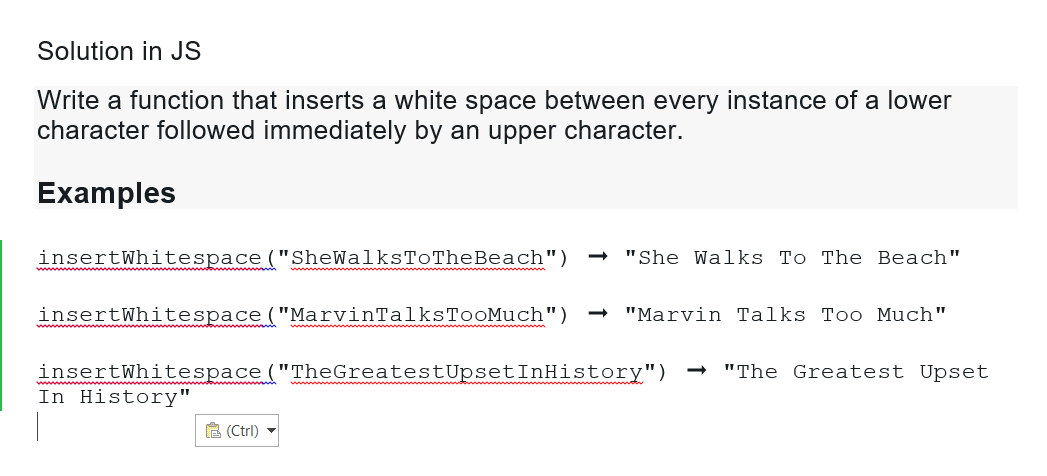
Solution in JS Write a function that inserts a white space between every instance of a lower character followed immediately by an upper character. Examples insertWhitespace ("SheWalksToTheBeach") "She Walks To The Beach" insertWhitespace ("MarvinTalksTooMuch") → "Marvin Talks Too Much" insertWhitespace ("TheGreatest Upset InHistory") "The Greatest Upset In History" (Ctrl)
Q: Code a JavaScript function that simulates the Math.pow() method, or the exponent (**) operator,…
A: 1) Below is JavaScript program that defines function that simulates the Math.pow() method, or the…
Q: Would you mind writing 350–500 words describing the benefits of NLP (Natural Language Processing)…
A: Start: However, we can assess financial documents like 10-k forms and forecast market moves using…
Q: 9.Write the CSS style rule to display an image that is fixed in position and is placed at 125 pixels…
A: The answer is given in the below step
Q: AT ARE THE BENEFITS OF USING CRYPTOCURRENCY IN RE
A: Introduction: Below describe the benefits of USING CRYPTOCURRENCY IN REAL LIFE Transactional…
Q: Are the preventive procedures sufficient to ensure the safety of the information system?…
A: Information security: Information security is much more than preventing unwanted access to data.…
Q: Data visualization techniques have often increased our comprehension of phenomena: consider the…
A: The question has been answered in step2
Q: Why should system calls be avoided in favor of APIs?
A: The set of protocols, functions and the routines that allow the exchange of the data among the…
Q: Is it possible to use autonomous computing to boost cloud computing efficiency?
A: Autonomic computing: Is a PC's ability to manage itself automatically using flexible improvements…
Q: Defend the benefits of cloud computing. Check to see if there are any risks associated with this…
A: Cloud computing is a method of remotely delivering computer services over the internet rather than…
Q: Describe why, given a heap data structure, the trickle down algorithm takes more operations than the…
A: A heap is a binary tree with the qualities listed below: It is always exhaustive. This indicates…
Q: Which group of software applications is in charge of monitoring the internal operation of the…
A: In this question we need to find out which software monitors the internal operation of the…
Q: List the similarities and differences between smartphones, PDAs, and portable media players and…
A: A smartphone is a cell phone with an operating system and more sophisticated networking and…
Q: What are the advantages of using CUDA and graphics processing units (GPUs) for computing?
A: CUDA & GPU:
Q: What really happens when nonfunctional needs aren't fulfilled? So what makes you believe that this…
A: There are many Consequences of not fulfilling non-functional needs in computers.
Q: Your father made the decision to start a software development company and made a start-up investment…
A: The following are the many kinds of network topology: Topology of StarsTopology of BusesTopology of…
Q: What advantages do client-server architectures offer over peer-to-peer systems?
A: This question comes from Networking which is a paper of computer science. Let's discuss it in the…
Q: Name three different ways to strike a line through text. E.g. LINE OF TEXT.
A: There are two ways you can strikethrough text in Microsoft Word. Neither one is better nor worse, it…
Q: Text files and image files are the two main categories into which files are categorized. Which of…
A: Introduction: To hold data, files are classified into two types: text files and binary files. Text…
Q: How are the encoding schemes of ASCII and Unicode different
A: How are the encoding schemes of ASCII and Unicode different?
Q: What do you think are the most significant benefits of arrays? This is the maximum number of…
A: Arrays will store the similar type of elements in adjacent locations. we uses indexes to access the…
Q: How much memory is required to store a single letter of the alphabet or a single tiny number?
A: Memory: Memory is the storage space where the data to be processed are stored. Memory is divided…
Q: 2.Name and describe three HTML tags used in creating a drop-down list.
A: The three HTML tags used in creating a drop-down list are: select option optgroup
Q: What methods may be utilized to improve email correspondence? Please provide detailed instances.
A: E-mail (Electronic mail) is a computer-based program that allows users to communicate with one…
Q: You struggle as a computer manufacturer to provide high-caliber devices with quick processing rates…
A: Definition: The number of cycles/seconds that a central processor performs is known as processing…
Q: When creating a thorough information security plan for your management information system (MIS), how…
A: MIS (Management Information System):- It is a PC based framework that makes data accessible to…
Q: Comment briefly on cyclomatic complexity.
A: 1) Cyclomatic complexity is a software metric used to measure the complexity of a program. 2) It was…
Q: What is dynamic scoping, and how ought one to use it? What performance effects does dynamic scoping…
A: Global identifiers, which are rare in current languages, are used when the scope is dynamic and link…
Q: a mining? How are th
A: Data warehouse: In computing, a data warehouse (DW or DWH), otherwise called an undertaking data…
Q: What is the major drawback of a write lock?
A: Write Locks: When a row or table has a write lock, it cannot be read by another thread if it has a…
Q: What distinguishes the ARM and Core i3 architectures most significantly? ARM:
A: Introduction: ARM: Advanced RISC Machines (ARM) is a family of older 32-bit processor cores mainly…
Q: Send us your thoughts on how to use ICT (information and communications technology) in the classroom…
A: When teachers are computer savvy and know how to incorporate ICT into the curriculum, ICT can impact…
Q: What protocol, if any, is used to protect communication between a web browser and a web server,…
A: Protocols are used for communication between a web browser and web server.
Q: What underpins systems analysis fundamentally?
A: Analysis of systems refers to the process of observing systems to solve problems or further develop…
Q: A supernet has first address of 205.16.32.0 and a supernet mask of 255.255.248.0. Prove that the…
A: Default Mask: 255 255 255 0 11111111 11111111 11111111 00000000
Q: The creation of public key cryptography was driven by the need to address two fundamental issues,…
A: Public key Cryptography: A public key pair (also known as a public key pair) is used in public key…
Q: The malevolent hacker must download malware that turns unprotected machines into zombies in order to…
A: DDoS (distributed denial-of-service): DDoS is a type of cyber-attack that causes a slowdown of a…
Q: Consider applying the variable elimination algorithm to the umbrella DBN unrolled for three slices,…
A:
Q: What are the differences between parallel/distributed databases and centralized databases in terms…
A: Definition: A distributed database is a word used to refer to a collection of data that is kept…
Q: How are the encoding schemes of ASCII and Unicode different?
A: ASCII and Unicode are two different ways to represent text.
Q: Give instances and talk about how the Internet of Things (IoT) is affecting business, with an…
A: Given: Give instances and talk about how the Internet of Things (IoT) is affecting business, with an…
Q: Implementations of ERP must take care of infrastructure. Describe the selection and installation…
A: The acronym ERP stands for - "enterprise resource planning." ERP implementation is analyzing the…
Q: What advantages do client-server architectures offer over peer-to-peer systems?
A: A peer-to-peer system is a computer network that allows peers to share network resources, processing…
Q: Take a project into consideration and map it both with and without architecture. how it will impact…
A: Take a project of software development in this project first we will consider the development of…
Q: How are the encoding schemes of ASCII and Unicode different?
A:
Q: A GSM system uses 124 channels and each channel is divided into 8 time slots. What is the maximum…
A: The answer is
Q: Memory addresses come in two different varieties. Instead of storing all the data in memory, why not…
A: The CPU has a strong relationship: With primary storage, often known as main memory, and refers to…
Q: Describe three situations where a real-time operating system may be beneficial.
A: An operating system is the program that, after being initially loaded into the computer by a boot…
Q: Why are thin clients different from fat clients?
A: A software that runs locally and makes a service request to the server is referred to as a client.…
Q: What separates an output device from a dot-matrix printer?
A: Output Device: It is an electromechanical apparatus that transforms data from a computer into a form…
Q: What distinguishes the ARM and Core i3 architectures most significantly? ARM:
A:
Step by step
Solved in 2 steps with 1 images

- A. What does the following JavaScript code do?let titles = "Mr.|Mrs.|Miss|Ms.|Dr.";let spotTitle = new RegExp(titles, "g"); a. creates a text string and stores it in the variablespotTitle b. defines a regular expression with a global flag by creating an object constructor c. defines a function to search for the substrings"Mr.","Mrs.","Miss","Ms.", and"Dr." d. throws an error because it attempts to enclose a regular expression in quotation marks instead of forward slashes B. Which of the following regular expressions will match both the substring "cat" (part of the word “catering”) and the substring "Cat" in the string "For your catering needs, call Cat!"? a. /cat/ig b. /cat/g c. /cat/ d. / cat /hen a function returns an anonymously constructed object from the return expression the compiler can make more efficient code — by eliding the copy construction of the return value — using the ____. Select an answer and submit. For keyboard navigation, use the up/down arrow keys to select an answer. a. return by object optimization b. returned value optimization c. object optimization procedure d. retro-viral organism e. retro-active functional optimizationQ3: Write a program in € using OOP to create a class (A) . that contain integer number (), contain the function (FACT) to calculate the factorial of (x!) and create a class (B) . that contain integer number (). contain the functions (POWER), to calculate ( x7). Then creat class ()., with public visibility mode inherit from class (A) . and public visibility mode inherit from cla s (B), contain the fimction that find (x!/ x°)
- Programming Language: C Write the following three functions: a) The function gets an array A of length n of ints, and a boolean predicate pred. It returns the smallest index i such that pred(A[i])==true. If no such element is not found, the function returns -1. int find(int* A, int n, bool (*pred)(int)); b) The function gets an array A of length n of ints, and a function f. It applies f to each element of A. void map(int* A, int n, int (*f)(int)); c) The function gets an array A of length n of ints, and a function f. The function f gets 2 ints and works as follows: 1. Start with accumulator = A[0] 2. For i=1...length-1 compute accumulator=f(accumulator, A[i]) 3. Return accumulator For example, if f computes the sum of the two inputs, then reduce() will compute the sum of the entire array. int reduce(int* A, int n, int (*f)(int,int)); Test for the functions: // used for test Q3-find bool is_even(int x) { return x%2 == 0; } bool is_positive(int x) { return x>0; } void…a. Extend the definition of the class newString as follows:i. Overload the operators + and += to perform the string concatenation operations.ii. Add the function length to return the length of the string.b. Write the definition of the function to implement the operations defined in part a.c. Write a test program to test various operations on the newString objects.Q3: Write a program in C++ using OOP to create a class (A) , that contain integer number(x) , contain the iilnction (FACT) to calculate the factorial of (x!)and create a class (B) , that contain integer number (n ) , contain the functions (POWER),to calculate ( .xü).-Illen create a Class (C) , with public visibility mode inherit from class (A)and public visibility mode inherit from class (B),contain the tunction that find
- Q3: Write a program in C++ using OOP to create a class (A), that have a two dimensional array X[5][5], and function (input) to read it from keyboard Then create a class(B), with public visibility mode inherit from class (A), contain the function (sample_T) to print the element that form the letter (T)in array (X). Then create a class(C), with public visibility mode inherit from class (A), contain the function (sample L.) to print the element that form the letter (L) in array (X). Then create a class(D), with public visibility mode inherit from class (B) and (C), contain the function (RUN) to call the to function above.Question: Implement the following functions in your class: getTotalWords (returns the amount of total words), getUniqueWords (returns the amount of unique words), getMostUsedWord, (returns the word that is most used) getMaxOccurrence (returns how many times the most used word occured). Name them as indicated here. The code to add the functions to: import edu.princeton.cs.algs4.*;import edu.princeton.cs.algs4.LinearProbingHashST;import edu.princeton.cs.algs4.SeparateChainingHashST;import edu.princeton.cs.algs4.ST;import edu.princeton.cs.algs4.SequentialSearchST;import edu.princeton.cs.algs4.In;import edu.princeton.cs.algs4.StdOut; public class TestPerf { public static long LinearProbingHashST(String x[]) { LinearProbingHashST<String, Integer> st = new LinearProbingHashST<String, Integer>(); long start = System.currentTimeMillis(); for(int i = 0; i < x.length; i++){ String key = x[i]; if…Write a class basicMaths and use constructor to pass a number. Create a function FindNumber takes one number as a parameter and Ñnds if it is positive or negatieve number. Create another class intermediateMaths with same functions and redeÑne the FindNumber functionality by Ñnding the number as even or odd number. Create another class advanceMaths with same functions and redeÑne the FindNumber functionality by Ñnd the number as prime number or composite number. Consider the following example code for the logic of prime number:
- in c++ 1. Write a function that takes a 1 Dimensional array and an integer n andreturns the number of times ‘n’ appears in the array. If ‘n’ does not appearin the array, return -1.2. Write a function that takes a 2 Dimensional array and returns the positionof the first row with an odd sum. Assume that the column size is fixed at 4.If no sum is odd, return -13. Write a class, “pie”, that has a number of slices (int slices) as a privateproperty. Construct the pie with a number of slices and remove a slice witha function. Tell the user how many slices are in the pie.Write the following three functions: a) The function gets an array A of length n of ints, and a boolean predicate pred. It returns the smallest index i such that pred(A[i])==true.If no such element is not found, the function returns -1.int find(int* A, int n, bool (*pred)(int)); b) The function gets an array A of length n of ints, and a function f. It applies f to each element of A.void map(int* A, int n, int (*f)(int)); c) The function gets an array A of length n of ints, and a function f. The function f gets 2 ints and works as follows: Start with accumulator = A[0] For i=1...length-1 compute accumulator=f(accumulator, A[i]) Return accumulator For example, if f computes the sum of the two inputs, then reduce() will compute the sum of the entire array.int reduce(int* A, int n, int (*f)(int,int));Need Help fixing my code!! only under TODO's. // Util function to convert a FoodWastageReport class object into a serialized// JSON object.crow::json::wvalue FoodWastageReportToCrowJSON( const FoodWastageReport &report) { crow::json::wvalue report_json({}); std::vector<std::string> most_common_disposal_mechanisms{}; // TODO 1: Call the member function of FoodWastageReport class that returns // all the most common disposal mechanisms as a vector of strings. Store the // result in the vector declared above. FoodWastageReport report; std::vector<std::string> most_common_disposal_mechanisms = report.MostCommonDisposalMechanisms(); report_json["most_common_disposal_mechanism_"] = most_common_disposal_mechanisms; std::vector<std::string> most_commonly_wasted_foods{}; // TODO 2: Call the member function of FoodWastageReport class that returns // all the most commonly wasted foods as a vector of strings. Store the result // in the vector declared…

