?
A: With the introduction of cloud computing, many businesses are switching from on-premises servers to…
Q: How does "interdependence" differ from other system theory concepts?
A: In system theory, interdependence is a concept that refers to the mutual reliance and connection…
Q: Developers create web pages that request user data. How should data be submitted? Acquire, Publish,…
A: Introduction Web pages are documents that are designed to be viewed on a web browser and therefore…
Q: Agile system development has pros and cons.
A: The Agile technique is a method for managing projects by dividing them into phases. Constant…
Q: When you design the framework, consider all the obstacles and solutions. Cloud computing: a…
A: Introduction: Cloud computing is a modern technology with a reliable infrastructure that is…
Q: What is the concept of artificial intelligence in computer science, and how is it used to create…
A: Artificial intelligence (AI) is the simulation of human intelligence processes by machines,…
Q: Discuss CRISP-"Modeling" DM's phase's main tasks, activities, and outcomes. Explain.
A: How to Proceed The "Modeling" phase of the CRISP-DM methodology requires that we document the…
Q: What's the difference between symmetric and asymmetric key cryptography?
A: Symmetric and asymmetric key cryptography are two different methods of encryption used to secure…
Q: Explain computer cable kinds.
A: Analyzing the Issue: Coaxial, twisted, fibre, USB, series, parallel, and crossover cables are just…
Q: Distributed security systems (DSS) will continue on intranets and the Internet. Their user…
A: User interface (UI) design for Distributed Security Systems (DSS) should prioritize usability,…
Q: Why is memory management most efficient
A: Introduction Utilize repetition to commit information to memory. Repetition techniques include: The…
Q: Which kinds of systems are most amenable to being developed using an agile methodology
A: Agile methodology is a flexible approach to software development that emphasizes iterative and…
Q: sort function is missing
A: The Complete code is given below with output screenshot
Q: What distinguishes cloud-hosted IT security solutions from on-premises data center solutions
A: Introduction: When you often use cloud security, you don't need to spend money on specific gear or…
Q: CYMK is better for blown-up pictures than RGB
A: The CMYK (Cyan, Magenta, Yellow, and Key (black)) is the colour model that is used for printing…
Q: How does educational technology fit into our epidemic?
A: Introduction: Educational technology (EdTech) refers to the use of technology, such as digital tools…
Q: Wireless networks are fundamentally problematic. Explain how three of these problems influence…
A: Introduction: Due to their very nature, wireless networks present a number of obstacles that must be…
Q: Explain how a timer interrupt leads to a context switch.
A: Introduction: Maybe the virtual interrupt for the design of the working device is the "timer…
Q: What is the concept of operating systems in computer science, and how are they used to manage and…
A: Introduction: => In computer science, an operating system (OS) is a software program that…
Q: Students had to discuss three collaborative media formats. Accurate replies showed students…
A: Answer: We have discuss three collaborative media formats for the student . so we will see in the…
Q: When computers become more powerful, this happens. How may computers' importance in education be…
A: INTRODUCTION: Computers' impact has been felt ever since the first ones were built, but nowadays,…
Q: Consider this scenario: the manufacturer of online banking software has concealed a feature that…
A: We are going to investigate whether or if a person (the developer) has implemented a covert feature…
Q: Draw an NFA that accepts words from the alphabet {0,1} where the last character is not repeated…
A: Here is an NFA that accepts words from the alphabet {0,1} where the last character is not repeated…
Q: bubblesort.h is in second picture This is bublesort.c int compare(Entry a, Entry b) { // IMPLEMENT…
A: Bubble Sort in C is a sorting algorithm that works by repeatedly swapping the adjacent elements if…
Q: How should switches, routers, and cabling be secured?
A: According to the information given:- We have to define switches, routers, and cabling be secured.
Q: Example of Linux file permissions.
A: Provide an illustration of how to utilise the Linux file permissions system. In Linux, there are…
Q: Big data lets organizations track massive amounts of personal data. A corporation stores what data?…
A: Answer The term big data can be defined as large data sets that outgrow simple databases and data…
Q: How can Model-View-Controller Model-View-Controller? arrange web apps? Why use
A: Required: How exactly might Model-View-Controller help to organise web applications? What are the…
Q: What are the top three cryptography operations?
A: Cryptography involves various cryptographic operations used to secure digital data. Here are the top…
Q: After an interrupt service process, how does an application resume?
A: Interrupt Service Routine acronym. An ISR (an interrupt handler) is a software procedure triggered…
Q: As said, symmetric encryption has its applications, but asymmetric encryption techniques like public…
A: Introduction Symmetric encryption techniques rely on a single key for both encoding and decoding…
Q: Your math teacher has asked you to write a program that grades the multiple-choice questions in a…
A: Algorithm: 1. Define the correct answers as a list of strings. 2. Define the getInput function that…
Q: Hadoop offers tremendous redundancy. Its importance in hospital patient care is enhanced.
A: Introduction Hadoop is a highly redundant, open-source distributed computing platform used for data…
Q: Which Oracle 12c rights are available? Classify each.
A: Introduction The question relates to the Oracle 12c database management system, which is widely used…
Answer the given question with a proper explanation and step-by-step solution.
Please write the code in the software MATLAB to generate the image below.
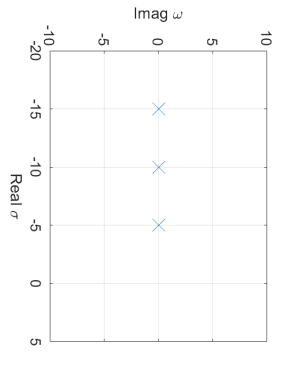
Step by step
Solved in 2 steps with 1 images


