SQL language
Chapter7: Database Administration
Section: Chapter Questions
Problem 11TD: Toys Galore currently has a credit limit of 7,500. Because Toys Galore has an excellent credit...
Related questions
Question
Please solve asap my deadline is very close
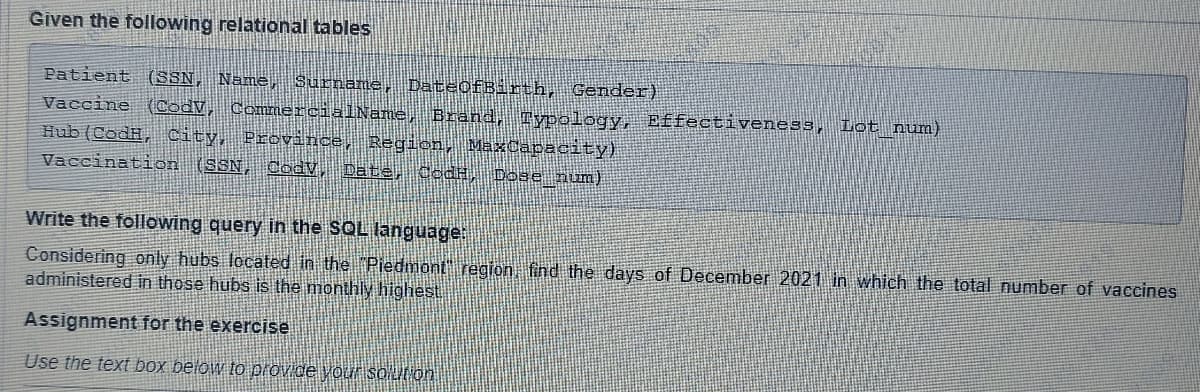
Transcribed Image Text:Given the following relational tables
Patient (SSN, Name, Surname, DateOfBirth, Gender)
Vaccine (CodV, CommercialName, Brand, Typology, Effectiveness, Lot_num)
Hub (CodH, City, Province, Region, MaxCapacity)
Vaccination (SSN, Cody, Date, JodH, Dose_num)
Write the following query in the SQL language:
Considering only hubs located in the "Piedmont" region, find the days of December 2021 in which the total number of vaccines
administered in those hubs is the monthly highest.
Assignment for the exercise
Use the text box below to provide your solution
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 5 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning