Small store dashboard. Store Sales Departments Jan Feb march April May June $1,800 Grocery meat $1,700 $4,650 $1,700 $1,990 $2,000 $1,150 $2,050 $1,100 $1,200 $1,120 $920 Produce $1,500 $1,200 $1,800 $1,720 $1,600 $1,130 $880 $1,020 $790 $800 $8170 81,090 Bakery Deli Clothing $1,700 $1,710 $9.00 $1,300 $1,000 $900 $1,100 $1,010 $1,200 $1,070 $1,150 $1,180 Pharmacy $1,730 $1,800 $1,120 $1,700 $1,960 $1,220 Gm $1,200 $1,900 $1,250 $1,900 $1,600 86700
Small store dashboard. Store Sales Departments Jan Feb march April May June $1,800 Grocery meat $1,700 $4,650 $1,700 $1,990 $2,000 $1,150 $2,050 $1,100 $1,200 $1,120 $920 Produce $1,500 $1,200 $1,800 $1,720 $1,600 $1,130 $880 $1,020 $790 $800 $8170 81,090 Bakery Deli Clothing $1,700 $1,710 $9.00 $1,300 $1,000 $900 $1,100 $1,010 $1,200 $1,070 $1,150 $1,180 Pharmacy $1,730 $1,800 $1,120 $1,700 $1,960 $1,220 Gm $1,200 $1,900 $1,250 $1,900 $1,600 86700
Fundamentals of Information Systems
8th Edition
ISBN:9781305082168
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter2: Hardware And Software
Section: Chapter Questions
Problem 1PSE
Related questions
Question
Develop the dashboard below and create graphs
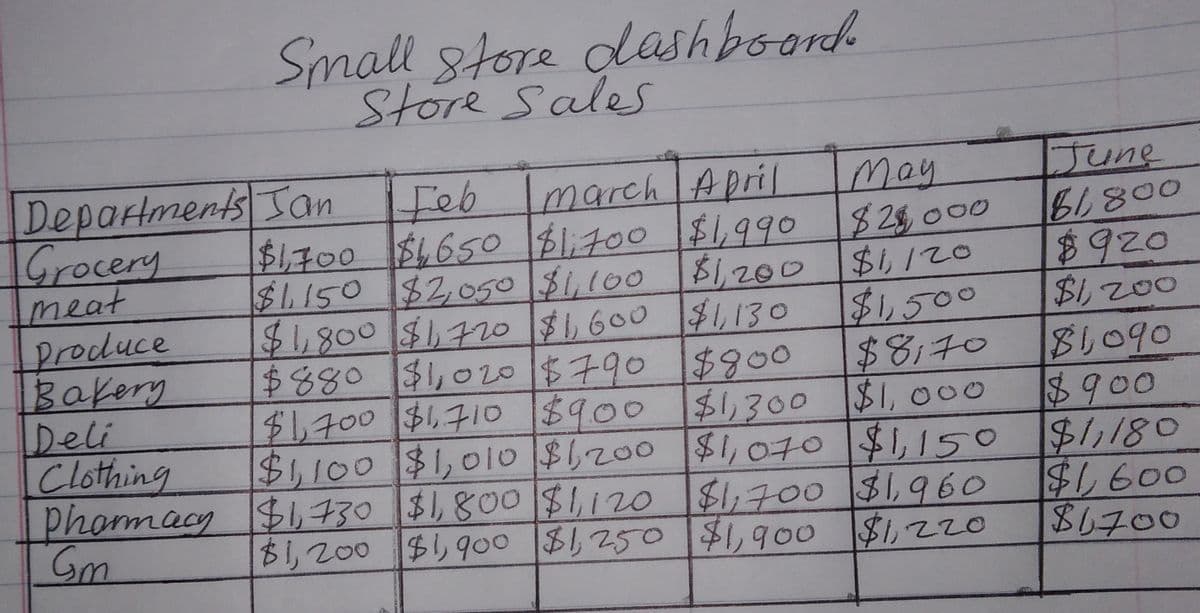
Transcribed Image Text:Small store dashboard.
Store Sales
Departments
Jan
Feb march April
May
Grocery
meat
$28,000
$1,200 $1,120
Produce
$1,500
Bakery
Deli
$1,700 $1,650 $1,700 $1,990
$1,150 $2,050 $1,100 $1,200
$1,800 $1,720 $1,600 $1,130
$880 $1,020 $790 $800
$1,700 $1,710 $9.00 $1,300 $1,000
Clothing $1,100 $1,010 $1,200 $1,070 $1,150
Pharmacy $1,730 $1,800 $1,120 $1,700 $1,960
$1,900 $1,220
Gm
$8,70
$1,200 $1,900 $1,250 $1,900
June
81,800
$920
$1,200
$1,090
$900
$1,180
$1,600
$1700
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781305082168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781285867168
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning