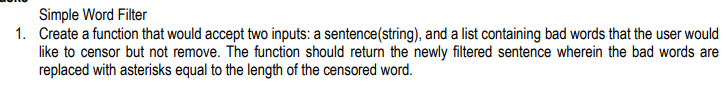
Simple Word Filter 1. Create a function that would accept two inputs: a sentence(string), and a list containing bad words that the user would like to censor but not remove. The function should return the newly filtered sentence wherein the bad words are replaced with asterisks equal to the length of the censored word.
Q: For linux: what would be the command to access or view the number of bytes in the file…
A: Lets see the solution in the next steps
Q: How have you taught web development to your community or a peer that has never heard of it before?
A: Introduction: For a community or a peer that has never heard of it before, We would approach the…
Q: es may be an excell
A: Social media are intuitive advanced channels that work with the creation and sharing of data,…
Q: 3. Express the other canonical form of the following boolean functions: a. F(x,y,z) = (0, 4, 5,7) b.…
A:
Q: rious types of DNS records. Each one should be thoroughly discussed, including examples of how and…
A: Introduction: The many kinds of DNS records are explained. Each of them will be briefly discussed,…
Q: Why is operation code a portion of machine level instruction that informs the central processor what…
A: Introduction: Operation code is the part of the machine-level instruction that tells the central…
Q: rating system, what is the relevanc
A: Introduction: The system partition is the disc partition that houses the system root, which is the…
Q: What are the potential repercussions of seeing human rights as just decorative moral aspects of…
A: What do we mean when we talk about human rights? In everyday life, human rights are nothing more…
Q: Describe the steps involved in software configuration management and distinguish between baseline…
A: Launch: Software configuration management (SCM) tracks changes to software. It involves…
Q: Which part of a device's hardware makes it possible for it to connect physically to a network?
A: Which part of a device's hardware makes it possible for it toconnect physically to a network?
Q: What are the repercussions that occur when the primary memory that is available is not distributed…
A: Operating systems also use multilevel paging schemes, making it take up more space to store the page…
Q: When describing processes that are not included in a systems analysis, it is a good idea to give…
A: Given: When describing processes that aren't part of a systems analysis, it's worth considering…
Q: Operating Systems Question 3 In your opinion, which of the potential drawbacks associated with using…
A: Introduction: As per our policy, "Since you have asked multiple questions, we will solve the first…
Q: Furthermore, the reasons why EDA may be more successful than hypothesis testing in data mining.
A: Introduction: An evaluation of a hypothesis would include a summary of the details of the study that…
Q: Provide samples of each kind of application software, and explain the differences between open…
A: Software for Applications: Application software is a sort of computer programme that performs a…
Q: Why are you concerned about social network privacy? How about describing a case study?
A: Many people throughout the globe have relied on social media for the last two decades. Humans'…
Q: When it comes to computers, architecture and organization based on the computer are two separate but…
A: Introduction: When it comes to computers, architecture and organization based on the computer are…
Q: This example might benefit from beginning with a database maintained by an airline that makes use of…
A: Consider a database system that employs snapshot isolation by an airline.
Q: When do you believe it would be appropriate to begin utilizing brouter on your network, based on…
A: introduction The above question is solved in step 2:- brouter is a network tool that works both as…
Q: What are the many applications and can you give examples?
A: Please find the different IoT applications in detail in the following steps. IoT Asset Tracking and…
Q: Linux is the only operating system that has all of the concurrent techniques that are being…
A: In software engineering, concurrency refers to techniques and processes that allow a computer to do…
Q: In the Linux operating system, what are the core responsibilities of the kernel?
A: Answer:
Q: In Exercises 15 to 22, (a) determine whether the graph is Eulerian. If it is, find an Euler circuit.…
A: Given graph contains, Vertices present in the graph= {A, B, C, D, E, F} That means it contains 6…
Q: If you have the time, could you go into further detail on how metrics are used in the software…
A: A software metric is a quantitative or quantifiable measurement of the qualities of a program.…
Q: Why did the original Linux developers choose to construct a non-preemptible kernel? What is the…
A: Given: Why did the initial Linux developers opt for a non-preemptible kernel? What is the advantage…
Q: If not the transport layer, then what makes it feasible for traffic on the Internet to go from one…
A: Given: To cater to the requirements of the many different application levels, there is a selection…
Q: What precisely is meant by the term "memory void"? How is it that this is even feasible, and how…
A: Given: Memory voids refer to any process that modifies or deletes unpleasant or humiliating…
Q: What do you call the parts of the operating system that are stored in the computer's memory? When…
A: In computing, reminiscence is a device or machine that is used to shop facts for fast use in a…
Q: Adhere to the following additional requirements: Each of the 6 classes will have exactly 2…
A: The following information has been provided for the question above: "Text format code" to copy and…
Q: In what ways does data independence come into play?
A: Intro In what ways does data independence come into play?
Q: DNS records, authoritative and root servers, and iterated and non-iterated requests are all covered…
A: Domain Name System (DNS) : The domain name system, or DNS, is the Internet's basic phone book.Humans…
Q: Question: Unit Converter Need HTML code a. cm to metre b. Metre to cm c. Metre to km d. Km to…
A: Find the required HTML code given as below and sample output :
Q: What are the responsibilities of an operating system when it comes to memory management?
A: Start: Memory management is a feature of operating systems that is responsible for managing the…
Q: Our LMS might be the target of a distributed denial-of-service (DDOS) attack. LMS is vulnerable to…
A: Intro DoS Attack: Denial-of-service (DoS) attacks target networks, websites, and online resources…
Q: What kinds of cultural and global political factors, such privacy rights, are taken into account…
A: Development: Data is pricey and every business's fuel. Today, data is shared abroad and used to make…
Q: Consider the following bayi Assign integers 9 to the nodes of the binary tree so that when you…
A: Tree traversal is also called tree search. It is a type of graph traversal that refers to most…
Q: What do you call the parts of the operating system that are stored in the computer's memory? How…
A: The solution is The kernel, which is computer software that resides at the centre of the operating…
Q: Why is there a limit placed on the number of iterations when using the waterfall This raises the…
A: The above question is solved in step 2:- Waterfall Model was the first Process Model to be…
Q: Try using Structured English to explain other kinds of processes, even if they have nothing to do…
A: Introduction:
Q: What are the four most significant qualities in software development? Consider the other four…
A: Launch: To jot down the four most significant traits Every software design is evaluated first and…
Q: How would you summarise the roles that each component plays if you were to list all of the…
A: Introduction: A Kernel is computer software that serves as the heart and soul of an operating…
Q: Please provide three compelling arguments as to why the spiral model is superior than the waterfall…
A: While in the spiral model, the customer is made aware of all the developments in software…
Q: Here, a concise synopsis of the two functions that are considered to be the most important aspects…
A: Operating System: This is the software that makes a computer work. An operating system is a…
Q: Is it feasible to describe all of the components that make up the kernel of a standard operating…
A: Given: Provide a one-sentence description of the role of each kernel component in a typical…
Q: Give at least three benefits that the Spiral model offers over the Waterfall technique. Compare and…
A: Given: The spiral model is one of the most prominent Software Development Life Cycle models for risk…
Q: What challenges does a design that utilises many threads bring to the table for an operating system?
A: INTRODUCTION: According to the provided facts, we must identify the primary barriers of the…
Q: What good is being bilingual if you're a systems analyst? In this situation, which organizations may…
A: Multilingualism gives you a significant competitive advantage in many workplaces. As the U.S.…
Q: What are some of the primary benefits associated with the abstraction of operating systems?
A: An operating system connects the user to the computer's hardware.
Q: What motivated the creation of Angular as a client-side framework?
A: Answer: Web developers utilized VanillaJS and jQuery to create dynamic webpages before the arrival…
Q: Identify errors/mistakes from the following PHP code segment. Rewrite the code segment with a…
A: The errors or mistakes given in the PHP code segment are corrected or fixed and comments for each…
Code in Python
Step by step
Solved in 2 steps with 1 images

- Write a function letter_count that accepts a string txt and returns a list containing the number of times that each letter of the alphabet occurs within txt. The returned list should contain the number of occurences of all twenty-six letters of the Latin alphabet, counting both upper and lower-case instances. For example, the string 'Abacus' contains two instances of the letter 'a', and so the first element of the returned list would be 2Given a list of integers, implement a function that returns a list of all the subsets of the input list, where each subset is represented as a list of integers.Write a function that takes a list removal(L), delete from it all the elements whose indicesare divisible by 3. And return the resulting list after removing unwanted elements.Example:>>>removal(['A', 'B', 'C', 'D', 'E'])['B', 'C','E'
- Create a function that takes each value of the averaged sequence and passes itthrough the mathematical function if x (the averaged value) is not equal to 5 andreturns 0 if x is equal to 5. These values are returned into a new list. f(x) = 1/x-5Implement a function findMixedCase in Python that: accepts a single argument, a list of words, and returns the index of the first mixed case word in the list, if one exists, (a word is mixed case if it contains both upper and lower case letters), and returns -1 if the all words are either upper or lower case. sample: >> findMixedCase( ['Hello','how','are','you'] ) # 'Hello' is mixed case0Complete the examples in the docstring and then write the body of thefollowing function:def same_first_last(L):""" (list) -> boolPrecondition: len(L) >= 2Return True if and only if first item of the list is the same as thelast.>>> same_first_last([3, 4, 2, 8, 3])True>>> same_first_last(['apple', 'banana', 'pear'])>>> same_first_last([4.0, 4.5])"""
- Using Swift programming language, write a function filter that takes a predicate and a list as arguments and returns a list of only those elements that satisfy the predicate. Example: (filter odd? '(1 2 3 4 5 6 7 8 9)) ==> (1 3 5 7 9) Please include a screenshot of the source code and output. Thank you!!Write a function (Ocaml) that takes an ’a list and an int list of values and returns second list, with its integers values replaced by the values from the first vector at the position specified by the integer (indexing starts with 0). Large and negative numbers are to be skipped.Write a function REMOVE-NUM that takes a list and returns a list consisting of the original list with all numeric atoms removed. Examples: (REMOVE-NUM '(2 A 6 B 1 C 7 D)) returns the list (A B C D) (REMOVE-NUM '(3 A 4 B (1 E) 7 D)) returns the list (A B (E) D)
- Suppose we have a singly linked list implemented with the structure below and a function that takes in the head of the list.typedef struct node{int num;struct node* next;} node;int whatDoesItDo (node * head){struct node * current = head;struct node * other, *temp;if (current == NULL)return head;other = current->next;if (other == NULL)return head;other = other->next;temp = current->next;current->next = other->next;current = other->next;if (current == NULL){head->next = temp;return head;}other->next = current->next;current->next = temp;return head;}If we call whatDoesItDo(head) on the following list, show the list after the function has finished.head -> 1 -> 2 -> 3 -> 4 -> 5 -> 6 -> 7Write a function removeN which takes three arguments called N, E and L (where L is a list) and returns a list equal to L but with the first N occurrences of E in that list removed. Note: only first N occurrences of E must be removed, not all occurrences! If there are less than N occurrences of E in the list, then all occurrences of E should be removed. Using scheme language Test Result (removeN 2 'a '(a b a c a d a)) (b c a d a) (removeN 4 'a '(a b a c a d a)) (b c d)Write a function sum67 that takes a list as an input parameter and returns the sum of the numbers in the list, except ignore sections of numbers starting with a 6 and extending to the next 7 (every 6 will be followed by at least one 7). Return 0 for no numbers.

