start Get positive integer from user, call it A. Get positive integer from user, call it B. C = A B = A true false B > 1? D = C E = A D> 0? B = B-1 false true Display the A = A + E value of A. D = D - 1 end
Q: mpare the advantages and disadvantages of First-fit memory allocation versus Best-fit memory allocat...
A: Kindly Note: As per our guidelines we are supposed to answer only first question. Kindly repost othe...
Q: Given the data word 10100111110 and the divisor 10111, a. Show the generation of the codeword at the...
A: Below is the answer to above question. I hope this will meet your requirement....
Q: networking - How does a centralised IP-based building security system aid in cost savings?
A: Introduction: The centrally managed IP-based building security system will be discussed in the provi...
Q: Discuss how you would implement the Boyer-Moore string search algorithm to do a string search in the...
A: Intro In computer science, string/pattern searching is a significant problem. When someone tries to ...
Q: Discuss any five disadvantages of cloud computing that are frequently overlooked.
A: Introduction: The phrase "cloud computing" refers to a sort of Internet-based computing in which an ...
Q: Could you perhaps describe in a few words the most common sorts of OS intruders?
A: INTRO Operating system (OS) intruders are a type of malicious software that secretly infect compute...
Q: 6. You are going to play WAR against the computer. This can be super basic. You can have the user "d...
A: Generate a random number from 2 to 14 (where 11 represents J, 12 represents Q, 13 represents K, 14 r...
Q: Go to the Scores by Date worksheet. In cell A3, insert another PivotTable based on the Calls table. ...
A: Here is the solution to the abov problem :- Step 1 Select the table from A4:J143 Step 2 Insert pivo...
Q: Matlab Create a 2D convolution that uses methods circular and nearest neighbor for border handling ...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: C++ Code Only: Write a program to print the following output: 1 12 123 123 4 123 45
A: Program Explanation :- First create the variable ro for program. Then Take the input from the user...
Q: Discuss the history of information systems, focusing on the main players and events that contributed...
A: Introduction: The use of computers to process data is the fundamental principle of information techn...
Q: P7. Consider the network fragment shown below. x has only two attached neighbors, w and y. w has a m...
A:
Q: Show the value that gets stored in the indicated variables(s) after the given sequence of statements...
A: The answer is given below.
Q: Computer Science 5. Using Dijkstra's algorithm, generate a least-cost route to all other nodes for n...
A: Here, we are going to find out the least cost route to all other nodes for node A. Dijkstra's algori...
Q: The OSI and TCP/IP Models are useful tools for understanding and communicating about connectivity an...
A: Introduction: The OSI model specifies how communication should be carried out, whereas TCP/IP protoc...
Q: Explain Geo Restriction in CloudFront Computer science
A: Introduction: We're thrilled to introduce Geo Restriction, a new tool that lets you utilize Amazon C...
Q: Write Java statements (not necessarily complete programs) to achieve indicated task. Declare a doubl...
A: import java.io.*; public class Main { public static void main(String[] args) { ...
Q: A flattened Neural Network for handwritten digital classification takes in 43X43 pixel images. How m...
A: Introduction: Here we are required to mention how many inputs neurons are in the network of 43 x 43 ...
Q: What is your understanding of Data security?
A: Kindly Note: As per our guidelines we are supposed to answer first question. Kindly repost other que...
Q: In a computer system, the bus is described as a collection of cables used to transport data from one...
A: INTRODUCTION:- In computer architecture, a bus is a communication system that transports data betwee...
Q: For each category of data owner, provide specifics on data security, data ownership types, and dutie...
A: Data security is the process of defending digital data against unauthorized access, corruption, or t...
Q: a. This adjustment can be done by normalizing to values between 0 and 1, or throwing away outliers. ...
A: The code is below: I have written it in C and Python.
Q: describe and explain network administration and network maintenance, with no definition and explanat...
A: Intro Network maintenance : Network maintenance is the process of keeping computer networks and the...
Q: Using python - show-step-by-step with any needed fuctions that need to be added and show screenshots
A: This Program is written for calculating the cost of different different sets of the consumption of t...
Q: Registers in the central processing unit are compact, fast data storage spaces that are used to temp...
A: Introduction: Registers are compact, fast, stand-alone data storage locations in the central proces...
Q: What will be displayed in the console, given this code?
A: The output of the above code is : 5 6 7 8 9 for(int ctr = 5; ctr<num; ctr++) { if(ctr *...
Q: Find simple connected graphs with the following vertex degrees if possible. 2 2 2 2 3 3 3 3 4 4 4 ...
A: Here in this question we have given three graph degree sequence and we have asked to find connected ...
Q: Define an integer vector and ask the user to give you values for the vector. because you used a vect...
A: Introduction Define an integer vector and ask the user to give you values for the vector. becaus...
Q: What security flaws are exploited and how may these issues be addressed in the future in the case of...
A: Introduction: Data damage is defined as any decrease in integrity or data acquisition. Damage to a c...
Q: // Suppose we have the following min-heap: // 2, 3, 4, 16, 7, 11, 9, 31, 18, 21, 12 // After callin...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Explain your understanding clearly by identifying technology and security procedures for the second ...
A: Introduction: Identify Trust Zones, Potential Adversaries, and Threats is the second phase in threat...
Q: Show the value that gets stored in the indicat int ans - 20, x - 50, y - 75; if (x >= y) ans + x + y...
A: Solution: Value stored in ans = 20 , x = 50, y= 75 if( x >= y) ans += x+ y else ans +=...
Q: What is a straightforward algorithm? *please give an example (if you can)*
A: Introduction: Here we are required to explain what is a straight forward algorithm.
Q: num3. What is the pseudocode and flowchart #include using namespace std; int main() { int x,n...
A: For this question we are required to design the Pseudocode and the Flowchart for the given code. Giv...
Q: In Symbian, Android, and iPhone, what impact has the file deletion algorithm had?
A: Given: In Symbian, Android, and iPhone, what impact has the file deletion algorithm had?
Q: The following numbers are inserted into an empty LLRBT in the given order: 11, 2, 14, 25, 15, 13, 16...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: 3. In the below PowerShell AD script why is ">>" used instead of "“>"? Get-ADForest >> ||dc1\shared\...
A: The answer as given below:
Q: Create a HTML page called q3.html. This page should contain a HTML form that itself contains three t...
A: The code is given below.
Q: What database management options are available to manage data integrity in the field?
A: Introduction: The operations required to maintain and make a database accessible are referred to as ...
Q: Observe the given code carefully. Try to understand from the given code and the outputs what to writ...
A: Given the code and complete the code with the relevant remaining code. The code contains class Dolls...
Q: Indicate whether or not the following is a valid Java statement. Whenever the statement is invalid, ...
A: double net profit = 5000.00; double is used to store float values ,it uses 64 bits to store a variab...
Q: Match the mode setting with the operation to be performed.
A: EDIT D) Save, delete, and change word address part program...
Q: s it a description of the operation of a computer? Then we'll talk about computer components, rig...
A: Intro A computer system works by combining input, storage space, processing, and output. let's disc...
Q: Preventing unethical and illegal behaviour in the field of computer science
A: Introduction: 'Unethical' refers to something that is morally incorrect, whereas 'illegal' refers to...
Q: convert from this coding below to mbed c++ #define BLYNK_DEVICE_NAME "NodeMCU" #define BLYNK_AUTH_...
A: It is defined as a compiled programming language originally derived from C. C++ supports object-orie...
Q: 1. Use open method to find the first positive and first negative solutions. In other words, find the...
A: For the regular expression given in the question number two L ((ab + b)* b (a + ab)*) we will have L...
Q: You will be building a linked list. Make sure to keep track of both the heac (1) Create three files ...
A: #include "ContactNode.h"//#include "ContactNode.cpp" #include <iostream>#include <string>...
Q: Define the phrase "access."
A: Definition: Access: The Access is been referred to as that of the permission that to use, for using ...
Q: num1. What is the pseudocode and flowchart #include using namespace std; int main() { int num...
A: For the given C++ code we will find out its flow chart and pseudocode for it. Please refer to the im...
Q: for line in f: sline line.replace('\n', '') sline.split(',') if t[4] "Iris-versicolor": val = 1 %3D
A: The solution is as follows: When you try to access an item with a value that is out of the list's in...
If both A and B are positive integers, which of the following is an equivalent result to the flowchart?
- A * B
- A ** B
- A * A
- A ** A
- none of the above
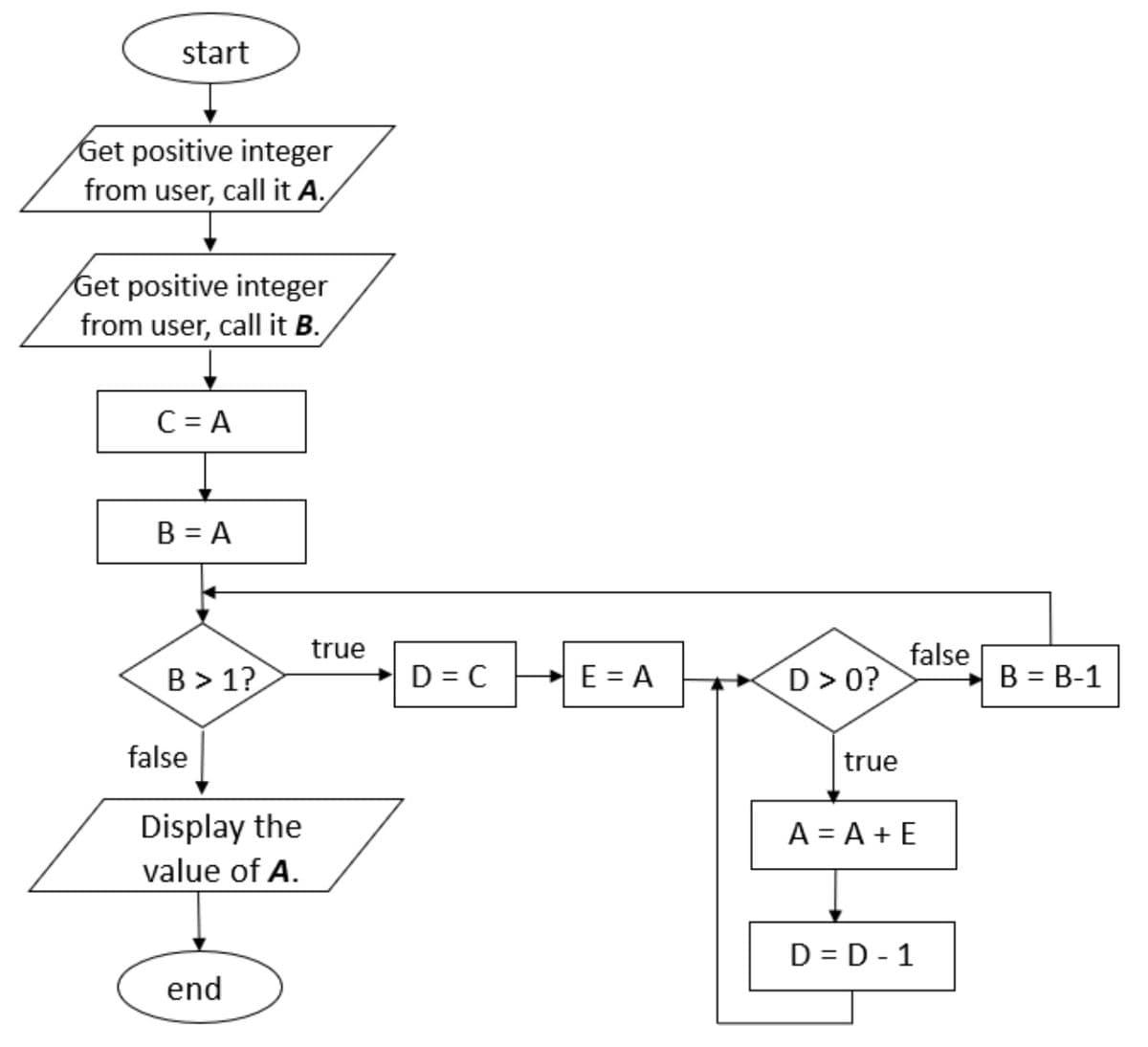
Step by step
Solved in 2 steps

- Write an application that prompts a user for two integers and displays every integer between them. Display There are no integers between X and Y if there are no integers between the entered values. Make sure the program works regardless of which entered value is larger.Allow a user to enter any number of double values up to 15. The user should enter 99999 to quit entering numbers. Display an error message if the user quits without entering any numbers; otherwise, display each entered value and its distance from the average. Write Java code please import java.util.*; public class DistanceFromAverage { public static void main (String[] args) { // Write your code here } }Allow a user to enter any number of double values up to 15. The user should enter 99999 to quit entering numbers. Display an error message if the user quits without entering any numbers; otherwise, display each entered value and its distance from the average. import java.util.*; public class DistanceFromAverage { public static void main (String[] args) { // Write your code here } }
- Write an application that reads an integer value from the user and prints the sum ofall even integers between 2 and the input value, inclusive. Print an error message ifthe input value is less than 2. Use Java. Sample Run Examples: Example 1:the user enters 14Output: Sum: 56Example 2:the user enters 1Output: Error number must be greater than 1write a psesudocode for a program that calculates the bill of a sandwich stand. The program should ask theuser to enter the quantity of each of the items. Then compute 13% GST on the total amountand generate a bill with items, their quantity along with price of each item and the total(inclusive GST). The stand has the following items:- Petti for $2.50- Drink for $1.25- Extra cheese topping for $1.25Write a program named GuessingGame that generates a random number between 1 and 10. (In other words, in the example above, min is 1 and max is 11.) Ask a user to guess the random number, then display the random number and a message indicating whether the users guess was too high, too low, or correct.
- One interesting application of computers is drawing graphs and bar charts.Write a program that prompts the user to enter 5 integers, and then outputs abar chart consisting of asterisks. The number of asterisks in each line of thebar chart must be equal to the number the user entered. You may assume theuser will enter only positive integers or 0. C++ please.Write an application that allows a user to enter any number of student quiz scores, as integers, until the user enters 99. If the score entered is less than 0 or more than 10, display Score must be between 10 and 0 and do not use the score. After all the scores have been entered, display the number of valid scores entered, the highest score, the lowest score, and the arithmetic average.In Java Create a class DoWhileEvent3, write code that ask the user to enter a positive or negative number or 'x' 'X' to quit the program. When out of the loop the sum of all numbers entered is printed. READ THE USER'S input as String an not as integer. Use a do while loop.
- Write a VB program to ask user to assign a value to “i” to find the answer for the following three cases. 1. Case 1. Assume i = 1 and HowMuch = 0IF i < 5 THENHowMuch = HowMuch + 1ELSEIF i = 5 THENHowMuch = HowMuch - 5ELSEHowMuch = HowMuch + 3END IFDISPLAY HowMuch2. Case 2. Assume i = 5 and HowMuch = 0IF i < 5 THENHowMuch = HowMuch + 1ELSEIF i = 5 THENHowMuch = HowMuch - 5ELSEHowMuch = HowMuch + 3END IFDISPLAY HowMuch3. Case 3. Assume i = 6 and HowMuch = 0IF i < 5 THENHowMuch = HowMuch + 1ELSEIF i = 5 THENHowMuch = HowMuch - 5ELSEHowMuch = HowMuch + 3END IFDISPLAY HowMuchIn Java Create a class WhileEvent3, write code that asks the user to enter a positive or negative number or 'x' 'X' to quit the program. When out of the loop the sum of all numbers entered is printed. READ THE USER'S input as String an not as integer.Write an application that reads an integer and determines and prints whether it’s odd or even. [Hint: Use the remainder operator. An even number is a multiple of 2. Any multiple of 2 leaves a remainder of 0 when divided by 2.]



