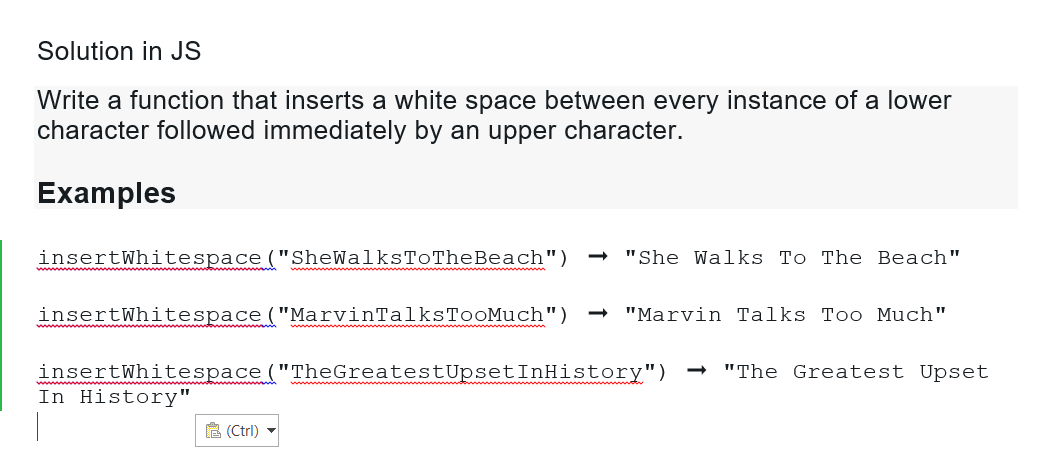
Solution in JS Write a function that inserts a white space between every instance of a lower character followed immediately by an upper character. Examples insertWhitespace ("SheWalksToTheBeach") insertWhitespace ("MarvinTalksTooMuch") "She Walks To The Beach" (Ctrl) "Marvin Talks Too Much" insertWhitespace ("The GreatestUpset InHistory") In History" "The Greatest Upset
Q: What kind of transactions can the device accommodate?
A: Typically, a transaction is a sequence of information exchange and related activities (such as…
Q: You struggle as a computer manufacturer to provide high-caliber devices with quick processing rates…
A: High-Caliber : 1Of a high standard; high caliber; (of a person) very competent; extremely…
Q: Describe why, given a heap data structure, the trickle down algorithm takes more operations than the…
A: A heap is a binary tree with the qualities listed below: It is always exhaustive. This indicates…
Q: The creation of public key cryptography was driven by the need to address two fundamental issues,…
A: Public key Cryptography: A public key pair (also known as a public key pair) is used in public key…
Q: It is better to have a computer with logical divisions and subsystems than one without.
A: Simple to decay the framework dependent on ordered progression refinement Can be utilized in a…
Q: QUESTION 6 Suppose that there are THREE free page frames named as 1, 2, 3 and FIVE virtual pages…
A: The Answer is :-
Q: in the next 10-20 years, express your prediction of data science. it can be in the field of…
A: Data Science will have a huge impact on business and society in the next 10-20 years. It will change…
Q: Successful ICT exploitation often requires data collecting from throughout the organization.…
A: According to the information given:- We have to define that successful ICT exploitation often…
Q: How are the encoding schemes of ASCII and Unicode different?
A:
Q: What protocol, if any, is used to protect communication between a web browser and a web server,…
A: The protection is very important between a web browser and web server. Because the web server access…
Q: The CPU enters values into memory locations, and certain registers are utilized to store both the…
A: CPU enters values into memory: Data exchange between the CPU and RAM Memory Data Register (MDR) and…
Q: Why is a good knowledge of Boolean algebra essential for computer scientists?
A: Boolean algebra is a form of mathematics that deals with statements and their Boolean values.
Q: he most effective use of error correction is in wireless applications. Do you concur or disagree…
A: Introduction: Error repair is the process of discovering errors in previously broadcast messages and…
Q: How are the encoding schemes of ASCII and Unicode different?
A: ASCII is a subset of Unicode encoding scheme.
Q: 2. Consider the following network address: a. How many subnets are there in this network? b. What…
A: The specified network address is 209.15.6.0/28. This means that after this host ID there is a in…
Q: The creation of public key cryptography was driven by the need to address two fundamental issues,…
A: The method of encryption known as public key cryptography requires using two separate keys, one of…
Q: Instructions: Test each function with a sample output A. The following code in the function…
A: 1) Below is updated is prime function with test code which corrects the is_prime function given in…
Q: Name the top five essential parts of a computer system.
A: The parts of a computer system are the most important components to understand, as they are the…
Q: How has technology changed the way we communicate?
A: Communicate: One of the most a significant ways that technology has revolutionized the way our…
Q: Differentiate between database management systems and file-oriented systems.
A: Please find the answer in next step
Q: What is a structural chart defined as? Describe the many categories of modules in a structure chart…
A: Introduction: What is the definition of a structural chart? Describe the many categories of modules…
Q: It is better to have a computer with logical divisions and subsystems than one without.
A: Subsystems and logical divisions combined on one machine
Q: What are the advantages of using CUDA and graphics processing units (GPUs) for computing?
A: Given: Advantages of CUD and GPU computing Code may read from any memory address, resulting in…
Q: Why is a good knowledge of Boolean algebra essential for computer scientists?
A: answer is
Q: What distinguishes MATLAB for solving computational geometry programs from other programming…
A: Introduction MATLAB MATLAB is a programming platform created specifically for engineers, trainees,…
Q: protocol called RTP (Real-time Transport Protocol) enables real-time data transmission and…
A: The Real-time Transport Protocol (RTP) is a network standard for transferring audio or video data…
Q: 2.Name and describe three HTML tags used in creating a drop-down list.
A: The three HTML tags used in creating a drop-down list are: select option optgroup
Q: the unified device architecture that wa
A: Solution - In the given question, we have to Define the unified device architecture.
Q: What are the differences between the business intelligence architecture's parts?
A: A business intelligence architecture is a platform for the several technologies an organization…
Q: What advantages do client-server architectures offer over peer-to-peer systems?
A: P2P is also known as peer-to-peer.
Q: State two advantages of the LoLiMoT neuro-fuzzy network.
A: The LoLiMoT algorithm partitions the input space in hyperrectangles by axis orthogonal splits. In…
Q: c# write program that Calculate a sum of secondary diagonal numbers in array square matrix
A: Introduction to Array An array data structure allows you to store numerous variables of the same…
Q: What protocol, if any, is used to protect communication between a web browser and a web server,…
A: Protocols are used for communication between a web browser and web server.
Q: When a web client tries to access protected resources on a web server, show how native auth
A: The following are the security methods it employs: Extended-release Security Context now creates…
Q: What do you think are the most significant benefits of arrays? This is the maximum number of…
A: Arrays will store the similar type of elements in adjacent locations. we uses indexes to access the…
Q: What does the term SIP (Session Initiation Protocol) mean?
A: SIP: Investors in a mutual funds have access to a facility called a Systematic Investment Plan…
Q: What database procedures are inaccessible to spreadsheet use?
A: Database: This is a term used to describe a data repository that is handled in a highly orderly way…
Q: in the entertainment, military, sports,
A: Introduction : Motion input is supported by mobile devices, computers and gaming devices. It can…
Q: Describe why, given a heap data structure, the trickle down algorithm takes more operations than the…
A: A heap is a binary tree having the following properties: It is always finished. This implies that…
Q: Which hardware configurations are necessary to guarantee the effectiveness of virtual memory…
A: Given: What hardware approaches are required to ensure the efficiency of virtual memory systems? Do…
Q: Solve this question with the complexity of O{n} Given Two integer array nums of distinct items and a…
A: According to the question, we have to write a program code according to given criteria. In step 2,…
Q: In JS Create a function that takes an array of integers as an argument and returns the same array in…
A: Algorithm - Take input from user. Now use the below logic - while(arr.length>0){…
Q: The tiers, cost-benefit analysis, and performance of client/server architecture should be explained
A: Introduction Client/Server Architecture is generally refers to systems that divide processing…
Q: The CPU enters values into memory locations, and certain registers are utilized to store both the…
A: Central processing unit is the component of the computer system which controls the interpretation…
Q: What exactly does the terminology "hardware" and "software" mean?
A: Hardware" and "Software: The term "hardware" a describes the actual, observable parts of the system,…
Q: Which group of software applications is in charge of monitoring the internal operation of the…
A: In this question we need to find out which software monitors the internal operation of the…
Q: What are a few of the most important things to take into account while backing up and restoring…
A: Start: Planning is done during the data a backup and recovery procedure to retain the back of the…
Q: Consider applying the variable elimination algorithm to the umbrella DBN unrolled for three slices,…
A:
Q: Your company is getting ready to add VoIP to its network. The business is concerned about how…
A: Quality of service (QoS) is the use of the mechanisms or the technologies which work on the network…
Q: Your father made the decision to start a software development company and made a start-up investment…
A: Several forms of network topology are described as follows: Star StructureBus TechnologyRing…
Step by step
Solved in 2 steps with 1 images

- A. What does the following JavaScript code do?let titles = "Mr.|Mrs.|Miss|Ms.|Dr.";let spotTitle = new RegExp(titles, "g"); a. creates a text string and stores it in the variablespotTitle b. defines a regular expression with a global flag by creating an object constructor c. defines a function to search for the substrings"Mr.","Mrs.","Miss","Ms.", and"Dr." d. throws an error because it attempts to enclose a regular expression in quotation marks instead of forward slashes B. Which of the following regular expressions will match both the substring "cat" (part of the word “catering”) and the substring "Cat" in the string "For your catering needs, call Cat!"? a. /cat/ig b. /cat/g c. /cat/ d. / cat /hen a function returns an anonymously constructed object from the return expression the compiler can make more efficient code — by eliding the copy construction of the return value — using the ____. Select an answer and submit. For keyboard navigation, use the up/down arrow keys to select an answer. a. return by object optimization b. returned value optimization c. object optimization procedure d. retro-viral organism e. retro-active functional optimizationQ3: Write a program in € using OOP to create a class (A) . that contain integer number (), contain the function (FACT) to calculate the factorial of (x!) and create a class (B) . that contain integer number (). contain the functions (POWER), to calculate ( x7). Then creat class ()., with public visibility mode inherit from class (A) . and public visibility mode inherit from cla s (B), contain the fimction that find (x!/ x°)
- Programming Language: C Write the following three functions: a) The function gets an array A of length n of ints, and a boolean predicate pred. It returns the smallest index i such that pred(A[i])==true. If no such element is not found, the function returns -1. int find(int* A, int n, bool (*pred)(int)); b) The function gets an array A of length n of ints, and a function f. It applies f to each element of A. void map(int* A, int n, int (*f)(int)); c) The function gets an array A of length n of ints, and a function f. The function f gets 2 ints and works as follows: 1. Start with accumulator = A[0] 2. For i=1...length-1 compute accumulator=f(accumulator, A[i]) 3. Return accumulator For example, if f computes the sum of the two inputs, then reduce() will compute the sum of the entire array. int reduce(int* A, int n, int (*f)(int,int)); Test for the functions: // used for test Q3-find bool is_even(int x) { return x%2 == 0; } bool is_positive(int x) { return x>0; } void…a. Extend the definition of the class newString as follows:i. Overload the operators + and += to perform the string concatenation operations.ii. Add the function length to return the length of the string.b. Write the definition of the function to implement the operations defined in part a.c. Write a test program to test various operations on the newString objects.Q3: Write a program in C++ using OOP to create a class (A) , that contain integer number(x) , contain the iilnction (FACT) to calculate the factorial of (x!)and create a class (B) , that contain integer number (n ) , contain the functions (POWER),to calculate ( .xü).-Illen create a Class (C) , with public visibility mode inherit from class (A)and public visibility mode inherit from class (B),contain the tunction that find
- Q3: Write a program in C++ using OOP to create a class (A), that have a two dimensional array X[5][5], and function (input) to read it from keyboard Then create a class(B), with public visibility mode inherit from class (A), contain the function (sample_T) to print the element that form the letter (T)in array (X). Then create a class(C), with public visibility mode inherit from class (A), contain the function (sample L.) to print the element that form the letter (L) in array (X). Then create a class(D), with public visibility mode inherit from class (B) and (C), contain the function (RUN) to call the to function above.Question: Implement the following functions in your class: getTotalWords (returns the amount of total words), getUniqueWords (returns the amount of unique words), getMostUsedWord, (returns the word that is most used) getMaxOccurrence (returns how many times the most used word occured). Name them as indicated here. The code to add the functions to: import edu.princeton.cs.algs4.*;import edu.princeton.cs.algs4.LinearProbingHashST;import edu.princeton.cs.algs4.SeparateChainingHashST;import edu.princeton.cs.algs4.ST;import edu.princeton.cs.algs4.SequentialSearchST;import edu.princeton.cs.algs4.In;import edu.princeton.cs.algs4.StdOut; public class TestPerf { public static long LinearProbingHashST(String x[]) { LinearProbingHashST<String, Integer> st = new LinearProbingHashST<String, Integer>(); long start = System.currentTimeMillis(); for(int i = 0; i < x.length; i++){ String key = x[i]; if…Write a class basicMaths and use constructor to pass a number. Create a function FindNumber takes one number as a parameter and Ñnds if it is positive or negatieve number. Create another class intermediateMaths with same functions and redeÑne the FindNumber functionality by Ñnding the number as even or odd number. Create another class advanceMaths with same functions and redeÑne the FindNumber functionality by Ñnd the number as prime number or composite number. Consider the following example code for the logic of prime number:
- in c++ 1. Write a function that takes a 1 Dimensional array and an integer n andreturns the number of times ‘n’ appears in the array. If ‘n’ does not appearin the array, return -1.2. Write a function that takes a 2 Dimensional array and returns the positionof the first row with an odd sum. Assume that the column size is fixed at 4.If no sum is odd, return -13. Write a class, “pie”, that has a number of slices (int slices) as a privateproperty. Construct the pie with a number of slices and remove a slice witha function. Tell the user how many slices are in the pie.Write the following three functions: a) The function gets an array A of length n of ints, and a boolean predicate pred. It returns the smallest index i such that pred(A[i])==true.If no such element is not found, the function returns -1.int find(int* A, int n, bool (*pred)(int)); b) The function gets an array A of length n of ints, and a function f. It applies f to each element of A.void map(int* A, int n, int (*f)(int)); c) The function gets an array A of length n of ints, and a function f. The function f gets 2 ints and works as follows: Start with accumulator = A[0] For i=1...length-1 compute accumulator=f(accumulator, A[i]) Return accumulator For example, if f computes the sum of the two inputs, then reduce() will compute the sum of the entire array.int reduce(int* A, int n, int (*f)(int,int));Need Help fixing my code!! only under TODO's. // Util function to convert a FoodWastageReport class object into a serialized// JSON object.crow::json::wvalue FoodWastageReportToCrowJSON( const FoodWastageReport &report) { crow::json::wvalue report_json({}); std::vector<std::string> most_common_disposal_mechanisms{}; // TODO 1: Call the member function of FoodWastageReport class that returns // all the most common disposal mechanisms as a vector of strings. Store the // result in the vector declared above. FoodWastageReport report; std::vector<std::string> most_common_disposal_mechanisms = report.MostCommonDisposalMechanisms(); report_json["most_common_disposal_mechanism_"] = most_common_disposal_mechanisms; std::vector<std::string> most_commonly_wasted_foods{}; // TODO 2: Call the member function of FoodWastageReport class that returns // all the most commonly wasted foods as a vector of strings. Store the result // in the vector declared…

