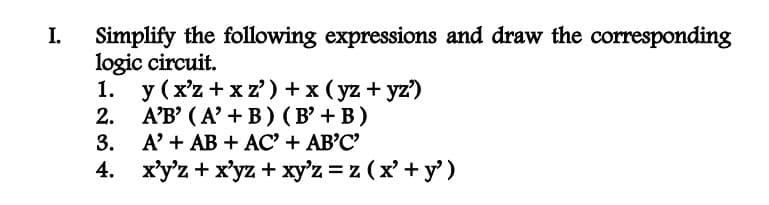
Simplify the following expressions and draw the corresponding logic circuit. 1. y (x'z+xz') + x (yz+yz')
Q: The following are the most regularly used internet protocols. To employ security successfully, it is…
A: Introduction: The Web is an Internet resource. They're Internet connection protocols. You can use…
Q: Reusable program components include dates, times, audio, and video.
A: Components that may be reused can be anything connected with software, such as requirements…
Q: Why is it vital to get familiar with the characteristics of the sigma notation?
A: Sigma notation is used to denote the sum of expression mentioned. It is denoted by ∑.
Q: A virus scanner, a file compression tool, or a data backup utility are all instances of software…
A: Question-wise Software programme is a collection of instructions for computer hardware. System and…
Q: Identify any three protocols that are unsecured or vulnerable to attack while considering the…
A: Three Protocol vulnerable to attacks are given below:
Q: Reusable program components include dates, times, audio, and video.
A: Introduction: A software is created by combining several software components.
Q: Algorithm for ROLA(Server-side Data Structures)
A: Algorithm for ROLA(Server-side Data Structures) :-
Q: Assume you have access to the DNS caches of your department's DNS servers. How would you go about…
A: Introduction: Local DNS cache may be accessed. This is the department's server. Local DNS cache is…
Q: Structured English may be used to explain processes in disciplines other than systems analysis.
A:
Q: 7. using c++, If c is a character (e.g. char c = ‘a’), then (int) c is a number between 0 and 255…
A: To determine whether (int) c1 is greater than (int) c2, and then returns the sum of the ascii values…
Q: Operating systems may be differentiated from one another in a variety of ways.
A: 1. MS-DOS: Microsoft Disk Operating System, or MS-DOS for short, is a text-only OS for IBM PCs using…
Q: function
A: Dear Student, The annotated code is being provided below -
Q: Which of the following measures are Null-Invariant. For the ones that are not null invariant,…
A: If we are computing the correlation between coffee (c) and milk (m), a null-invariant it is the…
Q: Because network speed is so important to the users of the company, identify three protocols that are…
A: Network attacks are illegal operations on digital resources connected to a corporate network.…
Q: You must know how to identify whether you have selected a RadioButton or a CheckBox control in…
A: According to the information given:- We have to define the whether you have selected a RadioButton…
Q: playoffs season! In this exercise, let's utilize dictionaries to see if we can model and learn more…
A: We need to write a Python code for the given scenario.
Q: What is the internet's role in the development of a global information network? Is it a good idea to…
A: In this question we need to explain the role of Internet on development of global information…
Q: how to build a for statement in AST using java parser?
A: The solution is given in the next step
Q: Examine the development of the internet and its technological roots.
A: Introduction: A worldwide computer network that uses standardized communication protocols to connect…
Q: As a university network administrator, you must choose an appropriate NAT approach. Make an attempt…
A: An organization's designated person in charge of administering computer infrastructures, mostly…
Q: Internet users have access to two types of services on the Internet. Describe the distinct traits…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: A virus scanner, a file compression tool, or a data backup utility are all instances of software…
A: Question-wise Software programme is a collection of instructions for computer hardware. System and…
Q: list the tcp/ip protocol suite layer that preforms each of the following: end to end flow control
A: Open System Interconnection(OSI) model is used to standardize how a computing or telecommunication…
Q: When and what software are in charge of creating a file extension? Give specific instances of what…
A: Introduction: There are several file types on your computer, each with its own file extension.
Q: A software development lifecycle's components may be found all over the place. Which stage of the…
A: Introduction: The Software Development Life Cycle (SDLC) is an organized procedure for producing…
Q: Choose the right answer from the list below. When we say "utilities," we mean things like word…
A: Introduction: Infrastructure software is used to manage the computer infrastructure, as opposed to…
Q: Provide the SQL to amend the original table design to allow for this change in requirement. It is…
A: Answer- The above is the code given in particular manner so that it sequence Providing the SQL to…
Q: List the TCP/IP protocol suite layer that performs each of the following functions: a. data…
A: Hello student The answer will be in next step
Q: As a university network administrator, you must choose an appropriate NAT approach. Make an attempt…
A: Introduction: An organization's designated person in charge of administering computer…
Q: Using c++, ) What input must be provided to this “ double Nested For Sum” fragment for it to display…
A: Answers:- input must be provided is 3 output is 48
Q: This article focuses on file extensions and the software that generate them. It is critical to have…
A: Introduction: Explanation of File Extensions: File extensions are used by computers to detect the…
Q: Describe shell globbing with an example. Describe the shell globbing characters with an example…
A: Unlike some standard programming language , shell doesn't support native regular expressions. So,…
Q: This article focuses on file extensions and the software that generate them. It is critical to have…
A: A file extension, often known as a file name extension, is the last component of a file name that…
Q: Suppose the web page you are working on contains one file input control with the id sourceText. What…
A: var text = document.getElementById("sourceText").files[0]; This code assigns the first file chosen…
Q: Question 3 CCC Complete scince how do you build an API that runs a Bash script? could you provide…
A: Python is the regarded as one of the most well-liked programming languages in the domains of coding…
Q: Is it still necessary to backup an Oracle database to RAID-capable storage? Typing rather than…
A: In this day and age, storage devices that are capable of RAID do not need Oracle database backups.…
Q: SOA (Service-Oriented Architecture) vs. Web Services (Web Services).
A: There are several significant distinctions between Web services and SOA. Web services are a kind of…
Q: From table 1, assuming the min confidence is 35%, and minsup is 37%, which of the following rules…
A: The following criteria from Table 1 are strong, given that min confidence is 35% and minsup is 37%:…
Q: First, when you hear the phrase "verification and validation model," what model comes to mind?
A: The above question is solved in step 2 :-
Q: ONLY IF STATEMENTS ALLOWED!!!! NO RANGE FUNCTION, NO SETS, NO LISTS, NO LOOPS, ETC Angela loves…
A: Here is your solution:
Q: SOA (Service-Oriented Architecture) vs. Web Services (Web Services).
A: Introduction: Most companies have long-term investments in infrastructure. Such projects save a lot…
Q: eal life world problem about quotient of functions on operation.
A: Solution- Function operations: plus, minus, multiply, and divide We have the abilities to multiply,…
Q: Is it still necessary to backup an Oracle database to RAID-capable storage? Typing rather than…
A: A recording media and computer components make up the technology known as computer data storage,…
Q: the second question
A: What Is the Meaning of TCP/IP (Transmission Control Protocol/Internet Protocol)? The language a…
Q: Is it still necessary to backup an Oracle database if RAID storage devices are used? Typing rather…
A: SOLUTION: Low-Cost Redundant Array is referred to as RAID. RAID is a practical approach to combine…
Q: What are the differences between on-premises data center IT security solutions and cloud…
A: Introduction: One important distinction between cloud computing and on-premises software is that it…
Q: Given the significance of the network to the organization's daily activities, identify any three…
A: Network is basically collection of computers,machines,etc. Protocol is basically set of rules.
Q: Primitive types are reference types. O True O False
A: Introduction Datatype: A variable's data type and the forms of mathematical, relational, &…
Q: Defining a system model seems to be a good aim, but what exactly does it entail? What factors should…
A: Model: System model has many uses, meanings, and disciplines. Model-based systems engineering aims…
Q: dentify any three protocols that are susceptible or prone to attack if he organization's users rely…
A: Introduction The following are examples of protocols: 1) Address Resolution Protocol (also known…
Step by step
Solved in 4 steps with 3 images

- (Mechanics) The deflection at any point along the centerline of a cantilevered beam, such as the one used for a balcony (see Figure 5.15), when a load is distributed evenly along the beam is given by this formula: d=wx224EI(x2+6l24lx) d is the deflection at location x (ft). xisthedistancefromthesecuredend( ft).wistheweightplacedattheendofthebeam( lbs/ft).listhebeamlength( ft). Eisthemodulesofelasticity( lbs/f t 2 ).Iisthesecondmomentofinertia( f t 4 ). For the beam shown in Figure 5.15, the second moment of inertia is determined as follows: l=bh312 b is the beam’s base. h is the beam’s height. Using these formulas, write, compile, and run a C++ program that determines and displays a table of the deflection for a cantilevered pine beam at half-foot increments along its length, using the following data: w=200lbs/ftl=3ftE=187.2106lb/ft2b=.2fth=.3ft1.) If f(x) = 2.x^2 - x + 5. What is f(-3)? 2.) If A = {a, b, d, e}, B = {b, c, e, f} and C = {d, e, f, g}. What is (A ∩ B) ∪ (A ∩ C)?2) Simplify the following Boolean expressions, using three-variable K-maps:F(x,y,z) = x′y′ + yz + x′yz′ PS:Please type instead of paper writing
- Please help with all of them and show work please Simplify the following expressions F(x, y, z) = xy + x’y’z’ + x’yz’ F(x, y, z) = x’yz + xy’z + x’yz’ F(x, y, z) = xy’z’ + xz + x’y’z F(w, x, y, z) =x’z + w’xy’ + w(x’y + xy’) F(w, x, y, z) =w’x’y’z’ + wy’z’ + x’yz’ + w’xyz + xy’z2. Given a boolean expression below, find the value of the expression if the values of P = 1, Q = 0, R = 1. Y = P.Q + Q.(R+P+Q)2. Look for the dual of the following Boolean expressions:a. xyz + x'y'z'b. xz' + x⋅0 +x'⋅1
- Write the robot program using the VAL+ for the following automation case. First draw the problem; then handwrite the VAL+ code. The robot picks up FIVE blocks of size 100x100x100 mm that are stacked at a fixed position and place them at the corners and center of a square table of size 500 x 500 mm. Select the original position on the table on your own.write a c++ program that creates all 4-digit combinations from 1 - 7 for example, the first combination should be 1 2 3 4... but instead of numbers, the output should be letters. for 1 = a, 2 = b, 3 = c, 4 = d, 5 = e, 6 = f, 7 = g and the output for 1 2 3 4 should be a b c d the output for 2 3 4 5 should be b c d e42. Consider the expression given below. The value of X is:X = 2+9*((3*12)-8)/10 a. 30.0 b. 30.8 c. 28.4 d. 27.2
- Keep the Diagram neat. Thanks. Implement the following boolean function using a) 16:1 mux b) 8:1 mux c) 4:1 mux F(A,B,C,D) =∑(0,1,2,7,8,10,11,13, 15)What is the output from the following print statement: print (1 / 3) print (10 + 3 * 7) print ((10 + 3) * 7) print ("Hi" + "there") print ("Hi" + 10) print ("Hi" + "10") Does e and f display the same result? Why? print ("Hi" * 10) print ("Hi" * "10") Does h and i display the same result? Why?1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as: 3)convert the following decimal fractions to binary with a maximum of six places to the right of the binary point: 1)25.84375 2)57.55 3)80.9065 4) Convert the following binary fractions to decimal: 1)100001.111 2)111111.10011 3)1001100.1011 5) Fill in the blank. The representation of 60 in binary using 8-bit signed magnitude is ______, in ones complement is ______, in two’s complement is ______, and in excess-127 is ______.



