- (SSL/TLS Protocol) Figure 1 shows a TLS message (I intentionally hide its message type). What is this TLS message? Give evidence to support your answer. What are the purposes of this TLS message?
- (SSL/TLS Protocol) Figure 1 shows a TLS message (I intentionally hide its message type). What is this TLS message? Give evidence to support your answer. What are the purposes of this TLS message?
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter8: Network Infrastructure And Troubleshooting
Section: Chapter Questions
Problem 8TC
Related questions
Question
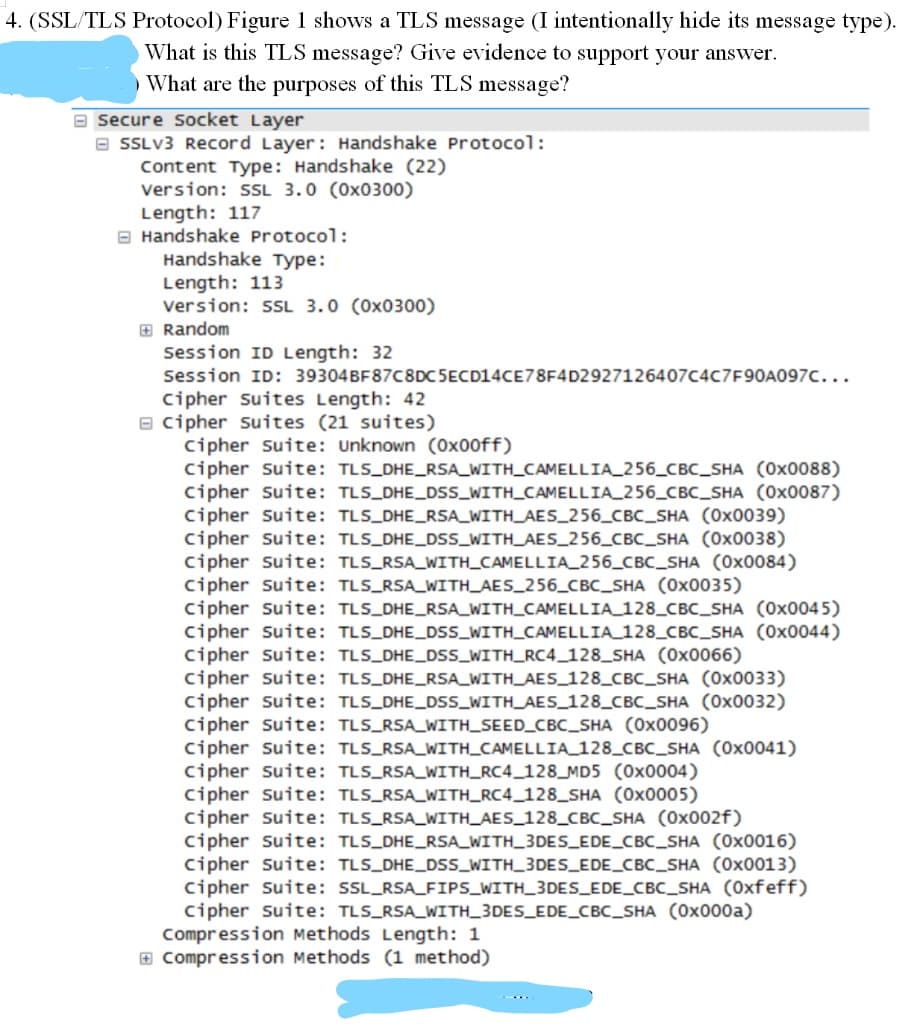
Transcribed Image Text:4. (SSL/TLS Protocol) Figure 1 shows a TLS message (I intentionally hide its message type).
What is this TLS message? Give evidence to support your answer.
What are the purposes of this TLS message?
secure socket Layer
a SSLV3 Record Layer: Handshake Protocol:
Content Type: Handshake (22)
Version: L 3.0 (0x0300)
Length: 117
O Handshake Protocol:
Handshake Type:
Length: 113
version: sL 3.0 (0x0300)
E Random
Session ID Length: 32
Session ID: 39304BF87C8DC 5ECD14CE78F4D2927126407C4C7F90A097C...
Cipher suites Length: 42
e cipher suites (21 suites)
cipher suite: Unknown (0x00ff)
cipher suite: TLS_DHE_RSA_WITH_CAMELLIA_256_CBc_SHA (0x0088)
cipher suite: TLS_DHE_DSS_WITH_CAMELLIA_256_CBC_SHA (0x0087)
cipher Suite: TLS_DHE_RSA_WITH_AES_256_CBC_SHA (0x0039)
Cipher suite: TLS_DHE_DSS_WITH_AES_256_CBC_SHA (0x0038)
cipher suite: TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (0x0084)
cipher suite: TLS_RSA_WITH_AES_256_CBC_SHA (0x0035)
Cipher suite: TLS_DHE_RSA_WITH_CAMELLIA 128_CBc_SHA (0x0045)
Cipher suite: TLS_DHE_DsS_WITH_CAMELLIA 128_CBc_SHA (0x0044)
cipher suite: TLS_DHE_DSS_WITH_RC4_128_SHA (0x0066)
cipher suite: TLS_DHE_RSA_WITH_AES_128_CBC_SHA (0x0033)
cipher suite: TLS_DHE_DSs_WITH_AES_128_CBC_SHA (0x0032)
cipher suite: TLS_RSA_WITH_SEED_CBC_SHA (0x0096)
cipher suite: TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (0x0041)
cipher suite: TLS_RSA_WITH_RC4_128_MD5 (0x0004)
cipher suite: TLS_RSA_WITH_RC4_128_SHA (0x0005)
cipher suite: TLS_RSA_WITH_AES_128_CBC_SHA (0x002f)
cipher suite: TLS_DHE_RSA_WITH_3DES_EDE_CBC_SHA (0x0016)
cipher suite: TLS_DHE_DSS_WITH_3DES_EDE_CBC_SHA (0x0013)
Cipher suite: SSL_RSA_FIPS_WITH_3DES_EDE_CBC_SHA (0xfeff)
cipher suite: TLS_RSA_WITH_3DES_EDE_CBC_SHA (0x000a)
Compression Methods Length: 1
E Compression Methods (1 method)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning